Goldilock: Your trusted offline security platform

Long before cryptocurrency became popular people kept their money in hidden places till banks were built and the responsibility of keeping money save was shifted to the banks. This banks build a strong room with couldn't be easily accessible but with time technology took over most of its operations and then people tried penetrating through the internet but all they could do was increase their figures but the cash in the bank remained safe.
Years later blockchain stormed the internet and interest of individuals and organizations. It was used to create digital currencies for exchange purposes. This currency had no physical form so hackers took advantage of its formlessness. Now we hear of companies and organizations been hacked despite their firewall and anti theft software.
What is Goldilock?

Do you always think of how to securely store your coin/data?
Imagine a platform which utilizes blockchain to provide an experience like that of or even better than our local banks when it comes to storing of crypto coins.
GoldiLock provides a storage system, which acts as a cold storage until such time that the user needs access to their funds/data.
Just like a cold room which stores food(coin) and prevents the action of bacteria(hackers) in a room different from the natural environment temperature( offline store/cloud).
This year the crypto market has experienced the worst with 2 massive hacks in less than 7 months. If this persists cryptocurrency might be threatened to restart or close down.
Aim and Objective
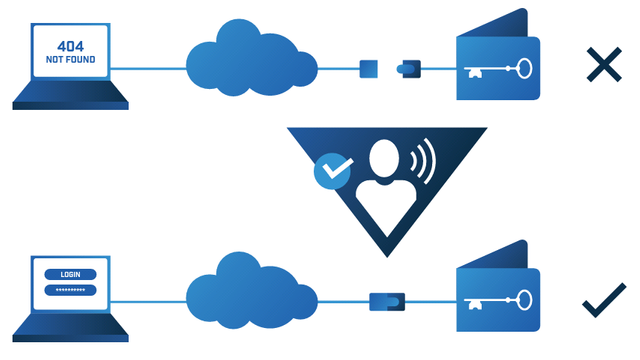
Reducing/Eradicating the possibility of hacking by using an offline/non IP technology with several secure authentication layers
It is done this way because of the belief that internet access encourages hacking/cyber theft, which is true in almost all cases.
Authentication Process Flow
Whitepaper page5
This means provides access just for a limited time to the offline device in which the user needs access to their private/sensitive data, the hardware device which stores all their information is then connected to the internet.
To shine more light on this let's look at an example. If i have a bitcoin wallet that partners with Goldilock this is what would happen, when I open my wallet which needs internet connection my private information wouldn't be shown because little from my personal observation I noticed that people tend to visit their wallets even if they have nothing to do there. So therefore as a user I would need to request for my details and immediately i would be connected to the offline device which stores it. This connection would be timed for security purpose, no risk is too small to take.
This is know as "physical airgap disconnection"
Current Storage Solutions
Current Procedures:
- Centralized - Exchanges, online wallets etc.
- Personal Cold Storage - Trezor, Ledger Wallet, Hard drives etc.
Centralized Storage
Majority of people in the space are familiar with the defect relating with centralized asset storage methods.
The users of an exchange/online wallet have no idea as to where their coins are stored or power over over the storage they believe the company/organization in charge of the wallet would be the one to worry about that alone which is true but it also affects the users if theirs a large scale hack.
Centralized storage procedure take the control of private keys to the keeper of the exchange/wallet private key.
Personal Cold Storage
This storage give a larger amount of promising security in terms of keeping your coin/data online. There are several hazards which can affect the physical devices that keep the private information e.g breaking or loosing the device
disadvantages of personal cold storage:
- Their's no access to the data when the device is not present.
- Device could be damaged or misplaced causing for the permanent loss of data.
Application
Source
This is a software designed to provide
GoldiLock quality services.
Very useful for the storing of personal information that you don't want to be known or lost, organizations would find it very helpful with regards to security.
Identity
When we talk of identity it requires a very high level of security because when we want to dive into things official we deal with accurately and precision. Normally documents like this could be scanned to an email and sent to the recipient but this would expose such data to hacking or stealing.
But now the advantage of
GoldiLock is that it allows access for that short instance in which it is needed after which the data goes offline, not penetrable by anyone.
Credit Score
We have heard of countless cases where by banks would be robbed and information of their customers exposed.
This is where
GoldiLock would be very helpful because with the database of the bank offline it would be virtually impossible to hack since it would only come on when the data is been accessed and I believe that it is well designed to only allow that fraction of information which is needed to be online at a particular instant.
Wallet
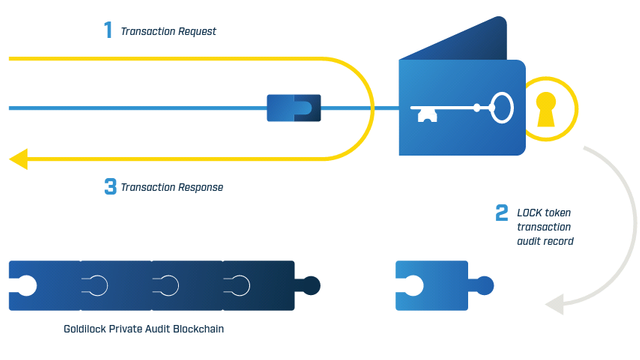
GoldiLock allows for the storing of cryptocurrencies in such a way that it doesn't affect the user's operations. The user is allowed to move freely withing the application but on demand for a secured/sensitive data there is a temporary connection between the app and the hardware thereby causing the hardware to come online via a non IP trigger mechanism.
GoldiLock Token
GoldiLock Token known as
Lock would be used to power the platform.
Whitepaper Page10
NEO will be the first blockchain to be integrated, with others following shortly.
The Goldilock Wallet service can be paid for on a subscription basis by
Lock.
Lock will also grant users a history of their node activity so you can monitor things from your own end as well.
Circumstances for Usage

