That's how you should guard against Trojan (if you care about you money and your privacy...)
Trojan, RAT, Remote Administration Tool, no matter how it's called, it's scary as it looks dangerous and effective.
In today's article I will explain how a Trojan horse works, we'll observe what it does and how it does it. At the end of this article, you will able to deduce ways to protect yourself from it properly.
WHAT IS A TROJAN HORSE?
A Trojan Horse is a healthy-looking program that contains a hidden malware program. And yet here is the definition of the most popular Trojan horse:
"A Trojan Horse is a program that takes control of a computer"
This is the commonly accepted definition, anchored in everyone's mind.
However, the initial definition of the Trojan Horse is not exactly this one, as we have just seen.
The term "Trojan Horse" comes from a legend of ancient Greece in which the Greeks used a giant wooden horse to conquer the city of Troy.
They hid inside the wooden horse, so they could enter the city. Once inside the city, they came out of this horse to open the doors to the rest of their army and to destroy the city.
The term "RAT" comes from the Remote Administration Tool and is used to take control of a remote computer (without hiding in a healthy appearance).
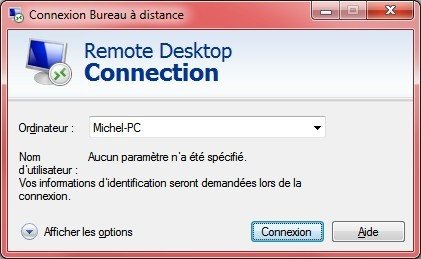
The RAT can be used 100% legally, especially for remote maintenance, if you have for example a big problem that only a technician can remotely solve. Besides, you have almost all a RAT on your computer, this is the Windows Remote Desktop.
Only today, the Trojan Horses allow to insert RATs in a discrete and hidden way in the computer of the victim. It is therefore currently that it is possible to take control of the remote computer.
It could thus be said that the RATs are legitimate and legal tools (if they are used with authorization) while the Trojan Horses allow to insert a RAT on a remote machine in order to control it.
FUNNCTIONING OF THE RAT
I will therefore assume in the following that the Trojan whose containe a RAT was sent and executed on a remote computer.
A RAT is composed of two parts: A customer and a server:
• The customer is the program launched on the machine (the hacker) that will control the other computer.
• The server is the program launched on the machine (of the victim) that will be controlled.
THE CUSTOMER
The technician will have his program that he will check from time to time to see if a consenting person is connected.
The program will ask for an IP address, a name and a listening port.
You should know that the customer will provide this information to a server skeleton (usually called Stub). The entire server will be initially created by the customer himself.
THE IP ADDRESS
This is to provide the address of our own computer, in fact we will provide the server that we will create our own IP address so that it can later send us the data simply.
Here the address 127.0.0.1 is special, it is the address of my local network, because I will not do the demonstration remotely but on my own pc. The customer and the server will be on my pc, but the connections will be through the network as if I were doing it on a remote computer.
THE NAME
This is the name that will be given to the controlled computer. If we control several we will have the names displayed in the ID column on a different line.
THE PORT
This is the number through which we communicate. To understand what a port is, take this analogy: The port is your phone number. If your number is 92 and the one of your mother is 85, then if we call the 85 by wanting to communicate with the 92 there will be a problem!
You and your mother are in the same house (same IP address), but each one have his phone number (each computer has multiple ports for different services).
SIGNS OF AN INFECTION
Now that the Client <-> Server connection is well established, we will take the opportunity to observe what is happening to pinpoint this connection and go into the detection and prevention against trojans.
To begin, we will see what happens on the network side.
For commands addicts, you can find the netstat -a command to see the connections:
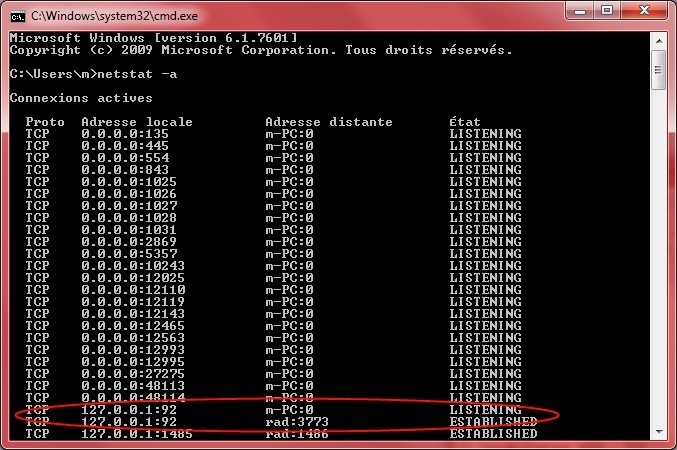
I circled in red the two lines corresponding to the customer and the server, we see that the connection is established on the address 127.0.0.1 and on the port 92.
