Cryptography + NSA + IBM + Cypherpunks + Hal Finney + Dorian "Satoshi" Nakamoto + Nick Szabo = Bitcoin
I Connected The Dots... Research All These Links Below And You Will Come Up With My Equation In The Title.
What gave it away for Dorian "Satoshi" Nakamoto was that he was in the Libertarian Party like McAfee who is also a strong advocate for online freedom from government control/regulation and into Bitcoin. People just don't join that party without having strong political views on personal privacy and freedom and are usually technologically sound.

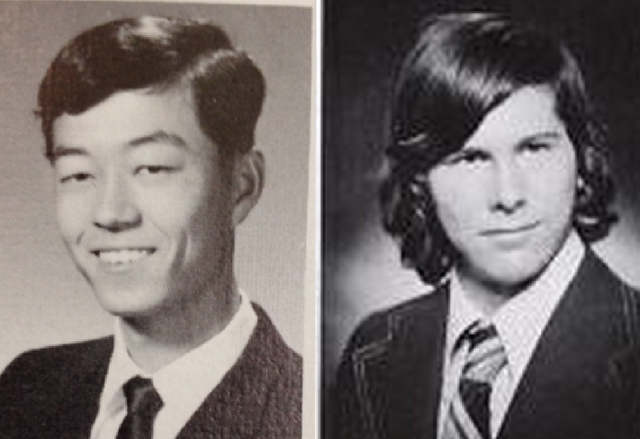
Dorian Nakamoto, then known as Satoshi Nakamoto, (left) in a 1967 yearbook photo from South Pasadena High School, and Hal Finney in a 1974 yearbook photo from nearby Arcadia High.
Bitcoin: Who Is Satoshi Nakamoto An inside look at the man behind Bitcoin
I personally believe Satoshi Nakamoto is Dorian Satoshi Nakamoto working with Nick Szabo & Hal Finney but I think Dorian left the project while Nick and Hal continued it.
https://en.wikipedia.org/wiki/Hal_Finney_(computer_scientist)
https://en.wikipedia.org/wiki/Cryonics
https://en.wikipedia.org/wiki/Proof-of-work_system
https://en.wikipedia.org/wiki/Cypherpunk
https://en.wikipedia.org/wiki/Adam_Back
http://www.cypherspace.org/adam/
https://en.wikipedia.org/wiki/John_Gilmore_(activist)
https://en.wikipedia.org/wiki/Gilmore_v._Gonzales
https://en.wikipedia.org/wiki/List_of_the_oldest_currently_registered_Internet_domain_names
https://en.wikipedia.org/wiki/Dynamic_Host_Configuration_Protocol
https://en.wikipedia.org/wiki/Bootstrap_Protocol
https://en.wikipedia.org/wiki/Bill_Croft
https://en.wikipedia.org/wiki/Eric_Hughes_(cypherpunk)
https://en.wikipedia.org/wiki/Anonymous_remailer
https://en.wikipedia.org/wiki/Cypherpunk_anonymous_remailer
https://en.wikipedia.org/wiki/Mixmaster_anonymous_remailer
https://en.wikipedia.org/wiki/Pseudonymous_remailer
https://en.wikipedia.org/wiki/CryptoParty
https://en.wikipedia.org/wiki/Timothy_C._May
https://en.wikipedia.org/wiki/Cyphernomicon
https://en.wikipedia.org/wiki/Jude_Milhon
https://en.wikipedia.org/wiki/Cypherpunk
https://en.wikipedia.org/wiki/Horn_%26_Hardart
https://en.wikipedia.org/wiki/Community_Memory
https://en.wikipedia.org/wiki/Computer_Professionals_for_Social_Responsibility
https://en.wikipedia.org/wiki/Mondo_2000
https://en.wikipedia.org/wiki/Boing_Boing
https://en.wikipedia.org/wiki/Vincent_Moscaritolo
https://en.wikipedia.org/wiki/Sameer_Parekh
https://en.wikipedia.org/wiki/Zooko_Wilcox-O%27Hearn
https://en.wikipedia.org/wiki/Zcash
https://en.wikipedia.org/wiki/Tahoe-LAFS
https://en.wikipedia.org/wiki/Phil_Zimmermann
https://en.wikipedia.org/wiki/Pretty_Good_Privacy
https://en.wikipedia.org/wiki/Mike_Janke
https://en.wikipedia.org/wiki/Silent_Circle_(software)
https://en.wikipedia.org/wiki/Lavabit
https://en.wikipedia.org/wiki/Lavabit#Ladar_Levison
