[Worker Proposal] A well-organised Security Response Cooperative System can protect EOS from DDoS.
Trends of the development of Distributed Denial of Service (DDoS) attack
DDoS has been rapidly evolving since its realisation in the early 2000s. In the middle of 2002, when malicious bot (BOT) started to occur in the Windows operating system, botnets have also been evolving with various methods. Within the last five years, Internet of things (IoT) devices have begun to be introduced into society in various ways, and so did botnets utilising these devices.
In early days, DDoS attacks caused by botnets were manually infected by Trojans with several hundreds of megabytes per second (Mbps) in size. However, since 2002 when Botnets became bigger and well organised, the size of these attacks also grew to several gigabytes per second (Gbps). Recently in 2016, it has been reported that 1.2 terabytes of attack traffic occurred against Dyn [1]
As the damage caused by the DDoS becomes a reality, the security experts and internet service providers (ISP) have been reviewing how to respond to such attacks.[2] As a result, network equipment manufacturers have begun to provide the equipment to filter the suspicious traffic at the entry points of the network and the ISPs have also provided services that protect users by bypassing these traffic. However, if the traffic exceeds the bandwidth of the network link to the server, the attackers mostly succeed. Recently, the attack volume of DDoS has become much more complex to efficiently cope with these attacks.

EOS Systems and DDoS
As BitCoin or Ethereum does not limited the number of block producers (BPs), the damage caused by the DDOS attack can be relatively minimal. However, EOS does limit block producer numbers and this may make the system more vulnerable to DDoS attacks. In other words, given that the number of BPs is limited to 21, and if the recent attacks occur to a certain number of BPs (e.g. half to a two third), we will have a huge problem as it will affect the consensus made by all BPs.
The need for a governance system for DDoS response in the EOS ecosystem
Proposal to construct an EOS BP Security Governance
- Create a communication channels amongst BPs for security events.
- Create a cetnre to mutually prevent severe security breach
- Cooperate with Computer Security Incident Response Team (CSIRT)
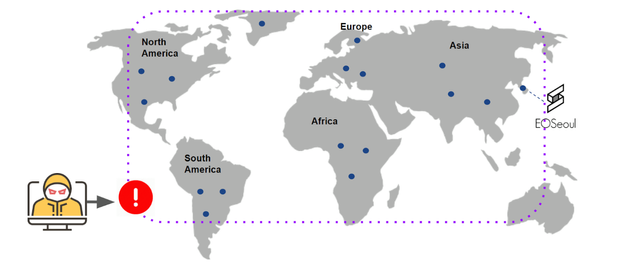
As simplified in the picture above, the important role played by the EOS BP network, it is more than likely that the network would be susceptible to the attacks with financial motivation.
We can predict how the attacks can occur in the following scenarios.
- A DDOS attack on a specific BP extorts or reduce its credibility as a BP resulting the loss of BP status.
- Simultaneously many BPs will be under the attack, causing the EOS system not to function normally in voting and other activities thereby threatening the ecosystem.
In scenario 1, each BP is required to respond by the DDOS response system and the EOS systems must have a system to exclude such BPS from participating in the consensus until it recovers.
In scenario 2 where multiple BPs are under attack, it is necessary to have a coordinated defense system for all BPs to participate. First, each BP need to be able to recognise the status of others. By recognising these status, normal BPs should be able to take the affected BPs out of consensus and replace them.
Then, when a BP is under the attack, it should notify other BPs to act together to remedy the situation to assist the BP back to the full functionality. There must be a system in place to notify, recover and prevent such attacks. Also to identify and remove the source of DDos attack in collaboration with CSIRT where BPs are located.
Recently, DDOS attacks with advanced botnets such as Mirai, are even more serious as the size of the attack is in several Tbps which is huge for a single BP to handle. In order to secure the network, all entities participating in the EOS ecosystem must participate together.
Reference
[1] https://dyn.com/blog/dyn-analysis-summary-of-friday-october-21-attack
[2] https://www.krcert.or.kr/webprotect/cyberShelters/cyberShelters.do