Crypto Academy / Season 3 - week 4 / Homework Submission Post for Professor @pelon53 / Root Hash and Merkel Tree
Introduction
.png)
Hello All proofer and students. This is @mousumimou. I read the lecture thoroughly for more than two time and now after getting the points, i am going to do my homework task about Hash Root and Markle for professor @pelon53.
Questions:-1
Hash rate
Hashrate is a proportion of the computational Power each second utilized when mining. All the more just, it is the speed of mining. It is estimated in units of hash which means the number of computations each second can be performed. Machines with a high hash power are exceptionally effective and can handle a great deal of information in a solitary second. BTC, the hashrate demonstrates the occasions hash values are calculated for PoW consistently.As the arrangement reached a hash measure of 10 Th/s, it destined it might brew 10 trillion calculations every second.
Question 2
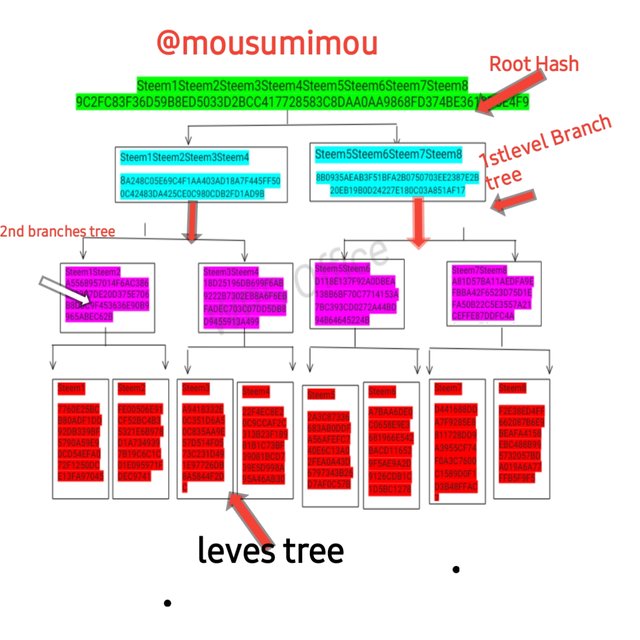
Make the following Merkle Tree: Transaction (tree leaves): Steem1; Steem2; Steem3; Steem4; Steem5; Steem6; Steem7; Steem8.
To create the Merkle tree, firstly generate the tree leaves hashes.
Tree leaves Hash
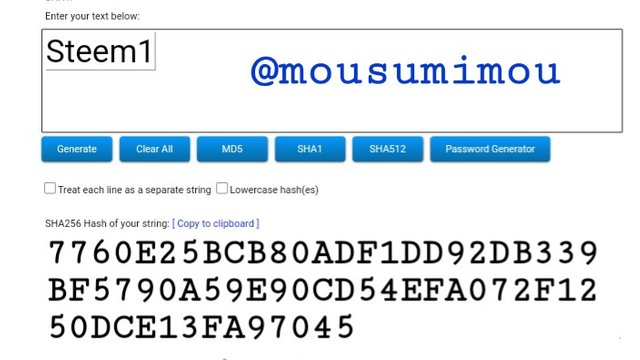
Steem1
Hash
7760E25BCB80ADF1DD92DB339BF5790A59E90CD54EFA072F1250DCE13FA97045
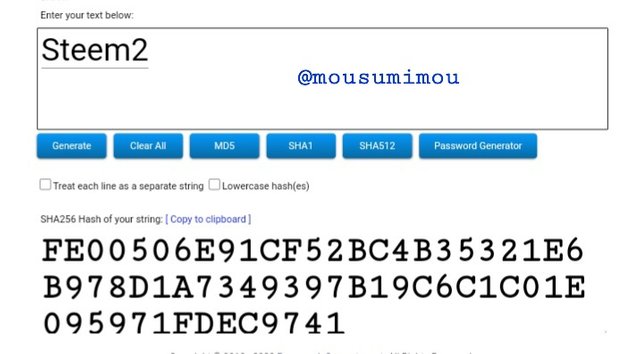
Steem2
Hash
FE00506E91CF52BC4B35321E6B978D1A7349397B19C6C1C01E095971FDEC9741
Steem3
Hash
--
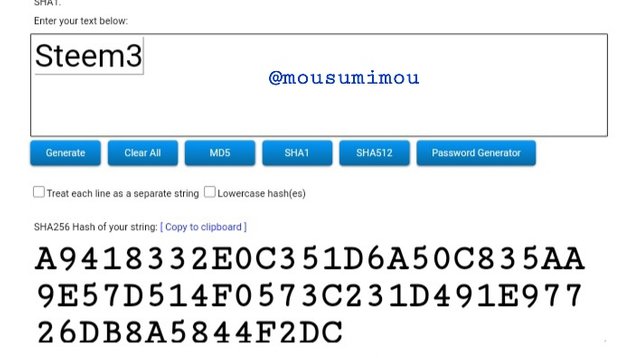
A9418332E0C351D6A50C835AA9E57D514F0573C231D491E97726DB8A5844F2DC
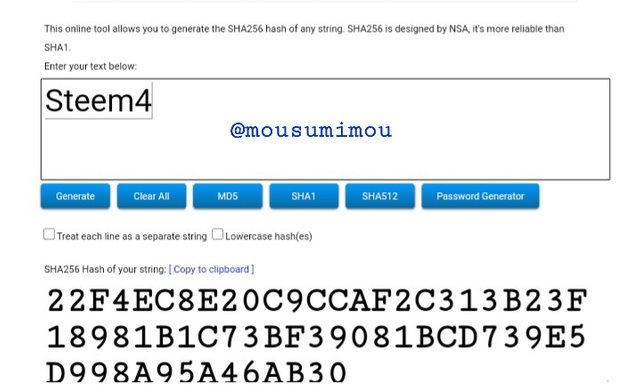
Steem4
Hash
22F4EC8E20C9CCAF2C313B23F18981B1C73BF39081BCD739E5D998A95A46AB30
Steem5
Hash
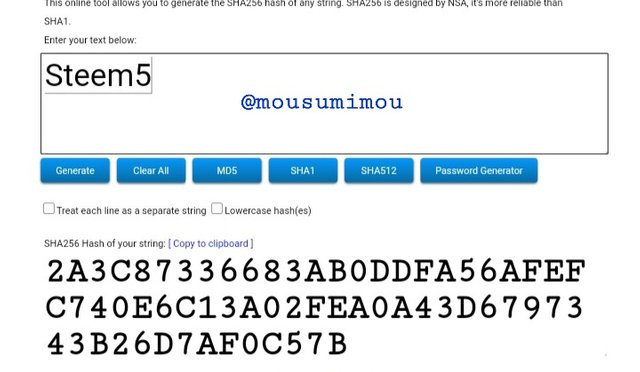
2A3C87336683AB0DDFA56AFEFC740E6C13A02FEA0A43D6797343B26D7AF0C57B
Steem6
Hash
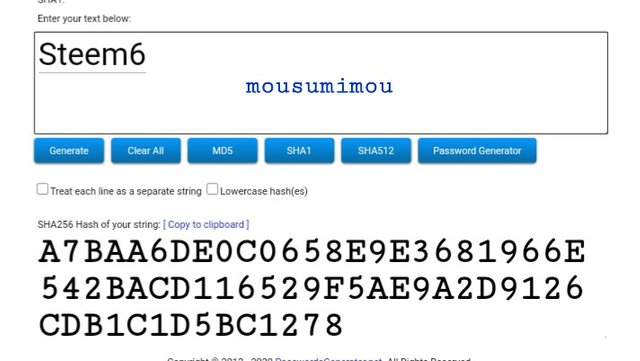
A7BAA6DE0C0658E9E3681966E542BACD116529F5AE9A2D9126CDB1C1D5BC1278
