Steemit Crypto Academy | Season 3 - Week 4 | Root Hash and Merkle Tree | Homework Post for @pelon53
Thanks to Professor @pelon53 for giving us this great lecture on Root Hash and Merkle Tree. After studying notes and reading around this week's topic, I have decided to review what I have learned in my homework task.

EXPLAIN IN DETAIL THE HASH RATE
Hash rate, also known as hash power, refers to measuring the speed of a computer needed for a miner to add new blocks to a blockchain network. This mining process uses the Proof of Work(PoW) algorithm consensus. The hash power deals with the speed and the efficiency of the computational capacity of the computer to mine new blocks on the blockchain.
This can be expressed mathematically as,
Hash rate = number of hashes solved/time
For miners to solve complex hash algorithms, computers with more speed and efficiency are needed to solve the high hash rates of the blocks. These high speed and efficient computers come at a cost, this needs enough money to purchase and maintain them and also consumes a lot of electricity.
The Hash Rate is an important part of crypto mining since the higher the computers' higher hash rates, the greater the chances of solving the complex algorithm to add the next block. With this the more rewards the miner gets.
For example,
Let's say a computer can calculate 90,000 hashes within 2seconds, then the hash rate of the computer will be,
Hash rate=hashes/second
Thus, Hash rate = 90000 / 2 second = 45,000h/s
Importance of Hash Rates
Computers of high hash rate are able to solve more blocks within a short time and hence the greater the mining rewards. This factor is one of the things to consider within the mining since low hash rates computers tend to take a long time before validating transactions as compared to high hash computers.
Blockchgians that need high hash rates for validations tend to be more secured as compared to those that need lrss. Bitcoin Blockchain that uses PoW needs more hash rates before a new block can be added. This makes it difficult for hackers to hack into the system.
Disadvantages of Hash Rates
Computers that have high hash rates are costly to buy and maintain. Normally miners spend a couple of amounts to purchase these machines, they are also expensive to maintain when there is a problem.
High hash computers also uses a lot of electricity, and most of the source of the electricity is from coal. Coal is known to cause a lot of pollution to the environment.

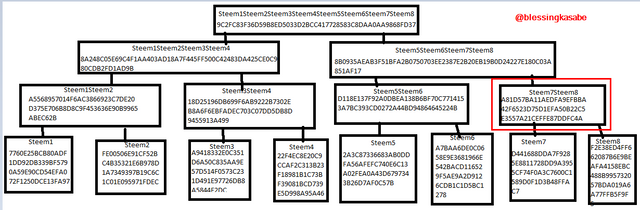
MAKE THE FOLLOWING MERKLE TREE: TRANSACTION (TREE LEAVES): Steem1; Steem2; Steem3; STEEM4; Steem5; Steem6; Steem7; Steem8.
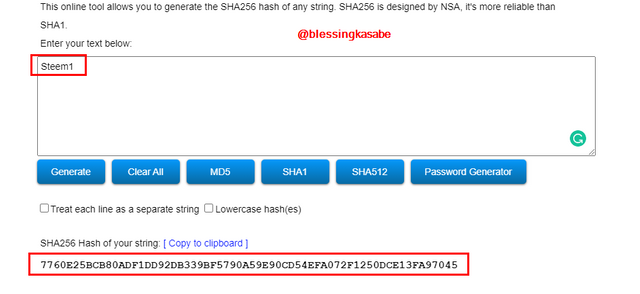
To make our Markle Tree, we first need to find the leaves of the tree. Let's go to source generate the hash codes for our tree,
- Steem1
7760E25BCB80ADF1DD92DB339BF5790A59E90CD54EFA072F1250DCE13FA97045
