Goldilock - securing your sensitive digital assets.
Introduction:
Cryptocurrencies and Sensitive digital assets have come to stay, and we as owners of sensitive digital assets must do our very best to ensure the safety and security of our cryptocurrencies and/or sensitive digital assets. However, it would seem that we have been going about it the wrong way all these while. Well, there is no need to fret, as GOLDILOCK has come to show us the right way to safeguard our cryptocurrencies and/or sensitive digital assets.


GOLDILOCK:
GOLDILOCK is a storage system built on the blockchain. GOLDILOCK makes other storage system method of storage look like a child’s play.
Some storage system make use of cold storage solutions to store cryptocurrencies and/or sensitive digital assets. However, this is not effective and efficient, as paper and USB thumb drives can be damaged, stolen or misplaced. Now, I know most of us would decide to store our sensitive digital assets in a bank vault. While this is very secure for you if you do not want to trade, it is unsuitable for people that require swift accessibility to their sensitive data, as it could days to access the USB thumb drive, even when it is needed urgently. Even encrypted cold storage solutions offered by some groups such as Xapo or Coinbase are not effective and efficient, as accessibility is extremely limited.
Other storage system make use of hot storage solutions. This is better than the cold storage solution, when we look at accessibility, as all you need to access your sensitive digital assets is the internet. However, when we look at security, the hot storage solution is ill-advised, as it is a public knowledge that anything on the internet can be hacked. We have seen it happen in the last few years.
GOLDILOCK makes use of both the cold storage solution and the hot storage solution to store sensitive digital assets.
The sensitive digital data are stored offline in a physical device (cold storage) via a physical airgap mechanism. Through this mechanism, the sensitive digital data cannot be accessed from the internet.
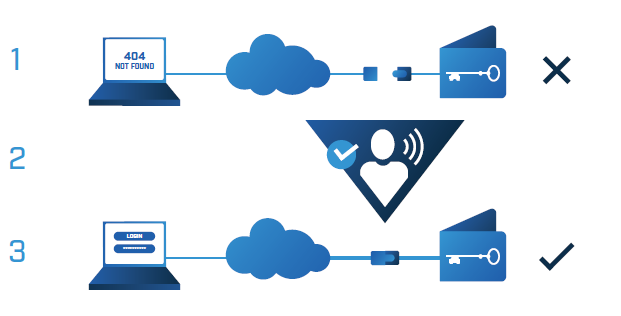
To access their sensitive digital data, the physical device containing the sensitive digital data is connected to the internet (hot storage) via non-IP technology that is securely encrypted. Using the required access credentials, the user can access the sensitive digital assets through a dedicated URL.

The combination of both the cold storage solutions and hot storage solution ensures that GOLDILOCK guarantees high end security and accessibility for sensitive digital assets of users.
I mean, you cannot hack something that is not connected to the internet. Even when the user connects the physical device containing the sensitive digital assets to the internet to gain access, the user is given a limited amount of time to access the digital assets through non-IP technology that is securely encrypted.
Talking about accessibility, with GOLDILOCK, all you need to access your sensitive digital assets is the internet. Hence, as you can rightly guess, accessibility is at a crazy enviable level. Even with this high level of accessibility, GOLDILOCK uses dedicated per-user hardware to process storage of encrypted data and also dedicated URL to access the sensitive digital asset. This means that, you can be sure that your sensitive digital assets are private to you, and only you have access to them.

