Wide Area Network (WAN) Technologies; A must read
Hello everyone and I welcome you to another eye-opening piece on everyday technology. As always, the basis for my blog is to enlighten everyone who would care to read through about internet technology they've been using all along and by so doing, bridge the gap to an extent, between the happenings at the backend and the front end of the internet.
Image source Maxpixel. CC0 creative commons license
I was in the office last week when one of my colleagues approached me and asked me, Henry, this our internet is it 4G or 3G? I could see his eagerness to shout yes! when I say it is 4G (I guess he's been arguing about something). Well, I have to tell him the truth and I told him, our connection is not 4G, I already guessed the next question and told him, it is PPPoE via the radio interface. I know right there that I have created more questions than I would love to answer but in the end, he asked, which is faster between 4G and the PPPOE, I told him that it depends, but PPPoE can be made to carry far more traffic than 4G.
Many are like him, even the core IT guys don't know the available wide area connectivity their company uses to connect to remote office(s) but hey, I'm here to clear the air. We've seen the evolution from EDGE to 2G, from 2G to 3G, from 3G to 4G and now we have 5G which in fact would be the topic of my next post. In the protocol stack, from Edge to 5G are all physical layer connectivity (Layer 1 of the OSI model) which helps to link mobile users through the help of embedded modem and air interface, though they're fast-rising wireless WAN but that's just one out of many other wireless technologies, so what then is wide area network?
))
Wide area networks are the interface connecting many local area networks. Image source Wikimedia. Creative Commons Attribution-Share Alike 4.0 International license.
We've discussed local area network extensively here in the community and from its name, we could infer that it is connectivity between devices that are within the same locality (let's not go farther than this). Hence, when we setup connectivities like hotspot (be it mobile), connect two computers using registered jack 45 cable, connect several computers using a switch, connect our computer to a wall jack in the home or office, they're all regarded as LAN.
Many of us were encouraged to be entrepreneurs and run businesses of our own, with some already leaving their own dream having offices in major cities in countries like LA, Miami, SA and so on. What happens when you decide to connect all these offices together or want to share the same service or services across all your establishments? Situations like this occur often and in fact, that has been one of the services that have kept the internet service provides in business. The technology that can perform such a task is known as WAN technology.
A wide area network that exists beyond the geographic boundaries of a local area network. Whereas a LAN is within the control of a single administrator, WAN consists of multiple administrators. A very distinguishing characteristic of WAN is the distance it spans, a very popular WAN is the internet, can we imagine the geographic scope of the internet? Also, Wide area networks are data communication network.
Wide Area Network and its enabling features
Standardization in the information and communication technology field is as important as the quest for improved performance, hence the role of standardization cannot be overemphasized. The main body responsible for this process is the International Standardization Organization (the ISO), which developed the Open system Interconnect (OSI) as a major guide in any development in the industry.
))
From the image above, we can see that all our wireless and wired connectivity that make up LAN exists only in layer 1 of the OSI, while WAN technologies exist within layer 2 and layer due to the need for additional error check, error correction and further need for addressing other than IP addresses and MAC addresses. Image credit Wikimedia. Image by BruceBlaus. Creative Commons Attribution 3.0 Unported license.
The main purpose of every wide area network is to safely interconnect equipment and devices that were initially limited by distance, hence eliminating the need for logical addressing techniques (IP addressing), this is why WAN services are within the range of Layer 1 and Layer 2 of the OSI model (i.e, the physical layer and the data link layer).
With WAN technology, network scaling has become less a problem but due to the fact that these technologies thrive in a multitude of other networks, wide area network comes with it, challenges such as security and the need for further addressing scheme. For instance, the multiprotocol label switching (MPLS) uses an addressing scheme called Labels(which is neither a layer 2 nor layer 3 technology but sits in between the two) which operates differently from the traditional IP and MAC address.
