Announcement on Nuls Smart Contract No Vulnerability Risk
Recently, It is said BatchOverFlow data in the Ethereum Token smart contract resulted in the risk of overflow of various ERC-20Tokens, which caused a large negative impact on the market and investors.
Although the hacker attacks have not yet reached NULS, the NULS core technology team took initiative to review all smart contract ERC-20 codes. Keep in mind, all of NULS source code is a standard ERC-20 code. After the NULS core team reviewed overflow detection, there is no risk of overflow. We are clarifying this matter so investors can rest assured that all major exchange platforms for NULS transactions and withdrawals are secure.
Regarding ERC-20 Token code being attacked:
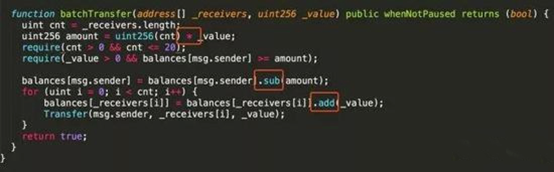
Its math operation did not use SafeMath nor did it do overflow checking.
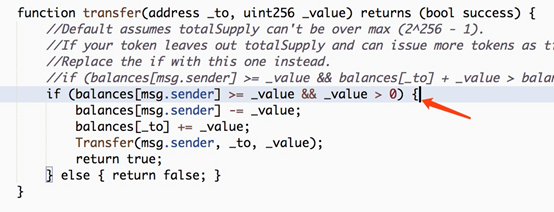
Again, NULS uses the standard ERC-20 code. It has been tested for overflow. There is no overflow problem.
NULS main net will soon be officially launched. After the completion of the public beta, token swapping will be carried out upon completion. We would like to welcome everyone to actively participate in the test phase and give your suggestions and feedback for any potential improvements.
NULS team
April 26, 2018
That's great to have NULS team publishing on Steem, don't forget to set your avatar!
thank you :)
Good Luck