FBI REBELS? Leak Hillary Clinton's Missing Emails Were Offered To JOURNALISTS & Darknet For $500K; Given To FBI Covered Up
This writer was sent a link dump detailing that Hillary Clinton's emails were hacked and for sale on the darkweb, offered to journalist for 500K several times then removed and sent to the FBI. The source also expanded on the accusations that Russia hacked the U.S. election, calling into question the veracity of cyber security firm Crowdstrike's accuracy and whether its Ukraine that interfered with the U.S. election.
In an amazing revelation a source has revealed and detailed several key pieces of evidence of the Clinton email investigation, Clinton's server was indeed hacked in 2013 and beyond during her tenure as Secretary of State.
This not only contradicts FBI director James Comey's statement stating there was no "direct evidence" that her home-brewed closet server "was successfully hacked," showing a cover up, but it also provides a basis that her server was so vulnerable that anyone with a bit of computer knowledge could have "hacked" it from inside their own basement since Remote Desktop Protocol (RDP) and VNC (virtual network computing) ports were open according to The Register.
"Clinton's server was very insecure, as has been said in the past by the media, its software wasn't even up to date and this caused conflicts with the State Dept server. This recklessness of not maintaining the server caused State Dept. employees to have to disable security features on the governments' own server just for Clinton's server to communicate with it. Which undoubtedly in my mind, opened government property to an array of attacks this is the tenacity of the cover up," the source wrote linking to their claims.
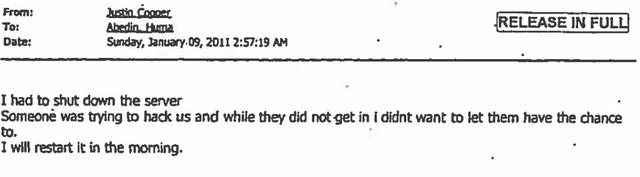
The Associated Press admitted that a set of Clinton's emails released by the State Department showed the government agency had to disable several security processes on their servers just to get it to accept email from Clinton's private email address. Another email reveals that Clinton's server was attacked 10 times and had to be shut down Judicial Watch documents revealed.
All it would require is just knowledge of how to connect to the server through RDP or how to exploit software installed on the machine that's outdated, so any script kiddie could have connected to the server downloaded any files and left without a firewall or any security measure in place.
No infamous media moniker "Russian hackers" that "hacked" the DNC needed, since Clinton's server was open to anyone in the entire world its the equivalent to leaving your front door wide open for robbers to come in and take whatever they want from your house and then leave.
"AK the Ukrainians interfered with our election more than Russians did," the source said in an email linking to majority of the material below.
DNC AND CROWDSTRIKE:
Onto the DNC and somethings to state then back to Clinton's emails. To put the nail into the coffin to Crowdstrikes' dangerous conspiracy that another nuclear power Russia hacked the U.S. sanctioned election and interfered in our democratic process without a significant iota of evidence to back their claims.
A question everyone should ask themselves, is how did the NSA not capture the packets leaving the U.S?
Even past intelligence veterans apart of VIPS or Veteran Intelligence Professionals for Sanity have stated the NSA would have caught an outside breach questioning the official narrative if the newly reborn Soviets hacked the DNC. It's cold war 2.0 mockingbird propaganda, without any conclusive evidence provided and its falling apart at its seams fast.
Those intelligence professionals include - William Binney, formerly the NSA’s technical director for world geopolitical and military analysis and designer of many NSA programs now in use; Kirk Wiebe, formerly a senior analyst at the NSA’s SIGINT Automation Research Center; Edward Loomis, formerly technical director in the NSA’s Office of Signal Processing; and Ray McGovern, an intelligence analyst for nearly three decades and formerly chief of the CIA’s Soviet Foreign Policy Branch.
"Forensic investigators, intelligence analysts, system designers, program architects, and computer scientists of long experience and strongly credentialed are now producing evidence disproving the official version of key events last year," the nation wrote.
Further it doesn't end there and its just the beginning, the so called "cyber security" company Crowdstrike which has anything but a pristine record also claimed the hacking of Sony in 2014 was done by North Korea which was also based on flimsy evidence according to wired.com.
