Toledo Blade:
The transaction ledger is public, Mr. Wu said, but the parties conducting the transactions are private, identified only by a numeric key. ... easy to track once you have the key,” Mr. Wu said. One high-profile example was the Federal Bureau of ...and more ... Dartmouth Review:
James Detweiler ... who many consider the foremost authority on blockchain among students at Dartmouth, was particularly far ahead of the curve. Detweiler first gained an interest in blockchain in 2015, during his Freshman spring on an LSA+ in Rome ...and more ... Council on Foreign Relations:
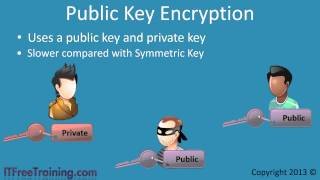
... secured with public key encryption. All transactions of most cryptocurrencies are recorded publicly on a universal and immutable distributed ledger known as the blockchain. Cryptocurrency users send funds between wallet addresses on the blockchain ... IT PRO:
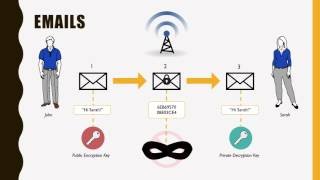
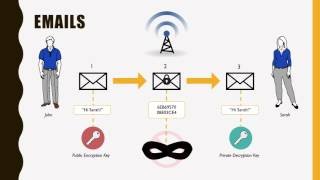
PGP uses layers of encryption, including public and private keys, in order to secure the content of whatever it is the user wishes to protect. For simplicity, as ... most widely used to encrypt emails, we will use an email for our example. Once the ... Automation World:
“This summary is then encrypted with the ... private key pair and appended to the data—this small encrypted block is the signature,” says Rooyakkers. “The complete appended signature record will also identify the signer, specify the cryptographic ... The Paypers (press release) (blog):
A blockchain identity management (IM) system, uses public/private key encryption and data hashing to safely verify data via the blockchain. A ... identity and data are stored on their device, and they are the only person that can determine which ...and more ... SemiEngineering:
More recently, however, chip companies and researchers have been exploring PUF as a way to create unique, undiscoverable, unchangeable identification numbers that can serve as the private key in public/private key networks and become the basis for much ... American Enterprise Institute:
Possession of the private key for an address allows the generation of transactions sending bitcoin from that address to another. Generating a valid sending transaction is not feasible without knowing the private key. The public and private keys are ...and more ... PR Newswire (press release):
Every message will be encrypted with a process whereby a public blockchain transaction on the EOT [ Encryption of things ] blockchain is used to encrypt the message and then sent to the key of the receiver on the EOT blockchain. A very small amount of ...and more ... Now. Powered by Northrop Grumman. (blog):
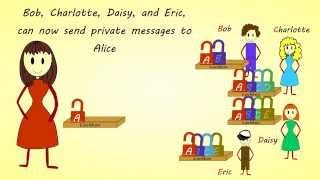
Sender and recipient ... need to agree in advance on specific code words, but only the encryption and decryption keys. Computer encryption systems are based on ciphers, and a whole branch of mathematics has developed around the techniques for ...
|
Follow our Community for More ! |
|
ASYMMETRIC ENCRYPTION - SIMPLY EXPLAINED
SYMMETRIC KEY AND PUBLIC KEY ENCRYPTION
HOW ASYMMETRIC (PUBLIC KEY) ENCRYPTION WORKS
PUBLIC KEY ENCRYPTION
PRIVATE KEY AND PUBLIC KEY
|
Latest posts from our Team ! |
|
[ Note for @steemcleaners / @cheetah ] The agreement of our Team: The following authors decided to create a Team in order to collaborate and share formats and content in our posts. Any copy of content between this Team does not constitute a plagiarism: @megan.brown @realskilled @rspower @rssniper @matthew.davis @rstracer @ali.wood
Your post is very nice,it gave me great idea!!!!!!!