New Cross-Browser Web Fingerprinting Technique Developed with 99% Accuracy
Web fingerprinting is a data tracking and identification mechanism that is used by banks and other companies as a way to authenticate and track users. This can be used for good, or for bad.
It might be good for banks to be able to verify and identity through other means, and can also be annoying for retailers to track us and deliver ads tailored to our previous web activity. And this all happens without even having cookies enabled.
source
Researchers in computer science and engineering from Washington University have gone beyond the standard single browser tracking, and have developed the first cross-browser fingerprinting technique. A paper has been published about this called (Cross-)Browser Fingerprinting via OS and Hardware Level Features.
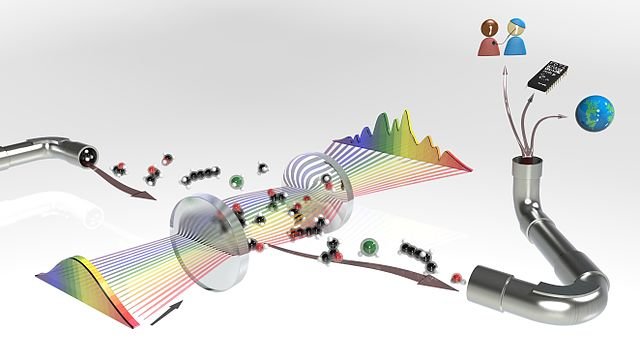
This approach is able to track an individual across different browsers on the same machine by getting hardware level information such as graphic card, CPU and installed script information that can correlate between browsers. This approach might be more complicated, and maybe even appear on first impression to be less accurate, but the opposite is the case in terms of accuracy with 99.24% of users being successfully identified through this new cross browser fingerprinting, as opposed to 90.84% identification success on single browser fingerprinting using the same data set.
Rather than only relying on the layer four Internet protocol as the main way to identify users, Yinzhi Cao and his team have chosen to go deeper to the operating system hardware features to getting even more unique identification. Using an IP is unstable and unreliable as it dynamically changes from each place you use the Internet, from home work or a coffee shop.
Specifically, WebGL exposes the graphic card for information, Audio-Context allows the audio stack to be reached, and hardwareConcurrency can get the CPU info. Additionally, removing any single feature in this cross-browser fingerprinting only decreases the accuracy by at most 0.3%.
The research team is ideally hoping that financial institutions will adopt this new approach in order to provide better multi factor authentication for their customers.
Some solutions to deal with these tracking methods are to employ anti-tracking mechanisms. Isolating your browsing mode can be done to make your profile private on certain sites and separate from your normal browsing profile. Some tools are TrackingFree, Do Not Track and Ghostery. These are to deal with cookie-based tracking, which doesn't deal with the new cross-browser technique. The browser fingerprinting can be better defended with Tor Browser which better anonymizes you're browsing.
References:
- Novel technique tracks more web users across browsers
- (Cross-)Browser Fingerprinting via OS and Hardware Level Features
If you appreciate and value the content, please consider:
Upvoting  , Sharing
, Sharing  or Reblogging
or Reblogging  below.
below.
Please also consider supporting me as a Steem Witness by voting for me at the bottom of the Witness page; or just click on the upvote button if I am in the top 50:
@krnel
2017-02-13, 12pm

I wonder if researchers give consideration to the potential results of their work. I guess that is an old question since at least the days of the development of nuclear weapons based on primary research by physicists. What ends up being developed as a consequence of primary research by computer scientists could be as devastating to humanity as nuclear weapons have been.
Indeed. Technological evolution requires a parallel development of higher moral awareness, or else we become our own worst enemies. Thanks for the feedback.
I don't know how you manage to put out so many high quality posts and still find things that are both interesting and will appeal to a lot of people! I think you must have cloned yourself and have a whole team of @krnels working day and night!
LMAO! Yes, I have heard that suggested by people before, they wonder how I am able to as well. :) Dedication, effort, etc. hehe. Thanks for the feedback.
Or maybe you are an AI or a terminator or something.
@KrNel, your post has been chosen by @STEEMNEWS.ONLINE as one of today's promoted posts for its excellent content. We've upvoted, resteemed and published it through Facebook & Twitter.
As the author of a SNO featured article, you've been awarded one TRAIL coin. Please stop by the SteemTrail Discord server to learn more about how to claim your TRAIL coin. You will need an Open Ledger account to do so.
STEEMNEWS.ONLINE is the @SteemTrail for #news and watches the #steemnews tag most closely. Please consider supporting excellent news articles by making steemnews.online one of your operators on Streemian, in addition to steemtrail.
Thank you for your hard work and contribution of excellent content to Steemit.

If you would rather not be promoted by STEEMNEWS.ONLINE, please inform us by replying to this comment and we will honor your request.
Thanks ;)
Running a machine virtualiser on your computer would allow you to visit sites with a browser which would report completely different specs to the actual machine you are using. Then if you used the Tor browser as well, that should keep you pretty private.
Can anyone find a fault in this?
This method of fingerprinting, called canvas fingerprinting, isn't new at all. It was originally developed in 2012 and has has been around and widely used for years. While the paper is new, it only represents a few relatively small refinements of already existant and widely deployed canvas fingerprint technology. Its something everyone should be aware of.
The legitimately scary thing is how many things you use every day that will break if you block it.
this is the original article describing the basic canvas fingerprinting technique. https://cseweb.ucsd.edu/~hovav/dist/canvas.pdf i think it was published in late 2012. From the numbers ive seen the canvas method already had an an accuracy rate in the high 90s (the outliers being people who are using tor, or who use anti-detect browser) or browse through VM.
As you so importantly underlined in the beginning of your article, such technology could be devastating for our rights and probably is already... The use of the tools offered at the bottom of your text can help and the whole thing makes me wonder the level of efficiency of this new cross-browser fingerprinting technique vs the tools I use.
Thank you again for another highly educational piece of writing, all for one and one for all! Namaste :)
The bright side is this can be another bottomless pit the few in control waste their fortunes on that will be subverted the moment they think they finally hold the one ring that controls them all.
Isn't it also possible to alter IP addresses? I think I said that right...to mask the actual IP address and reroute it through different ones?
Yeah proxies, that's what TOR does.
That's what I thought. It seems that I remembered during the elections the "Russian hackers" using their own IP addresses which was pretty unlikely, I think.
Pepe!
You can be also identified with your specific writing style. This applies also to writing code, if you are a programmer. It is called stylometry.