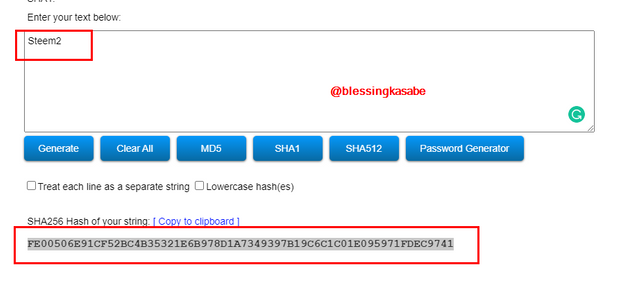
- Steem2
FE00506E91CF52BC4B35321E6B978D1A7349397B19C6C1C01E095971FDEC9741
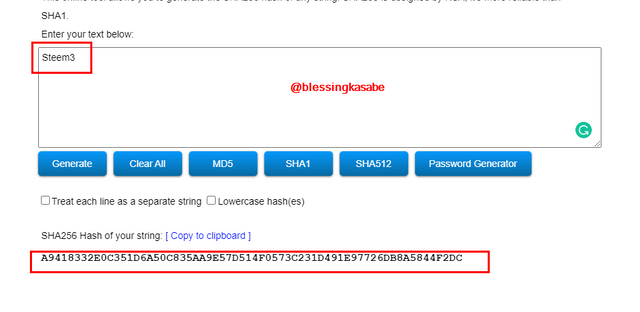
- Steem3
A9418332E0C351D6A50C835AA9E57D514F0573C231D491E97726DB8A5844F2DC
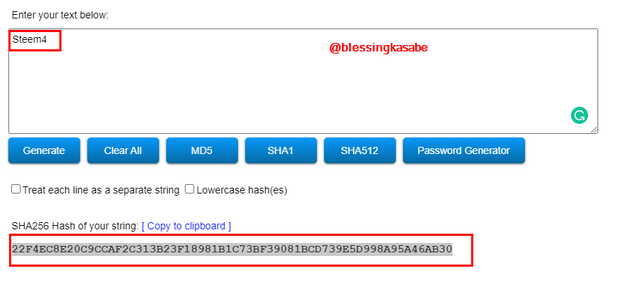
- Steem4
22F4EC8E20C9CCAF2C313B23F18981B1C73BF39081BCD739E5D998A95A46AB30
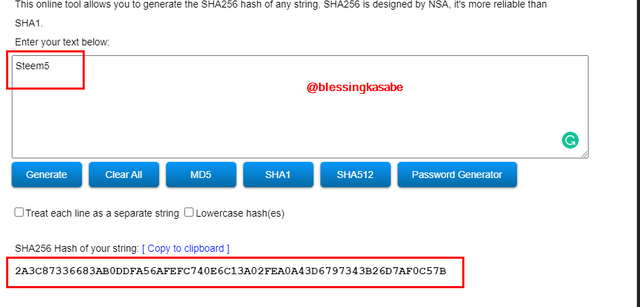
- Steem5
2A3C87336683AB0DDFA56AFEFC740E6C13A02FEA0A43D6797343B26D7AF0C57B
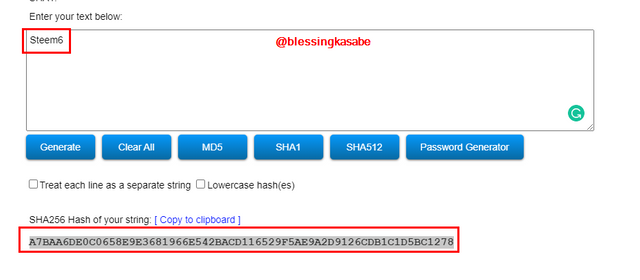
- Steem6
A7BAA6DE0C0658E9E3681966E542BACD116529F5AE9A2D9126CDB1C1D5BC1278
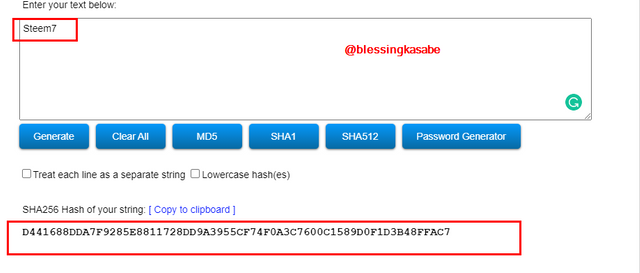
- Steem7
D441688DDA7F9285E8811728DD9A3955CF74F0A3C7600C1589D0F1D3B48FFAC7
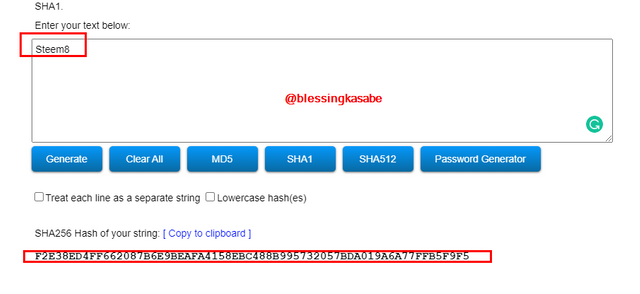
- Steem8
F2E38ED4FF662087B6E9BEAFA4158EBC488B995732057BDA019A6A77FFB5F9F5
Generating hash of the tree Branches
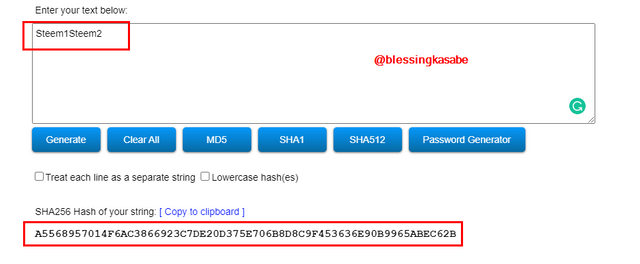
- Steem1Steem2
A5568957014F6AC3866923C7DE20D375E706B8D8C9F453636E90B9965ABEC62B
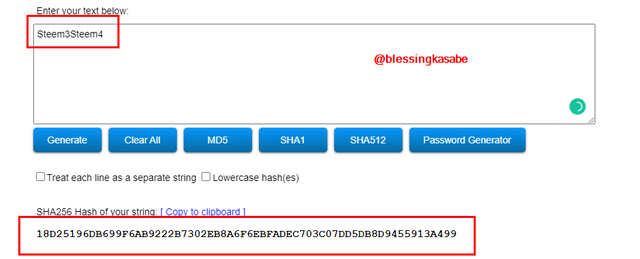
- Steem3Steem4
18D25196DB699F6AB9222B7302EB8A6F6EBFADEC703C07DD5DB8D9455913A499
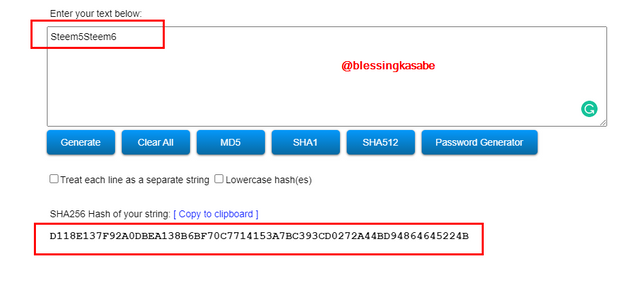
- Steem5Steem6
D118E137F92A0DBEA138B6BF70C7714153A7BC393CD0272A44BD94864645224B
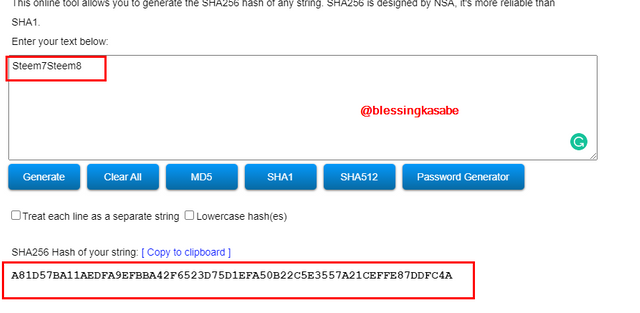
- Steem7Steem8
A81D57BA11AEDFA9EFBBA42F6523D75D1EFA50B22C5E3557A21CEFFE87DDFC4A
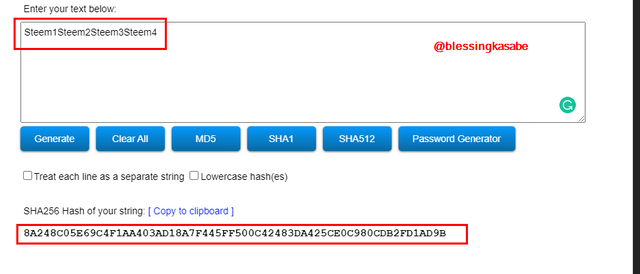
Generating Second-level branches hash.
