Running a Monero Full Client (Because Governments Will Crack Down on Exchanges)
There's so much going on in the cryptocurrency space, it's hard to keep up! Lately I've been focused on helping the @eosdac team build open source DAC/DAO software (you can see a walkthrough of our member client software here and why DACs are important via this talk here), working to make cryptocurrency easier to use with https://fio.foundation/ (you can see a demo here), and adding value through various advising and consulting gigs such as this @appics project to bridge the gap between STEEM and EOS. I'm still running my Steem witness nodes as well and will put out my thoughts on the upcoming Hard Fork 21 soon (basic summary: doing the same thing over and over again and expecting different results is insane, so I'm for making these changes to get new information on how we can improve the Steem tokenomics and long-term viability).
This weekend, I started playing with Monero and wanted to do a quick write up about the full client integrated with Ledger Nano S. It's been a bit tricky, and I wanted to explain what I've been learning through the process so if you try it out, you may have a better idea what to expect.
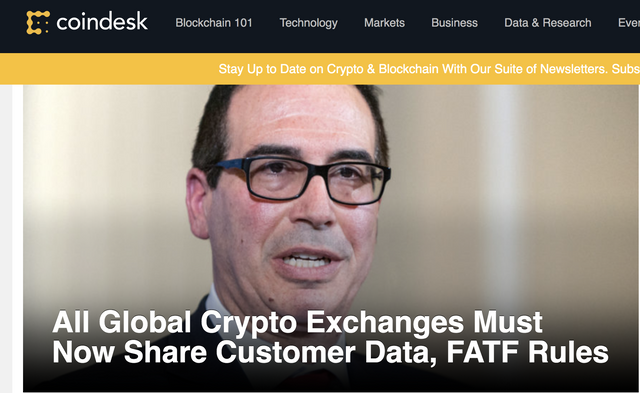
Why run a full client? Well, the answer to that relates to the answer of why Monero is interesting at all. If you've been following the cryptocurrency news, you may have seen this article by Coindesk: All Global Crypto Exchanges Must Now Share Customer Data, FATF Rules.
In summary, it basically says the governments and banks of the world are starting to get serious, organize together, and fight to maintain the control they now have over the human population via controlling currency. They are putting out guidelines which countries will then turn into laws (i.e. threats of violent force) regarding how cryptocurrency exchanges will have to share your personal information among each other, just like banks do.
Decentralized exchanges may help, but even those can get shut down or regulated if there are known humans involved in running them. Based on this news, I'm seeing a battle coming and a reason to have some exposure to more privacy coins like Monero. I want to get involved now before they are classified as illegal or removed from exchanges that play by the rules of violent governments. With major exchanges like Bancor closing its doors to US customers, the writing is on the wall. The battle over who can control value is coming.
I'm going to do what I can to ensure the individual can control their own store of value because that is part of the original reason for cryptocurrency to exist at all. Running a full client ensures I can participate with sending and receiving cryptocurrency, regardless of the decisions made by governments.
To first get an idea of what Monero is, check out this short 1 minute video:
Here's a slightly longer 5 minute video:
That channel has a lot of other useful videos as well which go into more detail explaining the technology involved.
So back to my full wallet setup. A couple years ago, I started using the Ledger Nano S, and it has served me well ever since. There is support for it in the full client wallet which is nice in that your computer will never have your private keys. They will remain safely in your hardware wallet (with one caveat related to the private view key which we'll get to later). If your computer dies, you're fine as your keys are safe. If your hardware wallet dies, you can easily get another one and restore everything with your seed phrase or use any other BIP39 compatible wallet.
First you'll need to download the wallet. You can go to https://web.getmonero.org/downloads/ or directly to the github here: https://github.com/monero-project/monero-gui/releases
Both include a hash so you can verify the file you are getting is trusted and accepted by the community. You can verify that on a mac using the openssl dgst -sha256 <file> command:
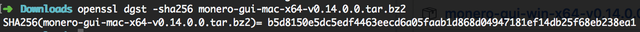
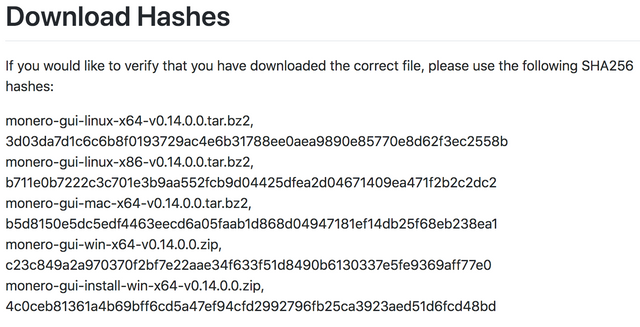
b5d8150e5dc5edf4463eecd6a05faab1d868d04947181ef14db25f68eb238ea1 matches up, so we're good to go.
Next, you'll want to install it and follow the step by step instructions on the Ledger website for setting up Monero (XMR).
Every time you start up the Monero Wallet to use it, it you'll want your Ledger Nano S device plugged in, unlocked, with the Monero app running. It will prompt you each time on whether or not to export the private view key. This key allows you to see your own transactions which would otherwise be private. This key will remain in your computer's memory as long as the wallet is running. This is part of how you stay completely anonymous.
