Goldilock - The ultimate digital data storage solution!!!
Introduction
The internet has become the center of IT revolution of the 21st century. This is because everything kept online is instantly accessible from any where at the speed of a click. Little wonder that almost every human endeavor and activity has found a solution online. Even though we have gone many steps ahead of time in our online activities, having sensitive digital data online presents its own risks. With the ever-present danger of hacking and frequent cases of intrusion, how do we store and ensure top safety of sensitive digital data - for example cryptocurrency wallet keys - and still make them available whenever and wherever we need them? Several possibilities have been mentioned. However, in this article, we take a deep look at Goldilock - a genius invention that will ultimately change how digital data is stored and accessed with security and quick accessibility as the core strengths of this unique solution.
What is Goldilock
The current wave of cryptocurrency technology has offered unlimited opportunities of investment for individuals and organizations. For individuals with blockchain wallets and other digital assets, security of investment is a recurring headache. Organizations too fear the worst with everyday reports of hackers breaking into secure systems and making away with valuable digital cash and other digital property. Generally, everything stored online carries overhead risk of loss, theft or destruction. This enormous risk factor is what Goldilock offers to eliminate.
Goldilock has dug deep into the mind of digital criminals and offers a digital assets security portfolio that keeps digital property beyond the reach of unauthorized users but within swift reach of original owners. It works by securely storing digital assets like cryptocurrency wallet keys, health records, credit card details, etc in an isolated physical storage platform. Goldilock employ layers of secure authentication to keep digital data completely isolated and safe; making them available only when they are needed. Since everything stored online could be hacked and stolen, Goldilock keeps your digital assets off harms way by securely storing them on a platform disconnected from the internet.
Why today's storage systems are flawed
Owners of digital assets are basically forced to choose either of two known vulnerable storage methods.
1. Traditional Cold Storage: This involves the use of personal hardware like CD's, flash drives, hard drives, personal server, or other devices to store digital property. Storing wallet keys in banks or using encrypted cold storage solutions like the one offerred by Coinbase are all in this category.
Shortcomings of cold storage:
Digital assets stored using cold storage is not completely safe. What happens in the case of natural disasters like flood, hurricane, or earthquake. The data and its storage medium is lost or destroyed. Cold storage is also prone to theft, hacking, misplacement or other data loss events. In the case of an encrypted cold storage system, the stored data may not be easily or quickly accessible and this defeats the objective of a cryptocurrency trading organization or individual.
2. Hot Storage: Hot storage carries the biggest risk factor since it stores data "securely" online. The fact remains that nothing is secure online. The best systems in terms of online security have been breached. Hacking cases continue to rise in frequency and severity.
So from the above analysis, it becomes obvious that if individuals or organizations want to keep digital assets completely safe and instantly accessible, traditional or hot storage solutions are not to be considered.
If that is the case, then there should be a system that combines the best of the two worlds. There is!! Look no further, Goldilock offers digital assets security that gives peace of mind.
Goldilock takes the best parts of cold and hot storage and built a superior storage infrastructure that worths a second look. See how it works.
The Goldilock Core Components - how they are integrated.
Goldilock essentially has 4 major components that works together to cover every possible application of Goldilock to individual cryptocurency enthusiasts, trading organizations or any other body in need of wallet key custody and general digital assets storage solution. We will take a look at each component:
1. The Goldilock Wallet: The Goldilock Core Development team will be in charge of developing Goldilock wallet for individual cryptocurrency users and investors. This initial development will be designed to store and handle cryptocurrency transactions using NEO, GAS, and NEP-5 tokens.
