Introducing Goldilock to Dtube. What is Goldilock?
What is Goldilock?
How do you store your cryptocurrencies and sensitive digital data?
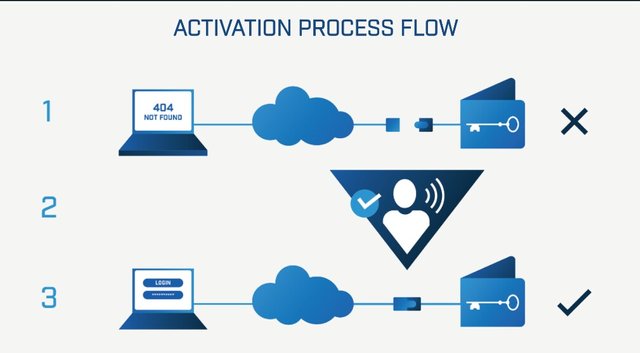
Goldilock is a revolutionary digital asset security system which acts as remotely disconnected cold storage until such time that the user needs access to their data for its intended purpose.
Goldilock's encrypted nodes remain vaulted offline, physically disconnected from the internet until a user brings their personal device online remotely via a non-IP (not over the internet) command, after which time they can access it using the same bank-level security mechanisms they would with other sensitive data. Once the user is finished using their node to complete transactions, allocate asset rights, or transfer specified data, the node then reverts to an isolated physical air gap environment, invisible and inaccessible from the internet.
Goldilock is built around the premise that anything connected to the internet can and will be hacked. The past few years have seen more than 3 billion data breaches across many sectors, from banking and credit, into personal health data and digital rights, through to billions of dollars stolen in the cryptocurrency industry, proving time and time again that no industry is safe from intrusion.
The inherent security vulnerabilities within internet and blockchain infrastructure are why Goldilock uses a physical air gap disconnection method. This means, as the name suggests, that the devices storing sensitive data are physically disconnected from the internet, remaining isolated in a vaulted location.
Current Storage Solutions
Current methods:
● Hot storage: Cloud storage, exchanges, online wallets, online multisig structures
● Cold Storage - personal USB hard drives, Trezor, Ledger Wallet, Xapo or Blockvault (the latter two being vaulted electronic storage for institutions, which takes days to bring online)
Hot Storage
Most individuals in the crypto space are familiar with the shortcomings associated with centralized asset storage methods.
The customer of an exchange or an online wallet generally has no idea or power over how their cryptocurrency is stored. The website could have security flaws, exposing all the user funds to hacks. There are a number of examples in recent history, most notably the famous Mt.Gox case, followed by more recent examples such as Coincheck losing over $500m in NEM, and just last month Bithumb and Coinrail. In 2018 alone, more than $750m in crypto assets have been stolen.
Personal Cold Storage
Personal cold storage offers vast security benefits over keeping your cryptocurrency or other sensitive data online. That being said, there are major issues when it pertains to losing/breaking the physical devices that keep your private information.
Problems with personal cold storage include:
● User must be tech-savvy, not conducive to mass adoption.
● Devices can be broken/lost, causing detrimental losses.
● Data is inaccessible without physical device present.
● Every major electronic hardware wallet has been hacked, including Ledger and John McAfee’s Bitfi wallet, released just last week.
● These solutions cannot be used by institutional clients for custody, leaving hundreds of billions of dollars on the sidelines until secure custody is truly solved.
● These methods apply to crypto only, and cannot be used for larger use-cases involving banks, credit agencies, digital rights holders, healthcare providers, nor any of the other major data custody providers who handle our sensitive data.
Application
There is a wide array of fields where Goldilock technology can be applied.
Goldilock can be used by individuals to store sensitive information, such as cryptocurrencies or personal files, or by larger institutions where security is a priority for their crypto or their customer data.
Identity
Digital personal identity data requires a high level of security. There are many services that require personal data to register, this can range from KYC to signing up for an insurance policy. Traditionally people handle the documents physically or scan and email the information required. This leaves huge security gaps, as your personal documents are stored online on your email account or on a drive, and are prone to hacks and malicious use.
Even with the introduction of blockchain identity services like CIVIC, losing your key means someone can steal your identity, and there not any safe back-up options for those keys. In this case, a provider like CIVIC can benefit from using Goldilock security services.
With Goldilock, users are granted access to their data and digital assets on a per need basis. After the user has finished performing their identity verification, for example, the data goes back offline, inaccessible for anyone to see or access.
Credit Score
Credit scoring companies have also been subject to hacker attacks. Recently, a well-known credit score company, Equifax, was attacked and the personal information of hundreds of millions of consumers was stolen. Consumers were then tasked with freezing their credit through a time-consuming and complex process, which later required them to jump through hoops to bring their credit back to active status – meaning they are again vulnerable.
Banks are partnering with Goldilock, integrating their security layer for larger accounts and for enacting wire transfers, with both being connected only for the duration of intended interaction of data with individual user accounts.
Wallet
Goldilock can be used to store cryptocurrency in a way that offers the security of cold storage, while maintaining the convenience of an online wallet.
Users are able to hold their cryptocurrencies with Goldilock, and the information will be stored offline until such a time that the user requests their individual encrypted node is connected to the internet using an analogue command off the internet, whereupon they can access their data via an encrypted channel over the internet after passing through bank-level security gateways.
