Crypto Academy Season 3 - week 4 | Homework Post for Professor @pelon53 | Root Hash and Merkel Tree
Thank you very much @pelon53 for this wonderful lecture. I really learned a lot from it
Here is my assignment.
Introduction
Hashes are functions that can convert data into compressed characters of both letters and alphabets in such a unique way that the data cannot be duplicated. With the aid of hashes, new blocks in the blockchain are connected to blocks already on the network. They provide blocks with unique and ideal identities to enhance accessibility and security in transactions.
Hashes connect numerous information about blocks in pairs till it reaches the last block which will then receive information on all the hashes and transactions on the blockchain networks.
Hashing data on a block enhances security and improves reliability which makes it easy to operate in mining cryptocurrencies. In mining coins, when there are large data, it becomes difficult for miners to handle. They will have to confirm the data on every block before a transaction can be verified which consumes time. But when all hashes can be classified into one hash called the root hash, this lengthy process can be avoided. This way, instead of verifying all the hashes on the block, the root hash can be verified instead.
Hash Rate
In cryptocurrency mining, a lot of hash algorithms have to be solved. The calculations of these algorithms are performed by supercomputers powered with great performance and speed. However, these computers are not of the same power and speed which means solving the algorithms is performed faster on some computers than others. How fast these computers solve the algorithms is known as Hash rate.
Hash rate, also known as hash power is the measure of how efficiently and effectively a machine mines during cryptocurrency mining. The greater the hash rate of a miner, the greater the speed at which a miner can solve a hash algorithm.
It is measured by the second. It is represented mathematically as Hash rate = total hash functions solved/time. Its SI unit is H/s which means hash per second.
Using the formula above to demonstrate how it is calculated, let’s consider a computer that solved 600000 hashes in 0.7 seconds, the hash rate will be = 600000/0.7 = 857142.857 H/s.
Hash rate is not only affected by the computer used; the cryptocurrency that is being mined also affects the hash rate. Different cryptocurrencies have different mining rates.
A demerit of hash rate is, there can be a situation where miners or a group of miners take control of more than 50% of the mining hash rate of the network, this is known as 51% attack. This way, they control a majority of the network and can solve algorithms way faster than others and this allows them to be able to reverse past transactions that need to be confirmed and re-spend the coins. This interrupts the confirmation of new transactions.
For example, if attackers spend 5ETH to purchase a product and cancel the transaction before it is confirmed, the 5ETH is brought back to their account which they can re-spend.
Also, a higher hash rate comes at a higher cost. Computers with a higher hash rate consume a lot of electricity. The higher the hash rate, the higher the energy consumed.
Merkel Tree
A Merkel Tree is a structure that encodes the data of a blockchain in a very secure way. It allows for very quick verification of the data of the blockchain and also makes it easy to move huge amounts of data from one node to another. It is also known as a hash tree or binary hash tree.
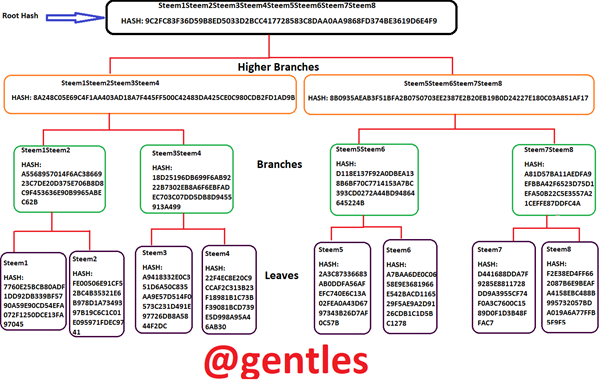
The Merkel tree has hashes at its bottom called leaves which continue up to other hashes in the middle, called branches they also build up to a single hash at the top known as the Root hash.
It is very useful as it enables users to confirm a certain transaction without having to download the whole blockchain which is very huge. It was proposed by Ralph Merkel and also resembles a tree hence the name Merkel Tree.
Make the following Merkle Tree:
Transaction (tree leaves): Steem1; Steem2; Steem3; Steem4; Steem5; Steem6; Steem7; Steem8
The steps commence from visiting the website https://passwordsgenerator.net/sha256-hash-generator/ and input the leaves one after the other to produce their hashes.
