Tomshwom's Advanced Crypto Security Guide (Part 2) - Wallet Analysis
Purpose
In this part of the guide, we're going to look at the existing security measures present in cryptocurrency wallet solutions. We'll look at some specific products as examples, but this is intended to be a generalized overview of the types of wallets rather than specific implementations that may break the mould.
If you missed part 1 of the guide that discusses how privacy, security, and trust apply to the cryptocurrency world, check it out here.
The final part will detail the steps for creating a wallet that surpasses current options in terms of both cost and security, so follow me if you haven't already and keep an eye out for it! UPDATE: part 3 is out and can be found here
Analysis
Definitions
First, lets get clarify some terms I'll be using:
- Wallet & address - the address refers to the public key portion of the cryptographic key-pair referenced by the blockchain, wallets are address managers that keep track of public/private keys.
- Cold storage - cold storage refers to a wallet that is never connected to an online system. Generally, funds are placed into cold storage and not removed for long periods of time (for security reasons).
- Hot wallet - hot wallets are the opposite of cold storage. They are stored on online devices are should be used for "fast & loose" transactions, not secure storage.
- Air-gapped - systems that are physically separated from any network that is linked to the internet are considered "air-gapped". For security, all devices used on air-gapped systems should be limited to that system's offline network. That means no sticking USB drives that were previously in your online computer into your offline systems, and it's not recommended to use devices that were once on your offline network on your online one since exploits can originate at a pre-user stage.
- Hardware wallet - hardware wallets are physical devices that manage addresses with the use of software.
- Paper wallet - paper wallets are physical storage of address information such as private keys.
- Software wallet - software wallets exist on online systems connected to the internet.
Hardware Wallets
I'll be using the Ledgeron Nano S as my example for hardware wallets since it's one of the most popular. The TREZOR works in slightly different ways, but both have the same advantages and disadvantages I'll be going over.
The LNS utilizes multi-factor authentication, namely knowledge and possession factors. It requires that you know the 4 to 8 digit PIN, and that you have the LNS itself in order to sign transactions. The device is further hardened from software alteration or key sniffing by using secure elements that support attestation, a clever way of solving the "compile it from source yourself" barrier. Overall, this is a very secure and easy to use solution. Unfortunately, the convenience comes at a price, and the demand has created a backlog of orders.
One problem I do have with hardware wallets is that they do not provide a robust method of storing the backup seed (generally a phrase of 24 random words that follow the BIP39 standard). If you lose control of this seed, you are completely compromised. Thus, the seed is critical to keep safe and secure, kind of like your private key... Now we're back at square one, you still need an air-gapped, encrypted system or physically secure location to store your sensitive data. Hardware wallets are just convenience items that still rely on conventional security practices.
You may think the solution to this problem is to not keep the backup seed. This is a terrible idea. Hardware wallets will degrade and eventually break or be lost/stolen. Additionally, there are security features in many of them that will completely wipe all the private keys if the PIN is entered incorrectly a small number of times.
In summary, hardware wallets are great at making wallets easily accessible while maintaining the security that is already in place. That means they are malware and end-user resistant (nothing is exploit-proof), but are only as secure as the seed which is left up to the user to manage. Ultimately, I would highly recommend them for 99% of use cases since storing the seed should be doable with very low risk. The only problem I have with them is that you are really just paying for convenience, not added security. Since inconvenience is one of the largest reasons that end-users fail to practice good security, I find the price justifiable for the average user. However, the price itself is an inconvenience that will not be attractive to many people (myself included), so for those who are willing to put in a small amount of effort, stay tuned for the third part of this guide.
Paper Wallets
Paper wallets, at their worst, are a QR code image of the plaintext private key to an address. It's not human readable, but I don't personally have the ability to memorize an entire hex encoded private key at a glance either, so this is not an added security. Since you have to actually dig out the wallet in order to sign transactions, they are less secure than hardware wallets because they can't remain in their secure location.
Additionally, paper wallets only cover the possession factor unless additional measures are taken to add a knowledge requirement. You could have a "paper" usb key with the keystore file paired with a memorized password to decrypt the wallet, but you're still in need of an air-gapped system to actually input any of this information on if you don't want it to be intercepted. They are susceptible to theft/loss and degradation, and the methods to account for this like lamination, metal engraving, and secure storage all entail some level of risk and/or cost. Additionally, the actual printing of a paper wallet is not 100% secure. Printers have memory and are often connected to networks that can be insecure and allow unwanted interception.
In summary, paper wallets - when created in a secure manner - can be effectively used as cold storage up until a transaction needs to be signed from the address. At this point, careful handling of the wallet and a secure system is required if the wallet is to be used afterwards. In my opinion, the overhead of properly creating and storing paper wallets justifies the cost of picking up a hardware wallet since that removes the need for a secure system and the risk of actually using the wallet is mitigated. I would only recommend paper wallets as a temporary solution to cold storage.
Software Wallets
Software wallets like Jaxx have a wide range of security levels. Some use rigorous multi-factor authentication to allow access while others only require that you hit 'run'. MetaMask at least requires that you enter your password to access the wallet. Still, software wallets are completely dependent on the security of the platform they exist on, and my opinion is that very, very few people have an appropriate level of security on their computers. The recent compromise of Jaxx, and the official response to not fix it, are good examples of just how easy it can be to exploit a wallet if the system is compromised.
The major issue with software wallets is that there is some exploit for every security measure. Passwords can be keylogged or sniffed from the clipboard, keystore files can be copied or corrupted, SMS verification can be attacked with SIM swapping, etc. Backup seeds still need to be securely stored and generated offline, so an air-gapped system should be used. In the end, there is no truly secure software-only approach. Aside from features and usability, software wallets are rarely better than simple password managers.
