Electroneum Hackerone Ethical Disclosure, and Unethical Practices by ETN Team
Ok, so this is going to be quite a long-winded post. I have several issues to go over, and I am making my full ethical disclosure about my Hackerone report to ETN since the team is making ethically questionable decisions, and calling out bug hunters in an unethical way.
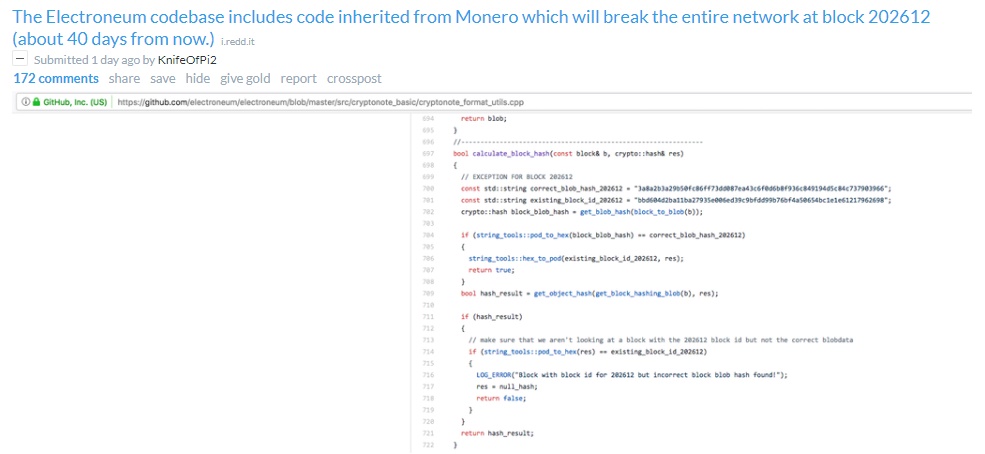
KnifeOfPi2's Reddit Post
KnifeOfPi2 is currently a hero for the ETN community, but due to the Dev's responses, he has been completely vilified. KnifeOfPi2 made a GitHub post to Electroneum's repository, and then a Reddit post to get some action taken. He discovered that there was a major bug in the Electroneum blockchain since they literally just copy pasted the Monero blockchain. At Block 202612 ETN network would cease to work.
The responses on Reddit were what you would expect. A bunch of people discussing the implications, and if it had indeed been fixed or not. The end of short was that the fix had not been implemented, but that the fix does exist. Unfortunately for ETN that means a fork. Now everyone should accept this fork as it fixes a fatal flaw, but ETN is the coin of the people...it is full of noobs, and anyone running the CLI wallet would need to get the new daemon and run it.
From browsing these posts all KnifeOfPi2 really wanted was to bring attention to the Electroneum team so they could fix the issue as it literally had a 40-day timer on it.
Well the ETN community is full of rational individuals who accepted this position, and talked about how to fix it...
...is what I wish I was ending this article with.
Instead the ETN community split, with a bunch of tech informed individuals trying to convince everyone of the validity and the severity, and then the HODL community flipping out calling everyone FUDDERS and that ETN is not that incompetent, and it is it's own blockchain, etc etc...
And the value of ETN tanked...losing almost 150 million USD in market cap and landing at around 9 cents USD...

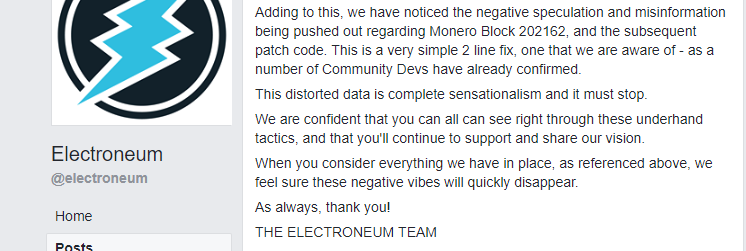
So what does a rational company do? They post on facebook of course! So the first post had a bunch of fluff about how amazing ETN is with the relevant stuff at the end:
Official Electroneum Facebook Flaming Starts
Just wow. Seeing this makes me incredibly uncomfortable being part of this community. This is directly from the ETN Team.
