How is it that hackers steal information from companies? Read this easy to understand information. Sure it will help.
Data hijacking, information theft and hacking of your company/corporate networks are just but a few of some of the most common modes.
As a pandemic spread and in just a matter of days the largest computer attack that has been recorded so far and that put on high alert companies and entities around the world. The dangerous WannaCry virus caused historical damage such as the closure of hospitals and colleges in the United Kingdom and China, the termination of employment in companies such as Telefonica in Spain and Renault in France and entities such as the Ministry of Interior Russia. According to security company Cyence, this cyberattack was estimated to affect around 10,000 organizations and 200,000 computers in 150 countries, with losses that could exceed $ 4 billion.
The episode, which took to the headlines fast, re-ignited global alarms on computer security and how these threats are increasingly powerful, harmful and continue to hit small, medium and large companies in which they cause deep damages such as interruptions in your services, financial loss and theft of confidential information.
In fact, organizations are one of the favorite victims of cybercriminals. More than 12,000 businesses worldwide were targeted for crimes of this type between October 2013 and early last year for transactions in excess of $ 2 billion, according to a report from the FBI's Internet Crime Complaint Center. And according to Juniper Research, it is estimated that between 2017 and 2021, the loss of information will cost organizations a total value of $ 8 billion in fines, operating losses and costs related to risk mitigation.
Is the world prepared for this unstoppable malware evolution? In this scenario, where computer attacks are no longer known, the challenge lies largely in the cybersecurity industry.
Some of the most common attacks are structured around the following:
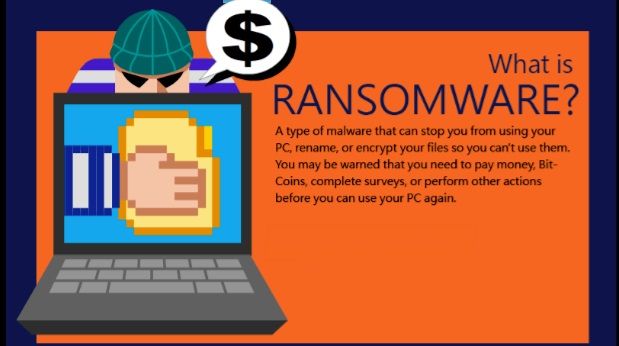
Ransomware.
This malicious code usually reaches computers through attachments in an email. When it is opened, the information on the hard disk is encrypted and the attacker asks for an economic rescue in return. In the case of WannaCry, this was to be paid with 300 bitcoins, a virtual currency that has been quoted in the last days for $ 1,700 and which prevents bank scans. Once a PC is infected, the virus tries to spread to other computers connected through the organization's network. However, the payment of the 'rescue' of the information does not guarantee the recovery of the same. In fact, some people or organizations never get decryption keys after performing millionaire transactions.
Ransomware is one of the most common forms of vulnerability to computer security, accounting for 85 percent of malware attacks, according to an IBM report monitoring more than 8,000 security clients in 100 countries during 2016; it is also the most profitable with respect to the risk-to-profit ratio. It is estimated that only in the first quarter of last year $ 209 million in rewards were turned.
Only during 2016, this form of virtual fraud caused losses of $ 1.5 billion, taking into account the loss of productivity & the Research and data recovery, according to Cybersecurity Ventures. One of the most worrying aspects of this type of attack has been the increase: while in 2015 there were 3.8 million cases in the world, the figure rose to 638 million last year, according to the security company SonicWall computing. With WannaCry, 2017 could be the worst year in ransomware attacks in history.
Phishing.
This technique captures personal data through web pages and fake emails in which attackers copy the design elements of an entity or platform almost identically, so that many users and companies end up being victims and granting their keys - In many cases banking - to a cybercriminal.
2016 closed down as the worst year of phishing in history with 1,220,523 attacks, up 65 percent from the previous year, according to a report from the Anti-Phishing Work Group (APWG). According to the organization, the phenomenon has increased by 5,753 percent in the last 12 years: while the monthly cases in 2004 were 1,609, by 2016 totaled 92,564.
At the corporate level, cybercriminals have managed to copy web pages that pretend to be access to, for example, corporate mail, or through attachments with names related to the corporation's activities.
They typically target companies that work with foreign partners and make payments through fund transfers. According to the FBI, such scams have been reported in 100 countries and fraudulent transfers have been sent to 79 countries, mostly to banks in China and Hong Kong, and it is estimated that by May 2016 this mode added higher losses to the already 3,000 million dollars.
Intervention of corporate networks.
Hackers can determine if any organization's corporate networks are vulnerable or not and attack by finding any holes in the security by sending a command or data to the server that will cause the network to crash and then run that code. When they access the network, they will have access to all the information stored in it, so the damages could be enormous. A critical point is that the attack will move to all computers that are also linked as mobile devices and other computers.
Generally, small companies are the most affected by this modality, since they do not have the security systems pertinent to mitigate this type of attacks.
Access to the Wi-Fi network.
Hackers can also access corporate networks over Wi-Fi wireless networks, so it's no longer enough to have secure passwords. One of the most common vulnerabilities is the use of the simple WPA2 security key sharing mode, which applies the same Wi-Fi access key throughout the Wi-Fi network for employees and visitors. Experts recommend using the PSK enterprise mode, with which different passwords can be set and encryption is used to encode traffic.
One of the best-known cases of fraud in this mode was in 2007, when cyber pirates stole information from some 46 million credit and debit cards from TJ Maxx and Marshalls.
…. And the best line of defense is ….
Use a firewall. This server will allow you to protect your computers against threats that could put your information at risk, block the computers, or even steal your passwords or sensitive data.
Constantly update operating systems, applications and software (including antivirus). Most security incidents are caused by a non-update or security patch that serves as an input hole for the cybercriminal, as happened with WannaCry: computers with an outdated version of Microsoft Windows were affected.
Make periodic copies of information security. This process must be constant and accompanied by a concrete definition of the procedures for restoring information in case of attack.
Establish security policies. You need to share with all in the company, colleagues, friends and family how to make good use of technology resources and to recognize possible false electronic mail, as well as other threats.
Did this post widen your know-how ...? Great, please UPVOTE and in addition, if it is such a nice one, i.e. above average, then go ahead and RESTEEM. Appreciate your comments also.



I believe that the presence of ransomware will help boost the amount of money in the crypto market since companies will likely begin stockpiling cryptos in order to buy back their computers. It will also prevent over regulation as hackers wont demand payment in currencies that can be easily tracked or invalidated.
thanks for the post! very enlightening info
Another scary thing about Ransomware - in the future, when the IoT becomes more widespread to devices like pacemakers, it could be infected in the same way, except this time, lives would be on the line...
yes; got hold on the article ..... could one eventually stop someones life by wifi... hummmm scary ...
Great information for companies to pay attention to. I like your post, keep up the good work.
nicely written!
thanks for sharing
Great reminders! People need to keep security top of mind these days.
This post is amazing! :)
Upvoted!
this is very iteresting.. thank you for the info!..
i'm @antoniomontilva i'm following you, i hope that you do the same :D thanks for all the support!
Really great article well formulated.
Only suggestion I would make is using headers (increases the font size for headers) would make it slightly more readable.
Thanks again for sharing great info
Unfortunately, we all will have to start taking very serious about this subject. For starter I moved from windows to a little safer Linux and I'm quite happy.