INTRODUCING GOLDILOCK : THE HIGHLY SECURED STORAGE PLATFORM

Pixabay
INTRODUCTION
One of the greatest challenges encountered by individuals, brands, organizations and companies is storage as well as safety of hard earned assets and resources.
Acquiring funds and even data can be a real pain in the ass, so after spending so much effort and time getting it, some random person or company will tell you some cock and bull stories of how they lost your funds or data.
With experience I know how heart breaking it is.
It could be you patronizing an online firm that specializes in the storage of data and funds. Then, you were oblivious of the fact that their infrastructure build and set up had flaws that would expose your highly sensitive information or bring a loss to your funds.
As a financial expert and worker with a highly reputable bank, even with our heavily guarded security men, we have experienced theft of funds one or two times, both from hoodlums and malicious staff membersAlso, highly classified information of customers have also experienced third party access due to no sophisticated storage safety set up or is it in cases where a sister branch was caught up with fire.
I like to point out that the problem of storage is not just limited to traditional means of storage. It has also eaten deep to every means of storage platform that exists or has ever existed.
INTRODUCING THE TWO KNOWN MEANS OF STORAGE
HOT STORAGE
Hot storage is a type of storage that is connected to the internet, by means of being hot, it simply implies that it is easy to setup, access and also can accept more tokens (cryptoccurrency)

Some examples include: Coinbase, Blockchain.info etc
Going forward, some online companies have passwords and private keys that are often protected with very awkward, outdated and inefficient security measures.
It looks promising but it cannot be trusted as it has failed in recent times.A friend of mine called from the states complaining of how insecure the online store has become, hackers could easily pounce on a technology while carting away with valuable assets and resources.
‘$500 million in cryptocurrency was stolen by hackers from Coincheck at a major Japanese exchange sometime ago and is unlikely to be the last such hack, according to a Wall Street analyst’.
"I think [the attack] does highlight the fact that the industry still has a long way to go in terms of basic issues of security," Nicholas Colas, co-founder of DataTrek Research, told CNBC's "Squawk Box" on Monday.
Source
Hot storage solutions also prove ill-suited when it comes to key custody. Simply put: anything connected to the Internet can be hacked.
Online hot storage wallets are also a problem as they are not invincible in this situation.

Some of the problems associated with the Hot storage include:
Denial of service
Theft
Custodial Custodian Collapse
Scalability Issues
COLD STORAGE
In simple terms, cold storage is not connected to the internet, unlike the hot storage, it is more secure. It is a bit more complex to use and as such requires some level of tech-knowledge.
Some cold storage wallets include:
Hard drives
Trezor
Ledger Wallet
Xapo
Then about cold means of storage, it has over the years experienced its own sheer of flaws and insecurity; a highly coordinated robbery attack could bring down a heavily guarded bank or financial institution.
Then, fire outbreak could also destroy manually saved data and information
Traditional cold storage solutions and prospects invariably are not the answer to providing investors with a suitable key management solution for their cryptocurrency, data and funds. Paper and USB keys can lost, stolen, or damaged.
The encrypted cold storage solutions offered by groups like Xapo or Coinbase have extremely limited accessibility which does not address most institutional custodial needs.
The storage of encrypted key in an inaccessible bank vault may seem as a promising prospect in curbing theft especially for individuals or institutions, one who might not want to trade, then problem arises in obtaining access to the USB, this is not practical for active asset handling.

The problems associated with Cold storage includes:
Hacking
Misplacements of keys or storage items
Theft
Destruction by natural disasters or man-made disasters
Requires highly tech-knowledge, hence not quite inviting
Expensive to buy
Considering the 4 billion records breached impacting email providers, banks, and credit card accounts over the last two years, and given that over $1.2billion in Cryptocurrency has been stolen in that same period, it’s clear that the traditional digital asset storage industry is compromised.
Source: Goldilock Whitepaper, page 4
Consequently, the crypto world has not been left out in these problems. As a matter of fact, these problems have decreased the adoption of crypto by investors and the world at large.
While Blockchain is inherently designed to be more secure than traditional ledger technology as well as other means of storage, the reality is that cryptocurrencies are susceptible to the same attack vectors as other digital assets, a perfect example is the case i mentioned above.
Then does it mean that no hope exists for the storage of data and funds, the answer is NO. A blockchain tecchnology saw all these problems and decided to bring a stop to the numerous problems
After going through the exciting features and infrastructure build of this blockchain, i can say a solution exists finally. i hereby introduce to you Goldilock