• Steem1
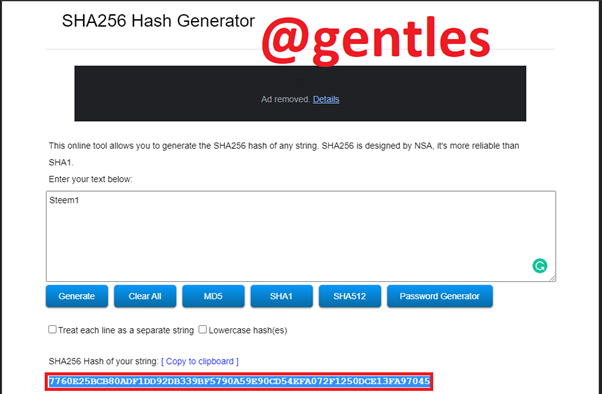
HASH: 7760E25BCB80ADF1DD92DB339BF5790A59E90CD54EFA072F1250DCE13FA97045
• Steem2
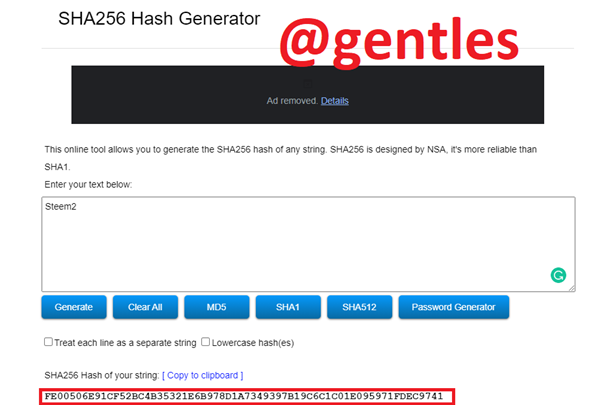
HASH: FE00506E91CF52BC4B35321E6B978D1A7349397B19C6C1C01E095971FDEC9741
• Steem3
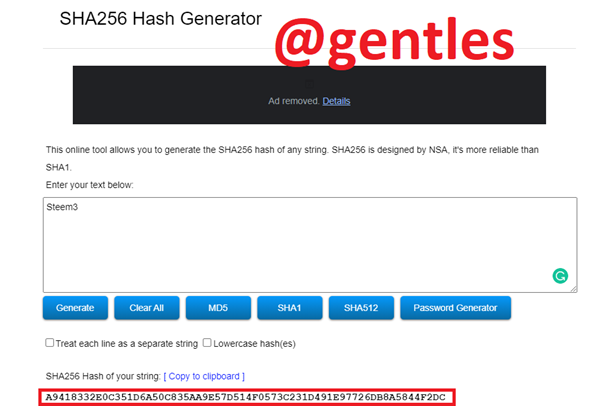
HASH: A9418332E0C351D6A50C835AA9E57D514F0573C231D491E97726DB8A5844F2DC
• Steem4
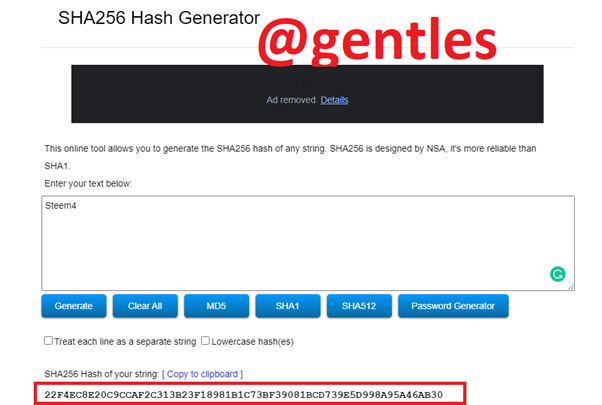
HASH: 22F4EC8E20C9CCAF2C313B23F18981B1C73BF39081BCD739E5D998A95A46AB30
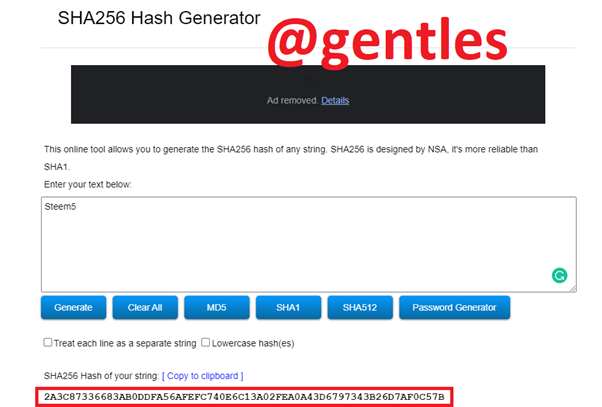
• Steem5
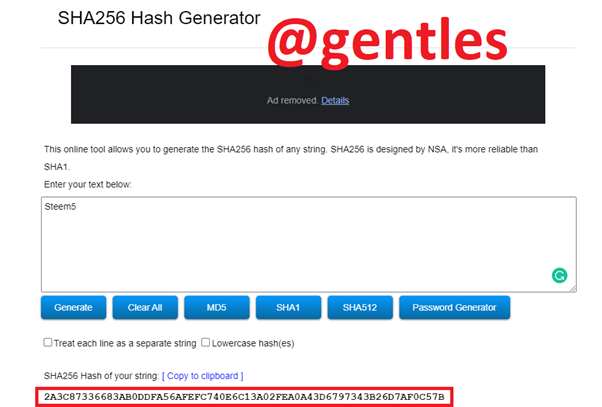
HASH: 2A3C87336683AB0DDFA56AFEFC740E6C13A02FEA0A43D6797343B26D7AF0C57B
• Steem6
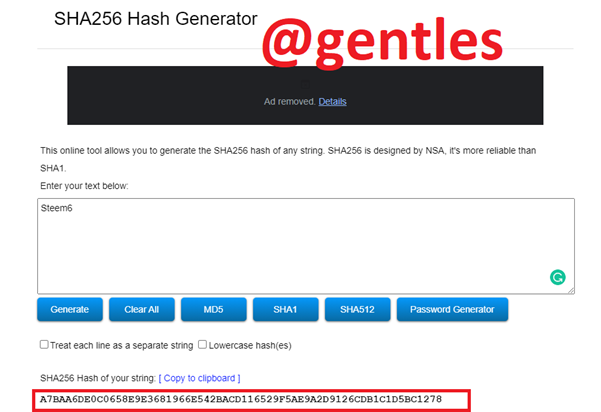
