Computer Hygiene Part 3 - Antivirus
Antivirus Software
Antivirus software can be a contentious topic in many tech circles. It seems like everyone suddenly becomes an expert on detection rate, heuristic analysis, and performance statistics as they push for one solution or another, all while leaving inquisitive readers feeling a bit like Elliot here..

Ultimately, there is no single solution. For some, not running any antivirus is going to be okay, and for others, the expensive enterprise-grade stuff will be best.
If you're reading this with pre-conceived ideas about what's best for you, then you likely already know your use case and are running an appropriate AV solution. This post isn't about which AV is "best", because there isn't one; it's about gaining insight into what AV does, what to look for, and how to evaluate what's right for you.
How Antivirus Works
Antivirus' job is to detect malicious software on a system, and either quarantine or warn the user about it. It does not prevent viruses and malware from getting on the system, but can quickly identify them before they have a chance to actually harm anything. AV detects malicious programs in a number of ways:
Signature-based detection
Signature-based antivirus finds malicious software by comparing the "signature", specific characteristics about a file used to identify it, against a database of known viruses. AV using signature-based detection must be updated regularly, since new signatures are constantly being added to the database. Signatures are more than just a file name, but are limited to information about the file characteristics instead of the function. Since the AV is comparing files against known threats, new viruses may not be identified, leaving the user vulnerable.
File emulation
File emulation, or sandboxing, goes a step further than signature-based detection. The AV actually allows the file to run, but it does this in a controlled, isolated environment (sandbox) where no harm can be done. Doing this allows the AV to see the function of the file, so more information can be gathered to determine if it's behaving maliciously or not.
File analysis
File analysis involves looking at the function of the file, generally through code examination, to determine what it will do. As opposed to file emulation, the file isn't actually run.
Other detection methods
In high-security or research environments, artificial intelligence and machine learning are becoming popular methods for detecting malicious code. These techniques can potentially detect advanced malware designed to circumvent traditional detection methods like those above.
Things to Look Out For
Nearly all store-bought Windows computers come with AV trials pre-installed. I usually see McAffee or Norton AV, but regardless, it's important to realize that these are trial software. They often expire after a few weeks and can become utterly useless while still consuming tons of computer resources. My recommendation: uninstall these and replace them with a new AV.
Uninstall your other AV programs. When two or more AV programs are running on the same system, you can run into some major issues. I've seen one AV find and quarantine a malicious file, only to have the second AV find the malicious file within the quarantine folder of the first. The second AV then tries to re-quarantine the file, including the host directory. Since the host directory is now an AV software, they end up in a tug-of-war over the malicious file, and can even render themselves completely useless by disabling each other.
Depending on the company, it can seem like there's 15 different versions of the same antivirus and the only difference is the word "Premium" or "Deluxe" in the title. This is usually only an issue if you're paying for your AV, which is not necessary for most users. Paying for AV will enable additional features like firewalls, spam filters, parental controls, backup utilities, tune-up software, and more, so it's important to look for a feature list when comparing AV.
As I mention above, paying for AV isn't necessary for most people. It's not inherently easier to just buy your AV program instead of downloading and installing the free version yourself, and the additional features are often redundant or unneeded (if you're following good general computer hygiene).
Most AV function the same way. Generally, AV software uses a mix of signature-based scanning, light emulation, and file analysis to find malicious software. The differences are mostly found in the features. Active monitoring scans in real-time, and can slow the system to a crawl if it's not properly configured or running on a system with few available resources. Email protection, spam filtering, parental controls, and firewalls can all be implemented in the email settings and operating system. AV generally does a worse job of things than setting up these features in the appropriate application, so paying for these additional features is not something I recommend for most people who are competent with a computer.
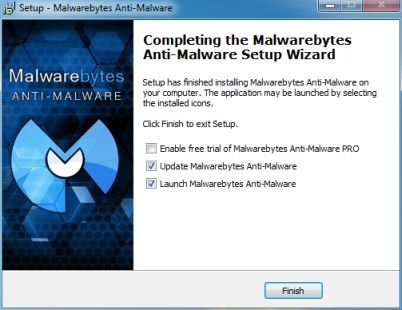
When installing a new AV program (or any software), watch out for options to enable trials, change default browser settings, or install additional software. Use the "Custom Installation" options and simply leave settings with their default values if you don't understand them (or better yet, google it and figure out what it is!)
Always tour the software by clicking on the options, exploring the settings, checking the account info, etc. There's very little risk that you will somehow "break" the software just by using it, and there's almost always a couple options you can enable/disable to make the software much better for you.
Debunking Some Myths
Android/iOS/Macs/Linux can't get viruses
False. While a computer "virus" has a strict definition, and there's very little evidence that these viruses exist on mobile platforms, there is certainly malicious programs that infect these devices. See Malware for iOS, 44 Android apps infected with malware, Mac virus blog, and "Is Linux Immune to Viruses?".
Windows Defender is all you need
Maybe. As discussed above, different users will find different levels of security more appropriate. Windows defender, or any device's built-in security, could be enough. It entirely depends on how the system is being used and what data is on it.
"I'm an advanced user, I know how to avoid getting malware"
Empirically, false. Advanced users are more likely to bypass security measures in order to run software that could be malicious. Whether it's running unsigned applications as privileged, using unverified freeware/pirated software, running in higher privileged modes, or simply ignoring security warnings and not running AV at all "because I know better", advanced users are totally susceptible to getting malware. The difference is only in how they get it.
Virus writers don't target Linux due to low market share
False. While Linux doesn't have a large market share on desktops, it's the opposite when looking at server or mobile platforms. These systems are constantly battling new malware that can certainly end up on your desktop Linux machine.
Personal Recommendations
The average user is storing personally sensitive information on their system. If you're storing sensitive government, company, or client information, a higher level of security is needed than what's recommended below.
Bitdefender Antivirus Free Edition and Panda Free Antivirus have a good track record for being lightweight and effective. They are not comprehensive security solutions, but add basic antivirus protection with minimal impact on system resources. I'm starting to lean more towards bitdefender these days due to Panda's UI changes and ads.
I strongly recommend pairing one of the above, or some other lightweight free AV, with Malwarebytes. See the previous Computer Hygiene Part 2 post for more info on setting up Malwarebytes properly.
Hopefully this post is more than the generic "run a free AV + Malwarebytes" advice that you could've gotten anywhere else. Actually understanding what your AV is doing is sometimes more important than running one, and this post was an attempt at education rather than advertisement.
Congratulations @tomshwom! You have completed some achievement on Steemit and have been rewarded with new badge(s) :
Click on any badge to view your own Board of Honor on SteemitBoard.
For more information about SteemitBoard, click here
If you no longer want to receive notifications, reply to this comment with the word
STOP@tomshwom , thanks for sharing how the antivirus system works and what are important details to look at.
Regards, @gold84
Not how you grow your blog