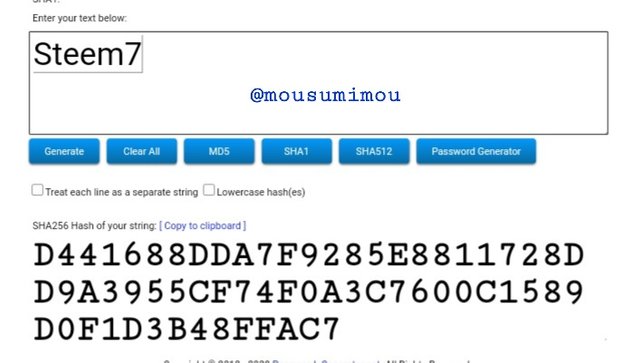
Steem7
Hash
D441688DDA7F9285E8811728DD9A3955CF74F0A3C7600C1589D0F1D3B48FFAC7
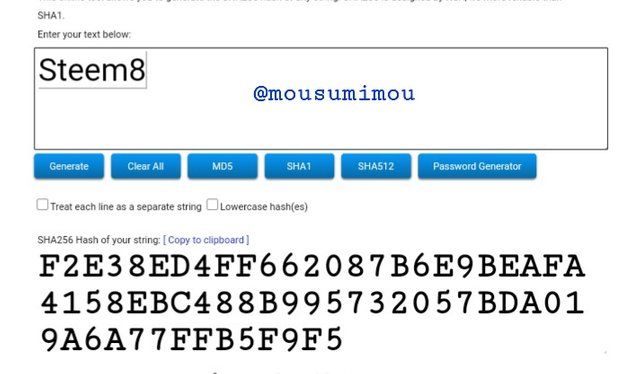
Steem8
Hash
F2E38ED4FF662087B6E9BEAFA4158EBC488B995732057BDA019A6A77FFB5F9F5
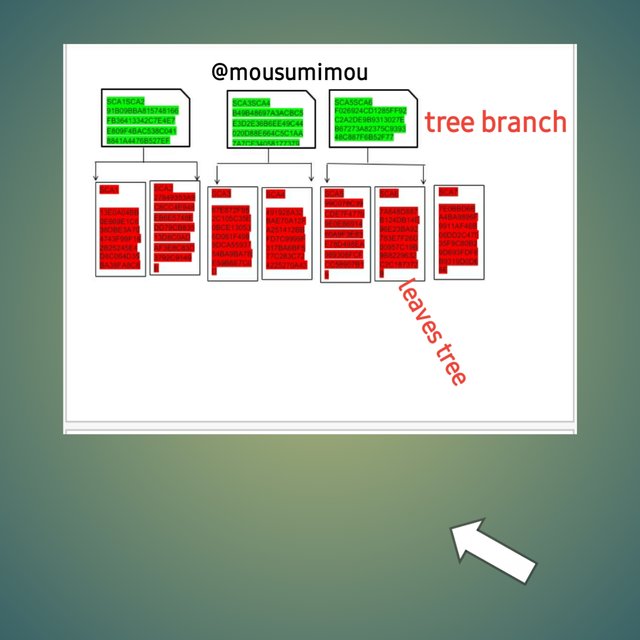
The next step in the Merkle trees is generating the branches.
Tree Branches hash
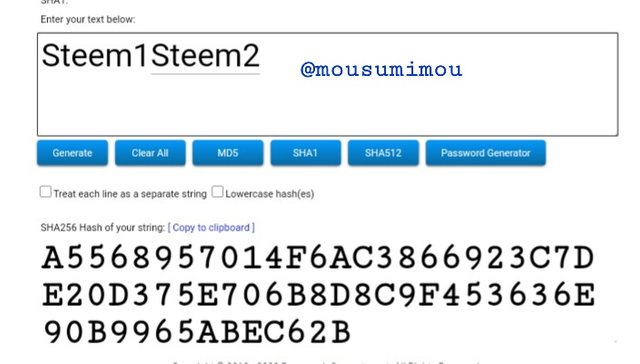
Steem1Steem2
Hash
A5568957014F6AC3866923C7DE20D375E706B8D8C9F453636E90B9965ABEC62B
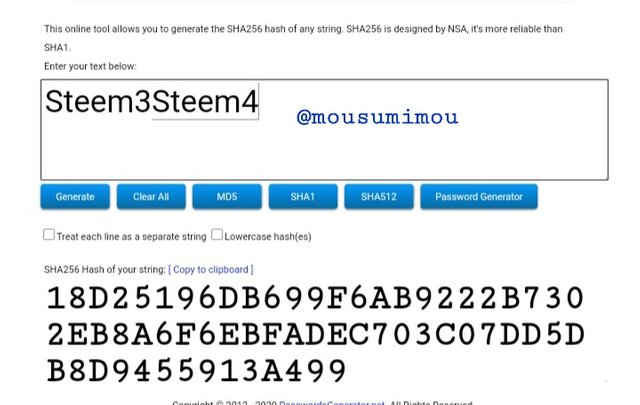
Steem3Steem4
Hash
18D25196DB699F6AB9222B7302EB8A6F6EBFADEC703C07DD5DB8D9455913A499
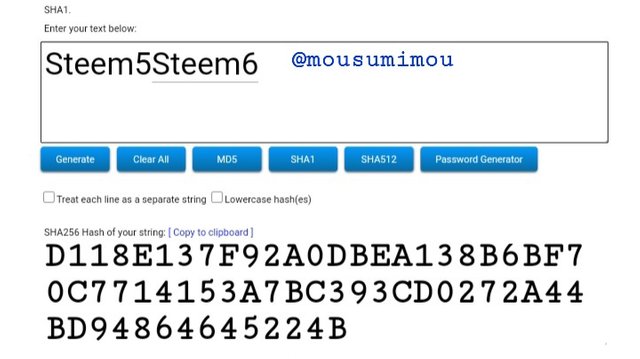
Steem5Steem6
Hash
D118E137F92A0DBEA138B6BF70C7714153A7BC393CD0272A44BD94864645224B
Steem7Steem8
Hash
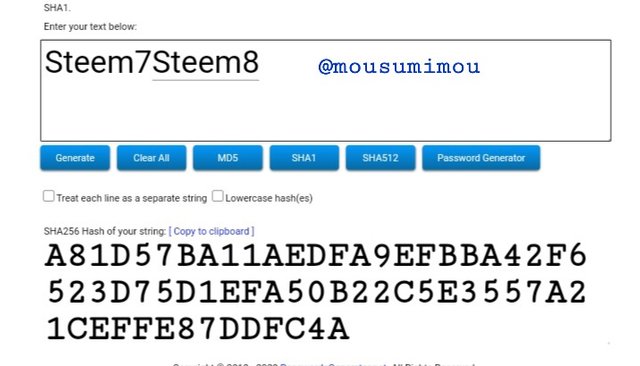
A81D57BA11AEDFA9EFBBA42F6523D75D1EFA50B22C5E3557A21CEFFE87DDFC4A
The next step in the Merkle trees is generating the second-level branches hash.