Marc Rogers director of security operations for DEF CON, the world’s largest hacker conference, and the principal security researcher for the world's leading mobile security company, Cloudflare wrote a report on the evidence and why its not conclusive for The Daily Beast.
A hacker known online by his alias Space Rogue revealed to business insider how vulnerable Sony's network was.
"The problem with that one is that the Sony network was documented Swiss cheese," Cris Thomas said.
The website Attrition.org has documented at least 24 hacks into Sony properties since 2011.
Then there is the case where the CrowdStrike may have completely fabricated an attack in the Ukraine blaming Russian hackers specifically their favorite "Fancy Bear."
Crowdstrike reportedly "misread" data, falsely attributing a hacking attack in Ukraine to Russia in December 2016. Voice of America, a U.S. Government funded media outlet, reported, “the CrowdStrike report, released in December, stated that Russians hacked into a Ukrainian artillery phone application, resulting in heavy losses of howitzers in Ukraine’s war with Russian-backed separatists. But the International Institute for Strategic Studies (IISS) told VOA that CrowdStrike is erroneously using IISS data as proof of the intrusion. IISS disavowed any connection to the CrowdStrike report.
What's more even Ukraine’s Ministry of Defense claimed the "combat losses and hacking never happened.”
Finally the last marble fell and the maker of the military app that was allegedly "hacked" called CrowdStrike’s report “delusional,” and told VOA that CrowdStrike never contacted them either before or after they completed their report.
Something that all these organizations and the FBI have in common CrowdStrike never contacted them after they were done their report.
So how did CrowdStrike's story originate? According to a PBS interview Dmitri Alperovtich stated, "Ukraine artillerymen were targeted by the same hackers who were called Fancy Bear, that targeted the DNC, but this time, they were targeting their cell phones."
" DMITRI ALPEROVITCH, CrowdStrike: Well, this is an interesting case we’ve uncovered actually all the way in Ukraine where Ukraine artillerymen were targeted by the same hackers who were called Fancy Bear, that targeted the DNC, but this time, they were targeting their cell phones to understand their location so that the Russian military and Russian artillery forces can actually target them in the open battle.
JUDY WOODRUFF: So, this is Russian military intelligence who got hold of information about the weapons, in essence, that the Ukrainian military was using, and was able to change it through malware?
DMITRI ALPEROVITCH: Yes, essentially, one Ukraine officer built this app for his Android phone that he gave out to his fellow officers to control the settings for the artillery pieces that they were using, and the Russians actually hacked that application, put their malware in it and that malware reported back the location of the person using the phone.
JUDY WOODRUFF: And so, what’s the connection between that and what happened to the Democratic National Committee?
DMITRI ALPEROVITCH: Well, the interesting is that it was the same variant of the same malicious code that we have seen at the DNC. This was a phone version. What we saw at the DNC was personal computers, but essentially, it was the same source used by this actor that we call Fancy Bear."
In another article published by WaPo Alperovitch stated:
“The Fancy Bear crew evidently hacked the app, allowing the GRU to use the phone’s GPS coordinates to track the Ukrainian troops’ position. In that way, the Russian military could then target the Ukrainian army with artillery and other weaponry. Ukrainian brigades operating in eastern Ukraine were on the front lines of the conflict with Russian-backed separatist forces during the early stages of the conflict in late 2014, CrowdStrike noted. By late 2014, Russian forces in the region numbered about 10,000. The Android app was useful in helping the Russian troops locate Ukrainian artillery positions.”
If you want to go further Crowdstrike's CTO and co-founder, Dmitri Alperovitch, is a senior official at the Atlantic Council, a think tank with openly anti-Russian sentiments that is funded by Ukrainian billionaire Victor Pinchuk, who donated at least $10 million to the Clinton Foundation. Alperovitch has even vetted speeches for Hillary Clinton about cyber security issues in the past.
Not only is it a conflict of interest for CrowdStrike to investigate the DNC hack because of ties to a candidate at the DNC but if CrowdStrike is working for Ukrainian Intelligence and is providing intelligence to U.S. Intelligence Agencies is it a conflict of interest?