HASH: A7BAA6DE0C0658E9E3681966E542BACD116529F5AE9A2D9126CDB1C1D5BC1278
• Steem7
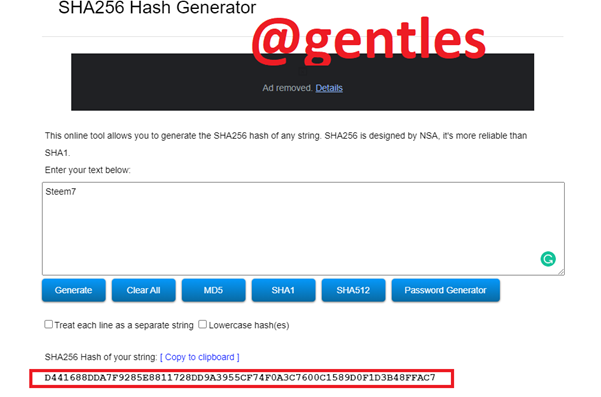
HASH: D441688DDA7F9285E8811728DD9A3955CF74F0A3C7600C1589D0F1D3B48FFAC7
• Steem8
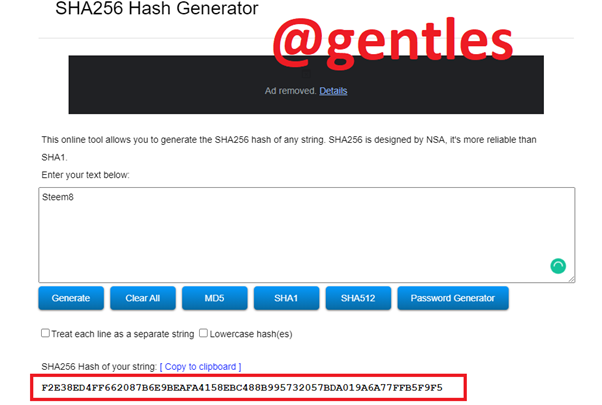
HASH: F2E38ED4FF662087B6E9BEAFA4158EBC488B995732057BDA019A6A77FFB5F9F5
Now I will continue by generating the Merkel Tree branches hash;
• Steem1Steem2
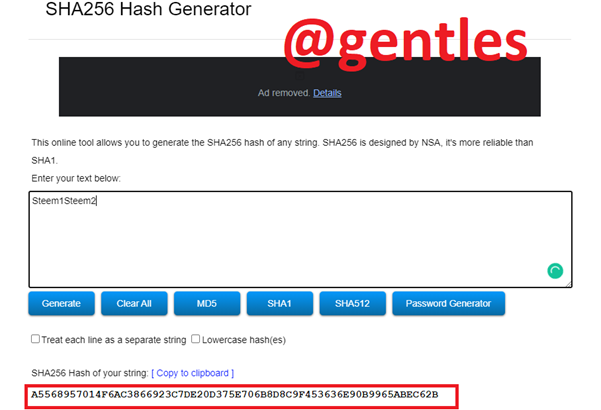
HASH: A5568957014F6AC3866923C7DE20D375E706B8D8C9F453636E90B9965ABEC62B
• Steem3Steem4
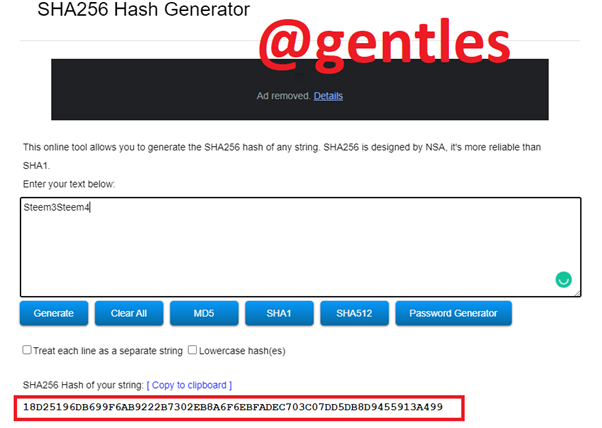
HASH: 18D25196DB699F6AB9222B7302EB8A6F6EBFADEC703C07DD5DB8D9455913A499
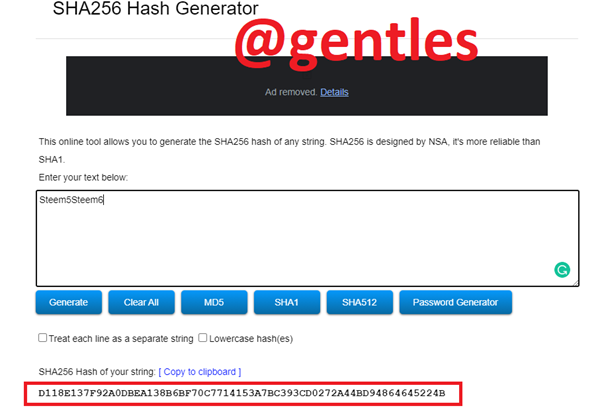
• Steem5Steem6
