How To Secure Your Linux Server
Securing your Linux based server is a vital part of having one to do whatever it is you need performed. I spun up my first server about five years ago to run a game server for my friends and I. Now I have them to do many things including an IPFS node, Monero full node, Monero CPU miner, cloud hosting through Nextcloud, and a VPN.
My Steem witness also run on a Linux server all by itself to help us all send transactions, upvote, and comment. It was during that initial setup that the idea to share what I do to make my servers more secure in a blog post. If you have any questions or have a step that you would add to the list, please let us know in the comment section! I am only one person, and there is no way that I have the best method without missing anything.
Steps To Secure A Linux Server
I will assume that the server host gave you the details to log into the server as root and that root is the only user on the system at first boot. If your host does not give you root access but a separate user, feel free to skip any steps.
I will also display commands as they appear on Debian based operating systems because Ubuntu is the most popular Linux server option. If you run Arch, the commands are very similar and all you will need to do is replace a few words here and there. If you need help, the Arch Wiki is your best friend, and it has everything you will ever need to know.
Update & Upgrade
No matter when you get your new server this needs to be your first step. Making sure your server is up to date is the first line of defense against attacks on your system.
To update on Ubuntu run apt-get update, this will make sure all the repositories on your machine are updated. Now we need to upgrade any software from those repositories that may be out of date for us. It's as easy as apt-get upgrade.
Pro Tip: You can run both of those commands together with && and have the computer automatically accept any yes/no questions with -y. The result looks like apt-get update && apt-get upgrade -y.
Install fail2ban
Fail2ban is an application that monitors your system log files for any signs of an automated attack on your Linux server. When Fail2ban sees this type of attack, it takes the parameters it needs and creates a new entry into your iptable blocking the address of the automated attack. A great feature of Fail2ban is that it can even alert you via email when it detects an attack.
On Ubuntu, servers run, apt-get install fail2ban to install the software. If you want to enable the email feature make sure to install Sendmail as well apt-get install sendmail.
Once installed, it is time to enable some firewall parameters with UFW. Run ufw allow ssh, and ufw enable. (These may already be set up from your host since you SSH'd into your server to run these, but it's a good idea to execute them just to be sure.)
Install NTP
apt-get install ntp
Edit NTP Configuration File
nano /etc/ntp.conf feel free to use any editor you wish; nano comes with Ubuntu by default.
At the end of the file add:
minpoll 5
maxpoll 7
Make sure they are on separate lines.
Enable & Restart NTP
sudo systemctl enable ntp
sudo systemctl restart ntp
Add Non-root User
adduser username
You will then get a prompt to enter a password. Make sure it is a good one with lots of entropy! If you have not read about diceware passwords, please read my post all about making good passwords because this is your main line of defense!
Add Sudo Privileged
usermod -aG sudo username
Log In As The New User
Once you have this step complete, open up a new SSH session while leaving this one intact. You want to make sure you can log into this new account and that everything is set up correctly. If not we need the original SSH session open to make edits.
Test sudo Command
sudo apt-get update is an excellent command to test that this user account has superuser access.
Log Out Of The User Account
exit
Change The Root Password
passwd
Test New Root Password
In the second SSH window that you have open log out of the user and log in as root here as well. This is to check that we typed our new password for root correctly and that we can log in if needed.
Log Out Of Original SSH Session
If you can log in as both root and the new user you can now close the original SSH window, and we are officially finished. Use the user account that you created for all your operations. Root is kind of like a back up to fix things if that user account is compromised or attacked.
Thanks For Reading!
If you have any topics that you would like me to cover, please feel free to comment them below, and I'll add them all to my list!
All images came from royalty and attribution free sources unless specified.
Join us over at the Creators' Guild Discord group! We are here to encourage, support and increase the creation of quality content.
If you have any questions about the future of Steem
or my witness, please feel free to message jrswab#3134 on Discord.
Click here to vote with SteemConnect!
Or go to https://steemit.com/~witnesses
You can see all active witnesses on @drakos' steemian.info
Looking to support my content creation efforts outside of the Steem Blockchain?
Check out jrswab.com/support

I will post a few things to read here. Btw I run the subreddit https://reddit.com/r/linux_mentor so feel free to post this on there.