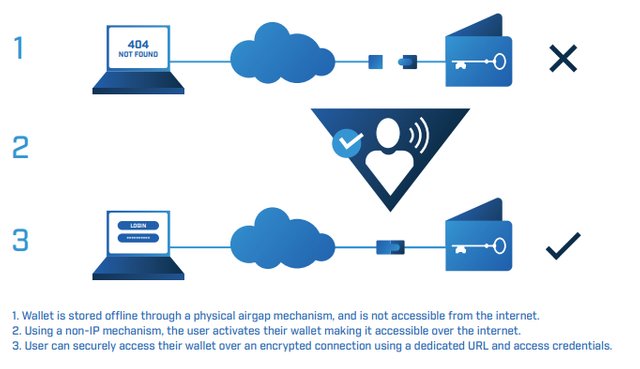
How the Goldilock wallet works: Users or investors are given Goldilock cryptocurrency wallet which runs inside a web browser. Each wallet has a personal URL that can only work with it. No two wallets can have the same URL. The wallet key is safely stored in a unique, encrypted hardware wallet device. This device kept offline. To make use of the wallet, the user goes through a two-step authentication process. First, a non-IP command and second, a PIN/voice verification is issued over the Public Switch Telephony Network (PSTN). If the verification steps are successful, the user is authenticated and access is granted for the transaction. The wallet remains online for the limited time of the transaction. Once the transaction is completed and the user is done with the wallet, the wallet is closed and the unique hardware wallet device will be automatically disconnected from the Internet pending when another transaction is due.
2. Goldilock API Services: For organizations with already made wallet systems or ones that want to develop and run their unique, objective-driven apps on top of the Goldilock framework, the Goldilock API services come handy. It creates a streamlined means to plugin into the Goldilock and take advantage of the unique storage services by Goldilock.
Goldilock API will be deployed physical vaults stored in various data centers all over the world. The organized obtain a lease of these vaults and have a completely secluded infrastructure to run run internal, sensitive applications for their organization's use.
Goldilock API is well suited for institutions who need to leverage remotely-operated airgap technology to store sensitive information, including private crypto keys and critical digital assets.
3. Goldilock Colocations: Colocations are physical storage hardware or digital assests silos kept safely in data centers scattered across the globe. These data centers are built and maintained by Goldilock to service institutions that prefer to store and access digital property on a "dedicated" or private hardware. They lease the vaults and make use of them to run corporate internal apps and also store sensitive digital property for their organization.
4. On-Premises Deployment Option: This works hand-in-hand with the colocations explained above. They are physical devices that enable remotely-operated airgap security used in operating the physical vaults. Digital data storage and processing can happen on spot, anywhere no matter the location of the physical vaults. This option serves both private individuals and corporate organizations.
Why was Goldilock built on NEO
NEO is a unique blockchain technology so different from what others offer. While many blockchains focus on offering security or utility tokens, NEO goes beyond. NEO is a distributed network-based blockchain technology to secure digital assets using digital identity and smart contracts. By building a system fully focused on digital asset, digital identity and smart contract, NEO hopes to set a standard in digital assets management recognized and approved by organizations various governments of the world.
Again, because NEO built its blockchain as a distributed network where stakeholders benefit from the smart economy, the blockchain can grow and sustain the needs of its users in the future.
SO because of developing community-based blockchain that benefits from digital assets, digital identity and smart contract management, NEO is the most ideal deployment platform for Goldilock as the two parties share the same vision for the future of blockchain technology.