https://en.wikipedia.org/wiki/Dark_Mail_Alliance
https://en.wikipedia.org/wiki/Cryptography
https://en.wikipedia.org/wiki/Whitfield_Diffie
https://en.wikipedia.org/wiki/Martin_Hellman
https://en.wikipedia.org/wiki/Blockchain
https://en.wikipedia.org/wiki/Diffie%E2%80%93Hellman_key_exchange
https://en.wikipedia.org/wiki/Public-key_cryptography
http://ee.stanford.edu/~hellman/
https://en.wikipedia.org/wiki/Beyond_War
https://en.wikipedia.org/wiki/Ralph_Merkle
https://en.wikipedia.org/wiki/Cryptographic_hash_function
https://en.wikipedia.org/wiki/Merkle%E2%80%93Hellman_knapsack_cryptosystem
https://en.wikipedia.org/wiki/Merkle%E2%80%93Damg%C3%A5rd_construction
https://en.wikipedia.org/wiki/Merkle_tree
https://en.wikipedia.org/wiki/PARC_(company)
https://en.wikipedia.org/wiki/Khufu_and_Khafre
https://en.wikipedia.org/wiki/Block_cipher
https://en.wikipedia.org/wiki/Snefru
https://en.wikipedia.org/wiki/Elxsi
https://en.wikipedia.org/wiki/RSA_(cryptosystem)
https://en.wikipedia.org/wiki/Ron_Rivest
https://en.wikipedia.org/wiki/Introduction_to_Algorithms
https://en.wikipedia.org/wiki/The_Art_of_Computer_Programming
https://en.wikipedia.org/wiki/Adi_Shamir
https://en.wikipedia.org/wiki/Leonard_Adleman
https://en.wikipedia.org/wiki/DNA_computing
https://en.wikipedia.org/wiki/Turing_Award
https://en.wikipedia.org/wiki/Differential_cryptanalysis
https://en.wikipedia.org/wiki/Eli_Biham
https://en.wikipedia.org/wiki/Steven_Levy
https://en.wikipedia.org/wiki/Wired_(magazine)
https://en.wikipedia.org/wiki/Nicholas_Thompson_(editor)
https://en.wikipedia.org/wiki/Andy_Greenberg
https://en.wikipedia.org/wiki/National_Security_Agency
https://en.wikipedia.org/wiki/IBM
https://en.wikipedia.org/wiki/Thomas_J._Watson
https://en.wikipedia.org/wiki/Data_Encryption_Standard
https://en.wikipedia.org/wiki/National_Institute_of_Standards_and_Technology
Capstone (cryptography)
https://en.wikipedia.org/wiki/Capstone_(cryptography)
Capstone is the name of a United States government long-term project to develop cryptography standards for public and government use. Capstone was authorized by the Computer Security Act of 1987[1] and was driven by the NIST and the NSA; the project began in 1993[2]. The initiative involved four standard algorithms: a data encryption algorithm called Skipjack, along with the Clipper chip that included the Skipjack algorithm, a digital signature algorithm, DSA, a hash function, SHA-1, and a key exchange protocol.[3] Capstone's first implementation was in the Fortezza PCMCIA card. All Capstone components were designed to provide 80-bit security.[4]
The initiative encountered massive resistance from the cryptographic community, and eventually the US government abandoned the effort. The main reasons for this resistance were concerns about Skipjack's design, which was classified, and the use of key escrow in the Clipper chip.