Second Level Tree Branches hash
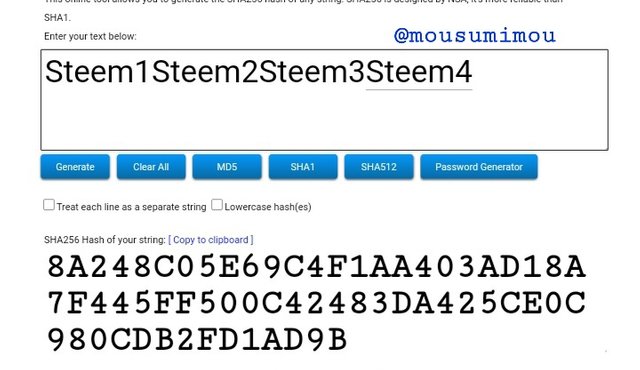
Steem1Steem2Steem3Steem4
Hash
8A248C05E69C4F1AA403AD18A7F445FF500C42483DA425CE0C980CDB2FD1AD9B
Steem5Steem6Steem7Steem8
Hash
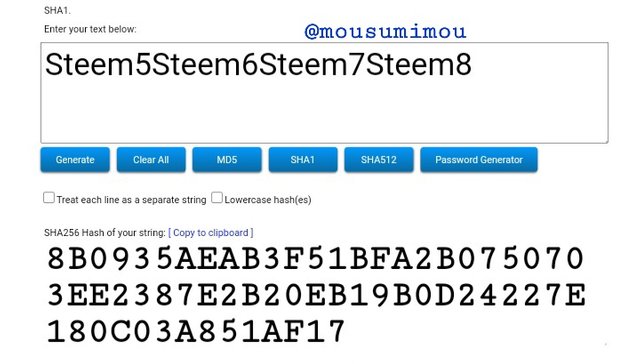
8B0935AEAB3F51BFA2B0750703EE2387E2B20EB19B0D24227E180C03A851AF17
The next step in the Merkle trees is generating a Root hash.
Root hash
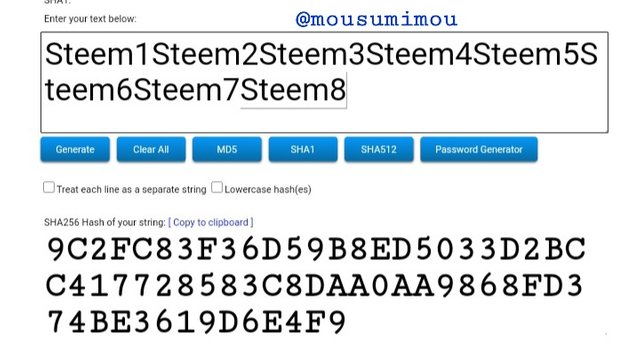
Steem1Steem2Steem3Steem4Steem5Steem6Steem7Steem8
Hash
9C2FC83F36D59B8ED5033D2BCC417728583C8DAA0AA9868FD374BE3619D6E4F9
The next step is creating the tree of the inputs and hashes
Merkle Tree
To make the Merkle tree, first generate the tree leaves hashes.
Tell the steps to follow to verify if Steem6 is included in the Markle Tree.
Source
To verify that Steem6 is included in the root hash for the Merkle tree, the user verifying will need to access the following.
