[EXCLUSIVE]! Get a professional lab featuring top hackers and more than 25 devices to learn hacking ...
Dear Sirs, We will be looking at an exclusive topic in the hack world, how to get an information security lab with more than 25 devices specially designed for hacking, with a variety of difficulties that simulate reality and enable you to learn and acquire skills in information security. The last of the most powerful hackers and information security professionals in the world, and the way to access it is not easy, but you must merit the honor of belonging to this laboratory by breaking through the entry code hidden in the site.
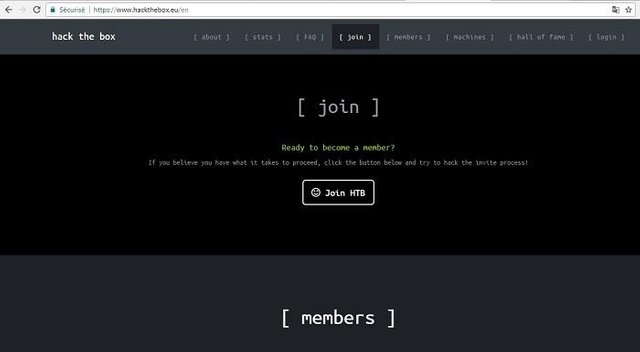
To start on God's blessing, first go to www.hackthebox.eu and go to [Join] and press Join HTB
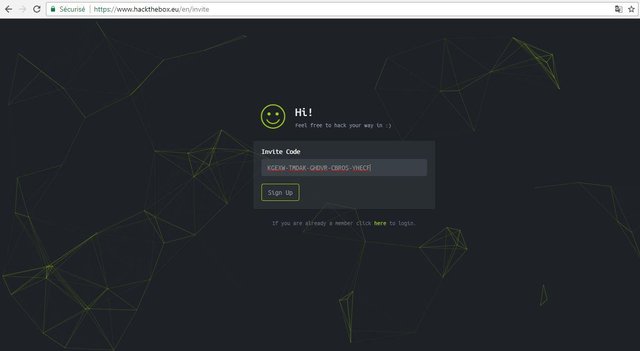
After that, we will be asked for the invitation code, which we will divulge on the site.
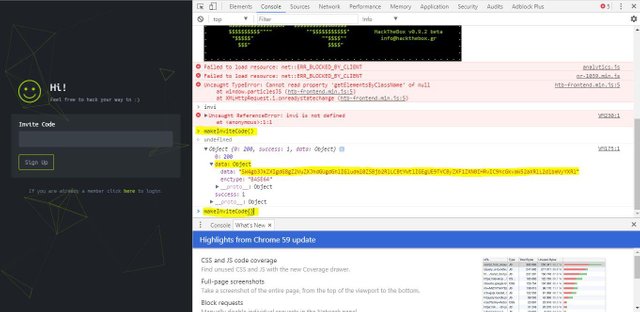
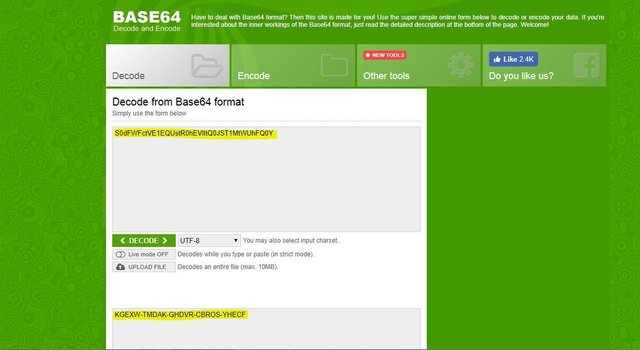
We show the page code source code to go to console and write the following command (makeInvitecode) then we go to Data where we will get encrypted code, in order to decrypt this code we will go to www.base64decode.org

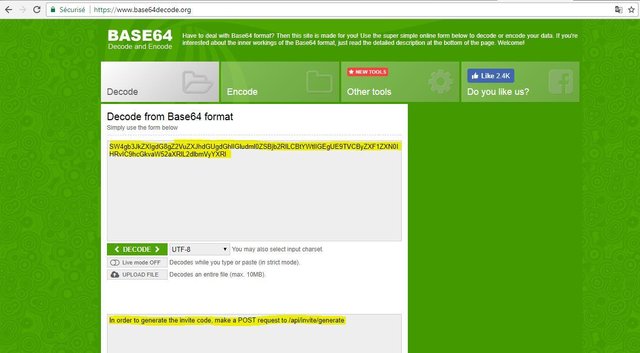
After decoding the code we will be asked to send a post request to api invite / generate /
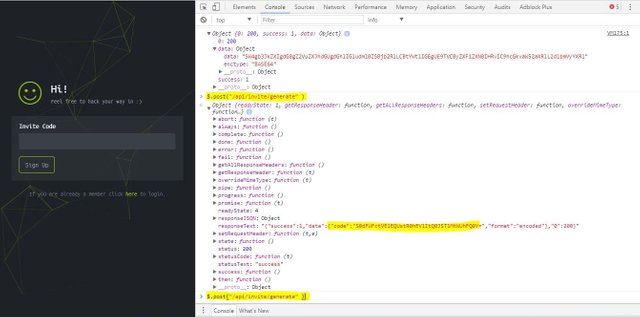
We go back to Console and then write the following command (api / generate / invite / `)).$ to find a second encrypted code in the JSON response as you see in the image
We decode the code in the same way as before to get the activation code as shown in the picture.