For a more complete overview, you can download TcpView which I’ve already talked about.
Let's look at connections with TcpView:
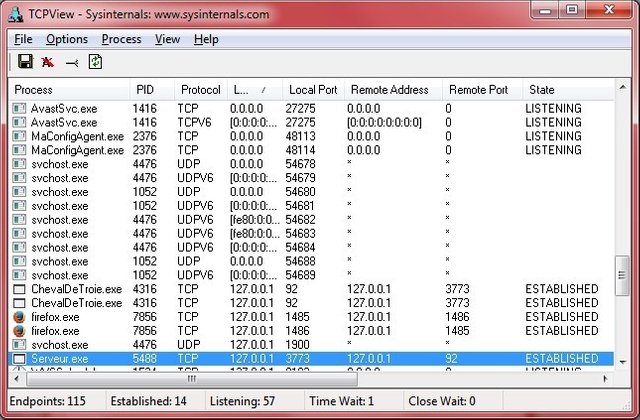
It clearly shows the names of the two processes, "ChevalDeTroie.exe " (which should be more properly called Client.exe) and Server.exe.
We also observe that for the customer, the local port is 92, and for the server it is the remote port.
What does this tell us?
We can check with TcpView all processes that have a defined remote port whose connection is established. If we do not recognize the process, we can directly right click then Process Properties to check its path and possibly delete it.
You can also click on End Process to finish the process.
Warning: Finish the process is not deleting the program. If it reboots when the computer starts, stop the process won't be enough. It will therefore be necessary to go into the file and delete the program.
Now, let's take a look at what's happening at the process level:
Open the Task Manager by pressing CTRL + SHIFT + ESC or CTRL + ALT + DELETE
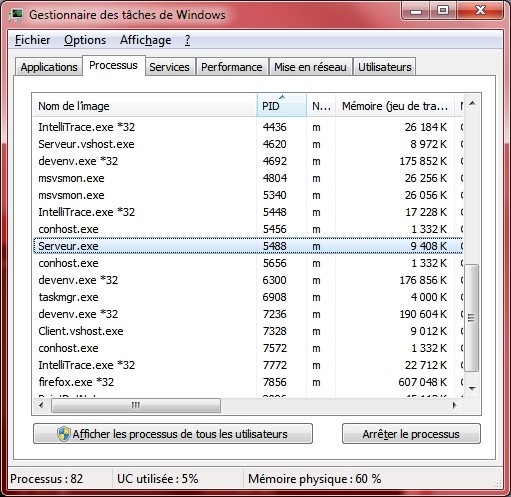
Surprise! Our server is here, we can stop there too.
How to guard against Trojan horses?
We have seen it, understanding how they work is a good start.
Here are other ways to prevent:
• Install an antivirus and a firewall: The antivirus detects known Trojans / RATs and the firewall blocks access to ports.
• Do not let anyone physically access to your computer: It is very easy to install a server while you are in the toilet.
• Pay attention to the content of e-mail attachments: a Trojan horse may be in.
• Pay attention to the trapped sites: Example with Java Drive By which makes it possible to run a program discreetly from a site.
• Be suspicious before clicking on a program: The ultimate instruction (mistrust and awareness) is still valid.
And finally, if your mouse moves alone, if your keyboard starts typing alone or if files / programs open by themselves you also have a worrying sign of Trojan horse contamination…
An easy way to reduce your chance to be hacked is to use the double authentification
If you think that you have already been hacked, you should read this post

Great overview, example, and advice. I would also add to not install software, extensions, or patches from untrusted sites or developers.
Thx man and you are totally right! It's hard to think of all tips..
Teamwork! :)
You got a 4.61% upvote from @lrd courtesy of @vijbzabyss!
We are offering 100% earnings for our delegators + 15% curation rewards for the largest delegator and 5% of curation rewards are burnt.
Delegate Now
You got a 17.94% upvote from @slimwhale courtesy of @vijbzabyss!
I think that, protecting yourself from any kind of viruses ect is always good and reasonable. Great post :D
Yes, it must be done nowadays