Hash of Steem5
Hash of Steem7Steem
Hash Steem1Steem2Steem3Steem4
Step 1
Calculate the hash of Steem6
Step 2
Since the hash of Steem5 , Compute the hash of Steem5 and Steem6. It will give the hash
Steem5Steem6
Step 3
Since the hash of Steem7Steem8 is known, Compute the hash of Steem5Steem6 and Steem7Steem8.
It will give the hash Steem5Steem6Steem7Steem8
Step 4
As the hash of Steem1Steem2Steem3Steem4
Compute hash of Steem1Steem2Steem3Steem4 and Steem5Steem6Steem7Steem8
It will give the Merkle root hash
Steem1Steem2Steem3Steem4Steem5Steem6Steem7Steem8
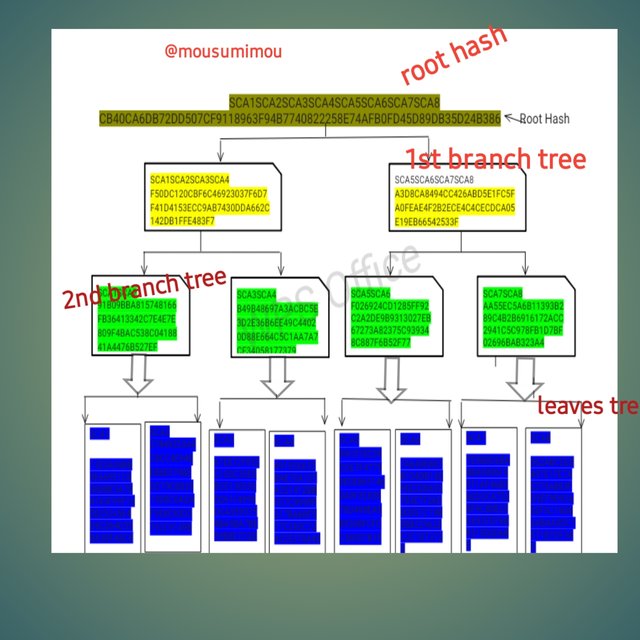
3.https://passwordsgenerator.net/sha256-hash-generator/ you must place each complete hash in the Merkle Tree.Transaction (tree leaves): SCA1; SCA2; SCA3; SCA4; SCA5; SCA6; SCA7; SCA8. Explain each step, show screenshots.
