The Economist:
What is notable about the effort now is that the challenges are no longer scientific but have become matters of engineering. The search is on for smaller atomic clocks, for example; for a means to amplify and route quantum-communications signals; and ...and more ... Ars Technica:
Programs and algorithms ... written in terms of logic gates; they use higher level constructs, from arithmetic to functions to objects, and more. The same is not really true of quantum algorithms; the quantum algorithms that have been developed so ... TechRepublic:
However, it can be difficult to cut through the marketing jargon used by these vendors to determine the value of the solution. At RSA 2017, Forrester noted that vendors are trying to improve their messaging to help customers distinguish between ... InfoQ.com:
BLS-based auditing algorithms have an edge over MAC and homomorphic methods because they, with the help of a homomorphic linear authenticator, support public auditing and data dynamics.7 Furthermore, ... signature size is much shorter than the RSA ... Hashed Out by The SSL Store™ (blog):
You see this during an encrypted web connection between a browser and a server. After the SSL certificate has been authenticated and the SSL handshake is complete, the browser and server exchange symmetric “session keys” that allow them to communicate ... SYS-CON Media (press release):
H) ("Orbite" or the "Company") announced today it has filed a motion with the Quebec Superior Court (the "CCAA Court") for the issuance of certain orders against Royal Sun Alliance ("RSA"), ... insurer for its Machinery and Business Interruption ...and more ... TechTarget:
The RSA is a relative slow algorithm for encryption; however, it is commonly used to pass encrypted shared keys for symmetric key cryptography. Since RSA encryption is an expensive operation, in IoT it is rather used in combination with symmetric ... Patently Apple:
Before starting USR, Dr. Weiss founded and served for many years as the CTO and Chairman of the Board of Security Dynamics Technologies Inc., now RSA Security LLC, a part of Dell Technologies. Dr. Weiss invented the SecurID tokens and their underlying ...and more ... The Verge:
Today, Google made major waves in the cryptography world, announcing a public collision in the SHA-1 algorithm. ... a deathblow to what was once one of the most popular algorithms in cryptography, and a crisis for anyone still using the function. The ... CSO Online:
As the effective bit length is shortened, the hash becomes less protective and less valuable. At the point when it is believed that someone can “crack” a hash within a reasonable period of time and resources (often still measured in the hundreds of ...
|
Follow our Community for More ! |
|
RSA ALGORITHM WITH EXAMPLE
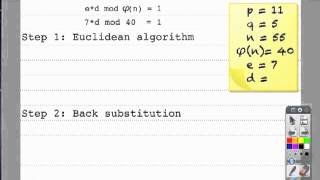
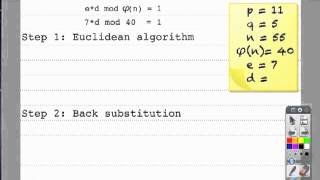
HOW THE RSA ALGORITHM WORKS, INCLUDING HOW TO SELECT D, E, N, P, Q, AND φ (PHI)
RSA ALGORITHM WITH SOLVED EXAMPLE USING EXTENDED EUCLIDEAN ALGORITHM | CSS SERIES #7

RSA CODE MADE EASY
PAPER AND PENCIL RSA (STARRING THE EXTENDED EUCLIDEAN ALGORITHM)
|
Latest posts from our Community ! |
|