Wide area network can be privately owned and in this case, the owner runs cables, radio links, satellite links, etc., to all the sites that need such connectivity. This solution is very costly is usually owned by governments and highly influential individuals or companies. The most popular WAN system makes use of carrier network services thereby making it possible for video, data, and audio transmission. Such systems are known as shared or public WAN services.
Let's get to know these WAN systems better.
Circuit Switching
The most secure method of connecting to many remote sites is by setting up a dedicated link between these sites but as we all know, this method is not only impractical but also extremely costly. A circuit-switched network is a way of connecting many remote devices through a means of a shared medium. To understand how circuit-switching operates, consider a large hall containing about 2000 people undergoing an interactive section. The best way to ensure that everyone's voice is audible enough is to create a public address system and give a microphone to everyone upon entrance!
Though this method ensures that everyone speaks at will and still be heard but definitely a costly approach. A better approach is to create a public address system with about 10 microphones, these microphones are then assigned to people situated at strategic places with a function of passing the microphone to anyone that indicates interest to speak.
Circuit switching operates using the same principle and is mainly applied in voice/audio transmission. It is made up of three phases which are:
- Circuit Setup
- Transmissioin of information
- Circuit termination
In circuit switching, a dedicated connection is dynamically setup between two initiating nodes and with a successful link setup, information is allowed to freely flow through the established channel at a definite speed or rate. Once a channel is established, it cannot be used (even if the channel is totally free) or its resources shared by other nodes within network making it act like a physical dedicated connection to remote networks.
))
A circuit switched WAN. Image desined by me using MS word. Computer icon from Wikimedia
From the image to the right, an office consisting of three branches are connected to a carrier WAN, in the absence of the carrier network, a full or partial connectivity to all the branch office would require at least 8 links and could span millions of miles. A dynamic link setup between branch A and say, branch B would render the link unusable by any other user until a connection between branch A and B had been terminated, this is the major drawback of circuit switched network.
A very popular circuit switching technique is the Integrated Services Digital Network (ISDN) which offers voice, data and video connectivity at a maximum rate of 128 kilobits/sec. ISDN is a WAN connectivity over copper cable connections and has two major limitations, the first is its slow speed of operation and the second is that the created channel is mostly underutilized.
Packet Switching
Whereas circuit switching is analog based in the sense that physical links (channels) are dynamically set up within a carrier network and data is allowed to flow within these links in chunks, packet switching is a digital form of data transmission which allows data to be split into parts and delivered to their destination via a virtual circuit.
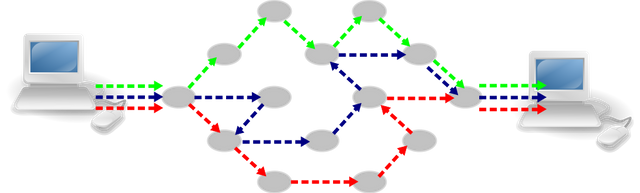
From the above image, it can be seen that data is broken up into packets, each packet is switched across different links, and these links are not fixed or predefined. Let's take a look at two popular packet-switched networks, Frame relay, and Multi-Protocol Label Switching.
A packet switched wide area network. Image source Wikimedia.
Frame relay
Frame relay is an improved technology from the legacy X.25 network which was developed long before the OSI model. Frame relay is capable of turning physical interfaces into a virtual interface which is then used to switch packets within the layer two of the OSI model.
Frame relay performs packet switching using what is known as statistical packet multiplexing which involves splitting an interface into many data streams of random integers which are of variable bitrate. This creates a very flexible channel which can be easily shared and its resource use maximized.
))
basic frame relay topology and equipment. Image credit Wikimedia. Creative Commons license.
The frame relay system consists of a customer premises equipment which includes a data terminal equipment (DTE), Data circuit-terminating equipment (DCE), Carrier network, committed information rate (CIR), virtual circuit and a channel service and data service unit (CSU/DSU). The DTE sits in the various remote sites that need to be connected and communicates directly to the DCE through the help of a CSU/DSU on a carrier network.