Tree leaves Hash
SCA1
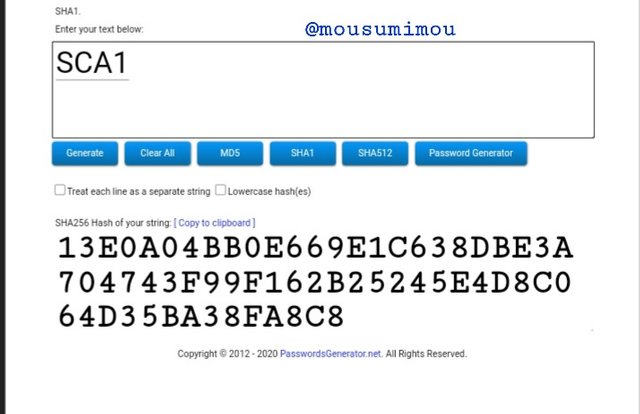
Hash
13E0A04BB0E669E1C638DBE3A704743F99F162B25245E4D8C064D35BA38FA8C8
SCA2
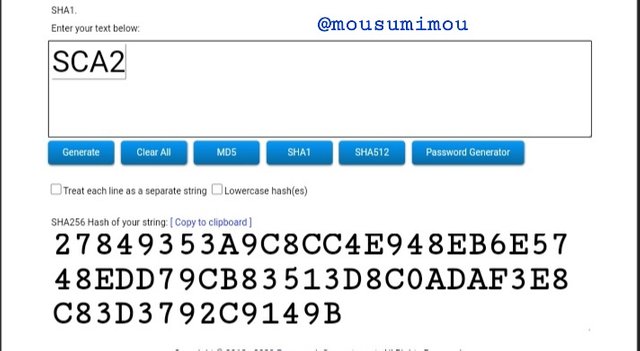
Hash
27849353A9C8CC4E948EB6E5748EDD79CB83513D8C0ADAF3E8C83D3792C9149B
SCA3
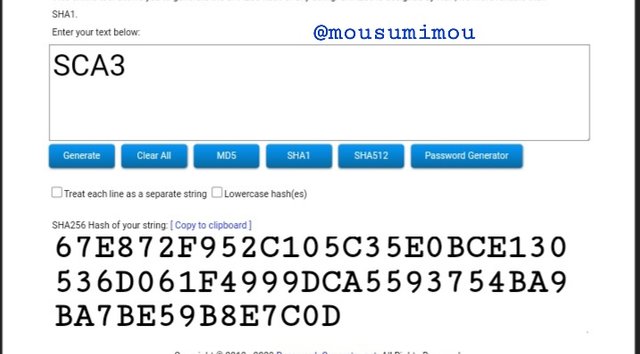
Hash
67E872F952C105C35E0BCE130536D061F4999DCA5593754BA9BA7BE59B8E7C0D
SCA4
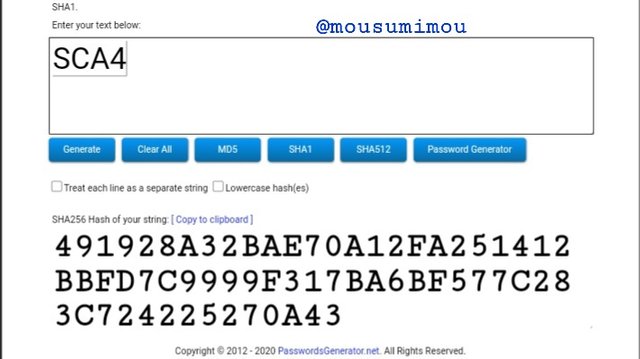
Hash
491928A32BAE70A12FA251412BBFD7C9999F317BA6BF577C283C724225270A43
SCA5
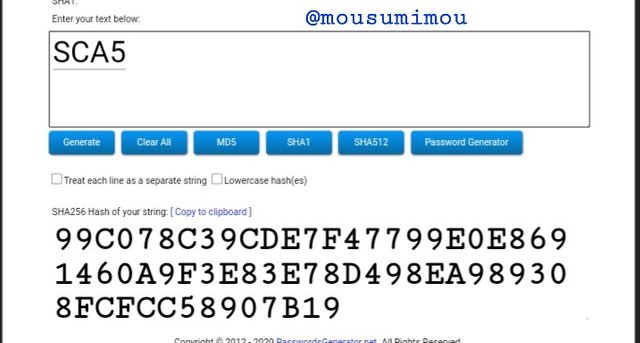
Hash
99C078C39CDE7F47799E0E8691460A9F3E83E78D498EA989308FCFCC58907B19
SCA6
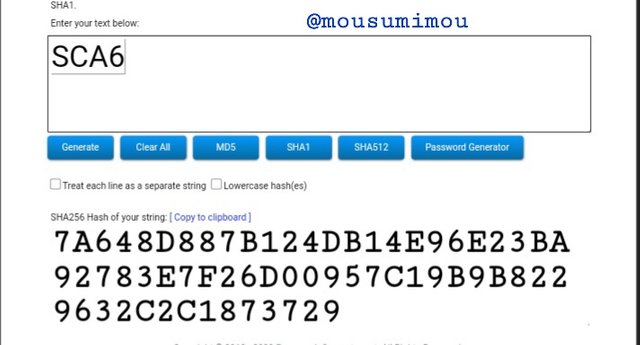
Hash
7A648D887B124DB14E96E23BA92783E7F26D00957C19B9B8229632C2C1873729
SCA7
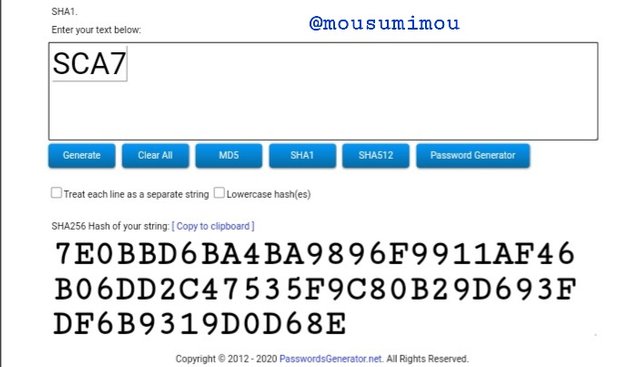
Hash
7E0BBD6BA4BA9896F9911AF46B06DD2C47535F9C80B29D693FDF6B9319D0D68E