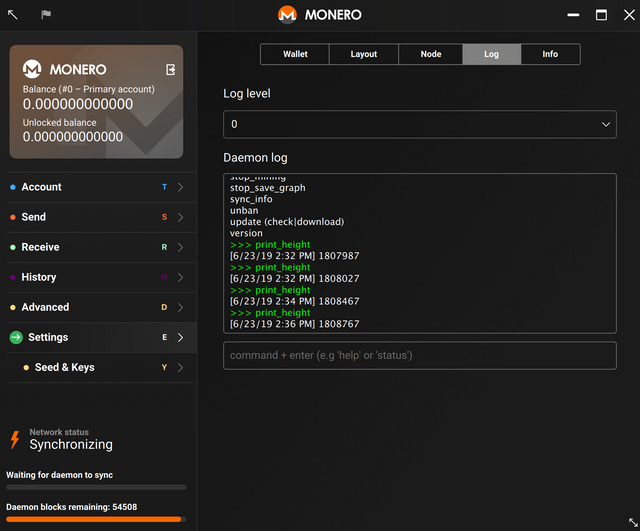
Next is the long, sometimes frustrating process of syncing your wallet. You can go with a bootstrap if you want, but your ip could be tracked as part of that process. I opted to sync the whole chain myself, and it's been running for over a day now and still has over 40,000 blocks to go. At one point, it thought I was all synced up:
Height: 1807467/1807467 (100.0%)
But the test transaction I sent to it wasn't there. Whenever you are working with a new wallet technology you're unfamiliar with, always send a test transaction first. When I checked a monero explorer, I noticed more blocks were on the chain than my wallet knew about (including my test transaction). I had to go into the settings and console to shut down the daemon and restart it again. After that, it continued to sync. I've heard stories of people having to resync multiple times to get it all the way there. If that happens to you, don't panic. Your funds are safe, it may just take a few attempts at syncing things up.
Keep in mind, downloading the entire chain will take a LOT of space and require a lot of bandwidth. As I said, I'm still not done, and I'm already up over 68 Gigs:
➜ ~ cd ~
➜ ~ du -h .bitmonero
68G .bitmonero/lmdb
68G .bitmonero
On the Mac, Monero also stores wallet information in ~/Monero/wallets which was a bit confusing to me since my use of the Ledger ensures my keys aren't part of the wallet. Looking around, I found it only stores wallet settings in the .keys file, not your actual keys as it has no way to get those from the Ledger Nano S.
With that, you should be all set using Monero on your own computer with your Ledger Nano S. If you want to get really creative, you can check out this article on setting up what is sometimes called a "25th word" for your seed phrase: Guide to hardened plausible deniability on Ledger nano S. It allows you to have multiple wallets on your Ledger Nano S, all using the same seed phrase.
I hope you found this useful. Stay safe out there, kids. As you may know, I'm actually a big fan of transparency in a voluntary society, but I also see what's coming. When criminals run the government, being a peaceful, voluntary, autonomous human being may become illegal. Tools like Monero can help us take back control. If you haven't read the Cypher Punk Manifesto in a while, now might be a good time.

Luke Stokes is a father, husband, programmer, STEEM witness, DAC launcher, and voluntaryist who wants to help create a world we all want to live in. Learn about cryptocurrency at UnderstandingBlockchainFreedom.com









Great to see someone facing what will come in near future to cryptos.
I ask many times already what will happen when regulations hit Steem
,the dapps and steem-engine, never got a useful answer..
Maybe you could tell your thoughts?
Thanks and have a great day
Tom
Posted using Partiko Android
No one really knows, I guess. At least there was no ICO and no premine, so it's most likely not going to be consider a security (but I'm not lawyer, so take my word for it).
What type of regulations do envision will come? Maybe the internal market will require KYC?
Yes, that's what I think when I read the last news...
Posted using Partiko Android
Most likely Steemit.com will just remove the internal market and people will run Condensor on their local computers. That wouldn't really be a bad thing. :)
Mimblewmble
Thoughts on this?
do you really need to go through the whole syncing process, download 70Gb to make a safe monero transaction?
Posted using Partiko Android
It's not about making a safe one as much as trying to make a fully, completely anonymous one. But even then, your IP might be tracked by your ISP. Monero was supposed to come with something called Kovri to hide IP addresses (because Tor has some known issues), but I'm not sure if it actually got implemented. Monero isn't perfect and it's a bit complicated to use, but it's still one of best tools we have so far.
Hi Luke, nice to see you on the dark side :)
The Kovri project has failed, unfortunately. There's been so much drama that it can't even be cancelled properly. The paranoid people now run Tor, a VPN or I2P separately in order to hide their IP address. There's a new project called I2P-zero which simply bundles I2P with Monero without trying to redesign it in another language.
You could connect to a remote node, on the desktop GUI or a mobile app. Or use MyMonero, which offers a web wallet and apps for all main platforms. This means that you trust the remote node to use the correct blockchain data. It doesn't affect your privacy very much AFAIK.
In the new version 0.14.1, there's a blockchain pruning feature, which means that you can save only a random 1/8 of the blockchain. This will reduce the size of the database to around 1/3 of the current size.
By the way, forget using a bootstrap file unless you have really bad internet but a good computer. It will take about as long as synching, it requires a lot of trust and it makes it an all-or-nothing process.
Full 100% and a resteem :-)
Any idea when it will be available for Nano X?
Assuming the website hasn't been compromised. Is there some reason why a PGP signature hasn't been attached?
No idea on Nano X, but you can ask in their Telegram.
Not sure what PGP signature you mean? Attached to what?
Maybe something has changed since the 90's, but in the past, when I got a file with a hash, a hash was signed by a known entity (a trusted PGP signature) so that you could know that it wasn't tampered with in between. A hacker could have uploaded their own malicious file and then posted the new hash up on the website and it would match. Something like this would prove that the website wasn't hacked and that the entity uploading the file proves that they did indeed sign it and not some hacker...
https://keybase.io/verify
I know you must know about these things, but this step seems to be missing.