Asking the Right Question
Charles Hoskinson took some time to respond my post on Cardano's consensus algorithm Ouroboros.
In his response he sets out a process that one must follow:
Start out with a Definition of Security, which apparently is the Foundation upon which all consensus protocols ought to be judged in our space. It defines what a secure Ledger is.
Next you need to prove that Proof of Work satisfies this so you have a benchmark.
Then you need to prove proof of stake satisfies this.
Proof of Work is not a Good Benchmark
According to Charles, the proof of work satisfies his definition of secure ledgers. In my opinion, proof of work provides terrible security based upon real world centralization in mining pools, misalignment of incentives, successful double spends, empty blocks, selfish mining, fee extortion, etc. Following the process laid out by Charles is an example of asking the wrong question: "How do we create a proof of stake algorithm with security properties of proof of work?". It will produce a proof-of-stake algorithm that fails to account for the problems present in proof of work because those problems are completely outside the scope of his definition of security.
For next time, consider making your post with Burn Reward option instead of Decline. You're more likely to get proportional attention to what your content is worth.
Using https://condenser.steemliberator.com/submit.html
Ps: An alternative solution would be have more people interested in a view that only show Declined payout posts. http://www.steemreports.com/trending-declined-payout-content/
Explanation for high upvote
This would be far better for the Steem economy, thanks for mentioning it and for continuing to attend to improving this platform.
This is great information as I am on the Verge of looking for solution on how to Decline my payouts as well.
I know this is a bot, but when you reply to "SOMEONE WHO CREATED THE PLATFORM" I am sure they understand the difference between Decline Payout and Burn Author Rewards. Since they or someone sitting next to them made the options.
Transisto is not a bot. Steemliberator is a project built by Netuoso after Dan left. It includes features (such as Burn Reward) which the Steemit version of condensor does not have.
So only the curators will get the rewards?
Yes and it reduce the supply of steem benefiting every steem owner.
It also in a negligible way not competing with the voting power it's redistributing to other posts.
Oh, I have no problem with the suggestion, or if it was a true bot or not. It struck me as funny with someone suggesting to Dan how something on Steemit works or what it does.
Well played. :)
or you could accept the payment and transfer it to me...I need money because I spend a lot in wine and prostitues
Great Suggestion!
but the burn author rewards is not in my option it only power up, default and decline payout.is it because am using steemit beta?
No it's a feature implemented only on https://condenser.steemliberator.com/submit.html
It's simply setting the main beneficiary as NULL. It's not possible to set other beneficiaries from Steemit. (it is on http://Chainbb.com)
Also steemplus addon allows it.
In his Reddit response to Dan's post, Charles refers to the EOS ERC-20 token distribution as an ICO, which is completely wrong.
In his cardano telegram response that has been posted to Reddit, he comments thus in response to the outrage at his failure to acknowledge his use of Dan's ideas without citation.....
This response, clearly rushed, reveals Charles's inconsistency. He says his protocol is distinctly different, then says DPOS is paxos with a voting system....so very similar other than voting then.
Then he accuses Dan of the same failure to cite, without any proof....which is what he is guilty of himself with respect to Dan's DPOS innovation.
Finally, he claims there is nothing in common between the ideas when he's just said DPOS is paxos with a voting system.
Dan isn't the one stealing ideas. He doesn't claim to have invented everything and does not claim everything else is junk.
Ethereum is an interesting computer science experiment. Does it scale without becoming something else entirely? No.
Instead of deflecting, I hope Charles can accept fair criticism and start acknowledging that he isnt the fountain of authority in this space. The world doesn't need any more egotistical academics, it needs real solutions to real problems as quickly as possible.
That Charles has no respect for Dan is clear. Why is that? What has Dan done other than what he said he would. Build tools that protect life liberty and property. Bitshares and Steem....two of the very best tools for accomplishing that. Yea, nothing to respect there.
I had a chat with Charles yesterday, well more an exchange of words in which Charles rants about his grevancies... I posted a little about this yesterday, and today Charles has begun hurling abuse at me over it.
If, as Charles claims, Dan called Charles a sociopath, I think he must have good cause for making such an assement. Charles isn't exactly demonstrating a rational behavior to the contrary.
Charles seems to be demanding respect and asserts that Dan has extremly little respect for him. The at times narcissistic ranting albiet humorously missfortunate was somewhat disturbing.
I don't know about you but I evaluate a project part on interaction with team members and community so when a team leader displays these types of characteristics it's going to naturally make me think twice about evaluating further.