As an Individual:
Imagine the risk I face by moving my documents and credentials with me on every journey. If I was to go on a journey and then at the airport my luggage gets mixed up and given to another person. If all my original documents and credentials are in it I wouldn't be seeing myself having a good time but instead a troubled one. But with the help of
GoldiLock my documents and credentials can be safely kept at home and all informations needed can be accessed with the power of just a click. Now no more worries about my documents and credentials because
GoldiLock has got me covered.
As an Organization:
Are you facing cyber security issues, your data gets hacked or is prone to, do you spend more on security upgrade than the estimated amount?
Why wait for a miracle when it's already here.
GoldiLock offers the most promising security ever by implementing NEO as its bases and others to build platform that doesn't just keep your data save from hacking but also from carelessness of operators.
Team
Adviser
Partners
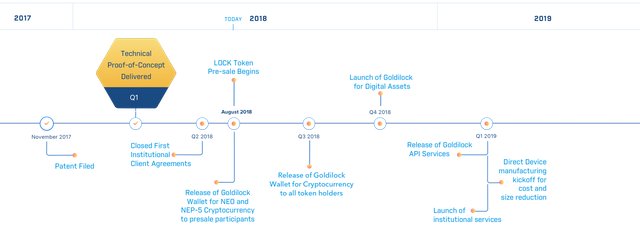
Road Map
Resources
Official Website
Whitepaper
Token Description
Telegram
Discord
Facebook
Twitter
LinkedIn
Github
Reddit
goldilock2018
https://steemit.com/crypto/@originalworks/810-steem-sponsored-writing-contest-goldilock
https://twitter.com/Ifechigo/status/1026571456174542849?s=20
goldilocktwitter
This post has been submitted for the @OriginalWorks Sponsored Writing Contest!
You can also follow @contestbot to be notified of future contests!
I'm open for corrections if you notice any. Thanks for reading
@resteemator is a new bot casting votes for its followers. Follow @resteemator and vote this comment to increase your chance to be voted in the future!