INTRODUCING GOLDILOCK
Goldilock is a blockchain technology that seeks to revolutionalize the way data is stored on the internet by building an ecosystem that will secure cryptocurrencies and digital assets for individuals and institutions
Goldilock principle faults the hot or cold storage means by advocating for right and just storage.
It will maximize effectiveness while minimizing the redundancy and excessive insecurities seen in the hot and cold storage platform
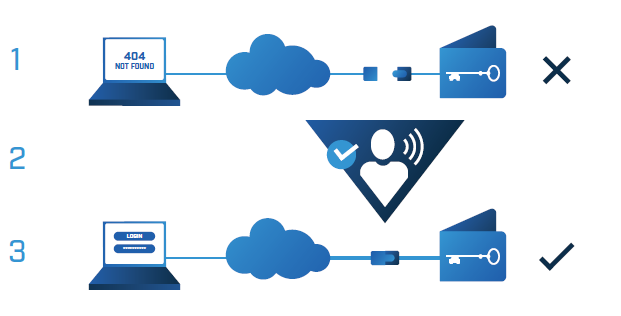
While looking at the vision, Goldilock is built on the premise that your data should not be physically connected to the internet when you’re not using it, but that it does need to be available to you from anywhere immediately when you want to access it.
Goldilock is redefining how sensitive digital data is handled by individuals and institutions.
It is a highly secured storage platform that ensures that the data and assets of individuals are secured, Goldilock remote, encrypted individual HSM vaults allow crypto keys and assets to be active and readily available online via a non-IP trigger mechanism, while also being disconnected and invisible from the internet when not in use by their owner.
This feature is mind blowing and unapologetically eclipses the highly error prone hot and cold storage medium

GOLDILOCK PREMISES AND CONSIDERATIONS TO UNDERLYING SOLUTIONS
- “Users need access to their personal data quickly, but only occasionally and for short periods of time. otherwise, online data is more useful to hackers than rightful owners”.
“Personal data (including private keys) must be isolated, secured from physical contact and related human error, and fully backed-up”.
“Personal data and private keys must be quickly accessible when needed”.
Adapted from the whitepaper, Page 5
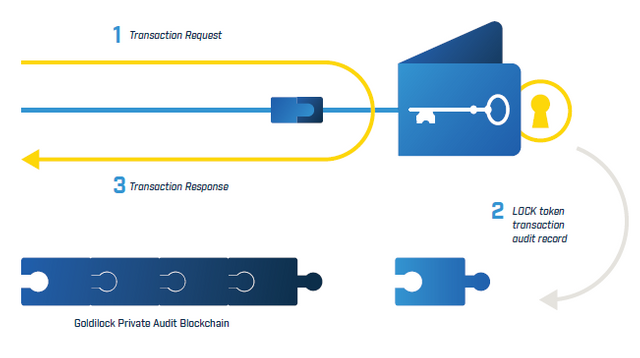
Goldilock is highly sensitive and cuts across the hot and cold storage. It is highly secured in the sense that the wallet is stored offline through a physical airgap mechanism and is not accessible from the internet
A user serves the sole right of activation, which can be done using a non-IP mechanism, which resultantly makes the wallet accessible over the internet
Users can also securely access their wallet over an encrypted connection using a dedicated URL and access credentials

THE GOLDILOCK SECURITY SUITE
THE GOLDILOCK WALLET
The Goldilock wallet is for specially designed for transaction purposes and is also cryptocurrency investors. The wallet will be built by the Goldilock Core development team.
However, the initial motive was for the wallet to be used for transacting of NEO, GAS and NEP-5. I mentioned earlier that the wallet will be offline, this is basically due to security reasons. Some other amazing features of the wallet include:The wallet will be disconnected from the internet and would reside on a unique, segmented and encrypted hardware device
The wallet can only be brought online through a non-IP command and PIN/voice verification over the non-IP Public Switch Telephony Network (PSTN)
There is an abrupt closure and disconnection of the unique hardware device whenever the wallet is closed
The wallet will maintain and function effectively through a unique personal assigned URL, the URL will be distinct from that used by others
Every signed transaction will require Two-Factor Authentication.

