Data Communication: A Closer look into Computer Networking
Communication, no doubt plays a key role in being productive in our daily activities. Banks, companies, organisations and individuals share information or data, communicating for various purposes to achieve a goal.
But have you ever wondered how group of computers communicates with one another and other computer hardware devices, why not let me have some of your time to take you through basics of how these communication processes are achieved regarding computer network communication.

Image Credit: Pixabay
Without taking much time, just in a simple way, I'd describe data communication as the exchange of data between devices via some form of transmission medium. A group of computers and other devices (such as printer) connected by communication links forms a network. A link thus, is a physical communication pathway that transfers data from one device to another.
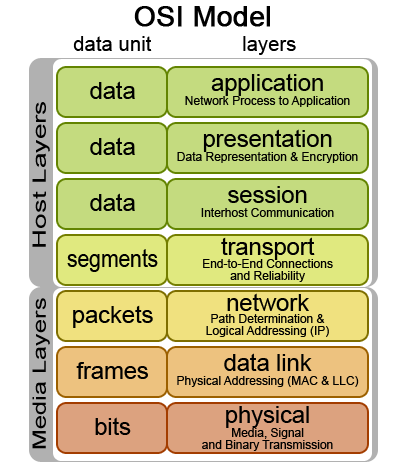
Data flow occur in different forms, defining the directions of flow of signal between linked devices. Data flow can occur in;
I, Simplex: This is way in which communication is only unidirectional. One transmits while other can only receive, signal transmission does not occur simultaneously.
II, Half Duplex: Each device can both transmit and receive but not at the same time. One can only send while the other receive.
III, Full Duplex: Device on full duplex transmission mode can transmit and receive at the same time.
Network of computers are available in different forms, a simple form can have it as a peer-to-peer network where every computer communicate with each other directly with no computer having higher authority than another, it can also exist in a Client-server form of network which involve the use of a central server to facilitate communication and resource sharing between other computers on the network.
The Client-server form of network supports larger network, provides stronger security, more flexible as compared to peer-to-peer but comes more expensive.
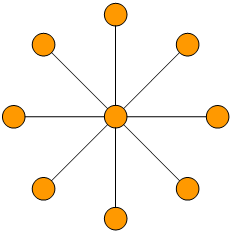
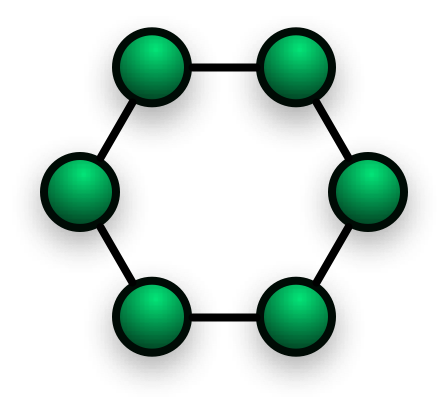
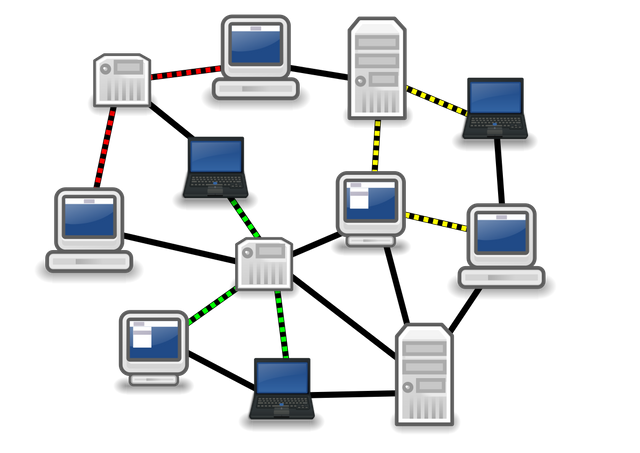
However, there are various ways in which network of computers are laid out, one which is referred to as Network Topology. Network Topology gives a representation of all links and linking devices to each other forming the network. It can be simply referred to as the physical or logical layout of links in a network.
TYPES OF TOPOLOGY
• Bus Topology: this is a configuration that connects all nodes to a single communication line carrying message in all direction. It is cheap and easy to install and as seen in the picture beside, it comes with the disadvantage of loss in transmission if a break in bus cable occur.
• Star Topology: As the name suggests, star configuration is one in which that centers around one major device to which all others are connected and through which coordination of messages are done. Here, Fault is easy to identify and isolate, failure of one does not affect the other but are found mor expensive to install compared to that of Bus.
• Ring Topology: Here, we have the configuration in form of ring where all nodes are connected in a closed loop on which messages travel in one direction. This is very easy to install but a break in the ring can disable the entire network.
• Mesh Topology: This Topology is the best logical topology wen it comes to data flow but very complex in terms of physical design. Here, each device is connected to every other device, giving the most fault tolerant of all.
The type of Topology to be chosen depend mainly on number of users, the purpose of the topology, and it's reliability.
Network of computer thus come in different categories which is determined by size, distance covered or physical architecture
• Local Area Network (LAN): Local area network is a type of network designed to allow resources to be shared between devices in an office, often limited to few kilometers which are mostly privately owned.
• Metropolitan Area Network (MAN): It is a computer network larger than LAN, it covers area of few city buildings of surrounding areas.
• Wide Area Network: This network connects two or more LAN over a large distance, it provides long distance transmission over a large area.