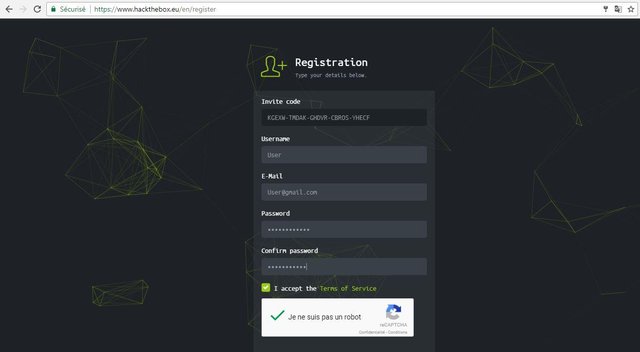
Finally we got the activation code to proceed with the registration process.
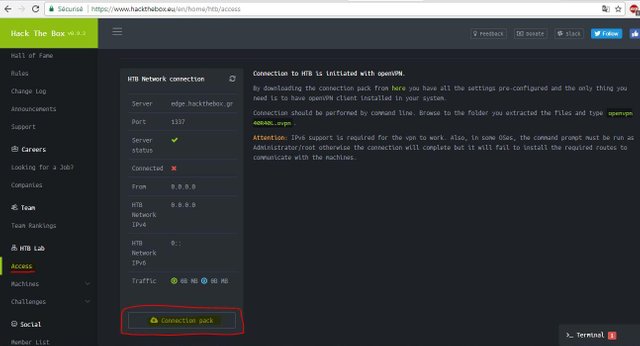
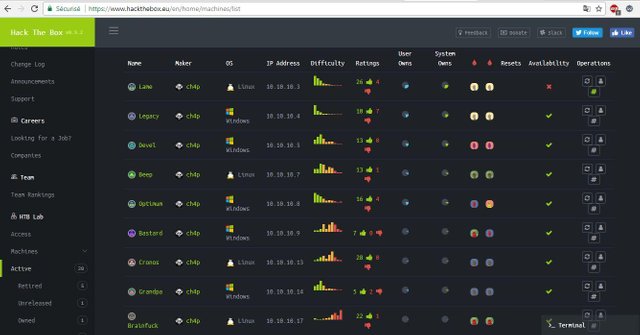
After registration we can access the front of the laboratory where we will find a variety of devices of different degrees of difficulty that can penetrate through the installation of VPN connects us to the network of the laboratory, as this network includes a group of hackers with high skills, advises the site using a virtual machine KaliLinux distribution for all operations Break and protect your files and your computer from damage.
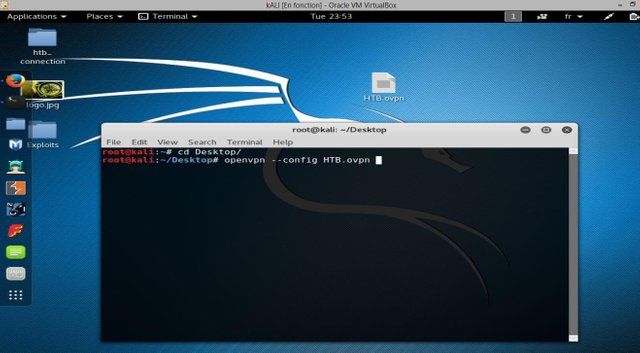
To create a VPN you need to go to Access and download the Connection Pack
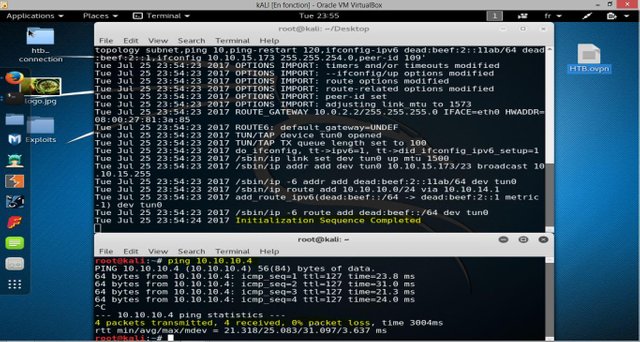
After downloading the file we type the following command "openvpn --config HTB.ovpn" in Terminal in the case of 'HTB' is the name of the file you uploaded.
You have to press the ENTER button, congratulations to the professional lab, you can directly penetrate the devices in your network.
Remember that the purpose of this lab is to give you a room to learn to penetrate to understand how to protect your devices, and that any penetration of any device outside this network is punishable by law.
I hope to get the topic of your admiration and if you benefited from it Vtkdira for my efforts Leave a comment to the motivational and shared the subject to benefit the benefit :)
And if you want to write to explain how to penetrate some of the devices in this lab all the details ask me in the comments section and I will be happy to meet your requests ^ _ ^

This post has received a 3.13 % upvote from @drotto thanks to: @hamzaoui.
this looks like a cool toy-
I would only access this site using a VM (gotta be careful of downloading stuff)