Hackers could guess your phone PIN using its sensor data
Instruments in sensible phones like the measuring device, gyro and proximity sensors represent a possible security vulnerability, in line with researchers from Nanyang Technological University, Singapore (NTU Singapore), whose analysis was revealed within the open-access cryptography ePrint Archive on vi Dec.
Using a combination of data gathered from six totally different sensors found in sensible phones and progressive machine learning and deep learning algorithms, the researchers succeeded in unlocking automaton sensible phones with a ninety nine.5 per cent accuracy among solely 3 tries, once attempt a phone that had one amongst the fifty commonest PIN numbers.
The previous best phone-cracking success rate was seventy four per cent for the fifty commonest pin numbers, however NTU's technique are often wont to guess all ten,000 potential combos of four-digit PINs.
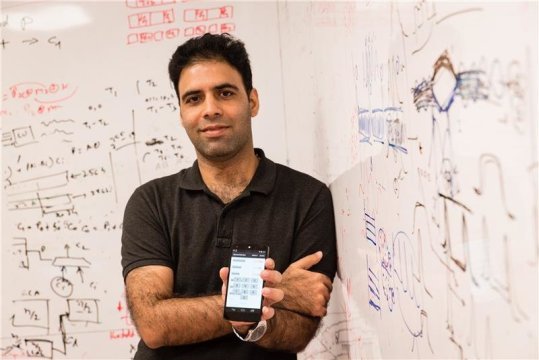
Led by Dr Shivam Bhasin, NTU Senior analysis somebody at the Temasek Laboratories @ NTU, researchers used sensors during a sensible phone to model that variety had been ironed by its users, supported however the phone was tipped and the way a lot of lightweight is blocked by the thumb or fingers.
The researchers believe their work highlights a big flaw in sensible phone security, as victimization the sensors among the phones need no permissions to tend by the phone user and ar brazenly offered for all apps to access.
How the experiments were conducted
The team of researchers took humanoid phones and put in a custom application that collected information from six sensors: measuring instrument, gyroscope, gaussmeter, proximity detector, barometer, and close lightweight detector.
"When you hold your phone and key within the PIN, the means the phone moves once you press one, 5, or 9, is incredibly totally different. Likewise, pressing one along with your right thumb can block a lot of lightweight than if you ironed nine," explains Dr Bhasin, United Nations agency spent ten months along with his colleagues, Mr. David Berend and Dr. Bernhard Jungk, on the project.
The classification algorithmic rule was trained with information collected from 3 individuals, United Nations agency every entered a random set of seventy four-digit pin numbers on a phone. At a similar time, it recorded the relevant detector reactions.
Known as deep learning, the classification algorithmic rule was able to offer totally different weightings of importance to every of the sensors, reckoning on however sensitive every was to totally different numbers being ironed. This helps eliminate factors that it judges to be lesser and will increase the success rate for PIN retrieval.
Although every individual enters the protection PIN on their phone otherwise, the scientists showed that as information from a lot of individuals is fed to the algorithmic rule over time, success rates improved.
So whereas a malicious application might not be able to properly guess a PIN instantly once installation, exploitation machine learning, it might collect information from thousands of users over time from every of their phones to find out their PIN entry pattern and so launch associate degree attack later once the success rate is way higher.
Professor Gan Chee Lip, Director of the Temasek Laboratories @ NTU, same this study shows however devices with apparently robust security may be attacked employing a side-channel, as detector information might be entertained by malicious applications to spy on user behaviour and facilitate to access PIN and parole info, and more.
"Along with the potential for unseaworthy passwords, we tend to ar involved that access to phone detector info might reveal so much an excessive amount of a couple of user's behaviour. This has important privacy implications that each people and enterprises ought to pay imperative attention to," same academic Gan. Dr Bhasin same it'd be better for mobile operative systems to limit access to those six sensors in future, in order that users will actively opt to offer permissions solely to sure apps that require them.
To keep mobile devices secure, Dr Bhasin advises users to own PINs with quite four digits, in addition to alternative authentication ways like one-time passwords, two-factor authentications, and fingerprint or face recognition.
Great post!
Thanks for tasting the eden!
You got a 3.30% upvote from @dailyupvotes courtesy of @likhon!
Please upvote this comment to support the service.
You got a 3.35% upvote from @brandonfrye courtesy of @likhon!
Want to promote your posts too? Send a minimum of .10 SBD or Steem to @brandonfrye with link in the memo for an upvote on your post. You can also delegate to our service for daily passive earnings which helps to support the @minnowfund initiative. Learn more here
You got a 3.98% upvote from @minnowvotes courtesy of @likhon!
Congratulations! This post has been upvoted from the communal account, @minnowsupport, by Likhon from the Minnow Support Project. It's a witness project run by aggroed, ausbitbank, teamsteem, theprophet0, someguy123, neoxian, followbtcnews, and netuoso. The goal is to help Steemit grow by supporting Minnows. Please find us at the Peace, Abundance, and Liberty Network (PALnet) Discord Channel. It's a completely public and open space to all members of the Steemit community who voluntarily choose to be there.
If you would like to delegate to the Minnow Support Project you can do so by clicking on the following links: 50SP, 100SP, 250SP, 500SP, 1000SP, 5000SP.
Be sure to leave at least 50SP undelegated on your account.