first computer was hack by the use of biotechnology
This is probably the first time a hacker uses DNA to successfully attack a computer software. The "hacker" here is a scientist at Washington University, and they say that by putting a malware into this particular genetic molecule, they take control of the computer used to Analyze the DNA sequence itself.
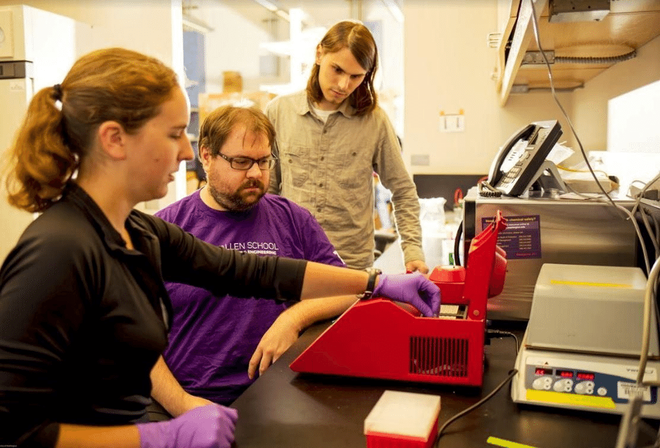
To conduct a computer hack, a team of researchers, including Tadayoshi Kohno and Luis Céz, coded the malware into a strip of DNA they bought online. The hacked machine is used to read the DNA sequence and when the processing begins, the malware starts to spread and hijack the computer.
This research opens up new hacking methods for hackers in the future: someday, fake blood samples or saliva samples can also be used to make access to school computers, Go to the police laboratories or infect other file types.
At present, this DNA malware is not really so dangerous. The researchers also acknowledge that for malware to penetrate the computer easily, they have cleared the way for it by disabling the entire security system as well as adding security vulnerabilities.
"Intrusion is basically untrue," said Yaniv Erlich, a geneticist and programmer, scientific director of MyHertige.com, a biology web site, in A publication.
The DNA will be presented next week at the Usenix Security Uses Conference in Vancouver. "We are researching emerging technologies and asking whether there is a potential security threat in the present moment, the idea of this conference is to go ahead and take that many steps." , Peter Ney from Tadayoshi Kohno's Security Division and also a research fellow at the Independent Research Laboratory.
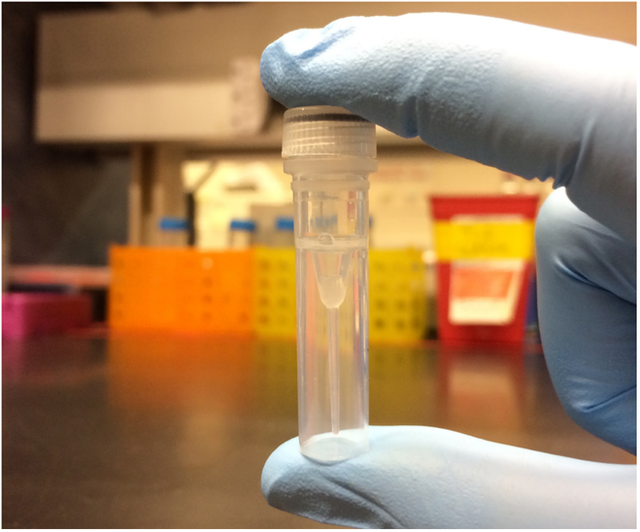
This is how they make this malware: the team translates simple computer instructions into short strings of 176 letters of DNA - including the letters A, G, C, and T familiar to anyone who cares. Little bit in the hour of biology. After buying a piece of DNA from the Internet for $ 89, they put the code into a sequencing system that reads these genes and stores them in binary form. Numbers 0 and 1.
This security attack takes advantage of the overflow effect - that is, when the data overflows, it can be represented as a computer command. In this case, the command could communicate with a computer server controlled by Professor Kohno's team, where they took control of the computer used to analyze the DNA sequence. .
The synthetic DNA company itself, who has already sold the DNA for scientists, has taken steps to stifle bioterrorism attacks. In the future, perhaps they will have to test each sequence of DNA that they may contain malware or computer viruses.
Viruses usually do not say anything, computer viruses can now also be transmitted by blood and saliva, which is unbelievable.
Unbelievable development of the technology but stealing and cheating via this computer advancement is degradable.
Great and Wonderful post! Upvoted. Plis help me Upvoting my lasts posts and Follow me!! I follow back always!!👍👍🙈
ok, me upvote and follow
Thanks for the write up. hopefully the manufacturers will fix it. But very cool. :)
Okey . And thank you
Can you vote for me?
Great post
Yeah. Can you vote for me?
This post was resteemed by @resteembot!
Good Luck!
Learn more about the @resteembot project in the introduction post.
@linhlinhvictoria got you a $1.61 @minnowbooster upgoat, nice! (Image: pixabay.com)
Want a boost? Click here to read more!