The Security Guide Everyone Must Have on Holidays!
It’s the holidays and it’s the opportunity to take some fresh air and to take our devices with us to enjoy the good weather while surfing on the net. But cybercriminals do not go on a trip, on the contrary they take full advantage of the relaxation associated with summer to carry out their attacks.

Source
No concern, here is a mini guide to keep you safe during these holidays!
Watch out for public Wi-Fi networks
In summer, we move more than in winter and we use smartphones, laptops and tablets outside. Enough to be easily tempted to connect to the first Wi-Fi we met.
But before connecting to a given network, here are some good practice to keep in mind.
"Do not make banking transactions by using a public Wi-Fi network"
It’s an advice which we often hear but we must know a little better why and how to avoid being hacked.
Let us say that an open Wi-Fi network is by nature usable by a pirate to spy on the pages which you visit on the Internet.
The Wi-Fi hotspots which we meet in airports, stations or even restaurants are potentially opened and thus not encrypted (if you do not need to enter a password to sign in, the connection is opened).
The purpose of the network encryption is exactly to avoid that your neighbors, although they are in the access field of your network, cannot observe the pages which you are visiting.
It is there that the HTTPs technology comes into play. A potential spy on an open Wi-Fi network can read all the data transiting in white (http) including the passwords.
But he will only see HTTPs sites visited without being able to read the sent data, which will be encrypted.
These exposure problems of the data were explained by diverse examples among which:
Firesheep: a tool which allowed to get back sessions (immediate connection at a user account of the network).
Wireshark, network analysis tool allowing to observe the data sent in light on the network.
How to protect itself from threats due to the open Wi-Fi networks?
To begin it’s interesting to make sure that the visited sites use the HTTPs protocol.
It exists for that a browser extension called http everywhere, which watches that the HTTPs protocol is used among the sites that you visit.
Using a VPN is also very recommended because your connection will be coded and encapsulate in a tunnel through Internet which only you have access. By way of Bonus: any blocking of Web sites or filtering at the public Wi-Fi will be cancelled with a VPN.
The Wi-Fi hotspot can even be hostile itself and spy on the connected users
Can we thus make banking transactions through an open Wi-Fi network?
The answer is Yes in theory because HTTPs code the transmitted data.
But if HTTPS in itself weakens, all the security is compromised. And HTTPs can fall rather easily. There are for example tools of "stripping SSL" (on the side of the access point) allowing to dynamically observe HTTPs sites and to redirect in a transparent way ** links from HTTPS to HTTP **on the visited pages. The traffic is thus got back in clear and sent back on the destination site with HTTPs just like that (attack of the middle man).
There are also specialized peripherals which persuade the computer that it reconnects to a known network while even there an attack of the middle man takes places: the data are collected by the peripheral and sent back towards their destination.
How to protect itself against hostile accesses points?
It’s necessary to begin by using a firewall as the Basic Windows firewall: Windows Defender.
And to choose a VPN is an excellent investment to protect itself, as we saw it previously.
It’s also useful to select "Public network" during the connection to the network. It’s the famous window which asks us if we connect home or from a public place:
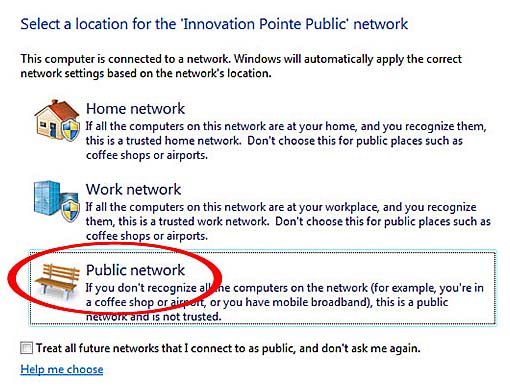
Setting the connection as public automatically deactivates file sharing, network discovery and public files sharing.
Finally, the ideal is simply not to make banking transactions through an open network.
Attention on the localization
Saying openly that we go on holiday on the social networks is never a good idea.
The ideal is rather to tell your holidays when you come back.
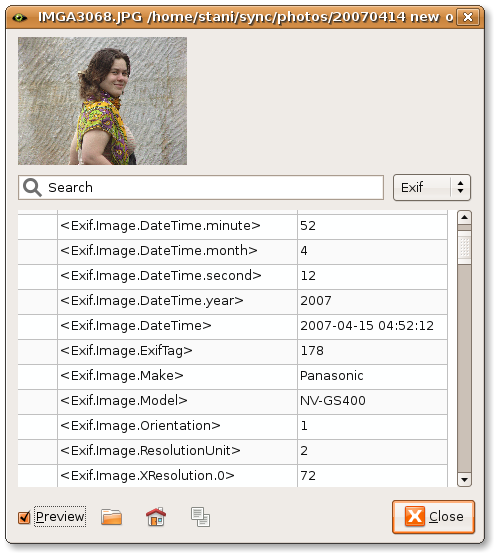
The pictures which you take with your devices also contain EXIF metadata’s (Exchangeable Image File Format).
These are data included in your photos which can be very interesting for a hacker given that the brand of your device as well as the precise localization of the place where the photo has been taken can be included.
Example:
Add a password or a locking
On holidays, we often embark our laptop, smartphone or tablet with us on the beach, on a field or even on public transport.

