Android Authority (blog):
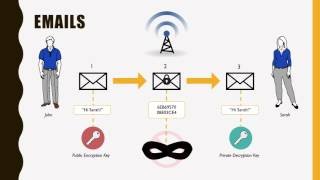
So what is encryption? It is the process of taking plain data, including text, and converting it into an unreadable (by humans or computers) form. The encryption process is based on a key, the analogy here being a lock which needs a key, and only ... Android Authority (blog):
Gary explains · How does public key cryptography work? – Gary ... Their secure and distributed nature means that traditional barriers are removed, however their reliance on public key cryptography can cause a lot of damage if (or when) a private key is ...and more ... Android Authority (blog):
If you look at the specs of any given generation of iPhone and compare it to the specs of a flagship Android phone from the same year, then you will notice that the iPhone tends to have less RAM. As a result some people have concluded that iOS apps ...and more ... Android Authority (blog):
In my previous article/video how does encryption work? I wrote about the principles of encryption starting with the Caesar cipher and following the development of cryptography through to the modern day with systems like DES and AES. All these systems ...and more ... Android Authority (blog):
... not free, in the sense that ... need some powerful hardware and a way to pay the hefty electricity bills, but bitcoin mining is a way to obtain some cryptocurrency without having to buy it on the market. Miners ... really do ... Creating a ...and more ... Android Authority (blog):
These imposter apps steal keys from you and then drain your accounts. Granted, each ... First, there was the Malwarebytes report about how millions of Android devices are unwitting crypto miners due to downloading malicious applications. ... How does ...and more ... seattlepi.com (blog):
The book promises to address the key question - will automation take away a select few of our jobs or conquer everything and make humans obsolete? - while explaining how best to prepare for whatever may come. Walsh, a leading expert in Artificial ... Irish Times:
Prof Gary McGuire, at UCD School of Mathematics and Statistics leads a research group working on the topic. “Blockchain technology uses a type of public-key cryptography known as elliptic curve cryptography,” he says, “which uses the complicated ... Light Reading:
Equinix, Inc., the global interconnection and data center company, today announced the launch of Equinix SmartKey, a global key management and encryption Software as a Service (SaaS) offering that simplifies data protection across any cloud or ...and more ... Blockchain News:
The report, entitled “The Quantum Countdown: Quantum Computing and the Future of Distributed Ledger Encryption”, is part of the Swiss-based Cardano Foundation and ... Distributed Futures research programme, dedicated to blockchain, cryptocurrencies ...and more ...
|
Follow our Community for More ! |
|
LEARN PUBLIC KEY CRYPTOGRAPHY IN JUST 18 MINUTES - CRYPTOGRAPHY TUTORIAL
PUBLIC KEY ENCRYPTION
HOW DOES ENCRYPTION WORK? - GARY EXPLAINS
ASYMMETRIC ENCRYPTION - SIMPLY EXPLAINED
INTRO TO ASYMMETRIC KEY CRYPTOGRAPHY

|
Latest posts from our Team ! |
|
[ Note for @steemcleaners / @cheetah ] The agreement of our Team: The following authors decided to create a Team in order to collaborate and share formats, content, and profits. Any copy of content between this Team does not constitute a plagiarism: @matthew.davis @ali.wood @megan.brown @rssniper @rstracer @realskilled @rspower