https://en.wikipedia.org/wiki/Clipper_chip
https://en.wikipedia.org/wiki/Skipjack_(cipher)
https://en.wikipedia.org/wiki/Alex_Biryukov
https://en.wikipedia.org/wiki/Impossible_differential_cryptanalysis
https://en.wikipedia.org/wiki/Dan_Brown
https://en.wikipedia.org/wiki/Digital_Fortress
https://en.wikipedia.org/wiki/Dual_EC_DRBG
https://en.wikipedia.org/wiki/Half-Life_2
https://en.wikipedia.org/wiki/Dystopia_(video_game)
https://en.wikipedia.org/wiki/Blowfish_(cipher)
https://en.wikipedia.org/wiki/Digital_Signature_Algorithm
https://www.google.com/patents/US5231668
https://en.wikipedia.org/wiki/Claus_P._Schnorr
https://www.google.com/patents/US4995082
https://en.wikipedia.org/wiki/ElGamal_signature_scheme
https://en.wikipedia.org/wiki/SHA-1
https://en.wikipedia.org/wiki/Key_exchange
https://en.wikipedia.org/wiki/Fortezza
https://en.wikipedia.org/wiki/PC_Card
https://en.wikipedia.org/wiki/Kerckhoffs%27s_principle
In cryptography, Kerckhoffs' principle (also called Kerckhoffs' desideratum, Kerckhoffs' assumption, axiom, or law) was stated by Dutch cryptographer Auguste Kerckhoffs in the 19th century: A cryptosystem should be secure even if everything about the system, except the key, is public knowledge.
Kerckhoffs' principle was reformulated (or perhaps independently formulated) by American mathematician Claude Shannon as "the enemy knows the system",[1] i.e., "one ought to design systems under the assumption that the enemy will immediately gain full familiarity with them". In that form, it is called Shannon's maxim. In contrast to "security through obscurity", it is widely embraced by cryptographers.
Origins
In 1883 Auguste Kerckhoffs?[2] wrote two journal articles on La Cryptographie Militaire,[3] in which he stated six design principles for military ciphers. Translated from French, they are:[4]
The system must be practically, if not mathematically, indecipherable;
It should not require secrecy, and it should not be a problem if it falls into enemy hands;
It must be possible to communicate and remember the key without using written notes, and correspondents must be able to change or modify it at will;
It must be applicable to telegraph communications;
It must be portable, and should not require several persons to handle or operate;
Lastly, given the circumstances in which it is to be used, the system must be easy to use and should not be stressful to use or require its users to know and comply with a long list of rules.
Some are no longer relevant given the ability of computers to perform complex encryption, but his second axiom, now known as Kerckhoffs's principle, is still critically important.
Explanation of the principle[edit]
Kerckhoffs viewed cryptography as a rival, and a better alternative than steganographic encoding, which was common in the nineteenth century for hiding the meaning of military messages. One problem with encoding schemes is that they rely on humanly-held secrets such as "dictionaries" which disclose for example, the secret meaning of words. Stenographic-like dictionaries, once revealed, permanently compromise a corresponding encoding system. Another problem is that the risk of exposure increases as the number of users holding the secret(s) increases.
Nineteenth century cryptography in contrast used simple tables which provided for the transposition of alphanumeric characters, generally given row-column intersections which could be modified by keys which were generally short, numeric, and could be committed to human memory. The system was considered "indecipherable" because tables and keys do not convey meaning by themselves. Secret messages can be compromised only if a matching set of table, key, and message falls into enemy hands in a relevant time frame. Kerckhoffs viewed tactical messages as only having a few hours of relevance. Systems are not necessarily compromised, because their components (i.e. alphanumeric character tables and keys) can be easily changed.
Modern-day twist
A modern-day twist to Kerckhoffs' tenets is the idea that the security of a cryptosystem should depend solely on the secrecy of the key and the private randomizer.[5] Another way of putting it is that a method of secretly coding and transmitting information should be secure even if everyone knows how it works. Of course, despite the attacker's familiarity with the system in question, the attacker lacks knowledge as to which of all possible instances is being presently observed.
This twist does not appeal to some cryptographers[who?], who opine that Kerckhoffs had no fetish for the secrecy of keys and was not opposed to keeping other components (i.e. tables, hashes, algorithms, protocols, etc.) of encryption systems "secret" so long as the system remains "indecipherable".