Cyber security expert Jeffrey Carr called the FBI/Department of Homeland Security Report, the only known "alleged evidence" released by intelligence officials, released in late December 2016 a “fatally flawed effort” that provided no evidence to substantiate claims that the Russian government conducted any hacks against the DNC.
“If the White House had unclassified evidence that tied officials in the Russian government to the DNC attack, they would have presented it by now. The fact that they didn’t means either that the evidence doesn’t exist or that it is classified,” Carr wrote in a Medium post on December 30, 2016, shortly after Crowdstrike claimed the Ukraine military was hacked.
“If it’s classified, an independent commission should review it because this entire assignment of blame against the Russian government is looking more and more like a domestic political operation run by the White House that relied heavily on questionable intelligence generated by a for-profit cyber security firm with a vested interest in selling ‘attribution-as-a-service,'” Carr added.
The "Russian malware" is actually Ukrainian public PHP malware called Grizzly Steppe and outdated not even private malicious code according to Word Fence which analyzed the sample DHS/FBI provided.
"The IP addresses that DHS provided may have been used for an attack by a state actor like Russia. But they don’t appear to provide any association with Russia. They are probably used by a wide range of other malicious actors, especially the 15% of IP addresses that are Tor exit nodes. The malware sample is old, widely used and appears to be Ukrainian. It has no apparent relationship with Russian intelligence and it would be an indicator of compromise for any website," Word Fence wrote.
“Intelligence agencies do not have specific intelligence showing officials in the Kremlin ‘directing’ the identified individuals to pass the Democratic emails to WikiLeaks.”
With Veteran officials disputing that the DNC was hacked and the malware being shown to have been public outdated PHP code former UK Ambassador Craig Murry’s admission of being involved in a conduit to pass the “leaks” should be looked at. “Now both Julian Assange and I have stated definitively the leak does not come from Russia," Craig Murry wrote.
In addition to Murry the statement made by legendary journalist Seymore Hersh that "Seth Rich had a dropbox with emails on it and was trying to sell them," also needs further investigation.
[RELATED: Cassandra Fairbanks Breaks Several New Leads In The Seth Rich Case]
Finally, the last point ill make about CrowdStrike is Alperovitch used to be in charge as VP of threat research with McAfee.
In December of last year, even his former boss John McAfee stated the report that Russia hacked the DNC was a “fallacy,” explaining that hackers can fake their location, their language, and any markers leading back to them. As Wikileaks revealed with its infamous Vault7 series in March only three months later proving the CIA had the capability to fake malware source code.
Through a project code-named ‘Marble’, which details CIA hacking techniques and how they can misdirect forensic investigators from attributing viruses, trojans and worms to their agency by using the source code of other languages, exactly as McAfee said.
Any hacker who had the skills to hack into the DNC would also be able to hide their tracks, McAfee said:
“If I was the Chinese and I wanted to make it look like the Russians did it, I would use Russian language within the code, I would use Russian techniques of breaking into the organization,” McAfee said, adding that, in the end, “there simply is no way to assign a source for any attack,” McAfee said to Larry King RT reported.
EMAILS:
Back to Clinton's emails, her server was breached in 2013, through the darknet application proxy software TOR or The Onion Router an IP exit-node address showed according to the FBI. This time it wasn't her account that was breached it was a staffer of Bill Clinton.
Further, Clinton herself admitted to a confidant that she suspected she had been hacked according to her top aide Huma Abedin. She reiterated that thought during a private speech transcripts published by WikiLeaks revealed.
“We were attacked every hour of every day and not only through the State Department system, but also through individual, personal accounts, just really fishing for anything they could get,” Clinton said in a private speech to employees of Deutsche Bank AG.
Maybe that's why one of Clinton's aides told a Platte River Networks employee "Clinton didn’t need access to emails older than 60 days so the retention policy should be changed according to an FBI report.