- Steem1Steem2Steem3Steem4
8A248C05E69C4F1AA403AD18A7F445FF500C42483DA425CE0C980CDB2FD1AD9B
- Steem5Steem6Steem7Steem8
8B0935AEAB3F51BFA2B0750703EE2387E2B20EB19B0D24227E180C03A851AF17
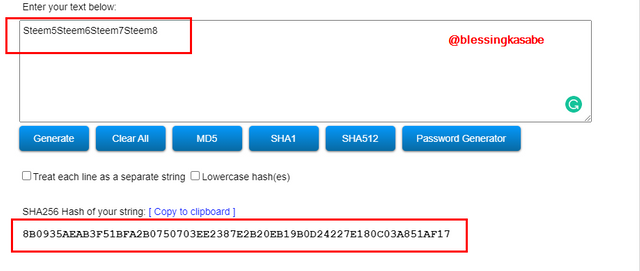
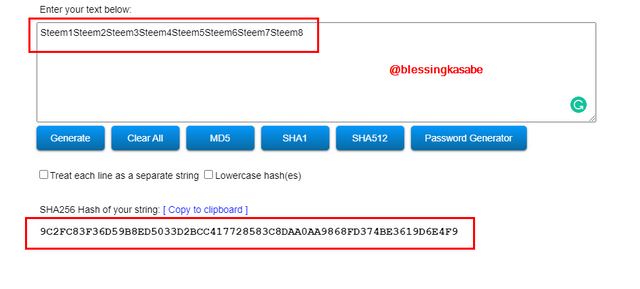
Generating Root hash
- Steem1Steem2Steem3Steem4Steem5Steem6Steem7Steem8
9C2FC83F36D59B8ED5033D2BCC417728583C8DAA0AA9868FD374BE3619D6E4F9
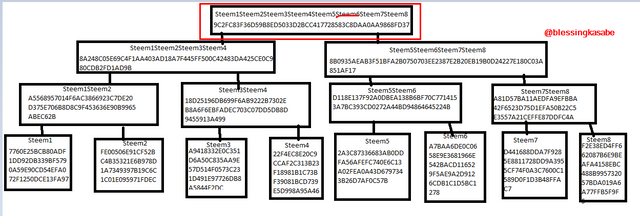
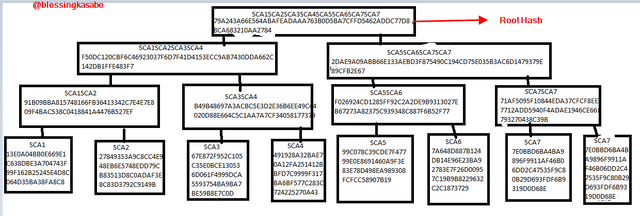
Merkle Tree
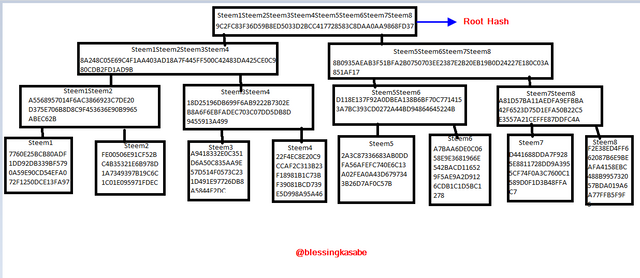
The steps to follow to verify if Steem6 is included in the Markle Tree.
Nodes of blocks are interconnected, hence the hash of one is altered then the remaining hashes will change given an invalid transaction.
To verify the particular node, we need the immediate nodes that surround it. So, therefore, Steem6 can be verified using 2 paths of the tree to reach the root.
- Steem5 is the match of Steem6 on the tree, hence we will verify Steem5 first.
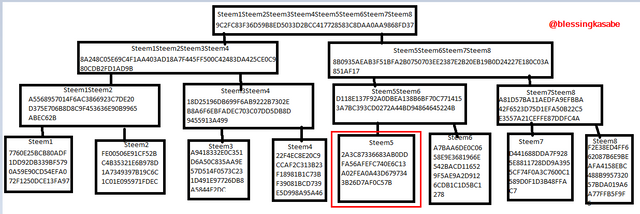
- We then continue to verify the Hash of Steem7Steem8 which is the branch above the nodes of Steem5 and Steem6.
- Now lets check Steem1Steem2Steem3Steem4
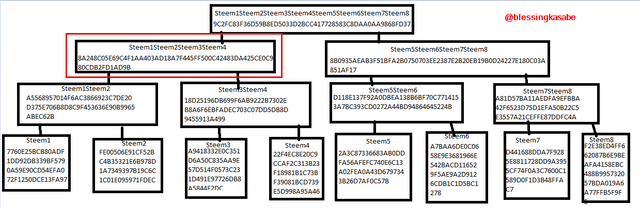
- Let's check The root hash to find out that our Steem6 is included in the tree.
