Warning: Every CryptoNote/Monero transaction in history will be retroactively exposed
The CryptoNote codebase and its best known currency-derivative Monero, both of which prominently use ring signature anonymity as their defining feature, build their entire privacy scheme upon said feature. This is highly problematic to anyone that relies on their transactions to be anonymous not only in the present but also well into the future as I will show in the following.
If someone or something (e.g. an AI) ever were to break ring signature anonymity every CryptoNote currency's blockchain will be completely de-anonymized from beginning to end. This only has to happen once. So in regards to anonymity Cryptonote has one centralized point of failure: The robustness of its ring signature implementation.
Case in point
A (former?) Monero team member going by the name of "Shen Noether" wrote a (now deleted) blog post about how he was able to break the anonymity of ShadowCash due to an erroneous implementation of ring signatures (Here's an archived version. - And an archive of that).
Shen went on to deanonymize the entire ShadowCash blockchain from start to finish just to prove the flaw he found was serious and painfully real. Had anyone -up to that point and subsequently- ever put their faith into SDC's flawed ring signature implementation and made a life and death transaction with ShadowCash, they'd be in mortal danger right now (to emulate doomsday rhetoric heard from Monero "steward" Riccardo Spagni in regards to other privacy-oriented currency projects and their purported flaws).
Safe Today != Safe Tomorrow
The important takeaway here is the fact that a single kink in this specific anonymity scheme's architecture will crush the privacy of every single user . It would be extremely naive to believe ring signatures are free of attack vectors in their current state.
This isn't even the most immediate danger, though: We are at the brink of quantum computing becoming mainstream and with its proliferation it is well known and acknowledged that Monero's ring signatures will be broken:
However, the traceable version Monero uses (for double-spending prevention) is indeed able to be broken (meaning public key linked to key image and thus signer revealed) due to the existence of a key image.
But wait: Aren't all cryptocurrencies done for with the advent of Quantum Computing?
Hardly. Bitcoin and similar cryptocurrencies can safely transition to Quantum resistant encryption without compromising the security of their blockchain because it was transparent from the get go. CryptoNote/Monero however obfuscates its entire blockchain with QC-vulnerable encryption. Anyone with a copy of any CryptoNote blockchain (obviously this is the very nature of a distributed ledger) will be able to retroactively expose every transaction ever done with it. This cannot be mitigated after the fact because it's impossible to prevent someone from retaining an "unpatched" copy of the chain.
Conclusion
Anyone entrusting their anonymity to the Monero- or any other CryptoNote-blockchain for that matter is relying on a house of cards and oblivious to inescapable future exposure.
Any serious cryptocurrency project marks itself as experimental software. I assume the same is true for CryptoNote/Monero (if that isn't the case, it should raise a red flag immediately). Ring signature privacy is a working scheme in the present but only a temporary fix and an experimentation on what can be done and what is feasible with current computing resources (even though it could be argued ring signature bloat is not scalable). To promote CryptoNote currencies as "drug money" or a safe haven of any sort while failing to mention the impending future of complete exposure is not only being reckless and irresponsible but is also endangering other people who might depend on an anonymity without a time limit.

This is quite interesting to read considering the immense popularity of this cryto-currency... Thanks for sharing with us all, especially here on Steemit.com
All for one and one for all! Namaste :)
Hello Eric and thank you for your feedback, much appreciated! I added a paragraph with new information which you also might find useful.
Thanks for the heads up! Namaste :)
What a seriously FUD article. I agree with your point "Safe Today != Safe Tomorrow", but the likelihood of RingCT being broken anytime in the near future is slim to none.
The reality is that Monero is one of the only (if not the only) cryptocurrency right now that offers real privacy. Could quantum computing break RingCT? Maybe. It could also break Bitcoin, PGP, SSL, and every other crypto.
Not sure who you are directing that at, but I've never seen a Monero dev promote it as "drug money". If you have evidence of that maybe you should include the link & reference.
yep, serious FUD. But not surprising from someone who is a long time Dash investor/pumper. He writes an article about Monero privacy and yet does not mention Stealth Addresses or the upcoming I2P? Nice try but no cigar.
https://www.monero.how/how-does-monero-privacy-work
https://www.monero.how/how-does-monero-work-details-in-plain-english
Regarding "drug money": I never said Monero devs promote it as such. However, the community at large irrefutably does. Just google "Alphabay Monero".
Indeed. People would be wise to not take the cryptonote anonymity for granted
people could be killed and die ;)
You make it sound like Monero is in a fixed state and unable to change. Quantum resistant cryptography is on the roadmap and will be introduced at some point within the next few years.
I agree: It can be fixed afterwards. Only the damage can never be undone by then.
Do you really think the day someone will break eliptic curve cryptography he will focus on Monero? You have to be more worried about nuclear codes and nuclear war than Moneros.
Great post man, I hope that Monero stays anonymous. Have some advice for people that want to make money with Monero. Read our investment detailed file for free: http://steem.link/4KnWc
No it is not surprising. He is a long time Dash investor. pumper and moderator on Reddit. I bet he is a Dash Master Node holder as well. A completely biased Monero perspective to say the least - obvious FUD poster and obviously has no clue of what he is talking about - or, he is just purposely lying and omitting pertinent information. If you want to learn about how Monero works including "stealth addresses" and other things this bozo (conveniently) left out of the article ... https://www.monero.how/how-does-monero-privacy-work
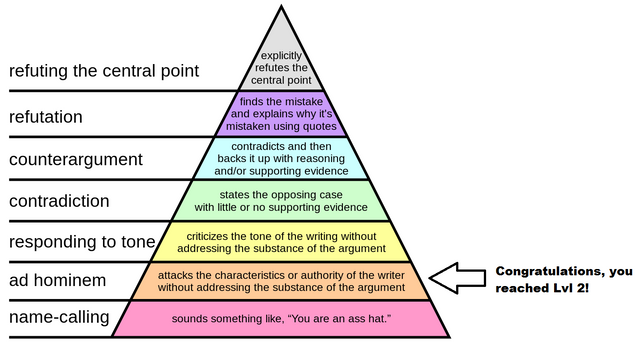
You seem upset. But that doesn't prevent you from reaching the top. Reality does.
Even the FBI thinks Monero privacy is good...
http://www.coindesk.com/fbi-concerned-about-criminal-use-of-private-cryptocurrency-monero/
Not that its proof either way, but do you trust the FBI? I don't think thats a good call.
Congratulations @macrochip! You have completed some achievement on Steemit and have been rewarded with new badge(s) :
Click on any badge to view your own Board of Honor on SteemitBoard.
For more information about SteemitBoard, click here
If you no longer want to receive notifications, reply to this comment with the word
STOPCongratulations @macrochip! You have completed some achievement on Steemit and have been rewarded with new badge(s) :
Click on any badge to view your own Board of Honnor on SteemitBoard.
For more information about SteemitBoard, click here
If you no longer want to receive notifications, reply to this comment with the word
STOPBy upvoting this notification, you can help all Steemit users. Learn how here!
Steemit is really a tribune of retarded idiots who have no clue about cryptography. This article is just a succession of lies.