Advantage of secret keys[edit]
Using secure cryptography is supposed to replace the difficult problem of keeping messages secure with a much more manageable one, keeping relatively small keys secure. A system that requires long-term secrecy for something as large and complex as the whole design of a cryptographic system obviously cannot achieve that goal. It only replaces one hard problem with another. However, if a system is secure even when the enemy knows everything except the key, then all that is needed is to manage keeping the keys secret.
There are a large number of ways the internal details of a widely used system could be discovered. The most obvious is that someone could bribe, blackmail, or otherwise threaten staff or customers into explaining the system. In war, for example, one side will probably capture some equipment and people from the other side. Each side will also use spies to gather information.
If a method involves software, someone could do memory dumps or run the software under the control of a debugger in order to understand the method. If hardware is being used, someone could buy or steal some of the hardware and build whatever programs or gadgets needed to test it. Hardware can also be dismantled so that the chip details can be examined under the microscope.
Maintaining security[edit]
A generalization some make from Kerckhoffs' principle is: "The fewer and simpler the secrets that one must keep to ensure system security, the easier it is to maintain system security." Bruce Schneier ties it in with a belief that all security systems must be designed to fail as gracefully as possible:
Kerckhoffs' principle applies beyond codes and ciphers to security systems in general: every secret creates a potential failure point. Secrecy, in other words, is a prime cause of brittleness—and therefore something likely to make a system prone to catastrophic collapse. Conversely, openness provides ductility.[6]
Any security system depends crucially on keeping some things secret. However, Kerckhoffs's principle points out that the things kept secret ought to be those least costly to change if inadvertently disclosed.
For example, a cryptographic algorithm may be implemented by hardware and software that is widely distributed among users. If security depends on keeping that secret, then disclosure leads to major logistic difficulties in developing, testing, and distributing implementations of a new algorithm – it is "brittle". On the other hand, if keeping the algorithm secret is not important, but only the keys used with the algorithm must be secret, then disclosure of the keys simply requires the simpler, less costly process of generating and distributing new keys.
https://en.wikipedia.org/wiki/Key_escrow
https://en.wikipedia.org/wiki/Silent_Circle_(software)
https://en.wikipedia.org/wiki/Sun_Microsystems
https://en.wikipedia.org/wiki/Andy_Bechtolsheim