Importantly, using the Goldilock model, the private key never leaves the individual node, meaning it cannot be stolen or corrupted while connected.
Voting Machines
The Goldilock patented security protocol can extend to very crucial and practical applications.
Consider it more as hardware that can be added to traditional voting machines. Those machines currently are online, all the time during an election. If each machine has a vaulted, encrypted node inside it which stores all vote data, and those machines in each physical location share a backup mechanism which is completely disconnected from the internet, those votes cannot be hacked. At the moment administrators wish to access the data remotely, they make the remote command to connect the node and deliver the data in a very short connection window thorugh our encrypted channel, thereby lessenning by 99.999% the amount of time machines are online, equally reducing the amount of time hackers have to fine and crack the machines to corrupt data.
Goldilock LOCK Token
LOCK is the utility token that will be used to provide a gateway for Goldilock services.
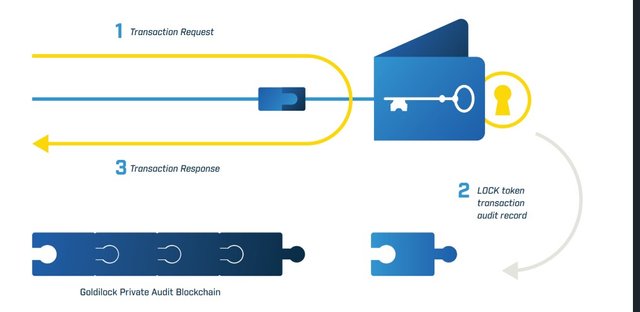
The LOCK token is required to access the Goldilock Wallet. When the user logs into the Goldilock Wallet, the Wallet will query the NEO public Blockchain to confirm the user’s public key address owns a LOCK token. If the user’s public key address owns a LOCK token, then the Goldilock Wallet will launch in the user’s browser. When the user is granted access, the Wallet will write audit information to our own Private Audit Blockchain. These audit entries will ensure that every time your private key is brought online, this access is written to immutable storage that can be queried from the Goldilock Wallet.
LOCK token allows Goldilock to provide users with a record of their node activity, while keeping user-owned data encrypted and locked away even from everyone including the Goldilock team.
NEO will be the first cryptocurrency to be integrated, with others following shortly thereafter.
The Goldilock Wallet service can be paid for on a subscription basis by LOCK.
Use-Case
Personal
Bob loves to travel. He has saved up enough money to quit his job and travel for a year. He will be travelling to big cities as well as remote locations, so he would like to minimize his luggage to essentials.
Throughout his trip, Bob will need:
● Documents - Passport, Driver's License, Visas, Insurance policies, etc.
● Finance – Cryptocurrency hardware wallet, banking USB key
While Bob was packing up his important documents in a small bag, he kept worrying about what would happen to him if he misplaced his documents and related hardware device. His entire trip would be ruined, and it would take him forever to replace all the lost documents.
Bob mentioned his worries to his friend, Alice, who mentioned Goldilock!
With Goldilock, Bob can rest easy. He can leave his documents and cryptocurrency wallets at home where they belong. There is no need for him to carry around such important items and risk losing it all.
Instead, he can store relevant data with Goldilock, and access his data whenever he needs it!
Commercial
A huge insurance company in New York, WeKeepInfoOnline Corporation, has been experiencing security issues. They use the highest layers of security protocols available today, and invest million in cyber security. Even with all of this, they are in constant fear of being infiltrated, since the data they store is extremely personal for their clients and any security breach would mean the end of their prospering business.
While they kept brainstorming ideas of how to improve their online protection, an engineer on the team brought up Goldilock.
The company immediately implemented Goldilock, and changed their name to WeDontKeepInfoOnline, propelling themselves to the forefront of information security. They can now sleep easy knowing that their data is invulnerable to hackers, since it is not online in the first place!
Goldilock provides an incredibly unique storage solution hence the slogan; it is "not hot storage, not cold storage, just right storage." Storage in such a way, that sensitive digital data can finally be fully protected.
For more information watch this short feature intro:
More Information & Resources:
Goldilock Website
Goldilock WhitePaper
Goldilock Tokenomics
Goldilock Telegram
Goldilock Discord
Goldilock Linkedin
Goldilock Facebook
Goldilock Twitter
Goldilock Reddit
Goldilock Github
you can aslo watch my video on youtube here my channel link
https://www.youtube.com/channel/UC6_XHdEKUonbY2RCgpS5JXw?view_as=subscriber

▶️ DTube
▶️ IPFS

This post has been submitted for the @OriginalWorks Sponsored Writing Contest!
You can also follow @contestbot to be notified of future contests!
You need to sync audio to the video :)
Ok @phoneinf i try my best to do it..
I can see..
Congratulations @kitani! You have completed the following achievement on Steemit and have been rewarded with new badge(s) :
Click on the badge to view your Board of Honor.
If you no longer want to receive notifications, reply to this comment with the word
STOPTo support your work, I also upvoted your post!
Congratulations @kitani! You have completed the following achievement on Steemit and have been rewarded with new badge(s) :
Click on the badge to view your Board of Honor.
If you no longer want to receive notifications, reply to this comment with the word
STOP