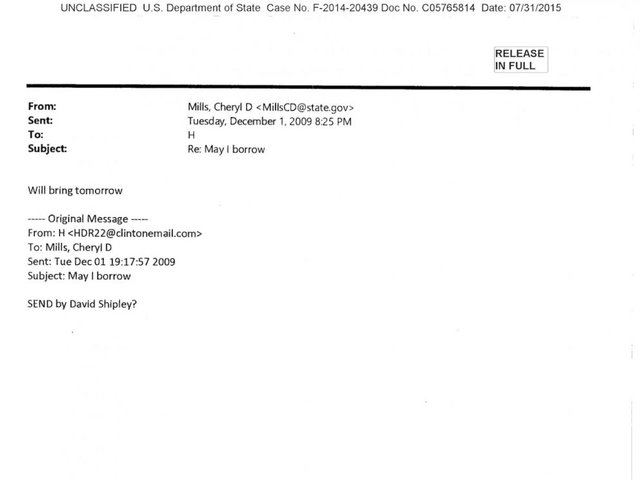
Then Bleachbit was used by Paul Combetta to wipe it clean and Clinton joked "wiped it you mean with a cloth or something" when referring to her bathroom server. Maybe that's why she read the book by David Shipley “Send: Why People Email So Badly and How to Do It Better," which discusses how to safely delete emails.
Despite this then director Comey stated in the FBI press release "we found no evidence that any of the additional work-related e-mails were intentionally deleted in an effort to conceal them" probably because the immunity deals stopped further investigation. If smashing blackberries and laptops isn't intent to conceal then what is?
Fear of investigation perhaps that's why Hillary joked years prior about not using email to actor Peter Paul stating:
"As much as I’ve been investigated and all of that, you know, why would I —- I don’t even want -— why would I ever want to do e-mail?" Clinton is caught on tape telling Paul on home video captured at a fundraiser event.
Clinton was trying to dodge FOIA request as she did when she was first-lady with the Email Gate X scandal before last year's email debacle. During the Project X Email Scandal, career White House staffers and contractors found that someone close to the first lady had basically turned off the White House’s automated email archiving system resulting in more than 1 million subpoenaed emails never released.
[RELATED: OBSTRUCTION OF JUSTICE: The Clintons’ Long History Of Losing Documents]
In one email released last year, the State Department's IT person explains the agency already has an email address set up for Clinton, but offers to delete anything contained in it -- and points out that using the State Dept. address would make future emails subject to FOIA requests.
This email according to my source completely destroys the lie that no one in the State Dept knew about Clinton's private email address activities. State employees interviewed by the FBI did not know she had a private server, the FBI said. (See page 13.)
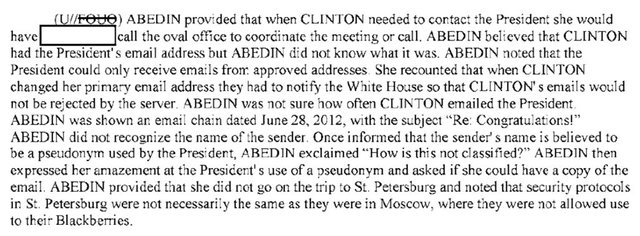
The FBI report also noted that when Clinton changed her email address she had to notify the White House so she could email former President Barack Obama and not have her messages rejected proving her server was known as Clinton stated.
Additionally, I find it extremely hard to believe no one in the NSA/CIA discovered Clinton's emails for sale on the deepweb and that journalist were being offered them for half a million dollars for several years. Some how, with all the software and technology that Edward Snowden revealed they didn't know the DNC was being hacked for months by those pesky Russkis or that Clinton's server was a private server not authorized by the State Dept? That server still made request to and from the State Dept and was visible to any IT professional yet its existence was unknown for her tenure?
According to the Washington Times reported in 2015 Clinton's missing emails were for sale on the darkweb for "several years" leading up to her 2016 election campaign.
The mysterious hacker who offered journalists Clinton's missing emails and tried to sell them on the darkweb had a sudden change of heart and turned them over to the FBI according to Radar Online.
"If these emails get out to the public domain, not only is Hillary finished as a potential Presidential nominee, she could put our country’s national security at risk,” an insider told Radar Online.