This distorted data is complete sensationalism and it must stop
We are confident you can all can see right through these underhand tactics, and that you'll continue to share our vision.
So instead of praising the Knife, they slam him as spreading sensationalism and using underhanded tactics. When the man just wanted to make the ETN community better. Just wow.
Also the ETN team completely glossed over the fact that this would require a fork, and acts like the 2 lines is no big deal. Forks can always be a big deal. They should be holding everyone's hand, telling them what to expect, thanking Knife, and being possitive. Instead they attack the users who are trying to make things better...
But it gets worse, oh so much worse.
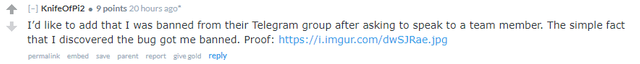
Knife was banned from the official telegram group for trying to contact an admin to advise of the issue.
This is the screenshot from knife, showing he can no longer contribute to the official telegram...
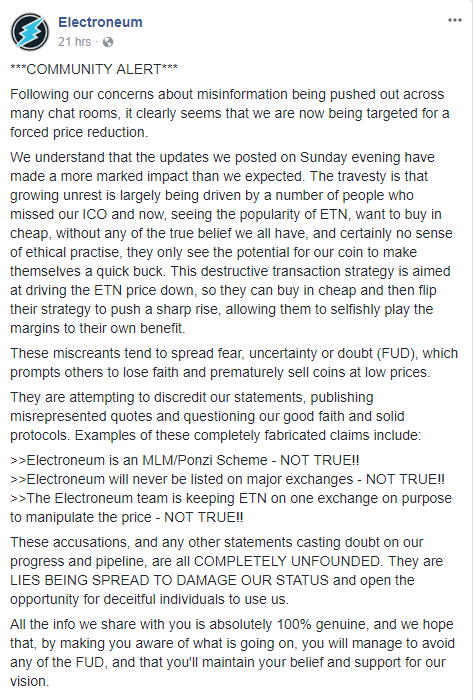
So what is a fledgeling company with a cult like following to do in face of all this contreversy. Double down of Course.
This...This is the one that gets under my skin. This is the one that tied everything together to be fully unethical. This is the Officer Electroneum Post which was pinned in telegram, and posted on facebook attacking bug hunters.
The TL;DR is this. The ETN Team is asserting those bug hunters, and concerned investors are targeting them for a price reduction.
They claim the people upset missed the ico, and is trying to drive the price down to get a better price.
They call bug hunters miscreants, and state that they are spreading FUD to lower the price, explaining what FUD is.
The bug hunters are apparently attempting to discredit statements, misrepresenting quotes, and questioning good faith? Solid Protocols?
I actually agree with the 3 bullet point about whats not true...I don't think ETN Team is being malicious, I think they are just incompetent.
This is the kicker though man, that next paragraph:
These accusations, and any other statements casting doubt on our progress and pipeline are all COMPLETELY UNFOUNDED. They are LIES BEING SPREAD TO DAMAGE OUR STATUS and open the opportunity for deceitful individuals to use us.
What?
again...
WHAT?
They are claiming all statements that may be negative, or concerned about the progress of ETN are lies, and those who post them are terrible evil people. How is claiming bug hunters, and concerned investors are outright lieing in all circumstances rational or ethical?
These guys went off the deep end with this.