The GOLDILOCK Security Suite:
Some applications and/or services included in the GOLDILOCK Security suite are:
GOLDILOCK Wallet:
This is an application that is highly recommended for cryptocurrency investors. With the features which the GOLDILOCK Wallet possess, cryptocurrency investors can be rest assured of security. These features includes:
- The wallet would be run inside a web browser that is authenticated over Secured Shell (SSL)
- The keys for each respective wallet would be stored on a physical device that is not connected to the internet.
- The wallet would only be brought online and accessed via non-IP mechanism
- Each respective wallet would have a personal and distinctive URL assigned to it
- Once the user is done accessing the wallet, the wallet is closed, and then, the unique wallet device is disconnected from the internet.
- Each transaction that would be signed requires a Two-factor authentication
GOLDILOCK API Services:
This gives an interface for institutions that use other wallet solutions to make use of GOLDILOCK’s airgap technology to store sensitive digital assets/information.
GOLDILOCK’s Colocations:
A colocation refers to a data center facility where institutions can rent space for servers and/or other computing hardware devices. With the GOLDILOCK Colocation, institutions can rent physical vaults that are strictly dedicated to GOLDILOCK in data centers to run their servers and still have direct control over their servers.
On-Premises Deployment Option:
With this option, user can use physical devices to remotely operate the air-gap mechanism to ensure security.

Recall that I made mention that GOLDILOCK would be based on the NEO blockchain. Now, I am sure that some of us would want to know why GOLDILOCK decided to use the NEO blockchain. Well, GOLDILOCK is making use of the NEO blockchain because the NEO blockchain has the following features:
Ability to audit digital assets and transactions:
GOLDILOCK attempts to entice large companies and governments to come operate on the blockchain, and for this to happen, these large companies and governments need to be able to audit digital assets and transactions. This is where NEO blockchain comes to play. You see, the NEO blockchain is building a digital identify mechanism that is capable of issuing and confirming digital identities via the Public Key infrastructure (PKI) X.509 standard.
Delegated Byzantine Fault Tolerance (dBFT):
The dBFT is a consensus mechanism that is an improvement to both the Proof of Work and the Proof of Stake consensus mechanism. With the dBFT consensus mechanism, holders of NEO tokens would vote for delegates and then, these delegates must reach an agreement before transactions are made. Also, with the dBFT consensus mechanism, transactions are processed faster (10,000 transactions per second) at no transaction cost. This is due to the fact that, with dBFT, the NEO blockchain is a platform that does not require numerous computer resources to verify transactions.
As we all know, two cannot work together, unless their goals align. With the features above, the NEO platform aligns with GOLDILOCK’s goal of providing their users an effective and efficient way to store sensitive digital assets.

Benefits of using GOLDILOCK:
A whole lot of benefits could be gotten by different institutions that decides to use and/or integrate GOLDILOCK. Let’s check them out:
For Individuals:
Indiviuals can take adavantage of GOLDILOCK's colocation and ensure that their sensitive digital assets are stored securely, effectively and efficiently.
For Insurance companies:
When people want to sign up for insurance policy in an insurance company, the insurance company asks for some personal details and/or scanned documents. These personal details and/or scanned documents are then stored in an email or drives that are prone to hacks. Once attacks take place, the insurance companies lose their credibility.
However with the integration of GOLDILOCK, personal details and/or scanned documents are kept offline, and are only brought online when they are needed. This means that, after the user signs up for the insurance policy, the personal details and/or scanned documents go back offline, which makes it secure, and free from hacks. With this, insurance companies have their credibility intact.
For Banks:
Any bank that integrates GOLDILOCK into their existing database would be making their database free from hacks/online attacks. This is due to the fact that the bank’s database is always offline and it only comes online when there is need for data to be fetched from users’ accounts. This greatly secures the bank’s database.
For Hospitals and legal institutions:
With the integration of GOLDILOCK, hospitals and legal institutions would no longer be prone to hacks/online attacks. This is due to the fact that the data of users are always kept offline and are only brought online when the need arises.
For institutions that require cold storage solutions:
When these kind of institutions integrate their existing technologies with GOLDILOCK, they can be sure of having high end accessibility to stored digital assets. Attached with this high accessibility is security and privacy.
For institutions that require hot storage solutions:
With GOLDILOCK been integrated into their existing technologies, these institutions can take advantage of the airgap mechanism to ensure security, while having their digital assets private to them.

