Stay Safe - 3 Quick Tips to Know if a Website Doesn't Give a Sh*t About Security
Hello Steemians! The internet is a dangerous place and we all heard of successful hacks and data breaches. Just to name a few examples, 2 months ago, Singapore's public health system was hit with the largest data breach in Singapore's history, Yahoo's 3 billion accounts data breach is still the largest in the world and other household names like Home Depot, Target and Sony were also once victims of hacks.
Being a cybersecurity professional, I believe that the security posture of a company largely hinges on the corporate culture. Personally, I look at the corporate website of a company to determine if they take security seriously. Today I am going to teach you 3 quick ways to know if a website doesn't give a sh*t about security 😆.
Poor SSL/TLS Configuration
SSL/TLS are network encryption protocols that are used to encrypt the traffic between you and the website. SSL/TLS has become an integral part of web browsing these days. According to this article, half of the world's websites have already implemented SSL/TLS.
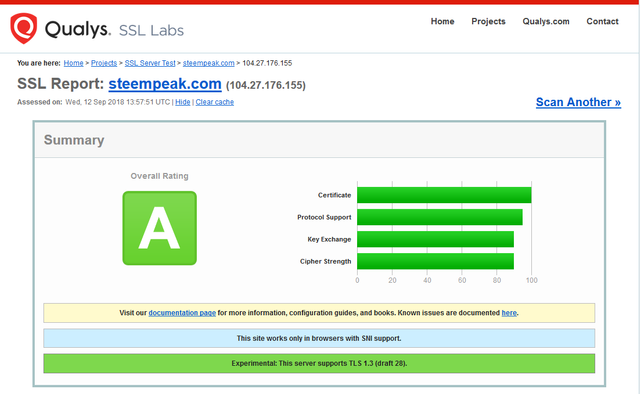
What many people do not know is that within the SSL/TLS protocols, there are also different level of security. To save everyone from the technical details, there is a service which will help you test the SSL security of another site and provide you with a graded report. This site is operated by Qualys which is a well-known name in the Cybersecurity industry.
Companies that take security seriously will enforce stringent settings for their SSL/TLS configuration. Taking a look at SteemPeak's SSL grade, we can see that the team have done a good job in their SSL/TLS configuration.
So the first check you can do when you first visit a site is to check how do the site fare in terms of their SSL/TLS configuration. A grade lower than "B" is a sure sign that the website is probably weak in their security design. Not implementing SSL/TLS at all simply indicate that they don't even care about security.
The Website Sends Your Password to You
Source
Have you encountered websites that send your passwords to your email? This is a typical warning sign of poor security hygiene. A good security practice is to hash your passwords before storing them into the database instead of storing them in clear-text. Hashing is a one-way cryptographic function. This means that it is easy to create a hash from the string of text (in this case your password) but it is extremely difficult to reverse a hash and get the clear-text. There are good reasons to store hashes instead of the actual passwords in the database:
- To prevent database administrators from seeing users' passwords
- To avoid passing clear-text passwords over the network as much as possible
- In the event of a data breach, only hashes will be leaked, hence users are still relatively safe
If you see websites sending you your passwords upon a reset or recovery, they are most likely being stored in clear-text in the backend. Although this is far and few these days, I still observe some older sites that are doing this.
Simple Authentication Mechanism
Quite sometime back, I have written a post on why passwords are the weakest kind of authentication mechanism. In this day and age, relying on just password authentication is no longer adequate. That is also why many popular sites like Google and Facebook have implemented multi-factor authentication. Typically, this involves your password and a token verification (e.g. SMS or software authenticators).
If a site does not support multi-factor authentication, then it should at least do a CAPTCHA check. CAPTCHA means "Completely Automated Public Turing test to tell Computers and Humans Apart". It is basically there to defeat automated brute-force attacks that can be used to compromise your passwords by guessing it multiple times.
If the site is only providing password authentication, it goes to show that they do not take security very seriously and they are leaving their users vulnerable to attacks.
Conclusion
I have described 3 simple ways to know if the website owner is taking your security seriously. If a site fails all 3 checks, it is more likely than not that they do not give a sh*t about security. You will then need to take additional precautions if you still want to use the site. I will recommend you to do the following:
- Do not disclose too much personal information on the site
- Use a randomized password which you have never used in any other sites (If you can use a new email address, that will be even better)
- Always browse the site with a private browser
Thanks for reading and I hope these are useful to keep you safe in this dangerous world 😎.
Projects/Services I am working on:
You can find me in these communities:


I think ive now spent hours solving CAPTCHAs
Annoying thing is they seem to fail alot more now. Like I have to go through many images and then just say "please try again".
But yes good points, checking their cert is always a good first step and see how they handle their password handling can be quick shocking sometimes.
Haha.. yes that's true. Also, I am using VPN and it sometimes causes the CAPTCHA to trigger a bit too often for my liking
Posted using Partiko Android
@culgin
Hah same, even worse when on TOR.
As always, a great article brother! And I know only using a password as security ain't safe but if it's pretty difficult the password should be (more or less) fine?
Usually I use different passwords everywhere.
Btw. when a website sends me the password I simply change it right after I received it. Simply because I don't trust them, normally haha.
Are there other famous security services like Qualys?
Yes bro, it is always more secure to use a strong password. And yes, there are many well known security companies. Symantec, Trend Micro, McAfee and FireEye to name a few
Posted using Partiko Android
Verry good your post!
Thank you!
Posted using Partiko Android
Amazing click
Hi @culgin!
Your post was upvoted by @steem-ua, new Steem dApp, using UserAuthority for algorithmic post curation!
Your UA account score is currently 2.899 which ranks you at #11035 across all Steem accounts.
Your rank has dropped 29 places in the last three days (old rank 11006).
In our last Algorithmic Curation Round, consisting of 487 contributions, your post is ranked at #437.
Evaluation of your UA score:
Feel free to join our @steem-ua Discord server
Congratulations,
you just received a 15.98% upvote from @steemhq - Community Bot!
Wanna join and receive free upvotes yourself?
Vote for
steemhq.witnesson Steemit or directly on SteemConnect and join the Community Witness.This service was brought to you by SteemHQ.com