Whatever, Charles claims to someday be adding to Cardano is really just empty words at this point academic peer review or not.
You know when you cannot argue, attack ad hominem...
Absolutely, goes without question and pretty much sums up why I ended that post with the video interview of Charles ranting about supposed addition ADA capabilities that Ethereum simply doesn't have, listen for Crypt0's response! "wooowhaaaa..t " it's hilarious about 1:13:00 in
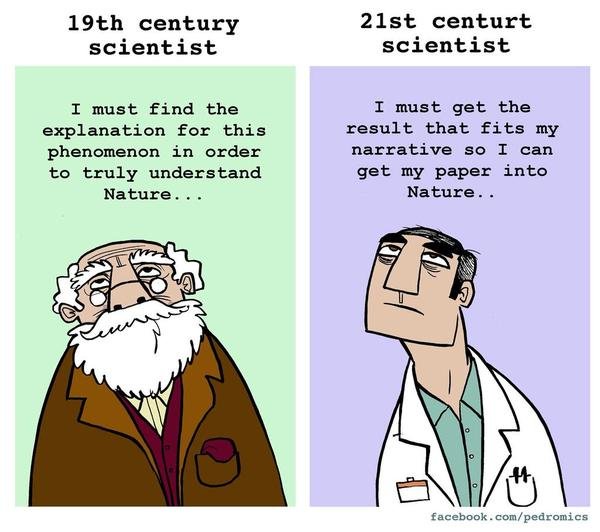
Charle's argument seems to be that peer review somehow ensures the quality of your idea or solution. The problem is, there is significant evidence (ironically often in the form of peer reviewed papers) that this is not the case:
http://www.lutz-bornmann.de/icons/BornmannARIST.pdf
https://www.scientificamerican.com/article/an-epidemic-of-false-claims/
so they... shouldn't try so hard? And just release rushed buggy hackable code that may have far reaching consequences not easily foreseen. Good point.
Thanks for sharing John, I wonder about Hashgraph, not so sure about @alexpmorris hehe :P
I'd probably hurl abuse at you too if you were to profit from making me look bad.
He makes himself look bad acting that way. I just shared the truth, as I saw, no big secret in that. If he disagrees or has issue fine but to the point there is no need to be abusive it just invites negativity.
You make yourself look bad. He takes the time to do an interview for you. To give you value by getting you views and you stab him in the back by trying to ruin his reputation.
I hope your EOS investment sets you up for life so you wont have to do any more backstabby interviews.
Well, you are entitled to form your own opinion. I don't agree with it for a number of reasons but have no qualm giving you the time of day.
Mind you, as the saying goes; looks can be deceiving and don't believe everything you read.
Incorrect, I did not interview Charles (I think you are confusing the hilarious video interview between Charles Hoskinson and @crypt0 (which I linked in my post)
Backstabbing!, also incorrect, Charles (the character in the mentioned Cardano Telegram chat) and I are not friends.
If there is anything else you would like to add, feel free to take this over to my post here and I'll gladly give you more time, I freely, do what I enjoy!
Most people may have a hard time controlling the initial feeling they have when they hear something they consider a verbal attack, but we do have control over how we react. Charles' reaction shows low emotional intelligence.
I like Cardano but I prefer Gina that works in a street close to mine...the problem is that she charges 50 euros....Vanessa charges 20 but she has no teeth
No teeth every time😂
Thank you, Dan, for inventing this tool that allows me to show what I need to the world without being censored. I really appreciate this Alternative Economy and it's an honor to be around so many smart people
Why are you attacking Charles seemingly without provocation?
BTC and BCH people go back and forth but they have legitimate reason to. Maybe I'm just new to the space but I haven't seen any other crypto leaders go out of their way to attack another project. It just looks very catty and immature.
If EOS is really better, then the market will follow eventually. So stop crying like a baby and actually do your job.
Peer review is not catty or immature, nor is creating a discussion based on facts. Reacting to having your hard work used without recognition is completely understandable and actually very necessary.
"Peer review" has a definition and this is not it. Competitors bad mouthing each other in public is only good business in WWE.
If he's genuinely upset at having his work stolen, just focus on proving that point and that's enough to sway public opinion I would think. Having a lecture about 'why I think my competitor sucks' is pretty sad. If I saw a lecture from McDonalds about how KFC's chicken sucks, am I really going to pay attention? If it's really bad, then surely someone besides a direct competitor should be able to point it out.
