Goldilock, The Digital Safe
How do you store your sensitive data and crypto assets?
Personally, I save my info on Telegram's cloud services. It allows me to save my data and private keys for free and access them on multiple devices at a time. I have always wondered what will happen if it gets hacked. I don't have much, but it's all that I have. I had thought that was the best on the market until I heard of Goldilock.
What is Goldilock?
Goldilock is a security system that will revolutionized how individuals and corporations store their data and crypto assets. Goldilock is a security system that is disconnected cold storage, and becomes hot storage when a user needs access to their data. It is a combination of cold and hot storage systems, and I will tell you about that in a bit.
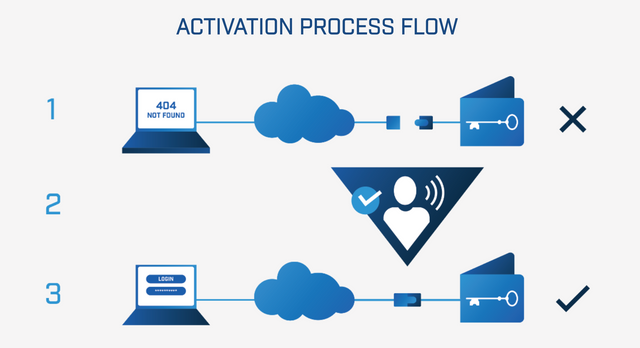
Goldilock's encrypted nodes work like a bank's vault. It remains offline, physically disconnected from the internet until a user remotely brings it online through a non-IP command. A user can then have access to their data and cryptocurrency and perform whatever transactions they want to. After the user is done using their node, the node goes back to an isolated physical air gap environment, invisible and inaccessible from the internet.
Goldilock is built around the idea that, everything online can, and will be hacked data point in time. Over the past few years, almost all sectors have received their fair share of data breaches. Sometimes very sensitive and personal information is stolen from this breaches. Other times, billions of dollars are stolen, proving that no industry is safe from data breach.
Source: WhitePaper, Page 5
Hot Storage: is when you store your data and cryptocurrencies online or on cloud. I requires minimum technical know how to use. Customers of such platforms often have no idea or power over how their data and crypto assets are stored. These websites and storage platforms could have security flaws, exposing the funds and data of users to attacks. In just 2018, over $750m in crypto assests have been stolen.
Cold Storage: is when you store your data and cryptocurrencies offline, often in a physical device. The biggest disadvantage is when you lose the device or it gets damaged. Device always has to be handy whenever you need access to your data and crypto. A user often needs to be a bit tech-savvy to use cold storage. Large companies and agencies like banks, healthcare providers and credit agencies can not use this form of storage.
Goldilock can be used in a wide variety of fields. Goldilock can be used by individuals to store personal information and cryptocurrencies. Large institutions can also use Goldilock to store their crypto and customer data.
Identity
Goldilock grants users access to their data on a per need basis. It only comes online so users can have access to it. After a user has verified their identity, the data goes back offline. There are huge gaps in the current identity verification methods. People have to handle documents physically or scan and email the required information.
Goldilock LOCK Token
Goldilock will use LOCK tokens to serve as a gateway for their services.
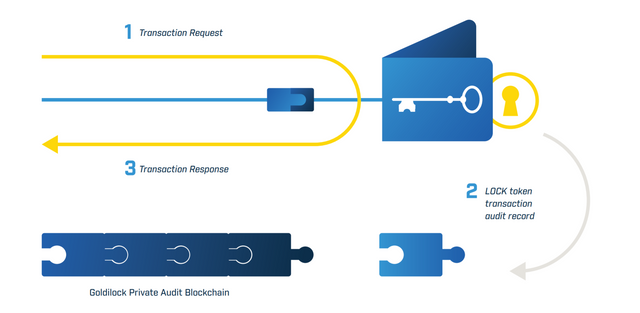
The LOCK token is required to access the Goldilock Wallet. When the user logs into the Goldilock Wallet, the Wallet will query the NEO public Blockchain to confirm the user’s public key address owns a LOCK token. If the user’s public key address owns a LOCK token, then the Goldilock Wallet will launch in the user’s browser. When the user is granted access, the Wallet will write audit information to our own Private Audit Blockchain. These audit entries will ensure that every time your private key is brought online, this access is written to immutable storage that can be queried from the Goldilock Wallet.
LOCK token allows Goldilock to provide users with a record of their node activity, while keeping user-owned data encrypted and locked away even from everyone including the Goldilock team.
Source: WhitePaper, Page 10
NEO will be the first cryptocurrency to be integrated, with others following shortly thereafter.
The Goldilock Wallet service can be paid for on a subscription basis by LOCK.
USE-CASE
Personal
Someone I know once tried having access to my telegram account. He knew my phone number, so registered telegram on his phone with my number. He then called to say he was doing some registrations online that will fetch him money. He had already used his number, so couldn't use same number again. He said he entered my number, so when I receive any code, I should send it to him. I was just lucky he wasn't close to me at that point in time. He could just see the notification on my phone without unlocking my phone and have access to all my funds. Goldilock seeks to prevent this kind of trouble. Your funds and data are easy to access, but only by you.
Cormecial
In April 2017, the website of GN bank was hacked. GN Bank or Group Nduom Bank, is owned by Ghanaian business man, Mr. Paa Kwesi Nduom who was the flag-bearer for the PPP in Ghana's 2016 elections. Here in Ghana, hacking is something that sounds far fetched. Lot's of people who have accounts with GN Bank trooped to various branches of the bank, asking for their funds. The bank lost a lot of money and most importantly, the confidence of some customers. If GN Bank had a system like Goldilock, they could have easily assured customers that thier funds were very safe because it's offline, so can't be hacked. Goldilock could have saved GN Bank huge sums of money.
More Information & Resources:
- Goldilock Website
- Goldilock WhitePaper
- Goldilock Tokenomics
- Goldilock Telegram
- Goldilock Discord
- Goldilock Linkedin
- Goldilock Facebook
- Goldilock Twitter
- Goldilock Reddit
- Goldilock Github
If you will like to take part, check out the contest post here
Twitter link: https://twitter.com/fredkese/status/1026883343483318273
goldilock2018
This post has been submitted for the @OriginalWorks Sponsored Writing Contest!
You can also follow @contestbot to be notified of future contests!
You just got upvoted by 50.0% upvote from @getkarma courtesy of @fredkese
This is an advertised post
The author of this post or one of his supporters has used one or more paid services to promote this post. This post's valuation and number of upvotes does not represent human curation. This means this post's valuation does not represent community appreciation and should be viewed as advertised content.
If you are new to these services please be warned that bid voting is a huge gamble with little return on investment if not utilized right and might also lead to a net loss.
If you like this service please update this comment for visibility and to support paying for the server costs.
Thanks
You got a 10.12% upvote from @joeparys! Thank you for your support of our services. To continue your support, please follow and delegate Steem power to @joeparys for daily steem and steem dollar payouts!