Let's now take a little dig into Networking proper
Here, we would look at how internetwork is formed, the collection of individual networks functioning as a single large network. This concept of internetworking involves the technique of connecting different networks by using intermediary devices (the gateway devices). Internetworking helps in data communication among different networks coupled with the use the internet Routing protocol.
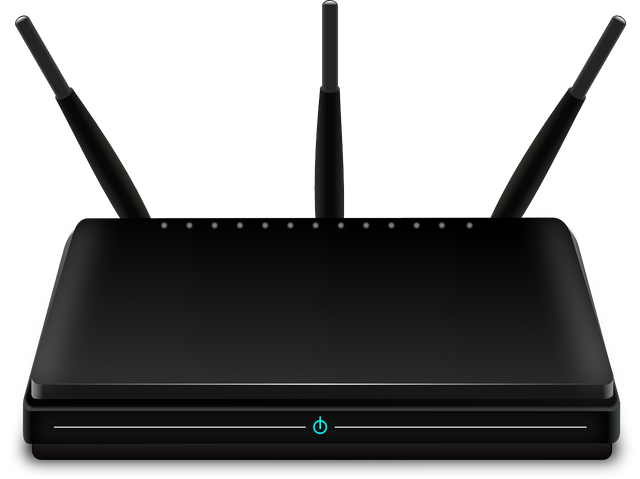
THE GATEWAY DEVICE
Gateway Devices are data communication devices such as routers that provides a remote network with connectivity to host a network. But before we talk about routers, let's have a look at hubs and switches.
• Hub: Hub is one of the devices used for connecting multiple computers together in a Local area network (LAN) for the purpose of resource sharing. Hub was one of the firstly introduced networking device by the Institution of Electrical and electronics engineering (IEEE), Hub works by receiving information from a node and forwarding to other nodes. Hub was the first to be introduced, it works in such an old fashioned way. Hubs are unable to tell one device to the other, hub receives information from one port of the device and sends to all other ports neglecting the fact that maybe the information is meant for those connecting computers or not. For instance, if you intend sending information across a LAN to one major computer connected by a hub, the information will all be received by all other computers connected to the hub. However, Hub is characterized with the simplest and cheapest way to create a network but it has a way of wasting the rate at which data is sent, causes unnecessary traffic and it operates at half-duplex i.e. cannot at the same time, send and receive data.
• Switch: This is neither the electrical nor mechanical switches this time, but computer networking switches. It was the second developed by IEEE, definitely expecting some level of development on the firstly introduced device right? Okay, let's keep following. Switches are able to connect multiple computers together in a Local area network i.e. provided with more ports to accommodate more computer devices, but not just that. Unlike hub, switches creates a switch table ( that's where the name comes in) to match ports to which information is intended to be delivered to. Switches are able to differentiate between computers and stores up the layout in its address book. Switches helps in managing bandwidth usage, minimizes traffic and optimized it's performance operating in full-duplex.
• Router: Here comes the big boss, 'Router'. Routers are gateway devices used to send data or technically speaking, routes packet of data between different networks. Unlike Switches and hub, instead of facilitating communication just between local computers, router also works to routes data to other networks, thereby allowing internetwork communication including the internet.
For data communication to be achieved within network of devices with the help of the gateway devices, a special set of rules are used in communication between the endpoints. Network protocol is it that defines conventions for communication between devices, it is a widely agreed upon format for data transmission between devices, specifying how data is sent and received as messages.
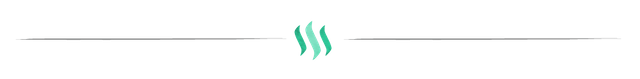
A reference model of networking protocol was developed by Open System Interconnection (OSI) defining networking framework to implement protocols in seven layers. This layers having their distinct function in achieving data communication
Wikimedia Creative Commons BY-SA 3.0 License: OSI Reference Model
As shown in the figure above, the model comprises seven layers;
Layer 7 - Application layer
Layer 6- Presentation layer
Layer 5- Session layer
Layer 4- Transport layer
Layer 3- Network Layer
Layer 2- Data link Layer
Layer 1- Physical Layer
Here's a simple way you could code these layers:
All people seem to need data processing (taking from top-bottom)
The OSI reference model helps us understand better the networking concept and how hardware and software interacts. To get a full gist of how this works, do check this post by @henrychidiebere which focus on the OSI reference model.
NETWORK SECURITY
There are various levels of security installed or configured on system network to ensure the restriction of unauthorized access to the network. A weakly protected network leave hackers finding their way into the network, overriding the whole operation of a system.