Password Managers
Password managers like KeePass, LastPass, 1Password, etc. are an extremely valuable piece of security that you should be using. However, passwords are very different from private keys. Generally, you can recover from a compromised password, and even if the account is lost it is unlikely that permanent, irreversible damage was caused. If losing passwords were this big of a deal, security would not be an afterthought to many people these days and everything would use 3 or 4 level MFA.
Blockchain is different. There is no aggro transaction reset. There is no authority to help you get your funds back, no 'undo' button. This means password managers are completely out of the question in terms of having a highly secure wallet.
Summary
In this post, we've gone over the requirements for a secure wallet solution such as offline generation and storage, multi-factor authentication, and redundancy. We've also looked at how hardware, paper, and software wallets differ and the trade-offs associated with using them.
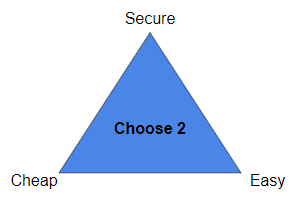
In the final part of this guide, we will address the issues of cost and seed phrase security in hardware wallets and follow a step-by-step guide for creating a cheap, usable, and extremely secure wallet for all your cryptocurrency needs.



Remember to read through part 1 of the guide to get a better understanding of the importance of security, privacy, and trust!
Part one was actually more insightful for me....I already had most of the concepts of part two. But I actually have a better feel for security after reading part one and will be further researching some of the links after reading part 3.
My Ledger Nano s arrived today finally: https://steemit.com/cryptocurrency/@valderrama/my-ledger-nano-s-has-finally-arrived
I'm hoping I can set it up tonight.
Awesome, remember to store your seed securely!
I will store it in 1Password. :)
That's a pretty good idea, but for the sake of argument, it's possible that the seed will be picked up by a keylogger when you type it into the 1Password client, or sniffed from the clipboard if you copy/paste it. I'm not super familiar with 1Password's sync requirements, but you could try adding your seed to the client with your internet physically disconnected from your system. I would first download/update malwarebytes, disconnect from the internet, run malwarebytes to make sure nothing is found, put the seed into 1Password, reconnect to the internet and allow the local DB to sync to the cloud (if that's how 1Password works when offline).
Still, any time you access 1Password you are allowing potential keyloggers to pick up information that could directly or indirectly leak your seed. Because of this, I recommend using an offline password manager (1Password 4, KeePass) to store the seed and move the database to a flash drive (multiple for redundancy). Do this when your system is offline, making sure to reboot before and after you plug in and format the flash drive, then store the password to that database in your 1Password cloud. That way, your 1Password database can be compromised and you won't lose your funds, or your flash drive could be stolen but it will be useless without the password and your redundant backups will ensure you still have your seed.
Excellent remarks. I will definitely take this into consideration!
Also imagine your phone gets stolen in an unlocked state (or someone saw your pattern from five seats over). Now an attacker has access to your phone and likely your password manager (1Password) and hence your seed too.
Great post! I was wondering though, you say password managers are "completely out of the question," but then you tell us how to use KeePass to store a wallet. I understand why you would never use LastPass or your hot KeePass database to store private keys, so I'm guessing cold-storage KeePass is your solution of choice...
Password managers alone are out of the question. In part 3, I go over the method I find to be most secure for personal cold storage. KeePass is involved, but the database is doubly encrypted (by KeePass and the persistent storage volume on Tails). You also need a secondary USB key containing the keystore file. Accessing the contents of the database requires:
An attacker could have 2/3 and still be totally unable to access the system, and if you are storing these properly you should be able to verify their physical security and take measures to move funds if one of the devices is compromised. This is why you should memorize at least one password, whether it's the KeePass one or the Tails encrypted volume one. That way there's no way that somebody can physically steal all the parts.
The wallet should only be used during creating (for testing), and for a one-time withdrawal (at which point you should create a new wallet for maximum security).
How does anyone access the funds of a deceased family member/spouse, if an essential password was stored in the deceased family members brain (e.g. brain wallet)? In terms of security (securing your blockchain assets), this is THE ultimate security risk for loosing all your funds (yes, you will be dead too, but you lost everything, right in the end there), that is overlooked all too often, I believe. What would you recommend, a a private key recovery mechanic for family members?
This is a very good point. If you want to allow somebody else to be able to access your wallet, especially in the case where you are no longer able to, you should be sure they are aware of how your security system is configured and where to find all the pieces to safely access it. For crypto, you would also want to have directions on how to actually sell the coins since it's unlikely that the people who would be helping in the case of a death would know, and you don't want to leave it up to a stranger online.
There are many ways to create a password that can be figured out by a specific person. Leave a note that says "The secret word is: the restaurant we met at + the year your aunt was born". Don't use sensitive information like SSNs. The note could be stored in a location outlined by your security diagram.
Another way is to avoid using a weak password like this and simply split the password into locations that you and your spouse only have physical access to, like a safety deposit box and a home safe.
This is great advice. Thanks!
recommend highly hardware wallets for 99% of cases, would like to define the characteristics of the 1% of other cases?
If you need greater security than what a hardware wallet can provide, or if you're very security-capable and just don't want to spend the money. I fall into the latter, which is why the bulk of my funds are stored in a similar set up to what I describe in part 3 of this guide.
Great post. Thanks for the upvote. I have updated my post here. https://steemit.com/steemit/@bitcoin1488/steemit-resteem-upvote-auction-also-on-ebay-as-a-reserve-auction