Goldilock Token
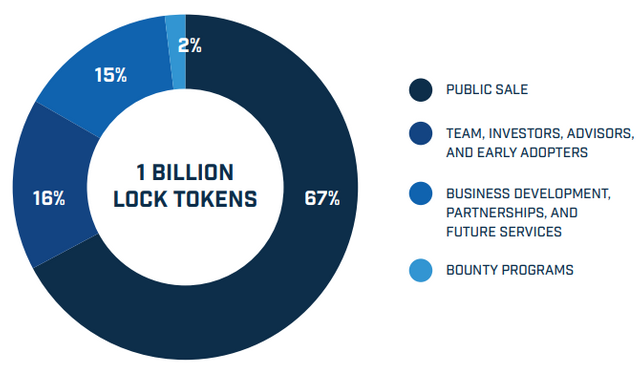
Goldilock utility Token is called LOCK. This token will be registered and 1 billion LOCK tokens minted for Goldilock transactions. These token will be used to store and access digital assets like cryptocurrency wallet keys, digital health records, credit card details and other digital property. Consider how the token is used for each transaction:
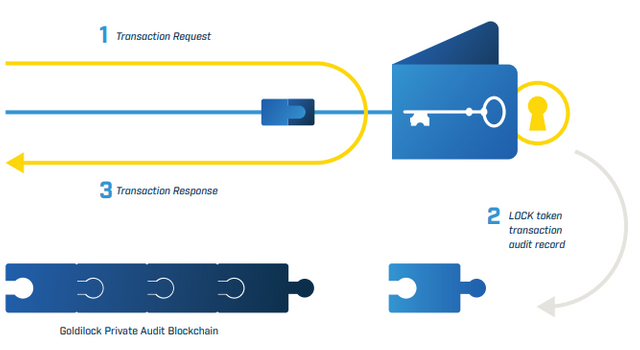
1. Transaction request: A user requests to login to his Goldilock wallet. The wallet queries the NEO blockchain to authenticate user's public key address and confirm that he has a LOCK token. Once confirmed, the wallet opens in the user's browser and is granted access to perform a transaction.
2. LOCK token transaction audit record: After access has been granted to the user to perform a transaction, the access record is permanently stored in Goldilock Private Audit Blockchain. This is to keep track of authorized logins and transactions performed on the user's wallet.
3. Transaction response: The user is allowed to perform his transaction- to store or retrieve digital property.
LOCK token allows Goldilock to provide users with a record of their node activity, while keeping user-owned data encrypted and locked away even from everyone including the Goldilock team. In addition, LOCK is to be the accepted method of subscription payment for individual users on the Goldilock Security Suite
How the LOCK token will be distributed
As mentioned earlier, 1 billion LOCK tokens will be minted for Goldilock transactions. The minted LOCK tokens will be distributed as shown in the chat below:
To preserve the project and protect token sale contributors there will be a mandatory six (6) month moratorium on selling LOCK Tokens for all founders and advisors. This policy will be built into the smart contract for total transparency.
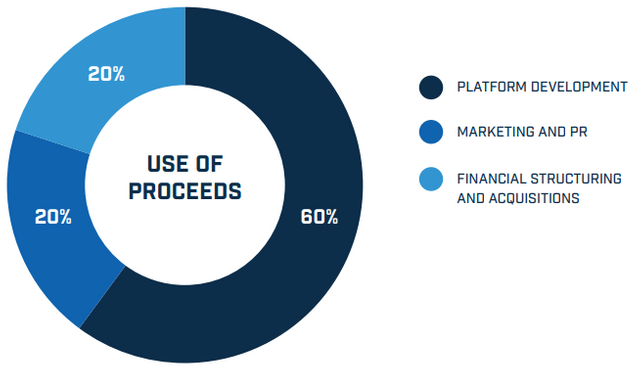
$50M USD will be raised from the token distribution and the funds will be utilized in the following manner:
Question: Who benefits from Goldilock technology? Answer: Everyone!
Goldilock for individual consumers: For individual users, Goldilock can be a powerful and secure tool to store private digital property like cryptocurrency wallet key, electronic medical records, credit and debit card information, insurance files, etc. Users are rest-assured that their digital assets are safe and secure from intruders using the unique solutions provided by Goldilock.
Organizations that handle sensitive records There are many institutions that deal with private records of their clients or customers. The following are top gainers in this case:
Hospitals: Throughout history, there have several cases of patient records loss, theft or mishandling. Also, storing patient records poses a great risk as sensitive data may be extracted, sold or collected illegally. Hospitals and medical institutions can safely store patient records offline and can retrieve them swiftly as at when needed by subscribing to Goldilock. Everyone is safe. Hospitals can avoid costly letigations from aggrieved patients whose personal life got leaked.