The DTE and the DCE are basically routers or layer three switches which are capable of routing packets within a network. The DCE in the service provider network dictates the speed of transmission by providing the clock rate and data synchronization with the customer’s equipment, the DTE. The CSU/DSU serves as a modem within the network and helps in changing the LAN encapsulation to WAN encapsulation and vice versa.
The CIR is the agreed minimum transmission speed for each virtual circuit. During the frame relay setup process, the service provider and the customer agree on a minimum speed at which transmission can occur within the service provider network. This CIR is usually dependent on the customer's budget.
Frame relay offers no error correction or error recovery, hence, it is used on links that are completely lossless. The DCE and DTE carry out data encapsulation in a frame format, the frame relay frame format is a 10-bit header frame format known as the data link connection identifier (DLCI).
The format of a frame relay frame is as displayed in the image to the right. The 10-bit header contains fields like the FCS (frame check sequence) which is neither used for error correction or error recovery, rather, when an error is detected in a frame, it simply drops such frame and waits for retransmission.
The forward explicit congestion notification (FECN) field is solely used to notify congestions in any chosen part within the virtual circuit. The data link connection identifier fields are two in frame relay header and they're for storing the logical sending and receiving DLCI number. This number is assigned by the service provider for any connected site and is only locally significant, which means that remote offices can be using the same DLCI number or a different number.
MPLS
Multi-protocol labels switching is the next big thing in the telecommunication industry and is among the leading WAN services offered by any service provider. It is one of the fastest and about the most affordable and secured WAN services presently available. It solved the major problem facing the frame relay, which is the issue of path congestion and delay in setting up virtual circuits in the cloud.
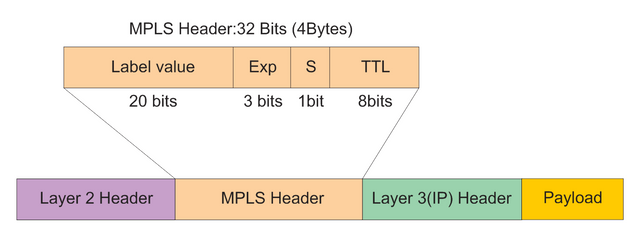
MPLS technology is known as a layer 2.5 protocol because it is neither in the layer 3 of the OSI model or in the layer 2 of the OSI model but combines the best qualities of these layers. The issue of addressing which is one of the major problems facing shared network is taken care of by assigning labels to packets as they traverse through the network.
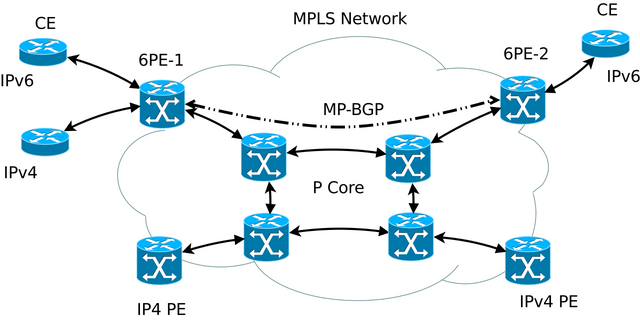
An MPLS network connecting various customers (CE) over a multiprotocol border gateway protocol (MP BGP) network. Image source Wikimedia. A Creative Commons Attribution-Share Alike 3.0 Unported, 2.5 Generic, 2.0 Generic and 1.0 Generic license.
By assigning labels to virtual links within a carrier network, MPLS switching performs the fastest routing job by eliminating the need to make reference to routing information base (RIB) or the routing table maintained by traditional layer 3 equipment like the routers and layer 3 switches.
The MPLS network consists of customer premises equipment or CE (customer equipment) which is basically a routing device, the provider edge(PE) device which is also a routing capable device siting at the service provider environment, the edge label switching router (ELSR) and the label switching router (LSR) which sits at the core of the WAN links carrying out extra fast switching between virtual links using labels. the PE is not aware of the MPLS network hence, they are kept out of the network loop.
