TAMUctf 2018 WriteUp (hashbrown)
With this task there was a linux executable given and you had to look for a suitable password.
A first investigation using strings showed a possible password hash.
$ strings hashbrowns
...
[^_]
please enter the password
the password is 20 characters or less
af-023ravj09javjap0ejafpeaf
input string
after
8819d19069fae6b4bac183d1f16553abab16b54f
success!
invalid password
;*2$"
...
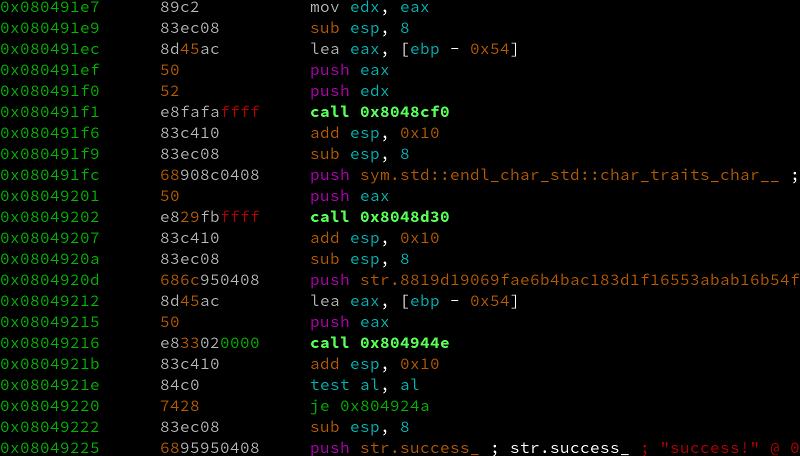
A look at the program code with radare2 showed that this string is actually used for a comparison.
With a bit of luck it is a password which can be cracked with a standard wordlist. And John could find it with the help of rockyou.txt within a few miliseconds.
$ john --wordlist=/opt/wordlists/rockyou.txt hash.txt
Will run 8 OpenMP threads
Press 'q' or Ctrl-C to abort, almost any other key for status
potatoes (?)
1g 0:00:00:00 DONE (2018-03-05 19:31) 9.090g/s 595781p/s 595781c/s 595781C/s 123456..ryanscott
Use the "--show" option to display all of the cracked passwords reliably
Session completed
After input on the website the field appeared in green.
As soon as I have a little more time, further writeups will follow.
Nice Post. Be Steem :)