Image Credit: Pixabay
Network security i'd say is one of the most important aspect of computer networking. A network of system left unprotected is prone to attack, either to the software or hardware part of the system. Network security is such an essential part of computer networking designed to protect and manage access to network and data. Network Security ensures defense against external forces interfering with the network.

Firewall is one of the security mechanism used in securing the network, it acts like a physical structure that stands between user information and external interference. Firewalls are set of programmes that keeps networks secured by restricting permission of unauthorized member. They are automatically built into gateway devices like switches and routers operating in conjunction with both software and hardware to carry out these set of rules.
Cryptography is another mechanism used in network security involving the process of encryption and decryption of messages in order to be safely transferred from sender to receiver.
The principles of network security ensure efficient network security such as:
I, Message Integrity: Network security ensures message arrived at the receiver end exactly the way it has been sent, maintaining the integrity of the message. Message integrity is extremely important especially when it takes place over the internet.
II, Entity Authentication: This ensures the origin of the message is rightfully identified, helping in establishment of proof of identities.
III, Message Confidentiality: This ensures that only the sender and the intended recipient should only
be able to access the content of the message, to all others, the message must be garbage.
IV, Message Non-repudiation: This ensures sender not being able to deny sending a message that he has sent ( i.e. a situation where a user denies a message she had sent). Non- repudiation helps by not allowing sender of a message to refute the claim of not sending the message.
V, The principle of network security also determines who should access the network and ensure available of resources to authorized parties at all times.
CONCLUSION
Data communication helps in resource sharing across different ends and has been very vital in getting information across to people, making day-to-day activities easily performed and achieved. Data communication within a network of computer are achieved in different ways depending on the purpose and number of users in the network.
Effective data communication is thereby required in achieving seamless communication between network of devices and it's characterized by its accuracy, timeless and ragged delay in delivery of data. Data shouldn't just be communicated but also prevented from attacks from external forces which makes network security an important aspect of computer networking. Providing security for Network ensures the reliability and integrity of the network, protecting network from being a victim of online hackers.
REFERENCES
If you write STEM (Science, Technology, Engineering, and Mathematics) related posts, consider joining #steemSTEM on steemit chat or discord here. If you are from Nigeria, you may want to include the #stemng tag in your post. You can visit this blog by @stemng for more details. 
I'm a proud member of @promo-mentors where you get mentored and guided on how to make quality posts on steemit amongst other benefits. Do join us on discord. We anticipate your arrival.




Hi @olajidekehinde!
Your post was upvoted by utopian.io in cooperation with steemstem - supporting knowledge, innovation and technological advancement on the Steem Blockchain.
Contribute to Open Source with utopian.io
Learn how to contribute on our website and join the new open source economy.
Want to chat? Join the Utopian Community on Discord https://discord.gg/h52nFrV
Data communication is of no doubt an essential part of networking.
Kudos bro
Hello! I find your post valuable for the wafrica community! Thanks for the great post! @wafrica is now following you! ALWAYs follow @wafrica and use the wafrica tag!
Hubs and switches are never gateway devices and shouldn't be listed as one. You have so much information packed here and that's nice but I have to point out some few things.
Oh! My Baad, that's definately an error ...thanks for the check, adjusted. I appreciate
Alright, looks better now. I'd say it was a nice read. Keep it up man
CONGRATULATIONS your post got mentioned in the @wafrica daily curation
https://steemit.com/africa/@wafrica/9yh6k-daily-wafrica-curation
Signed @jeaniepearl
I smell CSC here. Thanks for the reminder sir
You made me remember my N+ networking course at NIIT about a decade ago. Thanks for refreshing my memory
Aside from making money in this platform i think this is also a place for knowledge acquisition. Reading stuff like this helps to expand my mental capacity
I'm happy I'm able to impact some knowledge
Thanks for stopping-by @kingsyrus
The transfer of information is one vital way of life and the advent of information technology has revolutionized that. You have done more that well to give us a comprehensive writeup on data communication. You remind me of an electrical and electronic engineering course I took during undergraduate days.
Kudos pal!
I'm happy you could get a few thing from the post...Thanks for stopping-by
Always a pleasure sir.
as far as i don't like electrical engineering (pardon me bro). I love networking only that i missed out when its learning mattered most. Skipping outside engineering. Networking is the beat way to survive in our country (laugh). So i am not surprise in its vital role in data communication. Always good reading from you