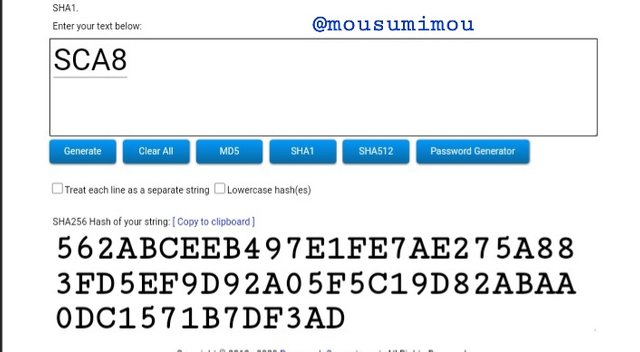
SCA8
Hash
562ABCEEB497E1FE7AE275A883FD5EF9D92A05F5C19D82ABAA0DC1571B7DF3AD
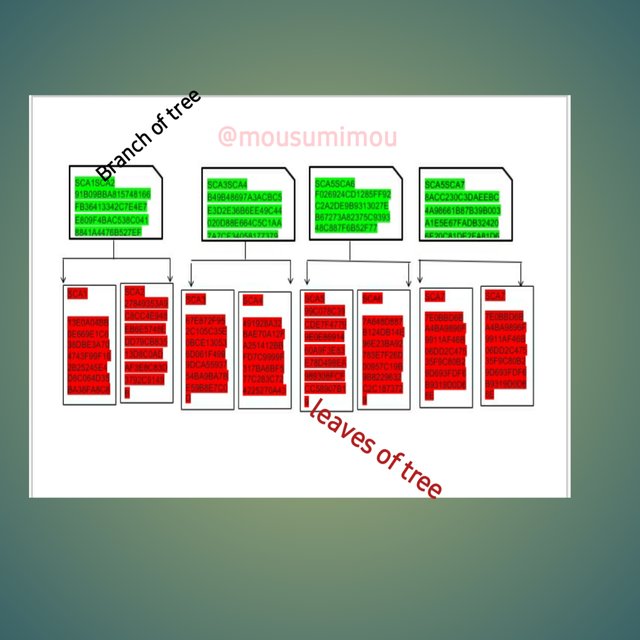
The next step in the Merkle trees is generating the branches.
Tree Branches hash
SCA1SCA2
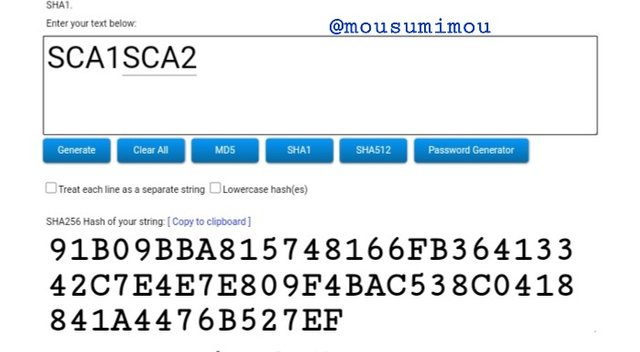
Hash
91B09BBA815748166FB36413342C7E4E7E809F4BAC538C0418841A4476B527EF
SCA3SCA4
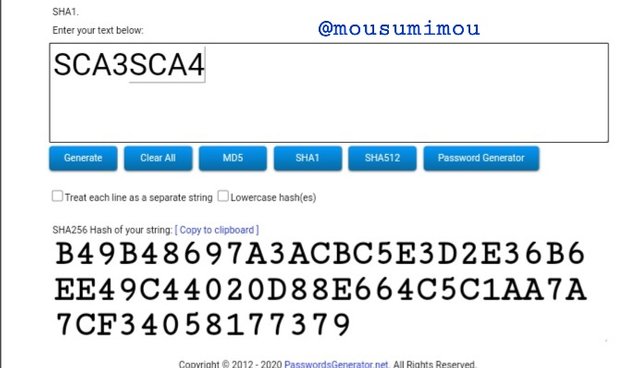
Hash
B49B48697A3ACBC5E3D2E36B6EE49C44020D88E664C5C1AA7A7CF34058177379
SCA5SCA6
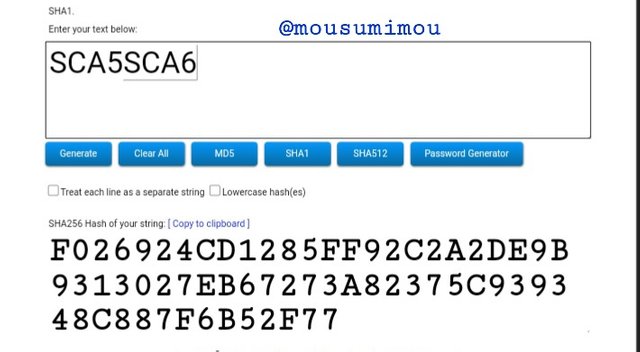
Hash
F026924CD1285FF92C2A2DE9B9313027EB67273A82375C939348C887F6B52F77
SCA7SCA8
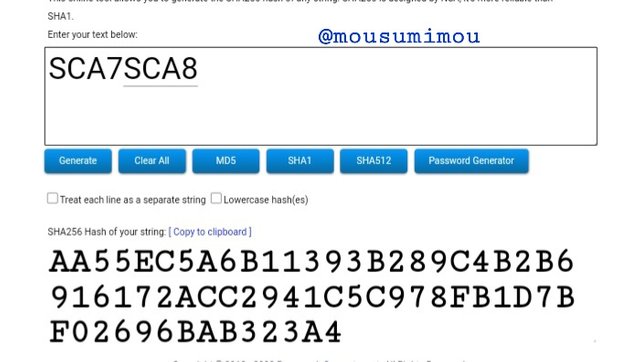
Hash
AA55EC5A6B11393B289C4B2B6916172ACC2941C5C978FB1D7BF02696BAB323A4
The next step in the Merkle trees is generating the second-level branches hash.