Using the SHA-256; you must place each complete hash in the Merkle Tree.
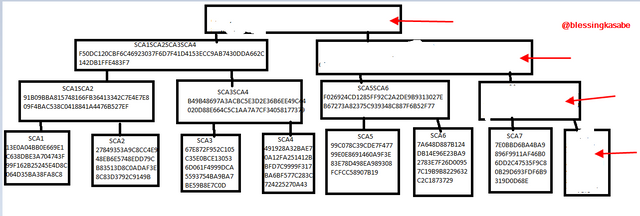
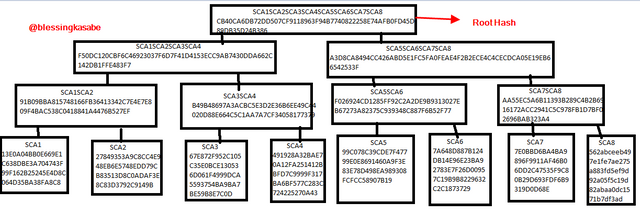
Transaction (tree leaves): SCA1; SCA2; SCA3; SCA4; SCA5; SCA6; SCA7; SCA8. Explain each step
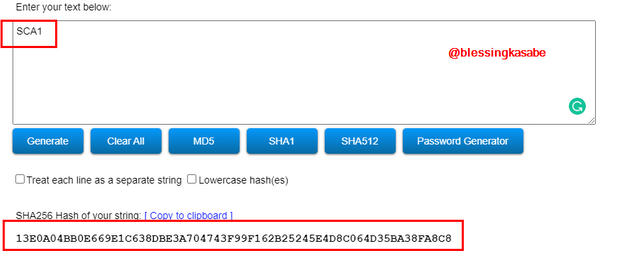
- SCA1
13E0A04BB0E669E1C638DBE3A704743F99F162B25245E4D8C064D35BA38FA8C8
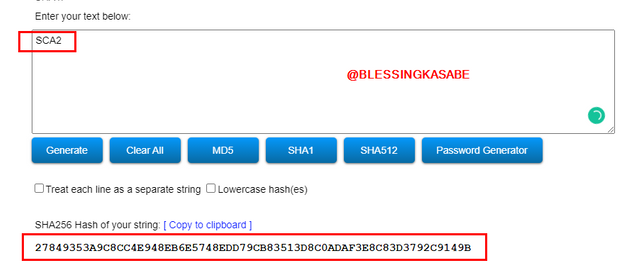
- SCA2
27849353A9C8CC4E948EB6E5748EDD79CB83513D8C0ADAF3E8C83D3792C9149B
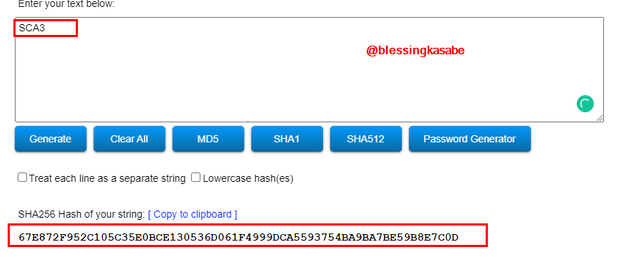
- SCA3
67E872F952C105C35E0BCE130536D061F4999DCA5593754BA9BA7BE59B8E7C0D
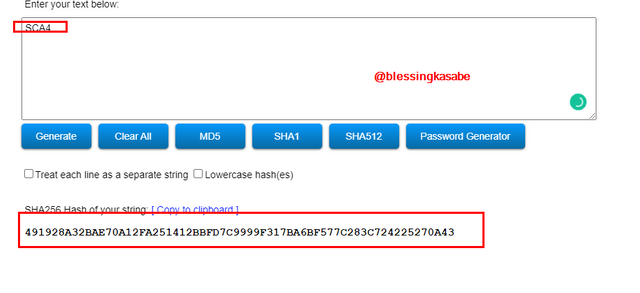
- SCA4
491928A32BAE70A12FA251412BBFD7C9999F317BA6BF577C283C724225270A43
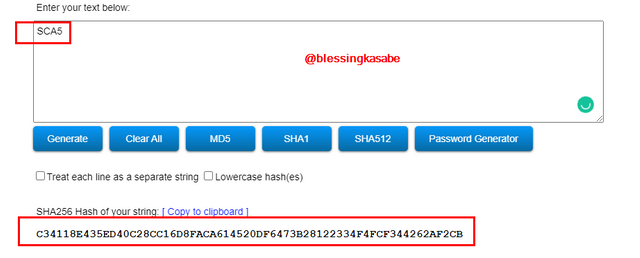
- SCA5
99C078C39CDE7F47799E0E8691460A9F3E83E78D498EA989308FCFCC58907B19
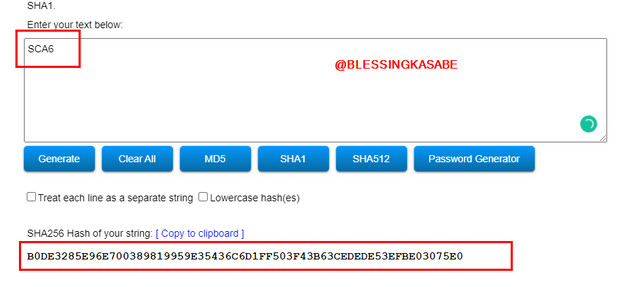
- SCA6
7A648D887B124DB14E96E23BA92783E7F26D00957C19B9B8229632C2C1873729
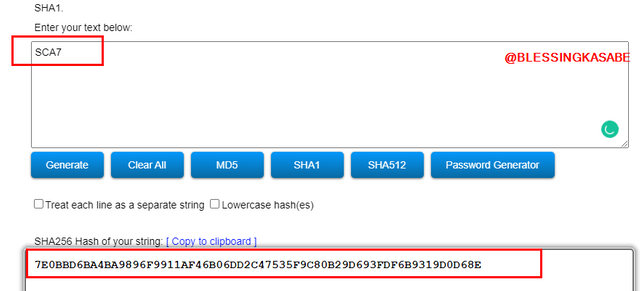
- SCA7
7E0BBD6BA4BA9896F9911AF46B06DD2C47535F9C80B29D693FDF6B9319D0D68E
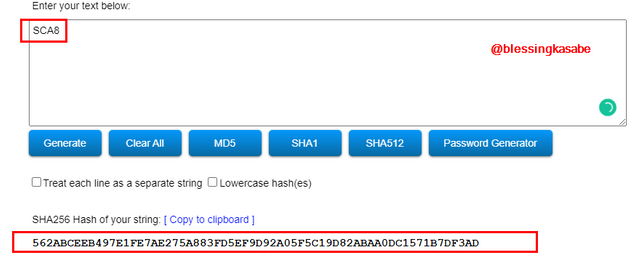
- SCA8