GOLDILOCK Token (LOCK token):
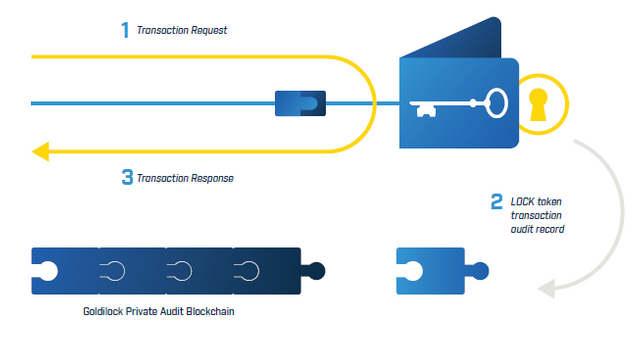
The Lock token would be the token that powers the GOLDILOCK platform. The lock token would be register as a NEP-5 asset on the NEO blockchain. It is with this Lock token that users would be able to uses the GOLDILOCK services/applications such as the wallet, etc.
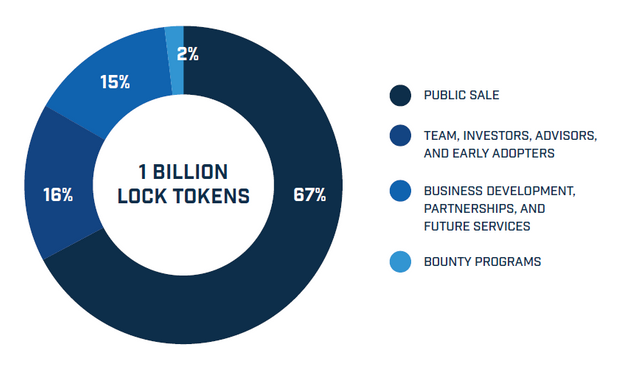
Below is a diagram that shows the Lock token allocation.
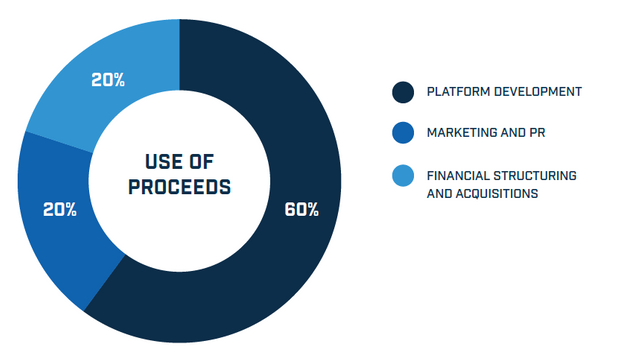
Below is the image that shows the use of the proceeds gotten from the Lock token sale.

Use-Cases:
Use-Case 1:
With the rate of hacks and attacks on cryptocurrency’s wallet, Mr. Oboh is scared of venturing into the cryptocurrency world. However, with GOLDILOCK Wallet Application, Mr. Oboh is sure of security and thus he ventures into cryptocurrency. With his trust in the security gotten from GOLDILOCK Wallet Application, he preaches the cryptocurrency gospel to his friends. This begins to cause mass adoption of cryptocurrencies in his community.
Use-Case 2:
Mrs. Yarinya needs to undergo a surgery at Toto Hospitals. However, she is weary of giving out her health records to the Hospital, as she saw on the news that hackers hack medical records of patients and sell them on the black market. However, with GOLDILOCK, Mrs. Yarinya can just connect her physical device to the Internet, and the doctors can check the information they require to perform the surgery. Once, the doctors are done going through the health information, Mrs. Yarinya can disconnect the physical device from the Internet, thus, the surgery can take place without putting her health information at risk.

