Securing your LastPass account with 2FA

Having a decent password manager is probably the minimum level of security that you should have when you venture out onto the internet and start creating accounts. A password manager gives you the ability to easily store and generate random strings of unique passwords for all aspects of your digital life and like most security services/products the real value is measured in disaster avoided, which is a perspective that isn't really front and centre concern in daily life.
Most critical accounts like Google, Kucoin and Binance will all offer some sort of 2FA option, so it is something that you will want to activate as soon as you have the chance to make sure that your accounts are safe and sound!
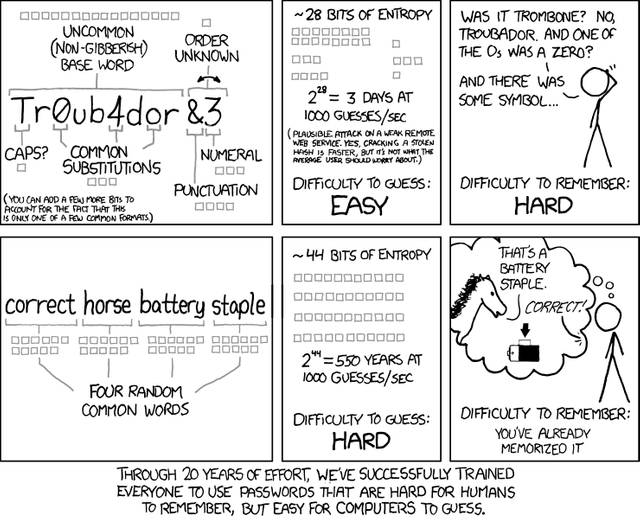
Unlike the offers to remember your password coming from your browser, LastPass encrypts your password database using your own master password (this needs to be strong as it now the focal point of your security). From there, you can generate lengthy random strings to act as unique passwords for your various accounts (or import your own) and LastPass will also store them. This means that they are easily accessible and securely stored and you don't need to know anything other than the Master Password.
I have also found that using a password manager is probably the easiest way to manage the key juggling required to safely use HIVE/STEEM. On HIVE/STEEM we have four separate keys that have different authorisation abilities. So, just as a quick recap:
MASTER: The GOD key, allows complete access to the account and authorises resetting of the other keys. Should NEVER be used a log-in method, stored securely and be very wary of anything that asks for this one!
ACTIVE: This is to handle all wallet interactions. It is of a higher level than the Posting key, so it can be used to authorise a dApp to do posting (votes, comments) activities on your behalf.
POSTING: The one that should be used for logging into front-ends. This just authorises posting, voting and commenting and is more than enough for most interactions with the HIVE/STEEM blockchain.
MEMO: for encrypting/decrypting wallet memos, currently the least often used.
Why would you secure your digital life?
Well, generally bad actors aren't really going to be interested in your personal life (unless you are rich or have some interesting history...) but you can be an interesting tool or stepping-stone to someone who is quite interesting to them. Keep in mind, a password manager is a basic minimum security step (that most people don't bother with) to prevent password reuse and insecure password generation... if you are really the target of a direct attack on your digital life, you are screwed and there is pretty much nothing you can do about that! Interestingly enough, if you are the target of a directed campaign, it is likely that bad actors will target the people around you first... to find the people that aren't using basic online security to get to you!
So, this is like many other things that afflict the world today... partly, the steps taken to use a password manager are for protecting yourself... and mostly it is about protecting the people around you. If climate change and Coronavirus has taught us anything... we, as a society, just don't give a crap about others!
Setting up 2FA

I tend to recommend LastPass as a the preferred password manager due to it's balance between security and ease-of-use. Sure, there are more secure options that don't involve having the encrypted password database stored online, but that is a bit of a abstract debate that doesn't take into account that most people will balance towards ease-of-use or NOTHING.
So, much of this guide is LastPass specific, but much of this 2FA based upon Time-based One Time Passwords (TOTP) is pretty standard with only the length of the symmetric key varying from vendor to vendor. It's pretty cool, well the mathematics is... the implementation is probably interesting for people who like coding!
As I had mentioned before, using a password manager means that the Master Password is now the weak point in your security as it is the single authorisation required to access your treasure trove of passwords. So, it is incredibly prudent to add 2FA (Second Factor Authorisation) as a second point of authorisation before anyone can proceed to decrypt the database of passwords.

So, from your LastPass vault, open the Account Settings option.

Navigate to the Multifactor options and select one of the free choices. These are apps that run on your phone (download ONLY from Play Store for Android or App Store for iOS!) that run an implementation of the TOTP protocol to give you new 6 digit keys every 30 seconds. This is pretty much like what you have with bank authenticators, but in that case the symmetric generation key is hardwired into the device.
I personally prefer to use the Google Aunthenticator as I trust that they will be around long enough to keep their app up to date with any critical security problems. They also aren't storing your symmetric key, and I'm not sure that all of them do that... So, I would stick to the LastPass, Google or Microsoft ones (and their less likely to be acquired by a different company and have their services "integrated").
However, for the completely paranoid... the last option (Grid) is a pen and paper version of the the TOTP implementation. GLHF... but I hope you remembered to secure your printer!