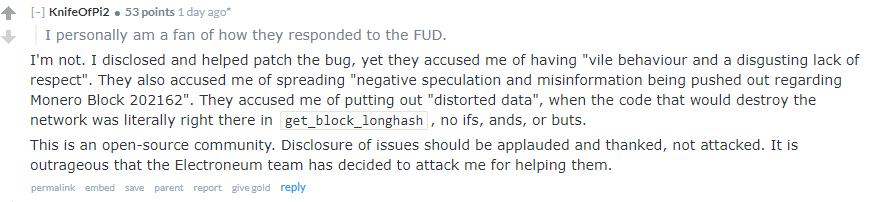
Knife's response:
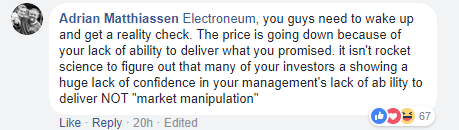
Some Facebooks responses which were immediately attacked by community members as being fud:
Rewind Time
So all of this just pissed me off because I have been waiting since mid November for ETN team to get off their asses, and be honest about the hackerone review. So lets go back in time.
These are the posts from the ETN team about the hackerone process. They claim no issues, and minor bugs have been found, and that no one should be worried. Nothing was compromised, and the marketing dudes with no dev team are trustworthy.
My Hackerone adventure
So a little bit about me. I am not some crazy amazing hacker. Not some crazy in depth programmer. I am a dude with an interest in tech, hardware, and software. I have taken some classes, and have a good sense of infosec. I have played around with pen testing, but nothing profesional. ETN Team announced the bug hunting bounty, and to be honest I ignored it.
Until one night I was sitting around in discord and someone I met on the hashparty channels messaged me and told me he is getting some minorly successful hits through SQL injection on the electroneum sites. Nothing reportable, but maybe a rabit hole worth exploring.
Well SQL injection is google warrior 101 level of penetration testing. So I figured why not lets give it a try. I start poking around with some things with no really promising results. I then decide to do a website scan to see what the site is made of. I had already determined the site was a Wordpress blog...so usually with wordpress its faulty plugins as the vulnerability. So I scan for what pages are live on the site, and their responses.
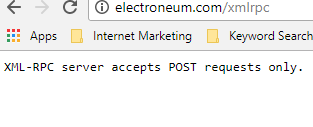
Everything comes back with standard responses, cant find, wont respond, exists and loads. And one page states unable to respond to XML request.
hmmm... Before I continue I want to confirm that this has been patched by the ETN Team through the server, I will show when later with screens, but this is an ethical disclosure. I would never post if it wasnt fixed.
Disclosure Time Baby
Well one thing I do know is if you find a weird error you should look into it because thats where the problem will be. So I go to the website:
and it said:
Well Danile, that doesnt seem like it does anything. How was this relevant or concerning?
I am glad you asked.
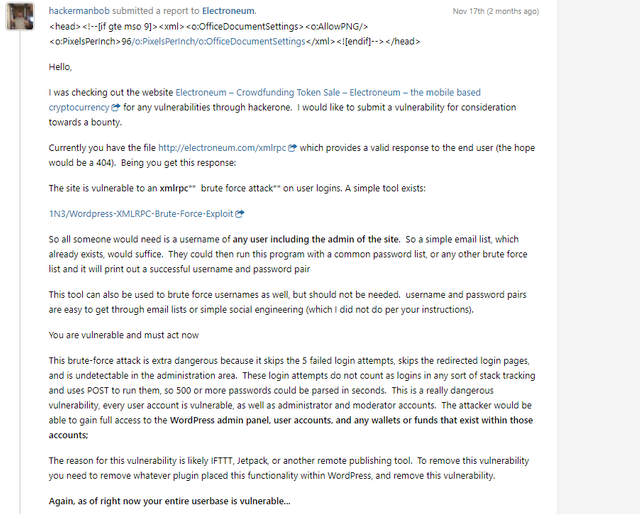
xmlrpc is actually a known exploit in the wordpress system that allows for massive password and username lists to be parsed instantly virtually undetectable, and returns login success or failures. It uses POST to send the credentials and data through to the site for remote posting.
This was removed from the version of wordpress the ETN Team was using...