Conclusion:
GOLDILOCK is here to ensure the secure storage of sensitive digital assets such as cryptocurrencies. And once cryptocurrencies can be well protected, mass adoption of cryptocurrencies is achieveable, as users are sure that their cryptocurrencies would be protected.
Every institutions that handles sensitive data should integrate the GOLDILOCK solution into their existing technologies, as with GOLDILOCK, high end security and accessibility is ensured.

More Information & Resources:
- Goldilock Website
- Goldilock WhitePaper
- Goldilock Tokenomics
- Goldilock Telegram
- Goldilock Discord
- Goldilock LinkedIn
- Goldilock Facebook
- Goldilock Twitter
- Goldilock Reddit
- Goldilock GitHub

GOLDILOCK in the news:
GOLDILOCK is on the news. Doubt me? Check the links below:

Check out this Video:

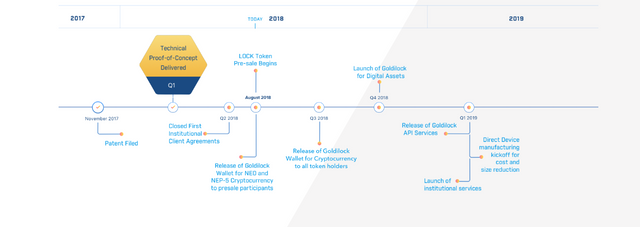
The GOLDILOCK roadmap:

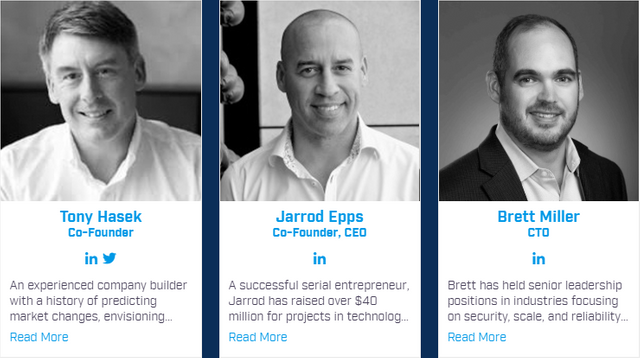
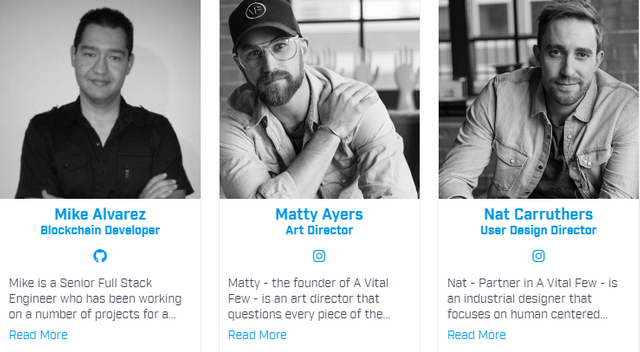
The GOLDILOCK Team:

The GOLDILOCK Advisors:

The GOLDILOCK partners:


This is an @originalworks sponsored contest

Link to Tweet:
https://twitter.com/okiTwiTs/status/1026812773261565953?s=19

goldilocktwitter
goldilock2018
Hello! I find your post valuable for the wafrica community! Thanks for the great post! We encourage and support quality contents and projects from the West African region.
Do you have a suggestion, concern or want to appear as a guest author on WAfrica, join our discord server and discuss with a member of our curation team.
Don't forget to join us every Sunday by 20:30GMT for our Sunday WAFRO party on our discord channel. Thank you.
Hahahahaha... I hope I can also recommend the hospital to Mr Dickson!! He's also having same issues!! 😂 😂 😂
Recommend the hospital. Goldilock is securing their medical records
Lolz... Wish you d best of luck in the contest..
This post has been submitted for the @OriginalWorks Sponsored Writing Contest!
You can also follow @contestbot to be notified of future contests!
Great entry as always @okipeter. I see that @originalworks appreciated your work :)
Thank you for making people aware of importance of the security nowadays and providing methods to increase its accuracy.
All the best