GOLDILOCK API SERVICES
The GOLDDILOCK API services will follow suite after the wallet. The main thrust of the API services will be to enable institutions that already have existing wallet solutuions to use GOLDDILOCK’S patent-pending solution that requires improved security.
This will however improve the security of their system and also increase users experience and trust. The API services will run both on the colocation facility and cloud.
The APIs can be embedded within non-decentralized applications or into stand-alone dApps.
Enterprises and partners alike will be able to build privacy-foucesed, consent driven applications

GOLDILOCK’S COLOCATIONS
For the sake of clarity, colocation is a type of data centre where equipment and several other computing hardwares are available for rental to insititutions as well as retail customers
Goldilock has a physical vault available for leasing by institutions who need them for direct control over their servers

ON-PREMISES DEPLOYMENT OPTION
This security suite allows users to remotely operate airgap security and is available for institutions and personal home use
WHY THE NEO SMART ECONOMY/ BLOCKCHAIN?
NEO is a blockchain technology that is non-profit oriented. It has over time been able to use the blockchain and digital identity to
Goldilock incorporated the NEO’s blockchain and smart economy because it meets with its guiding premises. Through the combination of its some factors outlined above, NEO seeks to build a secure blockchain that will be recognized by governments and enterprises and this was what endeared Goldilock to the NEO blockchain.
- Digitize assets
- Automate the management of digital assets using smart contracts
- Realize a “smart economy” with a distributed network
NEO is different from other blockchain smart contract competitors as it provides the following features:
COMPLIANCE AND REGULATION
Audit has a way of verifying and ensuring transparency while also maintaining the laid down standards. In the NEO blockchain, for large companines and governments to operate, they will require the ability to audit digital assets and transactions.
NEO will use the Public Key infrastructure (PKI) X.509 standard for identity, which will give them the strength and ability to confirm digital identities

IMPROVED POW AND POS
A mechanism known as “Delegated Byzantine Fault Tolerance” which is a coordinated improvement t the proof of work in Bitcoin and Proof of stake in NXT.
This dBFT ensures and enables holders of NEO tokens to vote for delegates and the delegates must reach a consensus on acceptable transactions, it is more like a synergistic approach.

FASTER TRANSACTIONS AND NO TRANSACTION COSTS
The use of the dBFT makes transactions faster and very scalable too. The blockchain can now process in excess of 10,000 transactions a second without transaction costs.
More so, the dBFT makes it convineint in that thousands of machines mining are not required to complete a resource-expensive algorithm needed to verify transactions

APPLICATIONS AND BENEFITS OF GOLDILOCK
HIGHLY SECURED AND VAULTED WALLET
In recent times, users of hot and cold storage platforms have experienced security issues and fear for loss of fund. As a crypto owner, securing your acquired coin/token and also data is of utmost importance.
Using GOLDILOCK, safety of wallets is assured, private keys cannot be easily exposed and classified information are isolated inside your hardware wallet and also is physically disconnected from the internet where it is locked in a vault with multi-location redundancy and can only be accessed through biometric gateways
This means that a user’s transaction can never be tampered with and your LOCK token is intact.
GOLDILOCK keeps you covered.

EXCLUSIVE DIGITAL RIGHTS MANAGEMENT AND PROTECTION
For movie and music makers, the stress of spending funds, energy and time producing a movie or music is excruciating.
Then, it is heart breaking seeing your content is being copyrighted. But there is solution to this, GOLDILOCK technology, movie or music makers can now have the ability to control who sends and receives their publications
It ensures that people access contents using the appropriate means and channels, it is a check on copyright. It extensively gives right to producers of contents.

BENEFIT IN THE HEALTH SECTOR
GOLDILOCK diversity cuts across the medical field. Most health care firms have an underlying problem of privacy as well as sharing data with authorized account holders like doctors, pharmacists etc. it has been a challenge as the combination of the afore mentioned has proved a herculean task.
GOLDILOCK has stepped into this by improving the ability for patients, families and health professional to share data more securely while also protecting individual rights in awesome ways which were impossible before now.

