Understanding the EOS Ghostbusters Security Approach

What is Ghostbusters ?
Ghostbusters started as an EOS testnet focused on researching and rehearsing the best practices for running the eosio software in as secure way as possible. It all started because we were worried about the lack of focus regarding infrastructure security.
The Ghostbusters Security Approach was founded by EOS Rio and HKEOS, but has since received contributions from Sw/eden, eosDAC, EOS Tribe, EOS 42, Sheos and many more BPCs in the infrastructure telegram channel. You can see the BPCs active in the network here.
Since this is a community driven project we feel that collaboration between BPCs is very important. This is an educational process and we invite more BPCs to participate in this.
Ghostbusters started as a research environment, not a launch initiative. It quickly attracted the attention from the community and other BPCs who were feeling the same way we do concerning security. Then people started recommending it as a launch approach.
So what is this approach exactly?
You can learn more about it in our Github repo.
It basically combines Keybase for trusted communication and Wireguard for secure node connections. With keybase you can verify your identity, so we guarantee only BPCs can join the group. Also, it has a safe message encryption.
Ideally, no public Internet access should be allowed to BP nodes while still allowing meshing between BP nodes. Hence we propose using secure P2P communication between BP nodes via point-to-point secure tunnels using the open source WireGuard kernel based VPN software. We have also verified that there are no known exploits for Wireguard.
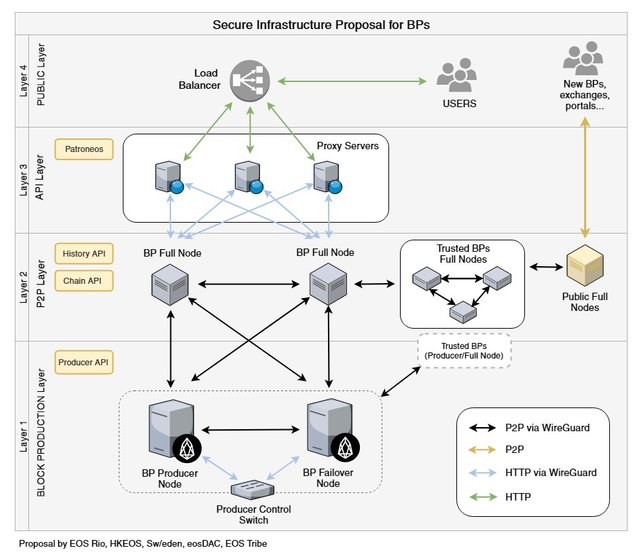
We designed a 4 layer approach to setting up the infrastructure. This has been done in collaboration with infrastructure security expert @jemxpat. It can be seen in the diagram below:
- 1st Layer: Producing nodes - These communicate using Wireguard.
- 2nd Layer: Full nodes to relay blocks, connected to the producing nodes and to other BPs via Wireguard.
- 3rd Layer: API layer where Proxy Servers (web firewalls) filter requests using Patroneos (released by Block.One). These add an extra layer of protection against malicious and malformed data, as well as against volumetric attacks.
- 4th Layer: Load Balancer incoming api calls are routed to our Layer 3 web firewalls.
Will this method be used at Launch?
We don’t know it yet, the community of BPs is reaching consensus on that, it should be defined pretty soon. Honestly, we just want what it’s best for the eos community. We need to take security serious to have a stable and smooth launch. We are committed to one mainnet.
We will continue to improve the Ghostbusters methods. We hope that these methods and guidelines can be seen as some kind of “best practices” and that they can be used by large parts of the BP community.
Please, note that, regardless of the method used to boot, the launch phases are still the same.
Security and Transparency
Security does not mean lack of transparency. We are constantly trying to be as transparent as possible. Our source code is available on Github and our suggestions regarding infrastructure are constantly being discussed and improved by the community :)
I hope you will get elected together with eosDac and other BPc
Excelente forma de trabajo, y sobre todo por la información que dan a todos los que hemos llegado a esta plataforma.Gracias por compartir.
This article has been translated into Korean: https://steemit.com/eos/@eosdac/eos-ghostbusters
Thanks!
I love this work, It´s far beyond my understanding so I am very happy that I have knowledgeable people doing this. Thank you!
Hey @eosrio, I am reaching out to you guys to get some information verified. Is it true that Dan dropped the constitution due to BP’s bitching like little kids about the addition of “owning 1% of another BP needs to be disclosed”.
Please tell me this is just bs rumors?
Hello @aclarkuk82, sorry for the late response. Apparently, this was removed from the constitution because it was not viable on the real world.
The term "ultimate beneficial owner" mean to trace back ownership to a human.
In the case of a BP which has owners which are other companies, it means that you must find all owners of that company. If the company is publicly listed on a stock exchange, there may be regulations about such disclosures.
If the shareholder in the BP is a fund, it may be illegal to disclose the owners, often called "Limited Partners". In some jurisdictions, privacy of limited partners is enforced by law, and it is almost always enforced by contract.
We would like to state we had no part in this discussion. We are a self-funded BP who is not owned by any company or fund. EOS Rio idea was conceived inside Rede Entropia, a blockchain & AI Lab here in Rio de Janeiro, but we are an independent front from them.
Ultimately, Dan removed the constitution because he wants the community to take charge. EOS now is a utility token owned by the community who should do its own constitution.
Thank you for the clear response guys
This is true but we are working as a community to add a set of governance documents ourselves
Congratulations @eosrio! You have completed some achievement on Steemit and have been rewarded with new badge(s) :
Click on any badge to view your Board of Honor.
To support your work, I also upvoted your post!
For more information about SteemitBoard, click here
If you no longer want to receive notifications, reply to this comment with the word
STOPDo not miss the last announcement from @steemitboard!