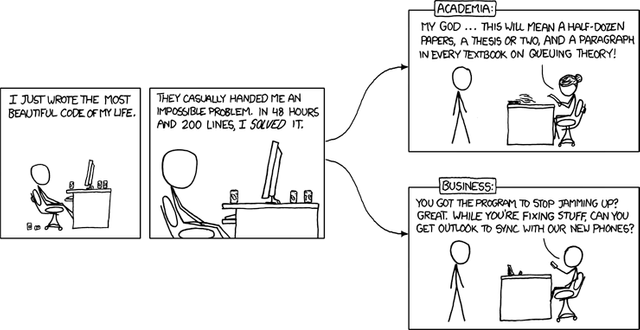
I agree, in the current academic space, far too many individuals ask the questions they can most easily (quickly) and uncontroversially answer. They need one to three papers a year in the right journals to get tenure. Meanwhile, in business, anything longer than three years is accounted as a write off or a hedge. There are almost always less risky investments with same return in most cases.
I suspect most know they are asking the wrong questions. Which does not mean they will ask different questions in the current environment.
Most scientists of the 18th, 19th, and early 20th centuries were independently wealthy. Ludwig Mises said it. Science was something they did because they enjoyed doing it. Result? No rush. More on point.
Alan Kay has a lecture at Carnegie Mellon, where he talks about the important problems in computer science.
Audience: That's great! Super! Now how do we get paid for working on these problems? How do we get paid for asking these questions? The answer, that science and income are different things, did not seem to satisfy the audience. Awkward silence.
I am unsure that we need to use any definition of security. We might take it as something to be solved for in the relevant problem context. We might not need to define our terms in advance. (Wheeler suggested this approach.) We might ask questions about decentralized systems without narrowing scope by using tacit definitions. ("N" is secure if "N interacting with M" is secure when "M" is also secure. That sort of thing.) We discover our proper scope in the relevant problem context gestalt.
By the way, Phys. Rev. E, not Nature, is now the place to look if you are interested in network phenomena, complex systems, etc, what is relevant today.
Thank you dan for the article, and i must say, i like the way how 19th century's scientist think :D
I agree!
Why did you let this dude premine?
No idea how busy you are and if you are aware of this:
https://steemit.com/@rewardpoolrape/comments
https://steemit.com/@eatsrewards/comments
Your old friend went on a crusade to destroy the STEEM blockchain.
I do believe you control either thejohalfiles, or freedom, and your account which still carries quite a clout.
This comment has received a 16.67 % upvote from @steemdiffuser thanks to: @stimialiti. Steem on my friend!
Above average bids may get additional upvotes from our trail members!
Get Upvotes, Join Our Trail, or Delegate Some SP
This pos very interesting to me..I salute of [email protected] visit my post please give me your contribution.thanks@dan.
I understand Charles' point about the benefits of peer review but on some level it just feels like clever marketing for Cardano. Ultimately software is validated and verified through testing. The game theory element of these systems is so complex now that the only way to test that portion is to set it loose and let evolution take place.
So we shouldn't peer review the architecture? Even I have to send my arhitecture plans for a review and I am not creating a multi billion dollar currency.
As I said, peer review has its benefits. Peer review possibly could catch flaws prior to investing a lot of time and money in a project. However, Charles making the assumption that Cardano is the only project that is doing peer review or doing peer review in the only correct way using the particular conference and boards they happen to select and then bashing every other project on the point seems to me more like marketing for Cardano then it does anything else.
No he is also talking about other peer reviewed papers/projects like zcash and others if you ever listen to his talks. Also talks about good things that other coins are doing, like dash treasury model. Also if you dont know IOHK has ETC team and Daedalus will support ETC so they are seeing a lot of potential in other projects. But of course he is trying to raise standards in crypto space. But in the end markets will do what markets do. And who would blame him the standards are awful so many scams and shitcoins.
@dan Good evening. Interesting point from Mr.Hoskinson, and is human nature to make the point he did. This are great times. Yet there's much to be proven, but people like you and others are creating a new road. (hope that makes sense). Best wishes.
You hit the nail on the head dan. Kudos for this.
I wrote so many articles in the past about this backward thinking from academia and why I actually avoid to invest in anything that comes from the space. Indeed, the mentality of the academic space is to find something that fits the narrative.
Most experiments from the space are not falsifiable. Anything goes as long as others have created the shell upon which their assumptions can be based. This is why we see fields like psychology invent disorders at will and an entire medical industry being based on it.
Cardano will fall onto its face and probably find the same excuse as with academia. Extended timelines and waste of resources.