Second Level Tree Branches hash
SCA1SCA2SCA3SCA4
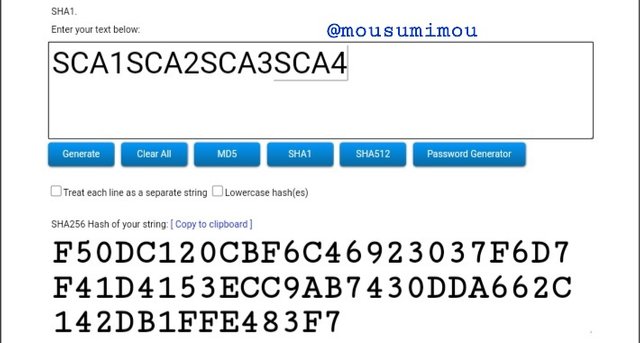
Hash
F50DC120CBF6C46923037F6D7F41D4153ECC9AB7430DDA662C142DB1FFE483F7
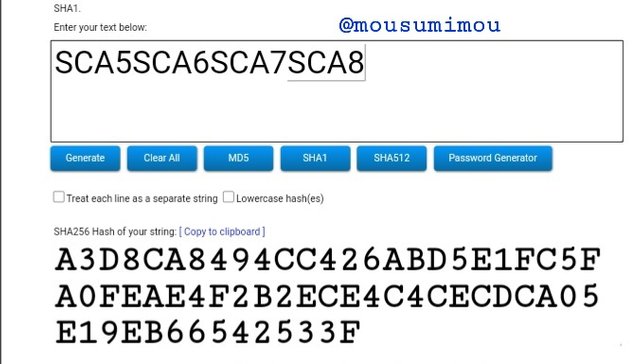
SCA5SCA6SCA7SCA8
Hash
A3D8CA8494CC426ABD5E1FC5FA0FEAE4F2B2ECE4C4CECDCA05E19EB66542533F
The next step in the Merkle trees is generating a Root hash.
Root hash
SCA1SCA2SCA3SCA4SCA5SCA6SCA7SCA8
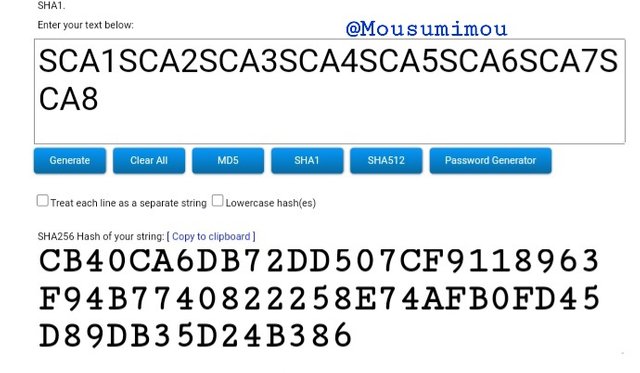
Hash
CB40CA6DB72DD507CF9118963F94B7740822258E74AFB0FD45D89DB35D24B386
If the number of leaves on the tree is odd, what should you do? Explain.
If the number of leaves on the Merkel Tree is odd we will not be able to compute the root hash reason it was decorated in a system to be compute in even numbers(2,4,6). as such the end leaf should be uncertain in other to become a master hash to engaged other branches
The tree above have seven leaves, so we should be uncertain the ends leaf by marking another SCA7 which is then submerged with SCA7 to get SCA7SCA7 as its main hash and from here we can proceed to the highe step branches as well as root hash.
Conclusion
We know that a hash is a alphanumeric code of fixed length that is generated by turn into any data to have is ambiguous .Merkle tree is a data processing that remaina all the hash codes for the transactions that are express throughout block. Hash system is totally strong and reliable. We user use this security system than fell secured. This lessons it too much important for everyone tader..