562abceeb497e1fe7ae275a883fd5ef9d92a05f5c19d82abaa0dc1571b7df3ad
Generating the branches of Merkle Tree
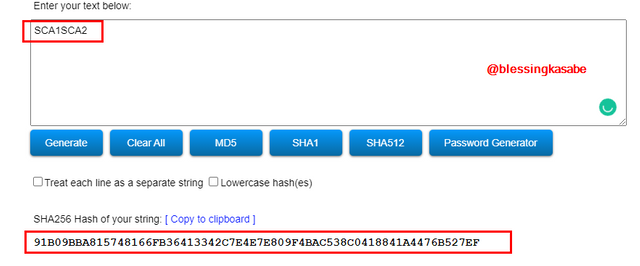
- SCA1SCA2
91B09BBA815748166FB36413342C7E4E7E809F4BAC538C0418841A4476B527EF
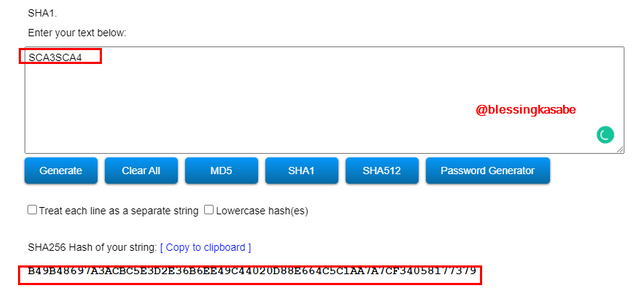
- SCA3SCA4
B49B48697A3ACBC5E3D2E36B6EE49C44020D88E664C5C1AA7A7CF34058177379
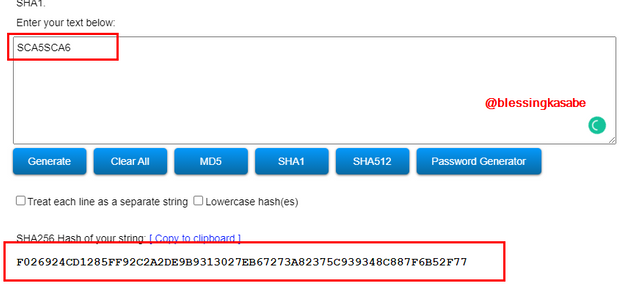
- SCA5SCA6
F026924CD1285FF92C2A2DE9B9313027EB67273A82375C939348C887F6B52F77
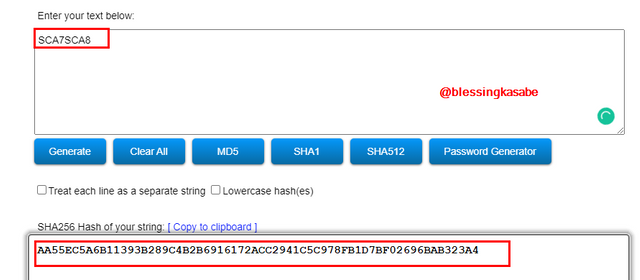
- SCA7SCA8
AA55EC5A6B11393B289C4B2B6916172ACC2941C5C978FB1D7BF02696BAB323A4
Generating the second-level branches hashes
- SCA1SCA2SCA3SCA4
F50DC120CBF6C46923037F6D7F41D4153ECC9AB7430DDA662C142DB1FFE483F7
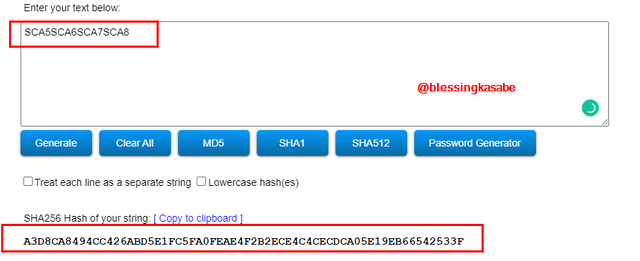
- SCA5SCA6SCA7SCA8
A3D8CA8494CC426ABD5E1FC5FA0FEAE4F2B2ECE4C4CECDCA05E19EB66542533F
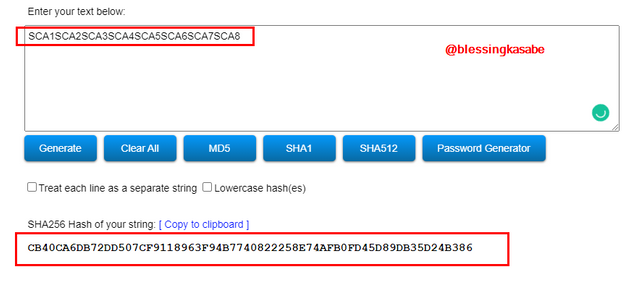
Generating Root hash
- SCA1SCA2SCA3SCA4SCA5SCA6SCA7SCA8
CB40CA6DB72DD507CF9118963F94B7740822258E74AFB0FD45D89DB35D24B386
Merkle Tree

If the number of leaves on the tree is odd, what should you do? Explain
In a situation where the number of leaves on the tree is odd, then the last leaf should be doubled in other to generate its root hash. Using the example below, we double SCA7
- Odd leaves
SCA7
7E0BBD6BA4BA9896F9911AF46B06DD2C47535F9C80B29D693FDF6B9319D0D68ESCA7SCA7
71AF5095F10844EDA37CFCF8EE7712ADD5940F4ADAE1946CE66793270438C39BSCA5SCA6SCA7SCA7
2DAE9A09ABB66E133AEBD3F875490C194CD75E035B3AC6D1479379E89CFB2E67
- SCA1SCA2SCA3SCA4SCA5SCA6SCA7SCA7
79A243A66E564ABAFEADAAA763B0D5BA7CFFD5462ADDC77D88CA683210AA2784
The Merkle Tree should look like this
Conclusion
Thank you @pelon53 for this wonderful lecture.
In conclusion,
- Markle tree plays a major role in the crypto space, this makes it possible to validate data and process transactions more efficiently o the blockchain.
• Computers with high Hash rates have more speed and are more efficient when validating blocks. The higher hash rates also provide high security on the blockchain, this makes it difficult for hackers to break into the system.
• High hash rate computers are costly to purchase and maintain. They also use more electricity.
Thank you for visiting my homework post.