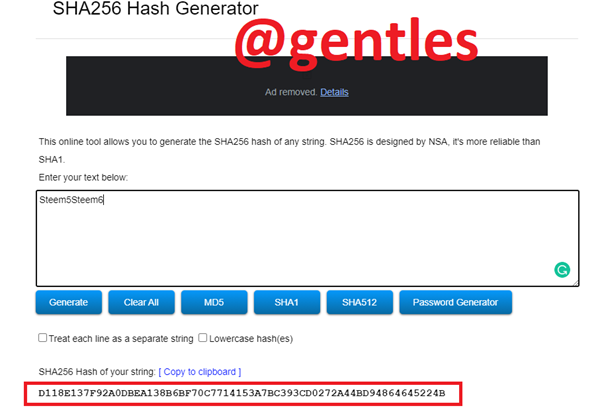
HASH: D118E137F92A0DBEA138B6BF70C7714153A7BC393CD0272A44BD94864645224B
• Steem7Steem8
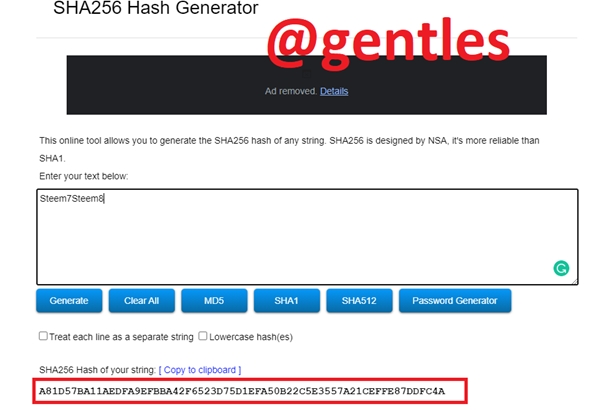
HASH: A81D57BA11AEDFA9EFBBA42F6523D75D1EFA50B22C5E3557A21CEFFE87DDFC4A
Higher branches;
• Steem1Steem2Steem3Steem4
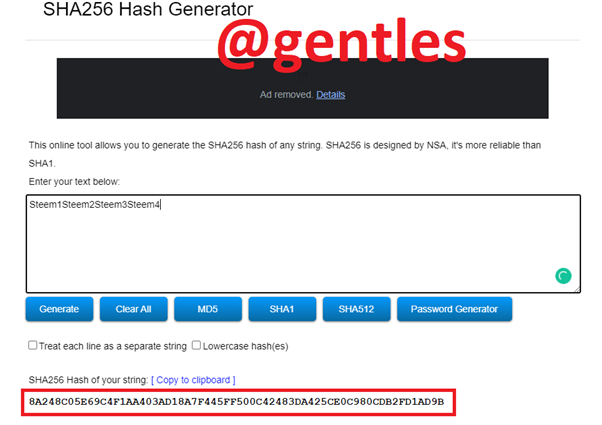
HASH: 8A248C05E69C4F1AA403AD18A7F445FF500C42483DA425CE0C980CDB2FD1AD9B
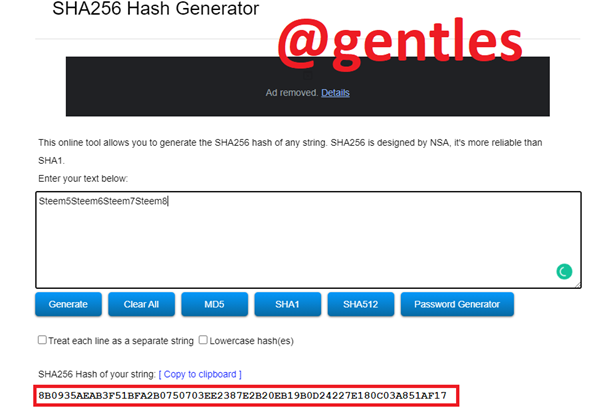
• Steem5Steem6Steem7Steem8
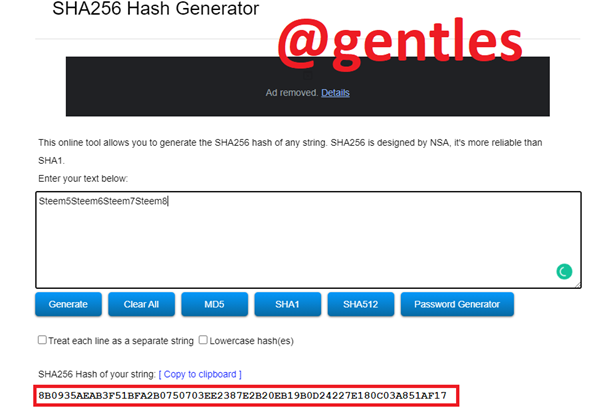
HASH: 8B0935AEAB3F51BFA2B0750703EE2387E2B20EB19B0D24227E180C03A851AF17
The root hash;
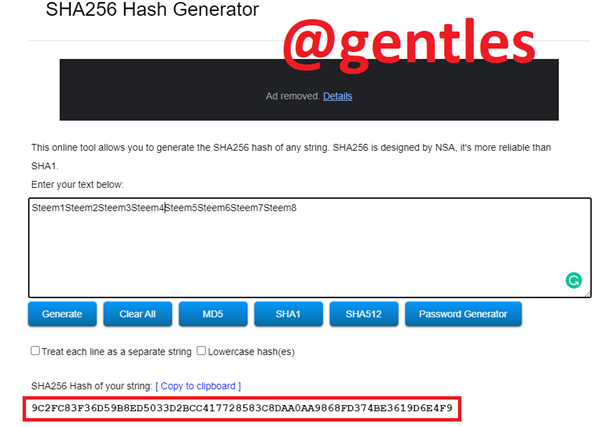
• Steem1Steem2Steem3Steem4Steem5Steem6Steem7Steem8
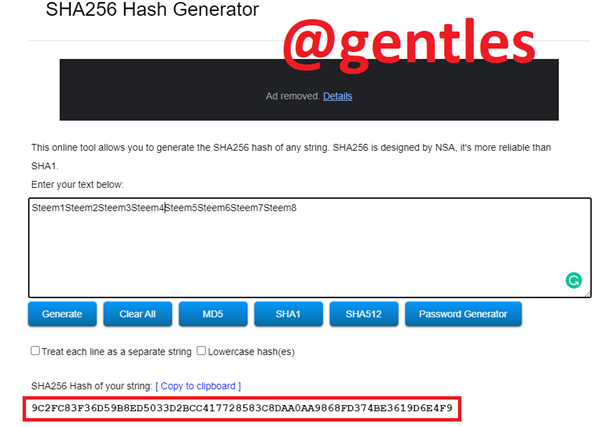