https://en.wikipedia.org/wiki/SUN_workstation
https://en.wikipedia.org/wiki/Stanford_University_Network
https://en.wikipedia.org/wiki/Carnegie_Mellon_Silicon_Valley
https://en.wikipedia.org/wiki/National_Academy_of_Engineering
https://en.wikipedia.org/wiki/International_Supercomputing_Conference
https://en.wikipedia.org/wiki/Cisco_Systems
https://en.wikipedia.org/wiki/Intel
https://www.intel.com/content/www/us/en/homepage.html
https://en.wikipedia.org/wiki/Fairchild_Semiconductor
https://en.wikipedia.org/wiki/Robert_Noyce
https://en.wikipedia.org/wiki/Jack_Kilby
https://en.wikipedia.org/wiki/Texas_Instruments
https://en.wikipedia.org/wiki/Calculator
https://en.wikipedia.org/wiki/Abacus
https://en.wikipedia.org/wiki/Mechanical_calculator
https://en.wikipedia.org/wiki/Analog_computer
https://en.wikipedia.org/wiki/Thermal_printing
https://en.wikipedia.org/wiki/Lynn_Conway
https://en.wikipedia.org/wiki/Very-large-scale_integration
https://en.wikipedia.org/wiki/Moore%27s_law
https://en.wikipedia.org/wiki/Rock%27s_law
https://en.wikipedia.org/wiki/Gordon_Moore
https://en.wikipedia.org/wiki/Arthur_Rock
https://en.wikipedia.org/wiki/Gordon_and_Betty_Moore_Foundation
https://cointelegraph.com/news/who-is-satoshi-the-hal-finney-dorian-nakamoto-connection
http://www.latimes.com/business/technology/la-fi-tn-bitcoin-founder-la-chased-20140306-story.html
Bitcoin’s Purported Founder Speaks Out
http://www.cbsnews.com/news/dorian-satoshi-nakamoto-i-didnt-invent-bitcoin/
http://leahmcgrathgoodman.com/
https://en.wikipedia.org/wiki/Leah_McGrath_Goodman
2014 bitcoin debacle[edit]
In a March 2014 Newsweek magazine cover story, McGrath Goodman published what she asserted to be the identity and location of Satoshi Nakamoto, the inventor of bitcoin.[10] The article has generated controversy for its methodology and conclusions.[11][12] Writing in Forbes magazine, Andy Greenberg stated that "Criticism of Newsweek’s article, which describes a silent standoff as reporter Leah McGrath Goodman’s stood at the end of Nakamoto’s driveway and was questioned by police, focused in particular on Goodman's decision to name Nakamoto’s family members and to publish a picture of his house."[13] Goodman wrote that when she asked him about bitcoin during a brief in-person interview, Nakamoto seemed to confirm his identity as the bitcoin founder by stating: "I am no longer involved in that and I cannot discuss it. It's been turned over to other people. They are in charge of it now. I no longer have any connection."[10] (This quote was later confirmed by deputies at the Los Angeles County Sheriff's Department who were present at the time.)[14] However, several hours later, Nakamoto's P2P Foundation account posted a message stating he was not the person in Newsweek's article.[15][16][17]
https://cointelegraph.com/news/who-is-satoshi-the-hal-finney-dorian-nakamoto-connection
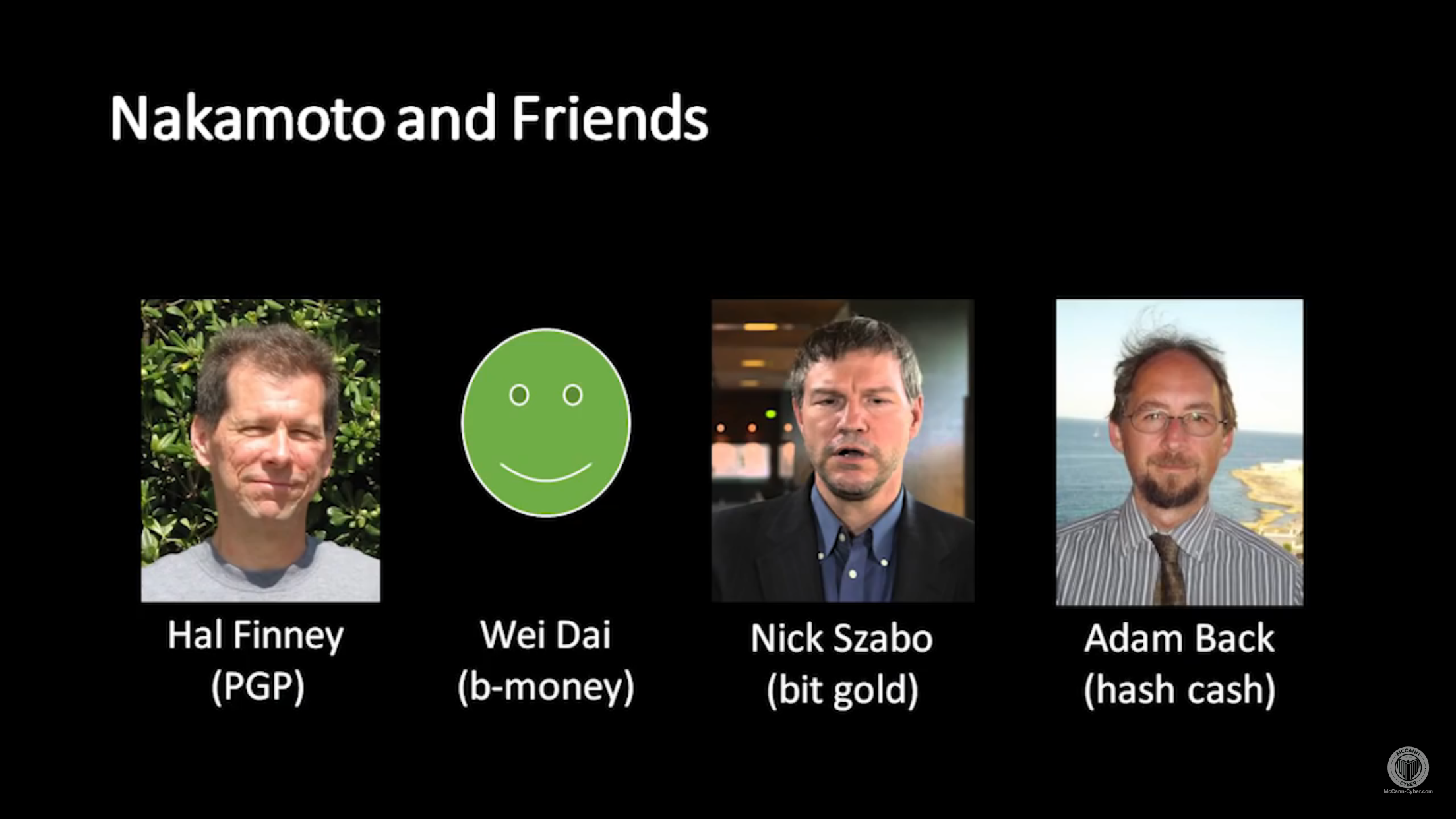
