Report The POST of Benjamin FRANKLIN Bacon - HoaxED WARS and Social Media Liability - RAWinformationWAR
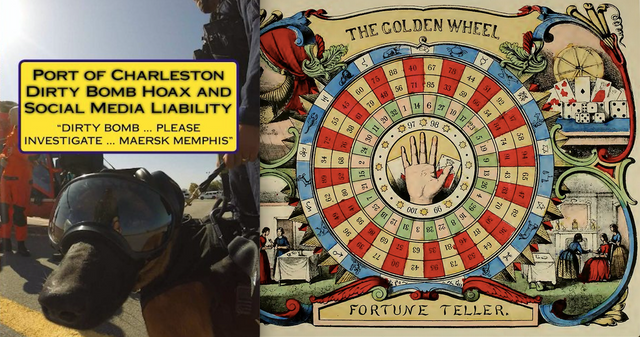
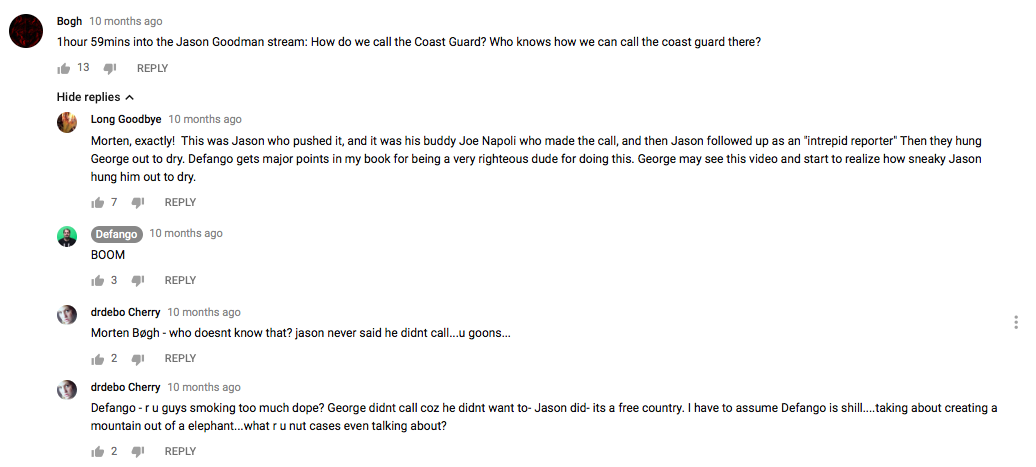
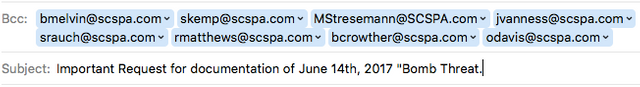
The only report that has ever been written about the Port of Charleston, S.C. Dirty Bomb Hoax of June 14, 2017. This booklet describes how social media hoax news sites can attack America's critical infrastructure. Seemingly, these deception merchants operate with no threat of legal action. This fertile environment has allowed the consequence-free attacks on maritime ports, generation of hysteria of supposed assassination plots, and generate fear over unsafe consumer products. The next generation of cyber attack tools will be based upon Artificial Intelligence and can execute complex social media attacks. Law enforcement is falling further behind the tip of the spear in comprehending the cyber warfare nature of these attach techniques.
Background and Purpose
"Information warfare" has become the buzzword for those looking to the future of U.S. national security as we approach the 21st century. Consensus has emerged that those capable of acquiring, leveraging, and protecting information and information processing systems will dominate the first decades of that era. However, little systematic thought has been given to the overall size and shape of the realm within which these contests will occur, the range of actors who will play significant roles, the instruments that will be brought to bear, or the opportunities and vulnerabilities inherent in the process.
This paper provides an initial exploration of the arena and attempts to (a) identify the key dimensions of the problem, (b) locate the most important areas of the global information systems, and (c) generate insights about the processes of important information interactions.
Typology of Information
The simple, but crucial, step of defining what is encompassed by the term "information" is all too often ignored by those who write about its importance and its future. Most typically in the fields of communication and computer systems "information" derives its technical meaning only when it is contrasted with the lesser category of "data." In this formulation, unsorted, inchoate data and reports (for example, raw sensor information or a set of unanalyzed news reports) are seen as data. Once sorted, classified, or interpreted into useful form (air tracks, an assessment of enemy military readiness, etc.) this same material becomes information. Thus, the key distinction is between data as raw material, and information as a product with added value for its users because of the processes by which it has been selected, organized, and presented.
Curated for #informationwar (by @truthforce)
Relevance: Hoax Wars
I do like that http://FAS.ORG website and it does help people know what they need to know. Media was taking over so much in the 1980's and now Internet social network ghettos in the 2010's.
∴
Er...wtf did I just read? Like, it totally made sense but....I have no idea what you just said...yet, I like it all the same! I suppose if you can't dazzle people with brilliance (which you can, obviously), then baffle them with bullshit (not saying that's what you did but, just saying). LOved it, Mr. Bacon! @hoaxwars !
I hate to break it to you Frank, but the 21st century started 18 years ago.
We approached and leaped right in. Few hiccups like Y2K, 911, chemtrails and 2012 Mayan calendar thing.
The year 2100 will start the 22nd century.
We’re going the other way from my perspective 😎🥓
That would take driving in reverse for a really long time.
Although I have a heavy duty rear bumper, I don't do backwards well and would just get stuck in a time warp. Maybe uni-brow boy can hack a time phone (bahahahaha)
I have an old fire phone - it's bad ass
Amazing post! I love it. Hey UPVOTE my post: https://steemit.com/life/@cryptopaparazzi/chapter-one-let-there-be-the-man-and-there-was-a-man-let-there-be-a-woman-and-there-was-sex and FOLLOW ME and I ll do the same :)