HASH: 9C2FC83F36D59B8ED5033D2BCC417728583C8DAA0AA9868FD374BE3619D6E4F9
• The Merkel Tree
How to verify if Steem6 is included in the Markle Tree.
• Leaf Steem5 should be verified first because it is paired with Steem6 in the Branch of the Merkel Tree. So regenerate Steem5
• Then generate the Steem5Steem6 branch
• Proceed and generate the hash of Steem5Steem6Steem7Steem8
• Finally, join it with Steem1Steem2Steem3Steem4 to produce the root hash.
The root hash should be the same to confirm.
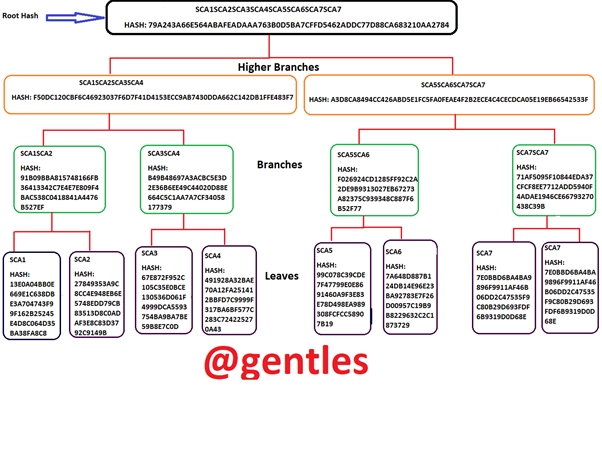
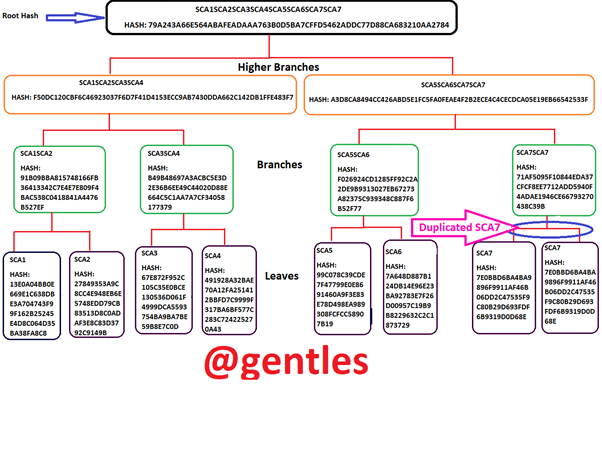
Making a Merkel Tree with SCA1; SCA2; SCA3; SCA4; SCA5; SCA6; SCA7; SCA8 as leaves.
Starting with the leaves.
