ABC Online:
Multiply p and q to get 187. ... call this value N — ... one of your public key numbers. Your second public number is a smaller one, which you can choose, and goes by the nickname e. There are some rules that restrict your choice*, but ... say ... invenglobal:
Asymmetric cryptography is a method that sends an encrypted message to a particular receiver who is the only one allowed to read the contents, although all users can check the ... authenticity. The blockchain network uses asymmetric cryptography ... Infosecurity Magazine:
Serious Cryptography – A Practical Introduction to Modern Encryption written by Jean-Philippe Aumasson, is an incredibly detailed and practical guide to modern encryption, written by one of the foremost authorities in applied cryptography and co ... EurekAlert (press release):
The BBVA Foundation Frontiers of Knowledge Award in the Information and Communication Technologies category goes, in this 10th edition, to Shafi Goldwasser, Silvio Micali, Ronald Rivest and Adi Shamir for their ... contributions to modern ...and more ... Gizmodo:
In a speech earlier this month, FBI Director Christopher Wray carried on the time-honored agency tradition of claiming that Silicon Valley can backdoor encryption safely if its workforce just nerds a little bit harder. The argument, made by Wray and ...and more ... Exchange News Direct:
The hard questions for individual computer system operators involve when and how to address the problem, given its uncertain timing and the evolving solutions. This research will seek to explain the problem in detail for both non-technical and ... NewsClick:
So far, around 80 per cent of all Bitcoins that can be created have been released into the system. Anybody who buys, sells, or creates Bitcoins, needs a personal key, a string of characters known only to the person. The private key pairs with a public ... FedScoop:
There are two reasons why ... difficult the communicate the urgency surrounding quantum computing, he said: explaining what it is and predicting when ... coming. And while predictions for mainstream arrival range between 10 and 30 years, the ... Globalnews.ca:
Kenneth E. Gray Jr., a lecturer in the University of New ... department of criminal justice and retired FBI special agent, agrees with ... sentiments on unbreakable encryption. “In the event that you have, say, a terrorist that is planning to ... iProgrammer:
... RSA algorithm (whose initials correspond to their surnames) which is explained in ... article on Public Key Encryption and is still a widely used protocol, particularly in combination with other techniques. Shamir and Rivest, now working ...
|
Follow our Community for More ! |
|
WHAT IS ENCRYPTION AND DECRYPTION ? | CONCEPT EXPLAINED (IN HINDI)
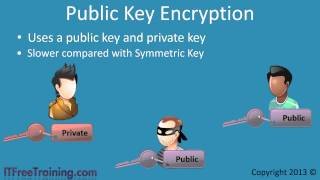
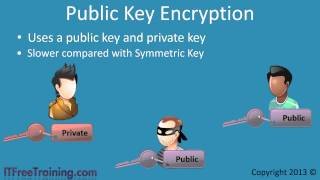
SYMMETRIC KEY AND PUBLIC KEY ENCRYPTION
WHAT IS WHATSAPP END TO END ENCRYPTION | HOW TO USE THIS.
END-TO-END ENCRYPTION HOW TO ENABLE IN WHATSAPP'S || TRICKS ||

HOW TO ENCRYPT YOUR ANDROID DEVICE
|
Latest posts from our Team ! |
|
[ Note for @steemcleaners / @cheetah ] The agreement of our Team: The following authors decided to create a Team in order to collaborate and share formats and content in our posts. Any copy of content between this Team does not constitute a plagiarism: @realskilled @rssniper @rspower @ali.wood @matthew.davis @rstracer @megan.brown