Why software wallets can never be secure and what to do about it
We made a mistake in the architecture of the internet in the early 90’s by not encrypting communications on the base TCP/IP layer. The result is that the IoT is building communications on the metaphorical equivalent of post cards (as Andreas Antonopoulos once said, “The S in IoT stands for Security). All information is on the outside of the envelope for everyone to see.
We try to fix this with VPN’s and TOR and use SSL, but while that prevents MitM attacks, it is not enough. This is not the way most hackers operate any more. Most typically you pick up trojans which are sniffing protocols that download to your machine when you visit a compromised website, then that malware operates as a keylogger and takes screen shots of important password/key generation events sending it back through the connection to a data source the hacker then monitors.
You have to understand that hackers are typically very smart. They will infect a machine and sit back and watch that machine for months and even years before striking. John McAfee explains this very well…
You can use tools like WireShark to inspect anomalous activity. One thing that I do is set up fake password files and then monitor access to those files. Name them something like passwords.txt in the root directory of your user documents folder and if you see access to that file in WireShark you can't explain, beware. I also use a tool called Zemana Antilogger on my Windows machines.
Zemana works by encrypting your keystrokes so that what’s sent back is gibberish. Some antispyware such as MacScan will detect if you have a keylogger on your system and disable it.
Unfortunately banking systems and centralized data structures will always be fatally flawed. The way to reduce risk from such things as the Equifax data hack is to decentralize collection of data back to the source forcing hackers to use botnets which is more difficult. This requires that machines be online at the time of a hack and many machines go offline from time to time. This reduces hacker rewards and incentives.
The answer to hacking isn’t more authority, but less of it. This is the correct way to build secure systems:
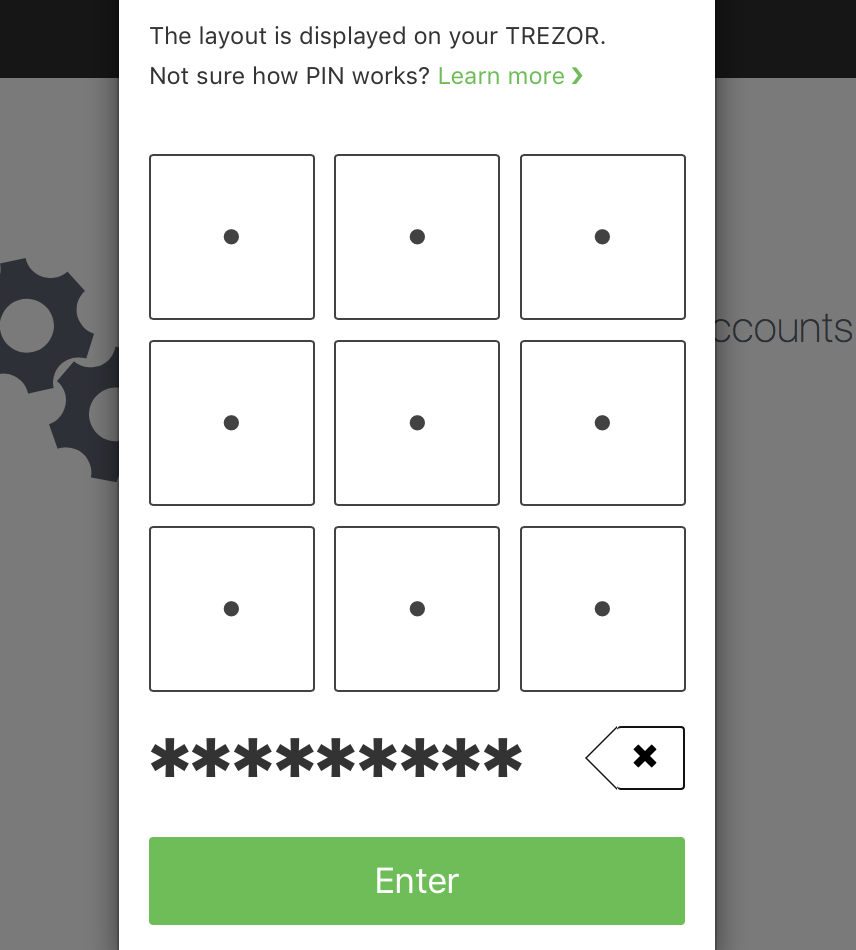
The best solution at this point is to use bitcoin or another cryptocurrency with a hardware wallet such as Trezor or Ledger S Nano. That way when a keylogger or malware takes a screen shot, the phrase is displayed on your device, but not on screen and looks like this:
One day, when bitcoin has reached 1 million / coin, a hacker will strike and wipe out wallets all over the world by stealing your keys. Don’t become a victim.
Donations (public bitcoin address):

3FwxQsa7gmQ7c1GXJyvDTqmT6CM3mMEgcv

Mobile devices are much more risky than desktop PC imho. If you're gonna keep any crypto on a mobile, make sure it's small amount just needed for spending on a daily basis.
Useful and valuable post. Its value resides in the money that can be saved. I'll take action with your advice :)
Very useful, thanks for the links. Upvoted and following.
Security compromised now, compromises security in the future.
Hackers can remain dormant, and even after upgrading your security will have access to your information.
The McAfee video is incredibly interesting and well informed, thank you.
@mrainp420 has voted on behalf of @minnowpond.
If you would like to recieve upvotes from minnowponds team on all your posts, simply FOLLOW @minnowpond.
This post has received gratitude of 3.34 % from @appreciator thanks to: @zoidsoft.
This post has received a 15.44 % upvote from @boomerang thanks to: @zoidsoft
@boomerang distributes 100% of the SBD and up to 80% of the Curation Rewards to STEEM POWER Delegators. If you want to bid for votes or want to delegate SP please read the @boomerang whitepaper.
This post has received a 1.67 % upvote from @buildawhale thanks to: @zoidsoft. Send at least 1 SBD to @buildawhale with a post link in the memo field for a portion of the next vote.
To support our daily curation initiative, please vote on my owner, @themarkymark, as a Steem Witness
This post has received a 2.41 % upvote from @booster thanks to: @zoidsoft.
Hello @zoidsoft, maybe you are the right man to ask. Could you please look at the following post and maybe you have an idea how it is possible to steel all my cryptos from my wallets? Can a trojan read a textfile from an usb flash drive, that is only sometimes connected with my computer? https://steemit.com/bitcoin/@sevenseals/need-help-all-my-bitcoin-and-ethereum-have-been-stolen-from-my-ledger-and-jaxx-wallet