• SCA1
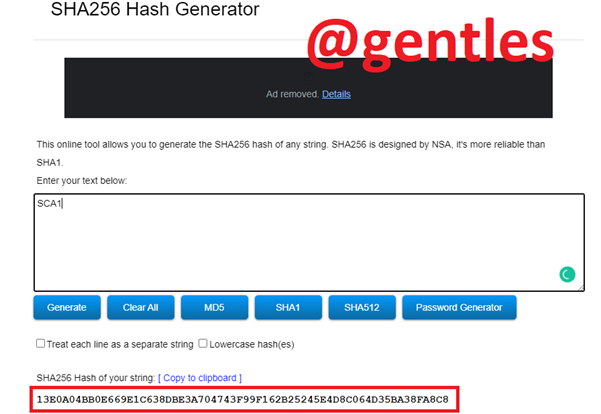
HASH: 13E0A04BB0E669E1C638DBE3A704743F99F162B25245E4D8C064D35BA38FA8C8
• SCA2
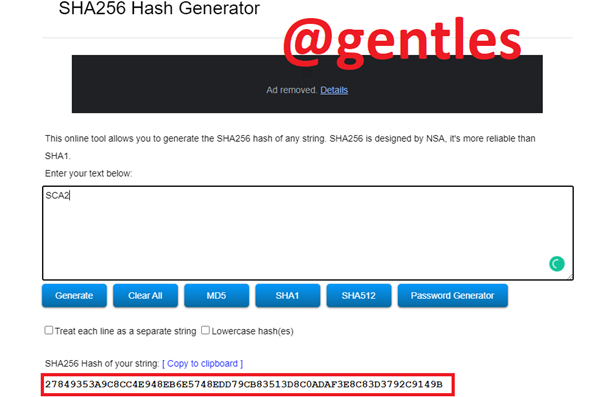
HASH: 27849353A9C8CC4E948EB6E5748EDD79CB83513D8C0ADAF3E8C83D3792C9149B
• SCA3
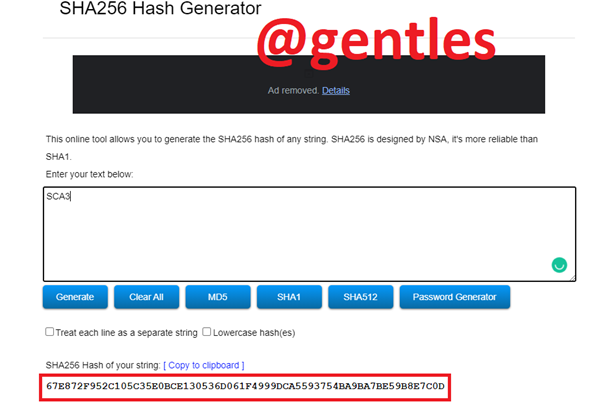
HASH: 67E872F952C105C35E0BCE130536D061F4999DCA5593754BA9BA7BE59B8E7C0D
• SCA4
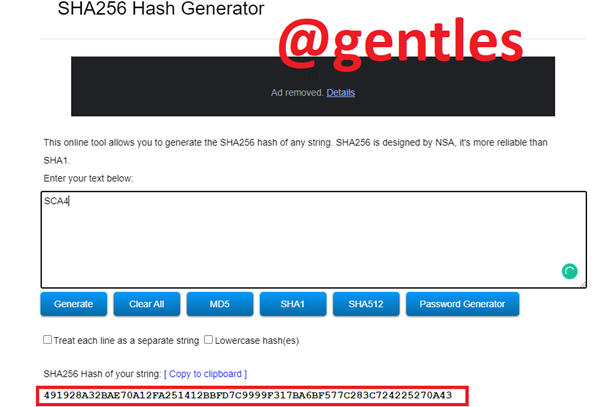
HASH: 491928A32BAE70A12FA251412BBFD7C9999F317BA6BF577C283C724225270A43
• SCA5
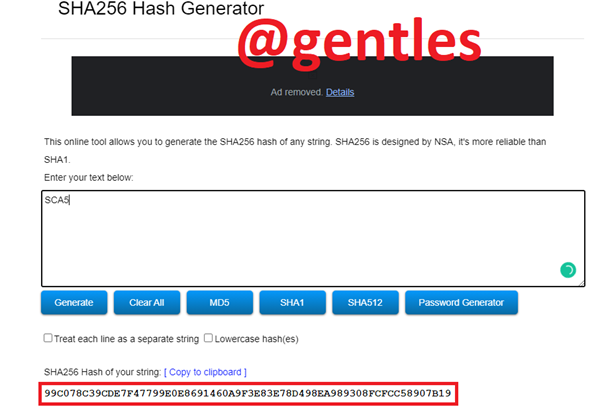
HASH: 99C078C39CDE7F47799E0E8691460A9F3E83E78D498EA989308FCFCC58907B19
• SCA6
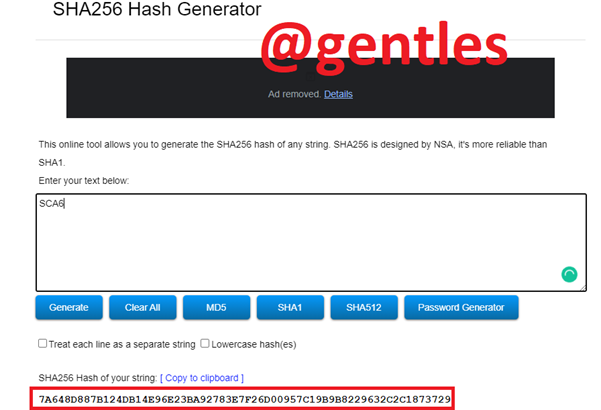
HASH: 7A648D887B124DB14E96E23BA92783E7F26D00957C19B9B8229632C2C1873729
• SCA7
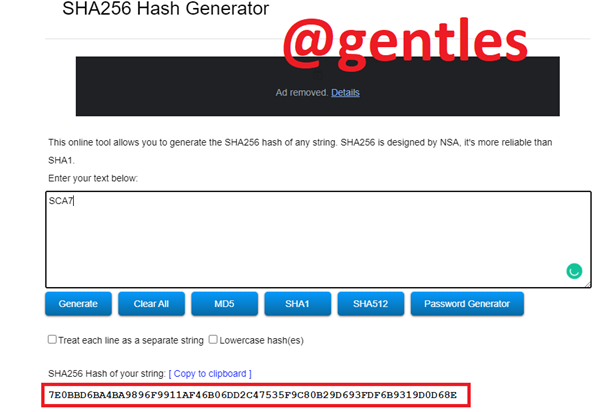
HASH: 7E0BBD6BA4BA9896F9911AF46B06DD2C47535F9C80B29D693FDF6B9319D0D68E
• SCA7
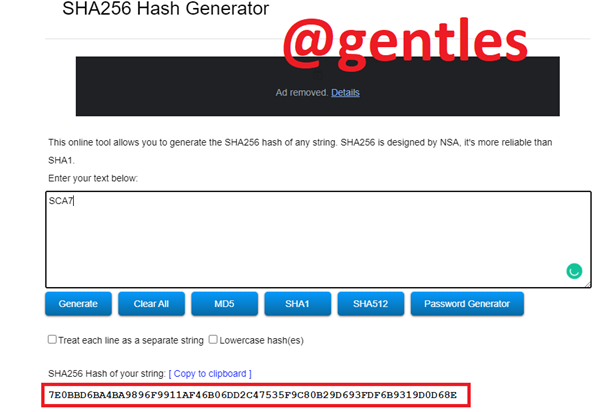
HASH: 7E0BBD6BA4BA9896F9911AF46B06DD2C47535F9C80B29D693FDF6B9319D0D68E
Branches;
• SCA1SCA2
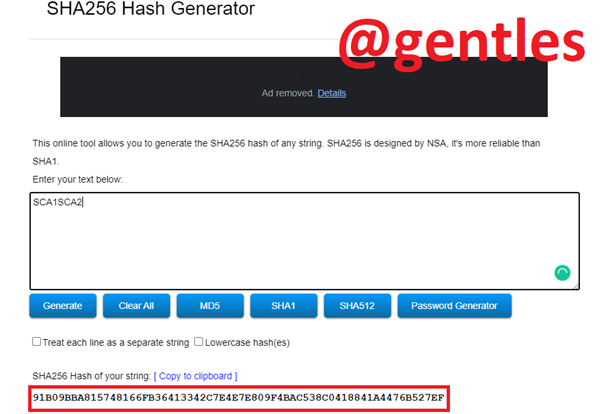
HASH: 91B09BBA815748166FB36413342C7E4E7E809F4BAC538C0418841A4476B527EF
• SCA3SCA4
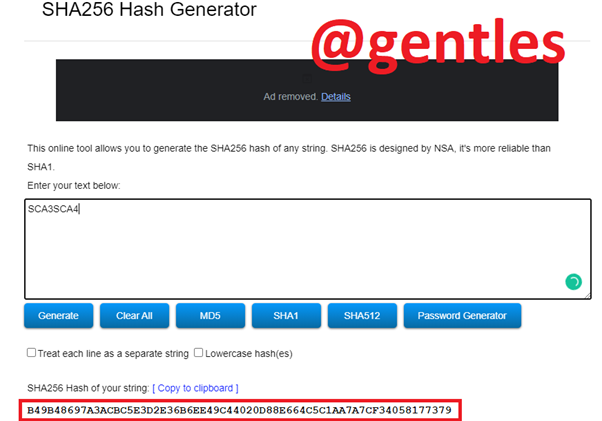
HASH: B49B48697A3ACBC5E3D2E36B6EE49C44020D88E664C5C1AA7A7CF34058177379
• SCA5SCA6
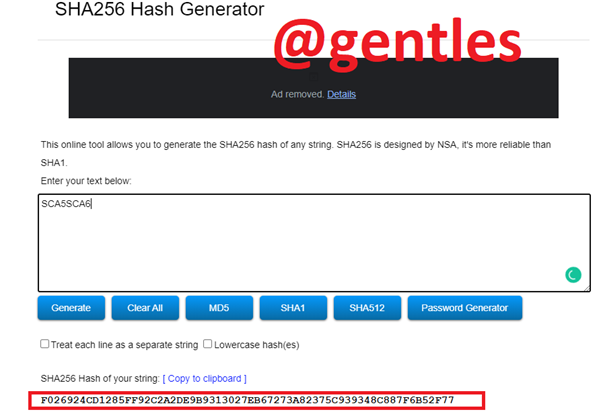
HASH: F026924CD1285FF92C2A2DE9B9313027EB67273A82375C939348C887F6B52F77