The Canadian Free Press noted that Radar Online is primarily a celebrity-driven website and that “They have a solid track record when it comes to being right about the things they publish, but political reporting about presidential candidates is not their forte.”
Was this the original Guccifer Marcel Lazăr Lehel who hacked and tried to sell Clinton's emails or another rogue political hacker and a new character to add to the mix of the mystery?
In 2013 it could have been Guccifer before he was arrested in his home country of Romania in 2014 for hacking local politicians.
Hacking attempts against Clinton’s private email server increased sharply after the New York Times revealed its existence on March 2, 2015. The cyber attacks were targeted against the server, an associated domain controller, and Clinton’s Apple iCloud account, the FBI stated.
Guccifer did admit to hacking Clinton's server which Comey later alleged that Guccifer had lied.
I some how find it hard to believe that a hacker who got into dozens of accounts prior including Sidney Blumenthal's email account and George Bush Jrs. lied yet alone couldn't breach such a weak server in terms of security.
"Clinton had an AOL-based account that she used as well a lot of people don't know of existence of this account," the source claimed citing the Radar Online link.
She also was operating - [email protected] and [email protected] at different time frames.
Then there is the GOP operative Peter W. Smith, who sought Clinton's emails and said he "discovered five groups of hackers two of which he alleged were Russian, on the darkweb that had copies of all 33,000 Clinton emails," he claimed. Smith unsure of the authenticity of emails hackers eventually did send them to him and he told them to pass them on to WikiLeaks.
Smith was then found dead in a hotel near Mayo Clinic on May 14, according to death records from Olmsted County, Minnesota before receiving the documents and wrote his own death note that he had taken his own life due to "medical difficulties and an expiring health insurance plan."
In September of last year, the Intelligence Committees in both the House and Senate claimed they possessed the so-called “Russian files” consisting of Clinton emails that ended up on ‘Deep Web allegedly by hacking a server setup by Guccifer in Romania. The FBI later confirmed the existence of this server and the files contained on it in the fourth part of its report on Clinton's email scandal.
Something to note is that Smith has a history of going after the Clintons and was one of the main forces behind the Trooper gate scandal which stemmed from accusations that Bill Clinton was sexually harassing women according to four state troopers who served on his security detail when he was Governor of Arkansas.
Clinton wasn't charged for her negligence despite an abundant amount of evidence that she intentionally broke the law willingly kind of like Marc Rich. Which the FBI leaked documents between fugitive Marc Rich and Bill Clintons pardon.
Clinton gave her aides direct instructions to remove classification tags - copy, then send classified materials and told her maid to print out classified information. Proving she knew that "C' was for classified not a subset showing a thread of emails as she claimed.
In the email exchange between Clinton and staffer Jake Sullivan from June 17, 2011, Clinton advised her aide on sending a set of talking points by email when he had trouble sending them through secure means.Part of the exchange is redacted, so the context of the emails is unknown, but at one point, Sullivan tells Clinton that aides "say they've had issues sending secure fax. They're working on it."
Clinton responds, "If they can't, turn into nonpaper w no identifying heading and send nonsecure."
The keywords are "no identifying heading and send nonsecure."
"Abedin Clinton's top aide regularly forwarded classified government emails to her serial sexting spouse Anthony Weiner so the disgraced former pol could print them out for her, Comey testified at a Senate Judiciary Committee hearing.
That must all be the "extremely careless in their handling of very sensitive, highly classified information," that Comey cited.
Here's one more according to the FBI's final report of the Clinton's case all the employees at Platte networks had access to Clinton's server and in turn classified information they weren't authorized to view.
Adding onto everything else the FBI reportedly agreed to help in the destruction of evidence by offering to destroy the laptops of Hillary Clinton's aides Cheryl Mills and Heather Samuelson as part of immunity deals offered during the investigation into Clinton’s use of a private email server when she was secretary of state.
In October of last year, the Republican chairman of the House Judiciary Committee wrote a letter to Attorney General Loretta Lynch asking why the DOJ and FBI agreed to the terms, after "finishing their search of the devices."