In order to have it on their site they had to have installed a plugin that renabled and installed the service. Great job ETN Dev Team!
So needless to say I am like daaaaang. Now lets see what we can do. So I load up the exploit onto a VPS and start trying some things.
I start by attacking my username (because yes I am an ICO investor), and 2 usernames I obtained permission to attack from another user in discord. At this point I couldnt remember if the site used usernames or e-mails for login so I tried both. And I found that it actually errored out completely if I used the wrong form. It stated it was an invalid string. Good to know. I tested long usernames that no one would have, and all kinds of stuff, discovering if the username didnt exist it just messed everything up.
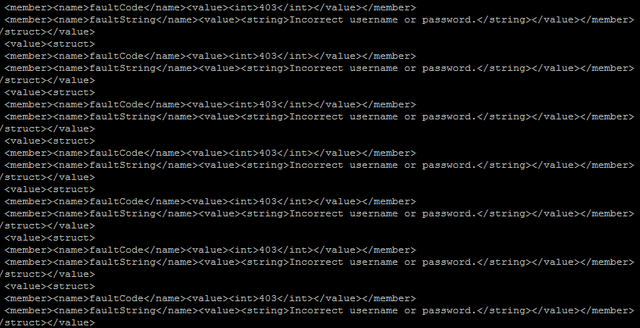
Nex, I loaded the verified usernames that I had permission to attack with a password list that I obtained from some simple googling. And mind you, these are the usernames used to register ICO accounts (super important later) The initial results.
I got a bunch of this. But at least it is connecting and stating incorrect username or password. Lets get a bigger password list...
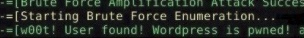
After a while I got this (username and pass left out for security obviously):
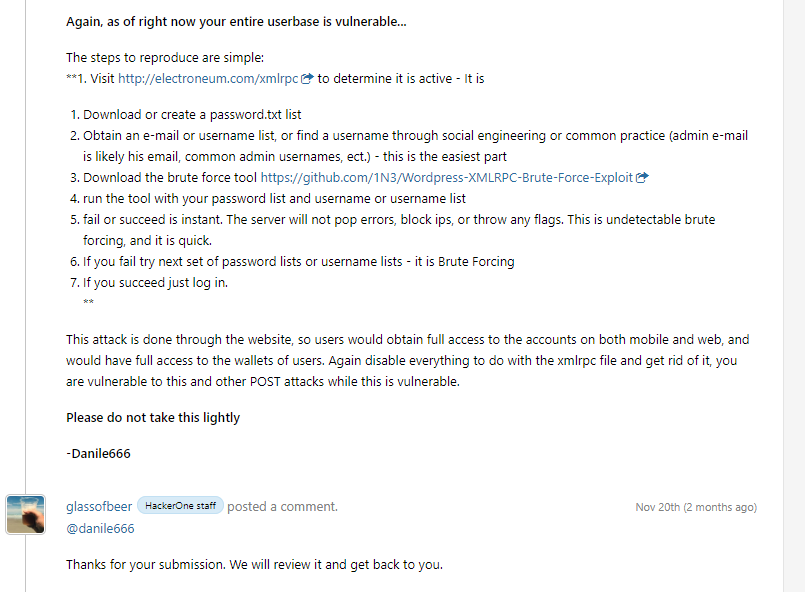
Whew, it works. Ok cool. I played around with it a bunch more, and made a hackerone report to the electroneum private program:
As you can see this report was made November 17th, and responded to on November 20th. This is the last I heard from anyone from hackerone or ETN Team.
I left it alone for a few days, confident I did the right thing. Wondering if I was the first to report it, and if I would get a bounty if I was first (ETN had promised bounties afterall).