• SCA7SCA7
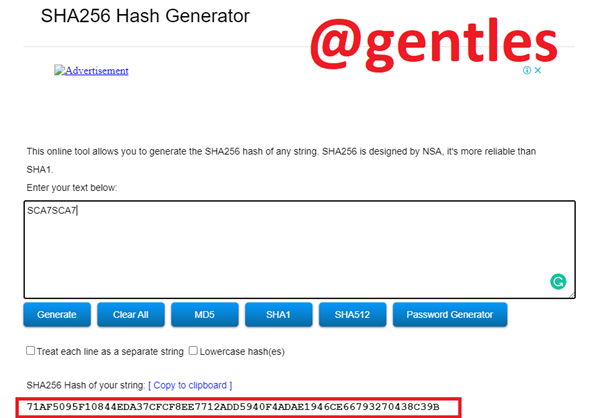
HASH: 71AF5095F10844EDA37CFCF8EE7712ADD5940F4ADAE1946CE66793270438C39B
Higher Branches;
• SCA1SCA2SCA3SCA4
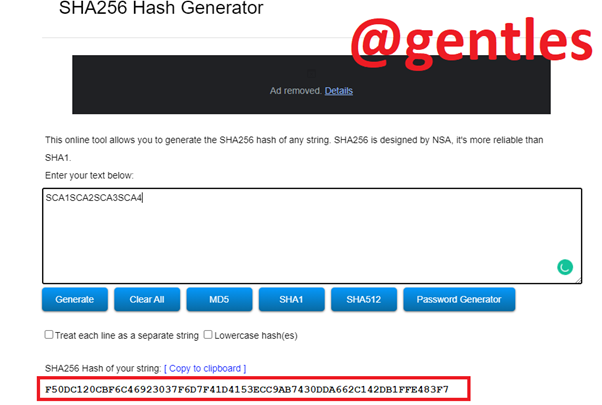
HASH: F50DC120CBF6C46923037F6D7F41D4153ECC9AB7430DDA662C142DB1FFE483F7
• SCA5SCA6SCA7SCA7
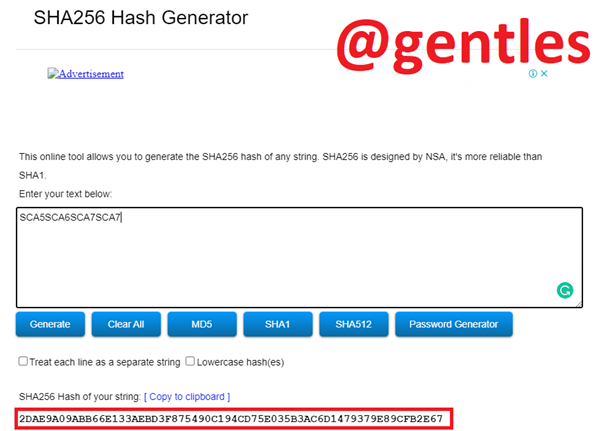
HASH: A3D8CA8494CC426ABD5E1FC5FA0FEAE4F2B2ECE4C4CECDCA05E19EB66542533F
Root Hash;
• SCA1SCA2SCA3SCA4SCA5SCA6SCA7SCA7
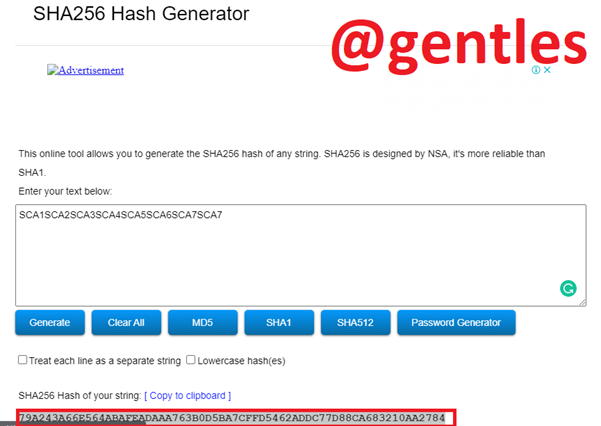
HASH: 79A243A66E564ABAFEADAAA763B0D5BA7CFFD5462ADDC77D88CA683210AA2784
Finally, the Merkel Tree
What to do if the leaves on the tree are odd
For a Merkel Tree to be complete, it should have an even number of leaves and branches. A Branch consists of two leaves and a Higher Branch has two Branches. Then the Higher Branches come together to form the Root Hash.
If the number of Leaves is odd, the last leaf should be duplicated so that it can pair to generate other Branches.
An example is the demonstration of the SCA Merkel Tree above. The leaves were seven so I doubled the last one (SCA7) to generating another SCA7 which was then paired with the previous SCA7 to produce SCA7SCA7 as its parent hash from which a higher branch will be generated.
Conclusion