“Like many things about this case, these new materials raise more questions than answers,” Committee Chairman Bob Goodlatte, R-Va., wrote in the letter.
Fortunately we learned that none of that evidence was destroyed and agents refused to break the law and commit obstruction of justice through destruction of evidence despite that they were ordered to do so according to Washington D.C. attorney Joe DiGenova.
Weiner's computer was discovered later in the case and allegedly had 10,000 emails in a file entitled "life insurance."
What was Abedin and Weiner keeping evidence of on their jointly shared laptop, blackmail and life insurance against whom? Why was Abedin printing out classified information? Just another two questions that need to be answered in this long saga.
So how former FBI Director James Comey and others can stand up and lie and state "there is no evidence anyone hacked Clinton's server," or "no evidence of intent" to commit a crime. Is honestly mind blowing and a perversion of the justice system when there is a huge hidden mountain of evidence, just building up being ignored by the authorities and suppressed, that used to be a crime called aiding and abetting in obstruction of justice?
What's worse is agents rebelled within the FBI and included cases of hacking in their report on Clinton's reckless mishandling of classified information contradicting their director noting the server was scanned multiple times and a [redacted] Bill Clinton staffer was hacked. Agents also stated anonymously that at least five foreign intelligence agencies breached Clinton's server.
That may be because many viewed Comey like a corrupt dirty cop during the investigation according to several personal and online sources.
"We will bring down the Clinton crime syndicate with a new chief, all this past evidence I provided you is enough to prove former FBI director James Comey had enough material to indict Clinton on, but he failed to act. Instead, he claimed that "no reasonable prosecutor would bring charges" against her and helped the case fail then re-opened it a mere 11 days before the election. Only because he was forced by career agents, who threatened to quit after finding new emails that suggested pay-to-play activities by the former Secretary of State. Don't believe me, believe former assistant FBI director James Kallstrom and Judicial Watch who have documented the rebellion going on here and the DailyCaller. Despite, that the press has reported senior agents were confused when Comey was fired, it was quite the opposite, many of us, former and current saw a glimmer of hope with a new director. Who wouldn't tell us to stand down from doing our jobs allowing us to serve our sworn oath we gave to the American people to protect the rule of law," the source said, words were rewritten and changed around for anonymity obfuscation purposes to prevent speech analysis.
“I know that inside the FBI there is a revolt,” former U.S. attorney Joseph DiGenova told The American Spectator.
“There is a revolt against the director. The people inside the bureau believe the director is a dirty cop. They believe that he threw the Hillary Clinton email case. They do not know what he was promised in return. But the people inside the bureau who were involved in the case and who knew about the case are talking to former FBI people expressing their disgust at the conduct of the director,” he stated
While Judicial Watch collaborated his statement reporting that retired and actively serving FBI agents told them that "Comey is a Dirty Cop."
As the whistleblower stated to me linking the following link, former assistant FBI director James Kallstrom did indeed state in the past during an interview that the Clintons are a “crime family." As has been alleged in the documentary "The Clinton Chronicles" by many others including Larry Nichols who worked at ADFA (Arkansas Development Finance Authority) bank during the years of the Whitewater land scheme.
Former NSA employee and whistleblower Edward Snowden has said anyone caught doing what Hillary did would face prosecution in fact someone in the U.S. Navy was charged and later sentenced for possession of classified information then destroying evidence.
Petty Officer First Class Kristian Saucier allegedly used a cellphone camera to take photos in the classified engine room of the nuclear submarine where he worked as a mechanic, the USS Alexandria, then destroyed a laptop, camera and memory card after learning he was under investigation.
"If any other State Department or CIA employee were using a private email server to send details about the security of embassies, as Clinton is rumored to have done, as well as sensitive meetings with private U.S. government officials and foreign officials over unclassified email systems, they would not only lose their jobs and lose their clearance, they would very likely face prosecution for it,” Snowden said in an interview with Al Jazeera English.
