// Small NEWS // How the Chinese Would Have Created The Ideal Backdoor With Their Microchip Spy
The material implant relied on the BMC chips of the motherboard, a component that can communicate with the outside and has privileged access to various parts of the system.
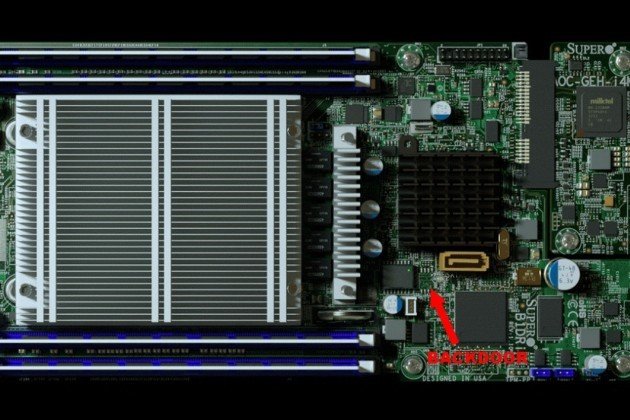
Revealed Thursday through a long Bloomberg’s survey, the tiny chip implanted by the Chinese hackers on the Supermicro servers motherboards established gateway dreamed by all the spies on the planet. Undetectable to the naked eye, this component was apparently placed between a SPI Flash chip and the BMC (Baseboard Manager Controller), if we believe the animation of the Bloomberg article
Zooming in on the Bloomberg animation showing the alleged malicious component in the Supermicro servers looks reasonable for the described attack. It is positioned on an unpopulated SOIC-8 SPI flash footprint between the SOIC-16 SPI flash chip and the BMC.
— Trammell Hudson (@qrs) 4 octobre 2018
The BMC chip is a strategic place of the motherboard. This micro-controller orchestrates a large number of technical parameters of the machine as the temperature, the fan speed, the energy input, etc. It also has the capacity to communicate with the outside. Indeed, the administrators system use the BMC chip to, for example, restart the system remotely. This feature was used by the spy chip to connect to Chinese hacker command and control servers and, thus, download malicious code.
But that's not all. The BMC chip is connected with many other parts of the server. According to Bloomberg, it would have allowed this chip to intercept and modify the instructions between the memory cache and the central processor.
The BMC is vastly over-privileged and tied into so many parts of the system. Securing it is vital to secure the root of trust, and open source firmware like OpenBMC and u-BMC are good first steps to trusting it.
— Trammell Hudson ⚙ (@qrs) 4 octobre 2018
From there, everything becomes possible. The aggressors can siphon for example secret keys or interrupt an update (what is practical if we want to avoid the installation of a security patch). It is also possible to modify Linux code and to deactivate an authentication procedure to connect more easily to the system. In brief, the machine is totally under the control of the Chinese hackers.

But attention: the Chinese are not the only ones to use hardware implants for espionage purposes. Edward Snowden's revelations had shown existence within the NSA of a whole catalog of "products" that the Americans secret agents could use to plumb a computer, a server, a smartphone, a screen, etc.
The installation of these implants was often made before the delivery. The parcel is intercepted and the product modified on the fly. The Chinese method, where the microchip is integrated at the same moment of manufacture, is obviously more efficient...
This news makes me paranoid and hungry against this world that doesn't allow us some privacy and enough liberty... And you?
I've made a lot of articles with tools, explanations and advises to show you how to protect your privacy and to secure your computer, GO check them out!
This is my guide to secure your PC after a fresh installation of Windows
If you think that your phone or your PC has been hacked, you have to check it right now!
That's how you can be more Anonymous on the internet!
These are the best VPN to protect your numeric life: NordVPN, ExpressVPN and CyberGhost!
Your PC is slow? That's why!
You Feel hot? Your computer also!
How an adware works?
That's how you should guard against Trojan!
What are the different types of hackers?

And Trump will do nothing about it, as long as they build a few buildings of his and keep staying at his hotels!

No matter what else you are impassioned to correct: Jobs, Tariffs, Russia, Dacca, Puertor Rico, Flint, EPA, Emoluments, ICE, Racism, Tax breaks, Bum Stocks, AHCA, BLM, Me too and the 100s of other reason.
This means there is only 1 way to deal with this.... Register and Vote.... It matters!
Register in under 10 minutes here till friday:
https://social20.turbovote.org
And MAKE PLANS TO Vote IN 4 WEEKS ON TUEDAY Nov. 6th
Congratulations,
you just received a 14.49% upvote from @steemhq - Community Bot!
Wanna join and receive free upvotes yourself?
Vote for
steemhq.witnesson Steemit or directly on SteemConnect and join the Community Witness.This service was brought to you by SteemHQ.com