The other options are worth a mention, but they aren't really aimed at the regular user. Yubico is a USB stick that functions as the second factor and likewise for the fingerprint/RFID card reader. The idea is still to have one other object required to authenticate the access to the password vault other than the master password.
STEP 1: Go to your Google Play Store or Apple App Store and get your preferred Authenticator app and install on your phone or smart device. Make SURE that it is the legitimate one from the correct publisher (a hint will be the number of times that it has been downloaded as well as the developer contact details).
STEP 2: Make sure that you have a Security Phone/Email setup from the Settings-->General page. This is used to send a single use password in the case that you need to perform a recovery (ie, you have lost one of the access tokens, the master password or the Authenticator (2FA) codes). It is best to use an email that is NOT your primary email or your normal phone number. Sim Swapping is a real thing!
STEP 3: From the LastPass settings (Multifactor) click the pencil icon to take an action and select "set up/enable".
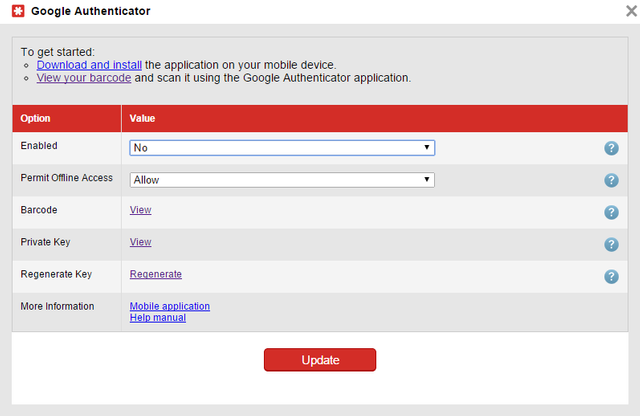
STEP 4: This screen should show up on your computer. There will be a barcode (QR code) and a Private Key (sequence of letters and numbers) which are two representations of the same symmetric key that you need to share with LastPass to ensure that you are generating the same sequence of one time passwords that LastPass expects to receive from you. It is symmetric as you share the same ciphering key (compared to blockchain and cryptocurrencies which harness asymmetric cryptography, aka public-private key cryptography).
STEP 5: Although it is tempting to just scan the QR code with your Authenticator app and just write down the alphanumeric private key, this is a really BAD idea! As that means that the QR code is definitely correct, but you are NOT sure about the backup!
Better to write down the alphanumeric in your notepad or wherever you are storing it offline. Then input the alphanumeric code FROM THE NOTEPAD! This means that any mistakes in the backup is caught now, and NOT when you are having a disaster emergency because you lost your phone!
An alternative is to have two devices, one to scan the QR code and another to copy as described above. That way you have one electronic backup as well as the handwritten one for a bit of extra redundancy.
To complete the setup, you will be prompted for the code to make sure that you have the right symmetric key producing the same sequence of numbers. If you had the code wrong (it will produce vastly different codes), then it will not complete the setup (that would lock you out!) and you have to start again.
STEP 6: After enabling the two factor (2FA), when you log into the LastPass vault, you will be required to authorise the computer that you are accessing it one. This means that you will need the Master Password PLUS the code from the Authenticator.
Then you can authorise the machine as a "trusted device" which will not need to be authenticated again for 30 days or if you revoke the authorisation through the settings panel on LastPass.
Conclusion
A Password Manager is a minimum basic level of security for online activities that most people don't bother with. This means that much of their online identities are vulnerable due to password reuse, weak password generation and insecure storage of passwords. Good digital security is not only important for yourself, but for all the people that you know or might have even a passing digital connection with.
A good password manager like LastPass fixes these problems but it does introduce the critical attack point of the Master Password. Thus, it is prudent to introduce a second factor to authenticate access and manage trusted devices and to shore up this potential vulnerability. Of course, keeping an eye on the trusted devices and IPs of attempted logins is also a pretty useful as well!
Coin Tracking
Looking for a quick and easy way to keep track of your cryptocurrencies? Coin Tracking offers a free service that includes manual tracking or automatic tracking via APIs to exchanges, allowing you to easily track and declare your cryptocurrencies for taxation reports. Coin Tracking can easily prepare tax information sheets that are catered to each countries individual taxation requirements (capital gains, asset taxation, FIFO). Best to declare legally and not be caught out when your crypto moons and you are faced with an unexpected taxation bill (unless you are hyper secure and never attach any crypto with traceable personal information, good luck with that!).
Keep Your Crypto Holdings Safe with Ledger
Ledger is one of the leading providers of hardware wallets with the Ledger Nano S being one of the most popular choices for protecting your crypto currencies. Leaving your holdings on a crypto exchange means that you don’t actually own the digital assets, instead you are given an IOU that may or may not be honoured when you call upon it. Software and web based wallets have their weakness in your own personal online security, with your private keys being vulnerable in transit or whilst being stored upon your computer. Paper wallets are incredibly tiresome and still vulnerable to digital attacks (in transit) and are also open to real world attacks (such as theft/photography).
Supporting a wide range of top tokens and coins, the Ledger hardware wallet ensures that your private keys are secure and not exposed to either real world or digital actors. Finding a happy medium of security and usability, Ledger is the leading company in providing safe and secure access to your tokenised future!

Account banner by jimramones



I've never used one, but maybe I should start. I keep them backed up offline, and have a system that works well enough for password security, but it could probably be simplified and improved.
I know some people that use the same password for everything, and it's something like their name combined with date of birth. Despite telling them so many times, some people just don't see how risky that is and don't even want to acknowledge it.
This is a very informative article you've published, thank you for sharing.
My pleasure... a password manager isn't foolproof, and it means that there are different attack vectors and vulnerabilities, but it is more secure against clipboard attacks and attacks on unencrypted storage....
The problem is that is risky, but the risk might not be borne by the person who takes security less seriously. Just like most societal things (like corona and the environment) the costs are borne by someone else!
Thank you for sharing very useful information. What can you say about HOTP algorithm? And how are one-time passwords for websites generated in general?
Your article was very interesting and informative. Unfortunately, many people really neglect their security and do not use at least 2FA. Personally, to avoid unnecessary risks, I use a powerful tool password otp generator based on (HOTP) Algorithm. Since protection systems built using HOTP are highly reliable and resistant to common cryptographic attacks.