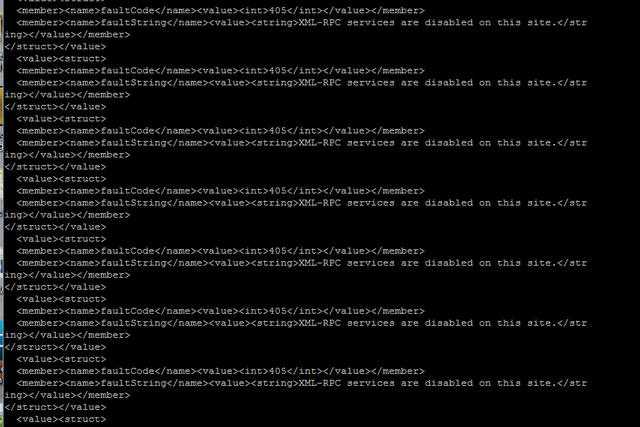
Well about a week later I wanted to see if they fixed it. They hadnt, same results. But the next day I got this result:
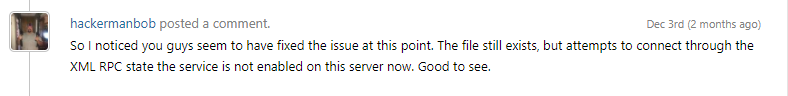
So the page still exists, but ETN employed the Apache fix or the .htaccess fix. Great, I am happy. I msg them again in December to see whats going on with the status:
Still super good news. Their site was compromised, but they fixed the issue. Super proud of myself. Except remember those posts in December above where Electroneum stated nothing major was found...nothing major was found...I could have had the login details to a large portion of the ETN community, including admins of the site, and wreaked all kinds of havoc.
But Electroneum.com is different from my.electroneum.com, different databases so everything was safe?
That is correct NOW
In November that was far from correct. Remember that part when I said these were confirmed usernames used in the ICO? yeah that is relevant here. In November either the database was not attached to the blockchain yet, and the usernames were just plain wordpress users with a variable tracking the amount of ETN to ultimately credit to the wallets (this is very likely given the delay by the way). Or initially the online backend shared database information with the wordpress site. Either way, ICO generated usernames were compromised...thats a big deal.
Why post now?
Because at this point I feel Electroneum is being dishonest and unethical. They should be thanking the hackerone freelance hackers, they should be thanking knife, they should be owning up to their mistakes instead of lieing to the community.
Am I bitter for not recieving a bounty? Look making this post 100% guarantees I will not recieve a bounty. I also may not have been the first to the punch. There is no way to know. But I will let you in on another tidbit of information.
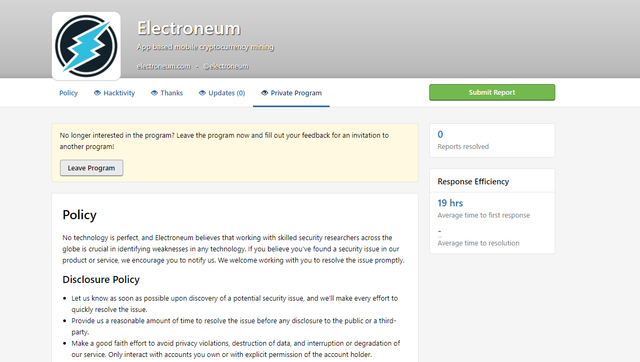
To this date the Electroneum Team has not resolved a single report in their private program. Not one...so no one has been paid bounties. No reports fixed. I cannot have been the only one to submit. So what gives ETN team?
Am I spreading FUD
Absolutely not. I am long on Electroneum, always have been, always will be. But the ETN team needs to step it up, own up to their mistakes, and communicate instead of pretending the fart rainbows all day long. If we are to succeed they need to be completely transparant. Quit lieing, and quit being unethical.
I was an ICO investor. I mined since day 1. I made a killing already and built extra mining rigs to mine etn with my initial profit. I have already mined it all back for longterm hold. I own a business that I started specifically to sell mining rigs to individuals who are uncomfortable building their own rigs.
