InfoWorld:
Encryption should be at the heart of every product or service that stores any kind of customer data. Several other security measures are necessary too, but when they fail -- as often they do -- you would want your customer data to be encrypted. ... ... Fibre Systems (press release):
Quantum computers will challenge existing communication privacy signature schemes where the key used to encrypt and decrypt messages depends on difficult computations. One of the most popular, the RSA algorithm, uses a large number as a public key ... iNews:
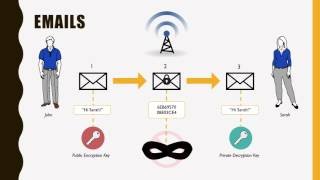
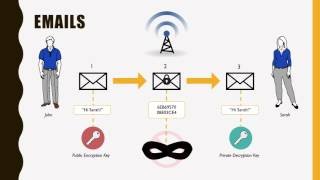
They both use ... to unlock the code and translate the message from gibberish into something meaningful. Symmetric key encryption is when the information is encoded and decoded using the same key. So say you are using a chat app, the chat app knows ...and more ... Networks Asia:
It seems like one after the other, and ... just in the last few months. ... why organizations need to be crypto-agile, expecting to transition from one encryption standard to another at a ... notice. ... the world we live in. Crypto ... TechCrunch:
While not quite a Canon 5D Mark IV, ... new multi-lens L16 will probably best the oversized rudders of competitors to get an on-camera encryption solution to market. The Palo Alto-based company has suffered its share of shipping delays, but company ... WIRED:
Public keys are long, so you ... just pick up a secure phone and read out the characters to the other person. You need a secure email exchange. By enlisting Lee once again, both Snowden and Poitras could anchor their trust in someone when setting up ... Ars Technica:
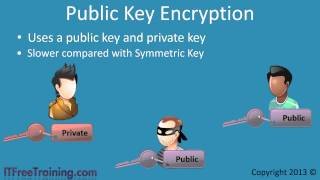
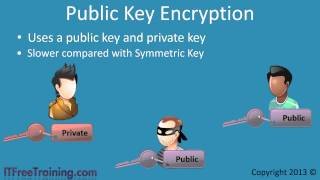
Until the 1970s, all publicly known encryption schemes were symmetric: the recipient of an encrypted message would use the same secret key to unscramble the message that the sender had used to scramble it. But that all changed with the invention of ...and more ... 99 Bitcoins (blog):
There are lots of different methods of encryption, each using different algorithms with their own advantages and disadvantages (such as AES, RSA, Twofish, Elgamal), but we ... need to actually understand them to use them. However, we will learn about ... BBC News:
Two graduate students stood silently beside a lectern, listening as their professor presented their work to a conference. Usually, the students would want the glory. And they had, just a couple of days previously. But their families talked them out of ...and more ... Naked Security:
Thanks to Dorka Palotay and Fraser Howard of SophosLabs for their behind-the-scenes work on this article. A few readers have asked us about a ransomware variant with the intriguing name of Mole. Interest seems to have been sparked by a recent security ...
|
Follow our Community for More ! |
|
PUBLIC KEY ENCRYPTION
PUBLIC KEY CRYPTOGRAPHY: RSA ENCRYPTION ALGORITHM

SYMMETRIC KEY AND PUBLIC KEY ENCRYPTION
HOW DOES A BLOCKCHAIN WORK - SIMPLY EXPLAINED
|
Latest posts from our Team ! |
|
[ Note for @steemcleaners / @cheetah ] The agreement of our Team: The following authors decided to create a Team in order to collaborate and share formats, content, and profits. Any copy of content between this Team does not constitute a plagiarism: @rspower @rssniper @matthew.davis @rstracer @megan.brown @realskilled @ali.wood

For future viewers: price of bitcoin at the moment of posting is 8171.40USD