I come from a background of penetration testing both web applications and infrastructure. Believe it or not but the easiest way to hack a company is to go for the Linux servers. Patching practices on Windows seem to be far better compared to the practices of Linux admins in the corporate world. Hacking a windows server is often far harder than getting in on an old unpatched Linux.
Some basic tips for your normal Linux sysadmin:
https://yoirtuts.com/index.php?title=Finfischer_Hack
https://yoirtuts.com/index.php?title=Hacking_TEAM_Hack
Good luck! Feel free to check the rest of my wiki:
https://yoirtuts.com/index.php?title=Pentesting
After reading through this again. Here are some thoughts I had.
Again thanks for the awesome post! Have a great day!
https://www.digitalocean.com/community/tutorials/how-to-set-up-multi-factor-authentication-for-ssh-on-ubuntu-16-04
Very cool idea! I do not have any expertise here so I am unable to share any best practices on that one.
Yes it is a good practice unless you need root. It's all use case in this matter.
I have not used 2FA on my servers yet but it's a great feature for sure.
I'll post some tutorials based on what I do if you want to add them to a future post then!
Working on setting up a new Linux server at home. These are some tricks I hadn't found in my research. Thank you!
You're welcome and best of luck!
Here are some more tips for anyone who is very new:
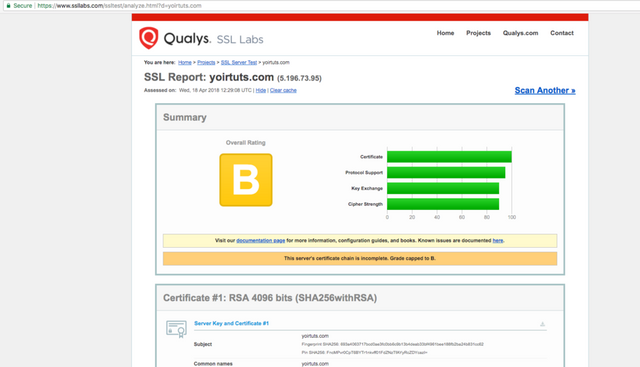
You can get a free SSL certificate from letsencrypt you can check on my website I make use of letsencryp(Oops I scored a B)t: https://www.ssllabs.com/ssltest/analyze.html?d=yoirtuts.com&latest
If you aren't using ipv6 then disable it on your server. This is an extra attack vector if you don't know how to lock down ipv6.
Learn to use iptables instead of ufw if you can. ufw is really just a wrapper for iptables:
Here are some links on SSL:
https://raymii.org/s/tutorials/Pass_the_SSL_Labs_Test_on_NGINX_(Mitigate_the_CRIME_and_BEAST_attack_-Disable_SSLv2-Enable_PFS).html
https://mozilla.github.io/server-side-tls/ssl-config-generator/
https://www.ssllabs.com/ssltest/
https://raymii.org/s/tutorials/Pass_the_SSL_Labs_Test_on_NGINX(Mitigate_the_CRIME_and_BEAST_attack_-Disable_SSLv2-Enable_PFS).html
https://raymii.org/s/tutorials/Strong_SSL_Security_On_nginx.html
https://www.owasp.org/index.php/Testing_for_SSL-TLS%28OWASP-CM-001%29
Here are some tutorials to get familiar with SSH and keys:
https://www.digitalocean.com/community/tutorials/ssh-essentials-working-with-ssh-servers-clients-and-keys
https://www.digitalocean.com/community/tutorials/how-to-set-up-ssh-keys--2
https://www.funtoo.org/OpenSSH_Key_Management,_Part_1
https://www.funtoo.org/OpenSSH_Key_Management,_Part_2
https://www.funtoo.org/OpenSSH_Key_Management,_Part_3
Hi, I just resteemed your post to over 33,800 followers. @a-0-0
This is a grammar nice and neat, everyone is not going to miss it, Hopefully your server is functioning properly to carry out the task.
This post, with over $50.00 in bidbot payouts, has received votes from the following:
upme payout in the amount of $52 STU, $91 USD.
For a total calculated bidbot upvote value of $52 STU, $91 USD before curation, with approx. $13 USD curation being earned by the bidbots.
This information is being presented in the interest of transparency on our platform @jrswab and is by no means a judgement of your work.
Nice post plzz follow me