I have spent countless hours in PM's on facebook, on hashpartys discord channels, and many other avenues simply helping people. Yes I am cautious, no i dont see 5 dollars tommorow, I see a dollar in a year or two. But that is really good for my position, and I only suceed when ETN does. So simply put I am not spreading FUD. I am disclosing because I feel ethically obligated to so maybe ETN Team will start doing the right thing, be transparant, and honest going forward.
Do not call out bughunters and investors as unethical and malicious, dont throw fits against your community. Simply embrace them. Thank them. Work with them. Explain the steps you are taking to correct the issues found. Instead of crying FUD.
Now this topic is really close to my heart. So please resteem it, and repost on other social media platforms so we can really get it out there.

Hi @danile666 I just read your entire post, which I do have to say was extremely detailed n clearly truthful as you’ve backed up your statements with actual facts. I’m also an ICO investor and can vouch that your time line is spot on. Unfortunately, this was my concern over the past coming weeks as we’ve continued to receive all this great “positive” news via FB about new exchanges, mobile mining being released, etc. However as the weeks begin to pass its beginning to remind me more of the ICO release again as they’re once again falling to stand behind their word and we’re instead left with nothing but empty promises and a longer wait. However, I’m with you and only gain by the price of the coin rising, not falling as I haven’t sold any of my initial coins. Although that outlook is starting to appear bleaker and bleaker as what you’ve just outlined complements my underlying concerns I’ve been having. Thanks for taking the time to let the truth come out. I’m sincerely hoping they can start to turn it around here in the coming months ahead!
For sure man, thanks for the kudos. I do believe the coin itself will recover in spite of the team. The community is huge and ever expanding. So this can go forward but the team needs to calm down.
Thats my concern at the present time. What price will this recovery come with? Will it mean a split in community as well as the coin comes to a fork as has been the case with bitcoin historically. ETNs large community following and support has been by n large it’s greatest asset to date as the team continues to make promises but doesn’t fulfill until weeks if not months later
No because the old blockchain just wont work, but there will be a lot of confused individuals who do not understand why their cli wallets no longer work.
Right but if they keep acting like everything is all good, rainbows and butterflies without addressing the problem at hand ETN will start to stand for Empty promises That go Nowhere
This post must be in trending page , from start to end you covered everything here . Etn needs to hire more devs .
lol, thanks for the confidence. Get it voted up and resteem it!
that's pretty cool to know....
Upvoted dude , Etn was in a big trouble . Fork it , save it .
They need to be upfront about the fork though man. Tell people, make guides, thank knife. work through it. Don't flame your bug hunters.
It’s only a soft fork, not an HF - no new chain will be created by this fork. The old chain will just stop working anyway.
But people still need to update their daemons.
Damn !!!! I have seen some youtube videos on it , nobody explained it in this much detail . Make a youtube video on it asap mate ! This needs to go viral .
We may or may not do a stream. Just letting stuff filter right now. Shit is fucked. Also I do not know if i have a large enough following to get it to go viral. We will see, but it is definately messed up.
Video will be out tommorow. ill link it when it is.
cool , do post it !
Well it is fucked but why not try and take advantage of the BS??
Because I am long on the position, and want it to suceed. I figure if we can get the etn team to pay attention and change their ways we can make profit on this...
My thinking is that if HackerOne works with a coin company that ends up beign a scam or failing for other reasons, their company will be associated with that failure. I can't speak for everyone but personally if that were the case and I ever saw that HackerOne was working with a new ICO, I would assume that to be a scam as well. So, ICOs would choose not to hire HackerOne so as to avoid investors thinking they're just another scam @danile666
So here is where the misunderstanding about hackerone comes into play. I think ETN just didnt know what they were paying for. Hackerone is really just a platform for freelancers to pentest company sites for bounties. So they put up the bounties, theirs ratings, and everything. I have no real reputation on hackerone, but my making this post kinda ruins any chance of a reputation. The ETN team just needs to step it up, quit blaming others, and get this stuff sorted.