A packet destined for the internet or a branch office is first placed on the CE which in turn passes it to the next hope device, the CE which not only wraps the packet in other protocols but also prepares this packet for encryption since all MPLS operations are carried out securely through an IPsec tunnel. The PE then hands this encapsulated packet(s) to the ELSR then creates a label and places this label just after the layer 2 header (before layer 3 header). Depending on the destination of the packet, its switching will be carried out completely based on the information contained in the label header. Three basic operations are carried out on the label and these include, Push, Swap and Pop.
MPLS header is placed between layer 2 and layer 3 of the OSI model allowing for a faster WAN switching speed. Image source Wikimedia. Creative Commons Attribution-Share Alike 4.0 International license.
A label with a swap flag is meant to be passed on to the switching device with a totally new label attached to the packet before forwarding such packet. The push flag is used by higher-level MPLS like the layer 3 MPLS or MPLS VPN, this is because push flags allow for further encapsulation of already existing MPLS encapsulated packets. The pop flag is used only when the packet is about leaving the MPLS network and is heading to a network that is MPLS unaware. The pop flag ensures that operation which involves the removal of all labels on a packet.
Point-to-Point connectivity
Head about leased lines? Leased lines are point-to-point connection which provides a dedicated connection between a service provider or various service providers and a customer or customers.
The operation of point-to-point links are fairly simple and involves securing a fixed interface on the service provider network via means like running fiber cable from your office locations to the nearest connection point on the service provider network, using two antennas, one located you a customer premises and the other on the service provider network thereby setting up a dedicated link between the two points.
A simple point-to-point WAN connectivity. Image designed using Cisco Packet tracer.
The encapsulation that facilitates such connectivity is known as point-to-point protocol which provides the link authentication, encryption and other necessary data handling technique that ensures fast and secured transmission. Point-to-point connections can be made to operate at a very amazing speed and is considered one of the costliest wide area connectivity. Cost of operation is usually based on the desired bandwidth by the customer. Point-to-point links are so powerful that the maximum operating speed a service provider network could be allowed on such links if the customer can pay for such services.
In point-to-point links, addressing is purely based on internet protocol (IP), this is because each point to point link is a network on its own and is referred to as a subnetwork.
Summary
The internet is nothing but roads setup for the sole purpose of passing information from one computer to another. Wide area networks are networks that spans great distances and helps in connecting offices and homes. One very good example of organization that can't operate without a WAN service is the bank with its branch scattered all over a country. WAN provides the necessary security and platform that ensure safe transmission of data between local area networks.
There a various WAN technologies and services offered by the servie providers today that I did not discuss herein which include but not limited to Dial-up services, cable modems, digital subscriber line, broadband services, wireless wide area networks like the 4G connectivity, etc.
I hope that this has been informative for you and I'd like to thank you for your time
REFERENCES
- Introduction to WAN technologies -Cisco
- Circuit switching -Wikipedia
- Packet switching -Wikipedia
- ISDN -Wikipedia
- Point-to-point WAN
- Multiprotocol Label switching -Wikipedia
- Frame relay packet switching technology -Lifewire
If you write STEM (Science, Technology, Engineering, and Mathematics) related posts, consider joining #steemSTEM on steemit chat or discord here. If you are from Nigeria, you may want to include the #stemng tag in your post. You can visit this blog by @stemng for more details. You can also check this blog post by @steemstem here and this guidelines here for help on how to be a member of @steemstem. Please also check this blog post from @steemstem on proper use of images devoid of copyright issues here.

))

This post has been voted on by the steemstem curation team and voting trail.
There is more to SteemSTEM than just writing posts, check here for some more tips on being a community member. You can also join our discord here to get to know the rest of the community!
Hi @henrychidiebere!
Your post was upvoted by utopian.io in cooperation with steemstem - supporting knowledge, innovation and technological advancement on the Steem Blockchain.
Contribute to Open Source with utopian.io
Learn how to contribute on our website and join the new open source economy.
Want to chat? Join the Utopian Community on Discord https://discord.gg/h52nFrV