A connection between the late computer scientist, Hal Finney, and Dorian Nakamoto could hold the answer to the creator of Bitcoin’s identity.
The identity of Bitcoin’s pseudonymous creator, Satoshi Nakamoto, has been the cause of much speculation since the cryptocurrency was created. This has especially been the case in recent weeks after Craig Wright claimed to be the man himself. An oft-overlooked connection between the late computer scientist, Hal Finney, and Dorian Nakamoto, born Satoshi, could hold the answer.
Hal Finney
Hal Finney was a computer scientist and pre-Bitcoin cryptographic pioneer who was reportedly the first person, other than Satoshi Nakamoto, to use Bitcoin’s software, file bug reports, and make improvements. However, an acquaintance and co-blogger of Finney, Robin Hanson, supposed that was “at least” 15% sure that “Hal was more involved than he’s said”, though he later redacted these claims when new evidence arose.
Dorian Satoshi Nakamoto
While Forbes journalist, Andy Greenberg, was investigating the identity of Satoshi, it was discovered that a man by the name of Dorian Nakamoto, born Satoshi, was living only a few blocks from Finney. His family home was facing foreclosure by his bank and the retiree was swiftly becoming a victim of the harsh financial climate in the United States.
While Dorian himself was initially investigated as many had suggested that he himself could be Satoshi, these claims were swiftly dismissed when Satoshi vehemently denied his involvement:
“I have nothing to do with bitcoin. I never worked for the company, I don't know any people there, I never had a contract there or anything like that. I wasn't even aware of the product,” he said.
The connection
Reddit user, /u/TaleRecursion, sums up the theory very well:
“I think he [Dorian] is the real person after whom the Satoshi persona was named. The coincidence of having a Satoshi Nakamoto living 2 blocks away from Hal Finney's home is just too improbable to be ignored.
Hal and his cypherpunk counterparts intended for this old friendly retired man whose house had been foreclosed by banksters to be the symbolic figure behind the financial renaissance on behalf of all the victims of the modern financial system. Satoshi is Dorian and I think it's just fine that way.”
Of course, this is far from concrete proof, and by no means proves Finney is Satoshi, but at the very least, it is surely fair to conclude that if Finney isn’t Satoshi, he must have at least told the ‘real’ Satoshi about his neighbour, Dorian.
A man with such a unique name living so close? I don’t think so.
Furthermore, when Greenberg asked the writing analysis consultancy firm, Juola & Associates, to compare a sample of Finney’s writing to a known sample of Satoshi Nakamoto’s, they concluded that its resemblance was closer than any other beforeseen sample, including candidates suggested by Newsweek, Fast Company, The New Yorker, Ted Nelson, and Skye Grey.