To put a password and to think of locking your session while you are absent is thus an obvious fact to mentioned. If not take directly the device with you.
We also recommend deactivating the Wi-Fi connections, Bluetooth and NFC (Near Field Communication) on devices endowed with these technologies when they are not used.
Attention to thefts
You arrive put under stress at the airport because the plane leaves in 10 minutes and you are only passing the security, so you hurry up and you get ready to run while under the stress you do not pay attention and your laptop gets stolen.

To avoid the thefts on holidays there are 2 principles to always have in mind
Verify regularly that all your luggage are present.
Do not display at sight of all valuables including smartphones and laptops.
To plan the worst, it’s also recommended to install surveillance applications on your computers and your smartphones to be able to trace a lost or stolen device.
Attention on the public computers
We have seen that connecting to a public Wi-Fi network can raise problems so it’s also necessary to mention the public computers which we are more likely to use on holidays.
We shall note for example cybercafé but also libraries and other places with free accesses to computers.
A keylogger can typically be settled there by another user or even by the owner itself.
Make sure that the computer which we use (who can very well be ours) is not infected by a hostile program is not necessarily an easy task. That's why I explained everything in a dedicated guide.
Raise awareness of children
On holiday, at home or somewhere else, the children probably use more than usually devices connected to the Internet.
To prevent all your banking data from finding themselves in the nature because your child (or any member of your family) has inadvertently shared them (the human fault once again), it’s necessary raise awareness on the risks of Internet and the safety precautions to always have in mind.
These precautions being the same ones as those we apply our self (non-exhaustive list):
Do not click on links or suspect programs.
Separate the sessions on the computers.
Do not communicate your password.
Always stay vigilant and be keep informed about the threats and the new safety ways.
Save everything
In case the worst happened, saving all your data before you go allows to escape many problems.
Here is a protection guide of data, you can naturally use the usual ways (USB keys, extern hard extern, Cloud … etc.).
To conclude, all these advices seem good to be bound to common sense and to good practices, and to tell the truth they are excellent defenses in IT security!
Good holidays to everyone!
I've made a lot of articles with tools, explanations and advises to show you how to protect your privacy and to secure your computer, GO check them out!
This is my guide to secure your PC after a fresh installation of Windows
If you think that your phone or your PC has been hacked, you have to check it right now!
That's how you can be more Anonymous on the internet!
How an adware works?
That's how you should guard against Trojan!
Why your PC is slow?

Congratulations,
you just received a 21.53% upvote from @steemhq - Community Bot!
Wanna join and receive free upvotes yourself?
Vote for
steemhq.witnesson Steemit or directly on SteemConnect and join the Community Witness.This service was brought to you by SteemHQ.com