Merkel Tree is a good concept that can be applied to areas other than blockchain technology. It secures data and makes it convenient to be transferred quickly.
In this lecture, I wrote about hashes in the first part where I explained what hashes are. I continued with Hash Rate which is the speed and power at which hash algorithms are solved. Then I added the explanation for the 51% attack.
In the second part, I explained what Merkel Trees are and demonstrated how to construct a Merkel Tree then showed how to verify if a leaf is included on the Merkel Tree.
Finally, I explained what to do in case of an odd number of leaves. In such a case the last leaf is doubled and paired.
Thank you
Gracias por participar en Steemit Crypto Academy Season 3:
Espero seguir leyendo tus publicaciones.
Pregunta 1, buena información. Bien investigado.
Pregunta 2, todos los hash coinciden, pero la verificación de Steem6 si la hubieras graficado se entiende mejor.
Pregunta 3, una confusión los hash no coinciden: SCA8 no lo vi. El hash SCA7SCA8 no lo encontré y colocas SCA7SCA7. El Root hash no coincide, porque colocas los datos mal, colocas dos veces SCA7SCA7.
Recomendaciones:
Prestar mucha atención cuando realices tareas que requieren concentración, para evitar errores que te perjudican.
Hacer cada respuesta bien sencilla para que cualquier persona pueda entenderla.
Calificación: 6.8