Greenberg suggested that Finney may have been writing on behalf of the real Nakamoto, or was instead using Dorian’s identity as a “drop” or “patsy whose personal information is used to hide online exploits.”
Finney ? Satoshi
Surprisingly however, after Greenberg met Finney, and saw the supposed email conversation between Finney and Satoshi, along with his Bitcoin wallet’s history that contained the very first Bitcoin transaction from Satoshi to Finney, which he forgot to pay back, Greenberg resolved that Finney was telling the truth. In addition, Finney denied being Satoshi when questioned by Greenberg.
Moreover, when Juola & Associates analysed Satoshi’s emails to Finney, they found that they more closely resembled Satoshi’s other writings than Finney’s did.
Legacy
As part of his extropian beliefs, Finney believed that in the future, technology will have advanced such that it will be possible for humans to live forever through a technological medium. When Finney passed away in Phoenix on 28th August 2014, he was cryopreserved by the Alcor Life Extension Foundation so that he could be ‘revived’ when the technology existed to allow him to continue living.
If this does eventually happen, and Finney is indeed ‘revived’, perhaps we will be able to put an end to the years-long debate over who Satoshi Nakamoto truly is, be that for the better or worse for Bitcoin.
https://en.wikipedia.org/wiki/Nick_Szabo
https://unenumerated.blogspot.com/
Nick Szabo (Bitcoin founder Satoshi Nakamoto?) Breaks his Silence with a Tweet
https://www.cryptocoinsnews.com/nick-szabo-bitcoin-founder-satoshi-nakamoto-breaks-silence-tweet/
The man everyone thinks is the creator of bitcoin gave a speech discussing the history of the technology
http://www.businessinsider.com/nick-szabo-ethereum-bitcoin-blockchain-history-satoshi-nakamoto-2015-11
How the Hunt for Satoshi Turned Dorian Nakamoto’s Life Upside Down: the Inside Story
https://bitcoinmagazine.com/articles/how-the-hunt-for-satoshi-turned-dorian-nakamoto-s-life-upside-down-the-inside-story-1443721034/
https://en.wikipedia.org/wiki/Bitcoin
https://en.wikipedia.org/wiki/History_of_bitcoin#Pre-history
https://en.wikipedia.org/wiki/Satoshi_Nakamoto
http://p2pfoundation.ning.com/profile/SatoshiNakamoto
Bitcoin and me (Hal Finney)
https://bitcointalk.org/index.php?topic=155054.0
Hal Finney on Bitcoin: In His Own Words
https://www.coindesk.com/hal-finney-bitcoin-words/
Hal Finney received the first Bitcoin transaction. Here’s how he describes it.
https://www.washingtonpost.com/news/the-switch/wp/2014/01/03/hal-finney-received-the-first-bitcoin-transaction-heres-how-he-describes-it/?utm_term=.19d10acf1b57
BITCOIN'S EARLIEST ADOPTER IS CRYONICALLY FREEZING HIS BODY TO SEE THE FUTURE
https://www.wired.com/2014/08/hal-finney/
Nakamoto's Neighbor: My Hunt For Bitcoin's Creator Led To A Paralyzed Crypto Genius
https://www.forbes.com/sites/andygreenberg/2014/03/25/satoshi-nakamotos-neighbor-the-bitcoin-ghostwriter-who-wasnt/#74f749b74a37
Obituary
Hal Finney
Harold Finney, futurist and cypherpunk, died on August 28th, aged 58
http://www.economist.com/news/obituary/21615469-harold-finney-futurist-and-cypherpunk-died-august-28th-aged-58-hal-finney
Who is Satoshi? - The Hal Finney-Dorian Nakamoto Connection
https://cointelegraph.com/news/who-is-satoshi-the-hal-finney-dorian-nakamoto-connection
Dorian Nakamoto, Disputed Bitcoin Inventor, is Traffic Safety Advocate
A California man named Dorian Prentice Satoshi Nakamoto denies having anything to do with Bitcoin.
Writer who named 'Bitcoin guy': Right man
try this one....
https://steemit.com/bitcoin/@harpooninvestor/did-nick-szabo-solve-nick-szabo-s-biggest-bit-gold-problem