Very good read Sir and sadly so much of it rings true. I never had the opportunity to invest in the ICO but I did Buy into ETN at an early stage. As a newcomer to the crypto world with not a lot of spare money Electroneum through buying and mining soon became by far my largest holding albeit a modest 10,000.
As time has gone by I have found it hard to understand some of there actions or in actions of late.
Exchanges or the lack of exchanges for me is a very strange one. I know It can cost a lot of money to get listed on an exchange but surely there is no lack of that after the ICO, I understand Exchanges must want to list a coin but surely there is more than one considering the amount of volume ETN would bring with out. So many coins release everyday and many of which are already on multiple exchanges so why not ETN.
( FUD ALERT )
The only reason I can imagine is they may have signed a deal with Cryptopia giving them exclusive access for a period of time but if this was the case just tell the community so everyone knows where they stand. If this is not the case ,,, well, the only others reasons I can think of don't stand the ETN in good light.
My main reason for getting behind Electroneum from the start was the fact they with bringing something new to the Crypto game something not seen before with any other coin. MARKETING! marketing to the masses and they started of very well indeed. But sadly there effectiveness at communicating with the community of late has seriously diminished.
Hopefully they will turn it round soon and address all the issues raised one way or another.
Mark
Well said, I hope they just step it up and start owning their mistakes, and talking about how they are correcting individual problems as they come up.
Also I see shitcoins pop on major exchanges daily right after ico. So there is no reason for this delay. They have something else going on there, and I am not sure what.
Also a negative opinion is not FUD. FUD is making shit up to manipulate the market. That is whats wrong with the ETN Team officially claiming anything negative is a lie and FUD.
Hello. I’m Knife.
Thank you for this post. I’d like to add that Richard Ells sent me an e-mail yesterday thanking me for my work, offered to make a Facebook post correcting the record, and then ignored my response. It looked like they were getting better, but their unethical behavior just continues.
The man himself. I appreciate the reply and feel for your plight man. Hopefully we can correct the team's behavior through some public disclosures.
Hey knife, I am currently making a video about this and would love it if you could get in touch and maybe do a short skype call so we can talk about this. Would you be interested? Also, thanks for your work disclosing the bug.
I’d be willing to speak over text, but skype would be off limits until I trust you.
Thats not a problem. I made and posted the video already today but I would be interested in following up with you because I left a lot of things out and it seems that this is still evolving. You can find my video about it here: https://steemit.com/cryptocurrency/@personanongrata/the-troubling-case-of-the-cult-of-electroneum
While I understand where you are coming from, I do not understand why after he thanked you, you are now expecting him to reply to you right away. I think it was good that he thanked you. But try to not expect him to reply to you immediately. He is a CEO, busy, and has a lot to deal with. You are not suddenly his only agenda in the day. He may probably reply to you when time is right.
I also think ETN team/ CEO did well by thanking you because they had already known about this issue since about 2 weeks ago when NEXT Exchange notified them about this block issue. You can verify this if you contact the Next dev team or if you look over the Next telegram group where there was already a talk about it. That is why NEXT delayed their exchange launch as well. However, ETN team is just slow, very slow.
Also, Richard had already mentioned about this block in one of his earlier videos last year, maybe that's why they didn't think it's a big deal and decided to thank you anyway.
Otherwise, I personally thank you for bringing this up to the public since it'd speed up the fix.
I resteemed. I got a few ETN in the ICO. I am still hodling but I would like to see more action from the team. Thank you for the awesome post.
You’re not alone @joeyknowsbest!
And I think this is the issue. Be upfront, honest, and move us forward.
More than ever, ETN team really need to actually get their coin on other exchange. I can see amateur miners moving to other coins like DCY or SUMO in the next two weeks if the price is not moving upward
I agree, also sumo is reguarly more profitable to mine than etn right now...i just hate the network and pools so i stay away from it.
This is so great! You got the great point here dear
What's wrong with the pools?