Obstruction and known negligence are the less serious crimes as money laundering and pay-to-play using the State Dept to enrich one's self is certainly against the law. A lesser crime in that nature was also prosecuted Congressman Chaka Fattah was convicted on charges of racketeering, corruption and stealing charitable funds last year.
With Comey gone as director, the ongoing probe of the Clinton Foundation denied to exist at first by the mainstream press, then buried in an article by the New York Times, and other investigations. These probes might finally show promise and yield results bringing the modern-day Bonnie and Clyde to the vice grips of justice in a prison cell along with their collaborators who aided and abetted them.
UPDATE:
"The Justice Department has reopened the investigation of Hillary Clinton's mishandling of classified material on her private email system while she was secretary of state, and is considering offering her a plea bargain if she will agree to plead guilty to charges of breaking the law, according to a Clinton attorney," Newsmax reported on 8/8/17 two days before this was leaked.
The Newsmax report is "unverified" according to Lawnewz.com but the website states that the author Ed Klein is known to have a good credibility and is close with President Donald Trump.
***NOTE: This writer is not a Donald Trump supporter and this report shouldn't be assumed to be in support of Trump, I don't care about your chosen political bias, left or right many are criminals, I care about the truth. The Clintons are corrupt and need to be taken down a good majority of the information provided here in was from a source the rest was me as usual connecting the puzzle pieces.
My pledge not to commit suicide permanently on the blockchain:
------------------------------------------------------------
Patreon: https://www.patreon.com/AKswriting
BTC: 1237PnfRsNXV2Ks16mHSZ1G7buwfyva331
ETH: 0xd7E20e359Da35E8f71110eE67a7ddbD912f6b98e
Another great post dude, well researched as ever.
I can't wait until the 'Clinton Crime Family' are finally taken down. They are one of Americas biggest embarrassments.
This was a genuine leak of links and information mostly I did add some additional details here and there but this was a pissed off former/current FBI agent.
Highly rEsteemed as always AK. This is a BIG one.
I have to share the fact that NO ONE is capable of bringing
down the Clintons... No One! If it were possible, then they would be in cages by now. But instead, we the people get to keep exposing the many, MANY crimes and the order followers in Washington continue to run around acting like nothing is wrong. Look at Comey's way at handling the original investigation; plenty of immunity offers and NO charges! Even all of this new evidence will be ignored by the Bureaucrats.
The simplest way to get HRC taken down is to plant a bag of Weed on her and order the DEA to enforce the God Damn Law! Apparently, ALL of these OTHER VIOLATIONS are Far too complicated for the Authorities to do anything about.
Thanks Frank time for much needed rest after that one.
Agree
I pray for the day the Clintons finally get what they deserve and the Clinton body count can finally stop.
they aren't going down dude, don't get your hopes up.
Thank you for sharing with us! I hope you enjoy the upvote!
who dares..
such a long and informative narratives full of insightful referrals as to true nature of things in this complex world of half truths
thanks for sharing and keep it up...
It was a leak of hundreds of links I couldn't have compiled all that if I tried without having the links since a lot of it is scrubbed now.
i thought so... nice one... i also know such revelations abound on trump camp as regards russian links and meddling...
The Russia meddling in the election is fake news DNC wasn't hacked by Russia the data was removed with a usb drive as William Binney has said NSA would have caught it.
Reshared @phibetaiota
One of the most packed reports of relevant OSINT.
Very great work. Thank you for your contributions.
~The Management
Very informative :) nice effort put in man thanks for the good read #jaillary
Thank you the effort was all my whistleblowers and read the up to date this is fucking incredible!
Thanks for the sharing !
Thank you so much for your effort !!
👍👍👍
Upvoted !
Welcome not a lot of effort in research with this one since I was given all the links and all I had to do is just scroll but putting the story together was certainly hard work. Thank you for your upvote and thanks for sharing.
Thank you so much @an0nkn0wledge !
very good post
good luck
Good luck? With? The Clintons?
lol
Excellent post -- I'm new here, but like keeping eyes on stuff like yours. Americans have got to take the nation back from the neocon jackals that I like to refer to as 'Muricans. We're one; they're the other -- not the same, at all.
Upvoted. Hillary For Prison!