GOLDILOCK AND IT'S BENEFIT IN THE BANKING SECTOR
As a bank worker, we often times experience situations of insecure transactions. Someone transferring money to someone usually might attract attention especially in cases of PEP (politically exposed persons). These types of transactions are not secured due to access by third party and at times theft.
The bank accounts of these PEP are not safe either as undue attention is unnecessarily being attracted and that is not healthy for the system
GOLDILOCK provides a secure backend solution for bank accounts and transfer managements.
SOLUTION FOR CONSUMERS
PRIVATE KEY CUSTODY
With the highly efficient structure of GOLDILOCK, individual consumers will be provided with an encrypted storage device, which is stored in a vault within a secure data center.
The supposed device will readily be offline and also offline. This encrypted storage device will allow users full control of the private keys which is already securely managed

SOLUTION FOR INSTITUTIONS
ONLINE/HOT WALLET OPERATORS
It allows leveraging at its maximum, hot wallet operators and custodial can leverage the remotely-automated airgap. Also, they could opt in for an in-house license or an outsourced service model.
There will be no third party access as even GOLDILOCK will have no access to client data
HARDWARE/COLD WALLET OPERATORS
A cold wallet storage can be incorporated and it can allow operators to leverage in order to enhance their existing technologies
LOCK TOKEN
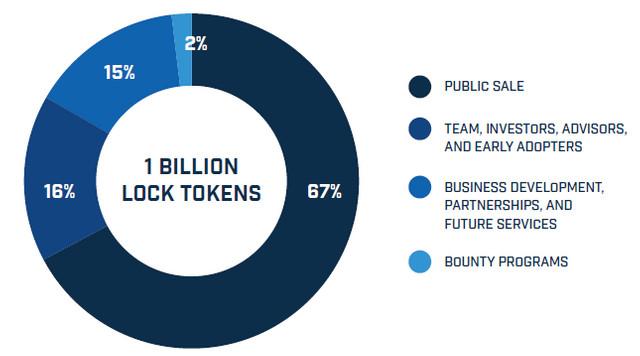
The LOCK token is the token of the GOLDILOCK, it is required to access the GOLDILOCK wallet. The token will be registered as an ‘NEP-5 assest on the NEO Blockchain.
Users, customers will be able to make purchases of this token which is coulpled with the proprietary smart contract logic
LOCK token allows GOLDILOCK to provide users with a record of their node activity, while keeping user-owned data encrypted and locked away even from everyone including the GOLDILOCK team. In addition, LOCK is to be the accepted method of subscription payment for individual users on the GOLDILOCK Security Suite.
LOCK TOKEN ALLOCATION
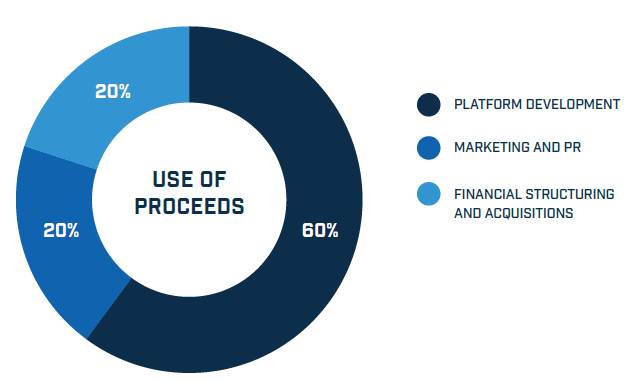
TOKEN PROCEEDS
USE CASE 1
Mr Kelemasco is a crypto enthusiast that has crypto coins in many blockchain technologies, he was happy from how much he has acquired without taking into consideration the safety of the coin.
Tragedy fell on him when several of his wallets were hacked and he lost millions of dollars in value. A friend introduces him to GOLDILOCK, he moves his assets to the technology and had rest of mind and lived happily

USE CASE 2
Mr Tunde is the Prince of Mbaise Kingdom and is also a chronic alcoholic drinker, he develops a serious health problem with his liver, where his liver was badly damaged and as such needed transplant and medical care. Since he was the prince, this vital information should not be known by his people. A serious hack was done on the hospital’s storage cloud and information was leaked.
He got lucky that the hospital was able to track down the hacker and conceal the information. The hospital apologizes and improved their IT knowledge, this led to the incorporation of GOLDILOCK and everything was returned back to normalcy

CONCLUSION
The global adoption of blockchain has suffered a lot due to security of funds and information. But with GOLDILOCK in place, a new breath of relieve and comfort will be seen
GOLDILOCK already ensures secured storage of very sensitive digital assets ranging from cryptocurrencies to data.
I believe that the joy of hackers will be caught short due to this platform and also users confidence will increase
To think that every sector of the economy benefits from this is a huge one and also a welcome development.
GOLDILOCK is indeed a gold lock.
MORE INFORMATION AND RESOURCES
Goldilock Website
Goldilock Whitepaper
Goldilock Tokenomics
Goldilock Telegram
Goldilock Discord
Goldilock LinkedIn
Goldilock Facebook
Goldilock Twitter
Goldilock Reddit
Goldilock Github
Goldilock Twitter

