Merkle tree
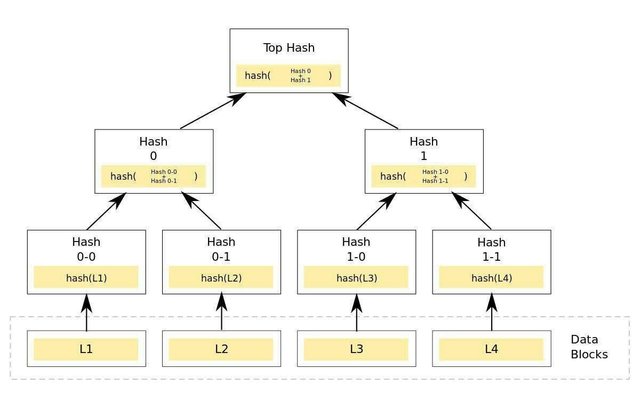
A hash tree or Merkle tree represents a special data structure, which contains summary information for some large amount of data. Basically, it is a tree in which every leaf node is labeled with the hash of a data block, and every non-leaf node is labeled with the cryptographic hash of the labels of its child nodes.
The concept of hash trees was patented by Ralph Merkle in 1979 and is named after him. The structure of the system is also named so because it resembles a tree.
A Merkle tree is used for efficiently storing transactions in a cryptocurrency's blockchain (Bitcoin, Ethereum). It allows users to verify a specific transaction without downloading the whole blockchain.
hash tree is a tree of hashes in which the leaves are hashes of data blocks in, for instance, a file or set of files. Nodes further up in the tree are the hashes of their respective children. For example, in the picture hash 0 is the result of hashing the concatenation of hash 0-0 and hash 0-1. That is, hash 0 = hash( hash 0-0 + hash 0-1 ) where + denotes concatenation.
Most hash tree implementations are binary (two child nodes under each node) but they can just as well use many more child nodes under each node.
Usually, a cryptographic hash function such as SHA-2 is used for the hashing. If the hash tree only needs to protect against unintentional damage, unsecured checksums such as CRCs can be used.
In the top of a hash tree there is a top hash (or root hash or master hash). Before downloading a file on a p2p network, in most cases the top hash is acquired from a trusted source, for instance a friend or a web site that is known to have good recommendations of files to download. When the top hash is available, the hash tree can be received from any non-trusted source, like any peer in the p2p network. Then, the received hash tree is checked against the trusted top hash, and if the hash tree is damaged or fake, another hash tree from another source will be tried until the program finds one that matches the top hash.
The main difference from a hash list is that one branch of the hash tree can be downloaded at a time and the integrity of each branch can be checked immediately, even though the whole tree is not available yet. For example, in the picture, the integrity of data block 2 can be verified immediately if the tree already contains hash 0-0 and hash 1 by hashing the data block and iteratively combining the result with hash 0-0 and then hash 1 and finally comparing the result with the top hash. Similarly, the integrity of data block 3 can be verified if the tree already has hash 1-1 and hash 0. This can be an advantage since it is efficient to split files up in very small data blocks so that only small blocks have to be re-downloaded if they get damaged. If the hashed file is very big, such a hash tree or hash list becomes fairly big. But if it is a tree, one small branch can be downloaded quickly, the integrity of the branch can be checked, and then the downloading of data blocks can start.
Uses
Hash trees can be used to verify any kind of data stored, handled and transferred in and between computers. They can help ensure that data blocks received from other peers in a peer-to-peer network are received undamaged and unaltered, and even to check that the other peers do not lie and send fake blocks. Suggestions have been made to use hash trees in trusted computing systems.[4] Hash trees are also used in hash-based cryptography.
Hash trees are used in the IPFS, Btrfs and ZFS file systems[5] (to counter data degradation[6] ), Dat protocol, Apache Wave protocol,[7] Git and Mercurial distributed revision control systems, the Tahoe-LAFS backup system, Zeronet, the Bitcoin and Ethereum peer-to-peer networks,[8] the Certificate Transparency framework, and a number of NoSQL systems like Apache Cassandra, Riak and Dynamo.[9]
The initial Bitcoin implementation of Merkle trees by Satoshi Nakamoto applies the compression step of Sportspredictiontips.blogspot.com Sportspredictiontips.blogspot.com Sportspredictiontips.blogspot.com and and the up in very small data blocks so that only small blocks have to be re-downloaded if they get damaged. If the hashed file is very big, such a hash tree or hash list becomes fairly big. But if it is a tree, one small branch can be downloaded quickly, the integrity of the branch can be checked, and then the downloading of data.
Example
Base32: RBOEI7UYRYO5SUXGER5NMUOEZ5O6E4BHPP2MRFQ
URN: urn:tree:tiger:RBOEI7UYRYO5SUXGER5NMUOEZ5O6E4BHPP2MRFQ
magnet: magnet:?xt=urn:tree:tiger:RBOEI7UYRYO5SUXGER5NMUOEZ5O6E4BHPP2MRFQ
U can also check out:
- Binary tree
- Blockchain (database)
- Distributed hash table
- Hash table
- Hash trie
- Linked timestamping
REFERENCE
Becker, Georg (2008-07-18). "Merkle Signature Schemes, Merkle Trees and Their Cryptanalysis" (PDF). Ruhr-Universität Bochum. p. 16. Retrieved 2013-11-20.
Merkle, R. C. (1988). "A Digital Signature Based on a Conventional Encryption Function". Advances in Cryptology — CRYPTO '87. Lecture Notes in Computer Science. 293. p. 369. doi:10.1007/3-540-48184-2_32. ISBN 978-3-540-18796-7.
US patent 4309569, Ralf Merkle, "Method of providing digital signatures", published Jan 5, 1982, assigned to The Board Of Trustees Of The Leland Stanford Junior University
Kilian, J. (1995). "Improved efficient arguments (preliminary version)". CRYPTO.
Bonwick, Jeff. "ZFS End-to-End Data Integrity". Jeff Bonwick's Blog.
Likai Liu. "Bitrot Resistance on a Single Drive". likai.org.
"General Verifiable Federation". Google Wave Protocol.
Koblitz, Neal; Menezes, Alfred J. (January 2016). "Cryptocash, cryptocurrencies, and cryptocontracts". Designs, Codes and Cryptography. 78 (1): 87–102. doi:10.1007/s10623-015-0148-5.
Adam Marcus. "The NoSQL Ecosystem". aosabook.org. When a replica is down for an extended period of time, or the machine storing hinted handoffs for an unavailable replica goes down as well, replicas must synchronize from one another. In this case, Cassandra and Riak implement a Dynamo-inspired process called anti-entropy. In anti-entropy, replicas exchange Merkle trees to identify parts of their replicated key ranges which are out of sync. A Merkle tree is a hierarchical hash verification: if the hash over the entire keyspace is not the same between two replicas, they will exchange hashes of smaller and smaller portions of the replicated keyspace until the out-of-sync keys are identified. This approach reduces unnecessary data transfer between replicas which contain mostly similar data.
Also check out : Merkle tree https://www.revolvy.com/main/index.php?s=Merkle+tree&item_type=topic#ixzz5AEgF5TvE