COVA - Creating a new Internet of Smart Data
COVA's solution would make the internet smarter; imagine an internet that conforms to your desire it doesn’t give room for data breach instead it learns from you. This new internet will be configurable in a sense that each user dictate how their data is used and transferred, you no longer need to fear for your privacy because it is now interwoven into the very data you are protecting.
The international network (internet) is a global network of computers that facilitates communication and sharing of content. The internet comprises of protocols, such as transport layer protocols like TCP/IP, and application layer protocols such as FTP, HTTP, SSH. These protocols make sure that data is properly packetized, addressed, transmitted, routed, received, and interpreted — it ensures that data gets to the intended destination.
Currently, the internet is composed of "Mindless data" data that is easily exposed and abused this have resulted into breaches that causes loss of valuable resources. Now imagine a new kind of internet that is made up of Smart Data that remembers, keeps a secret, and learns from its users. In case you are wondering what this smart data is going to be like here is an example of what it is:
- That a shopper’s mobile GPS data may not be used with her other data to construct an intrusive customer profiling.
- That these text messages can only be viewed after tonight.
- That a patient’s CT scan may be processed by an aggregate function and not rendered individually.
- That my credit card number may only be used once for a one-time charge. It will be erased from the server after the payment is completed.
- An ad or disclaimer has to be viewed before the rest of the content.
- and lot more
The internet would be lot more smarter and secured if it's composed of smart data and COVA wants to make this possible by creating an internet that uses smart contacts which forms a network of 'Smart Data' that keeps secret, learns from its users and improves upon the internet for the better.
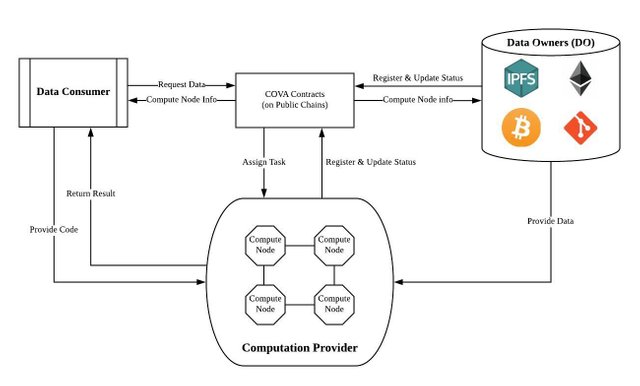
Their approach uses "Trusted Execution Environments (TEE)", TEE is the nodes that run on the chain and provide the high computational power that the chain needs to carryout it functions. It makes sure that any data that moves across these nodes will not be readable to the node owners and ensures that it privacy and security are kept. And also “Centrifuge” a Policy Specification Language (PSL) that specifies data usage policies in programming language and a Policy Enforcement Framework (PEF) that enforces the PSL through code. Finally, “CovaVM" a Policy Enforcement Framework (PEF) that enforces the policy written in Centrifuge. CovaVM is the counterpart of the Ethereum VM.
COVA's team is composed of prodigy hackers, awards winners in ACM, IOI, veteran Harvard and Silicon Valley coders.
Want to know more about COVA check them out on:
On their website: https://covalent.ai
Or Read COVA’s white paper: https://github.com/covalent-hq/wiki/wiki
You can also
Follow COVA’s Official Telegram Group: https://t.me/covalentofficial
Follow COVA’s twitter: https://twitter.com/@covatoken
Follow COVA’s Medium: https://medium.com/@covatoken

With GDPR bringing to attention Data privacy and the importance, this could be a good time for a project like Cova
Also with all the reports of recent data breaches by companies and attacks by hackers trying to access user data it's important projects like Cova can come up with solutions.