INTRODUCTORY VIDEO

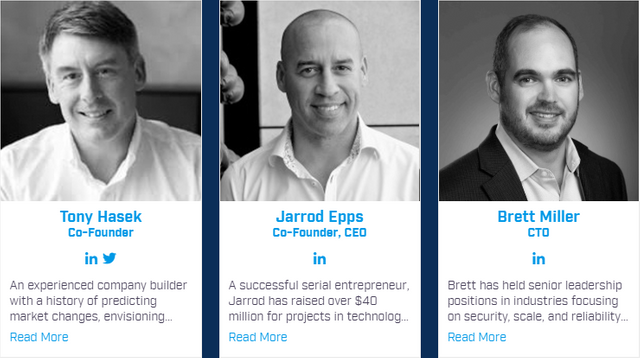
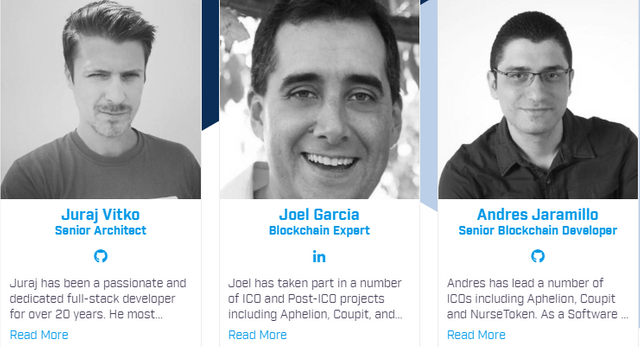
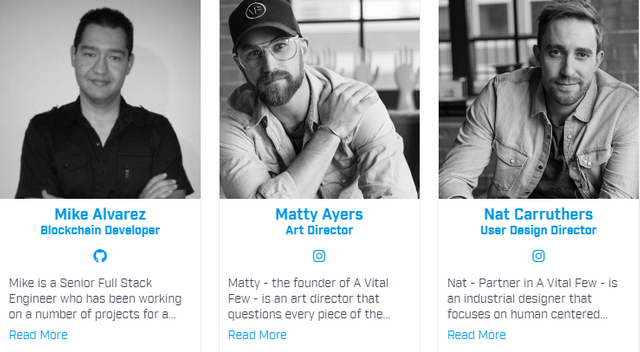
MEET THE TEAM
PARTNERS
ADVISORY TEAM
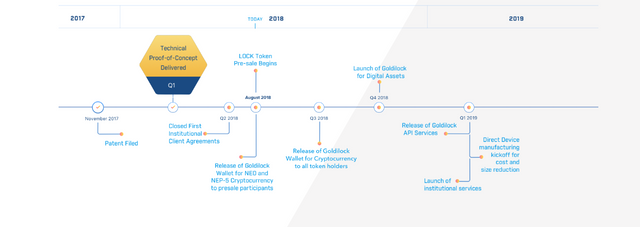
ROAD MAP

This is an @originalworks Contest
All images were gotten from Goldilock Website and
Goldilock Whitepaper

Twitter link
https://twitter.com/MrDonnest/status/1026947557593890816?s=20

goldilocktwitter
goldilock2018











Wow
See you at the top bro
Wanna see you hit that first price this time
Thanks boss. Let's just be optimistic.
This post has been submitted for the @OriginalWorks Sponsored Writing Contest!
You can also follow @contestbot to be notified of future contests!
Congratulations! This post has been upvoted from the communal account, @minnowsupport, by Donnest from the Minnow Support Project. It's a witness project run by aggroed, ausbitbank, teamsteem, someguy123, neoxian, followbtcnews, and netuoso. The goal is to help Steemit grow by supporting Minnows. Please find us at the Peace, Abundance, and Liberty Network (PALnet) Discord Channel. It's a completely public and open space to all members of the Steemit community who voluntarily choose to be there.
If you would like to delegate to the Minnow Support Project you can do so by clicking on the following links: 50SP, 100SP, 250SP, 500SP, 1000SP, 5000SP.
Be sure to leave at least 50SP undelegated on your account.
This is a good technology for the storage system.. Nice one @donnest.
#bigwaves