Banks: Banks handle lots of private data in form of credit card numbers, addresses, phone numbers, account numbers, etc. They also store sensitive hard copy files like house documents for customers. There will be no need for keeping lots of paper files if banks subscribe to Goldilock. Also, their electronic records can be safely kept in Goldilock Physical vaults and are retrieved when a transaction needs to be done.
Insurance companies: Many insurance companies have had to pay huge money to their clients because of data loss, theft or destruction. Many insurance companies current store client data in some cold storage or in the cloud. Goldilock utilizes the best of hot and cold storage. So if Insurance companies subscribe to Goldilock, they are sure there will be no data loss events. Goldilock can safely store client files and make them ready to use whenever needed.
Organizations that require cold storage: Remember that Goldilock utilizes the best part of cold and hot storage. If an organization requires cold storage, they are covered by Goldilock. They even have an added advantage of a second layer of security as Goldlock employs standardized hot storage security features like the SSL to secure data when they are being retrieved. This added incentive will serve as a core marketing strength to attract subscribers.
Organizations that rewuire hot storage: Many organizations use cloud storage facilities because they need instant access to their digital resources. If they embrace Goldilock, they will get far more than they bargained as Goldlock will also offer the offline storage mechanism which grantees that digital property does not remain a sitting and vulnerable target on the internet. They have this added layer of protection and they will be satisfied with the level of storage protection offered by Goldilock.
Use cases
Use case 1: Mr. Robert is a recognized independent researcher in the field of electronics. He has written lots of published papers about his research work. He uses a cloud storage service to save up all his published and published research work. Last night, he saw a news about the hack of a well-known cloud service provider. With the more frequent recent cases of hacking, he decided to find out about the rating of the cloud service he is using. unfortunately, he found out that his cloud service provider is rated 20th in terms of security. Fearing for the safety of his research papers, he decided to investigate other superior and more secure methods to store digital property. He stumbled upon Goldilock. He made further findings and discovered that Goldilock is the superior and unique solution he is looking for. He happily created a wallet with Goldilock, purchased some LOCK tokens and transfered all his works to Goldilock. He cancelled his subscription with the cloud service and is happy his files are now safe in the hands of Goldilock.
Use case 2: James have heard too much about crytocurrency. About the time he made up his mind to join the trend, his friend John lost thousands of dollars because the blockchain platform he was using got hacked. James was happy he was not a victim in that incident. Together, James and John approached Manley a well-known crypto trader and asked for advice. Manley adviced them to purchase cryptocurrencies with XYZ limited because they use Goldlock services to secure members crypto wallets. James and John created wallets with XYZ limited. 5 years later, they are still happy with the decision they made because no reports of hacking has been heard about XYZ limited.
Conclusion
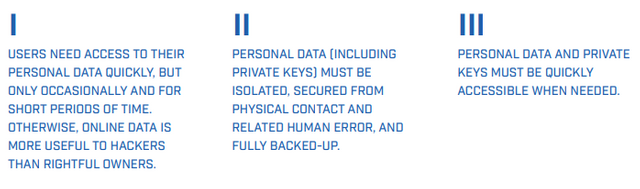
Goldilock is the ultimate solution for securing digital assests. It removes digital property from harms way by disconnecting the storage hardware from the internet. It makes the best use of cold and hot storage techniques to secure digital assets completly. To summ it up, Goldilock and its concept is built on 3 core areas that is badly lacking in today's storage solutions. Take a look:
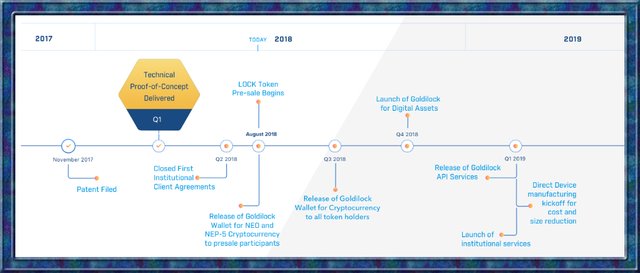
Goldlock Roadmap
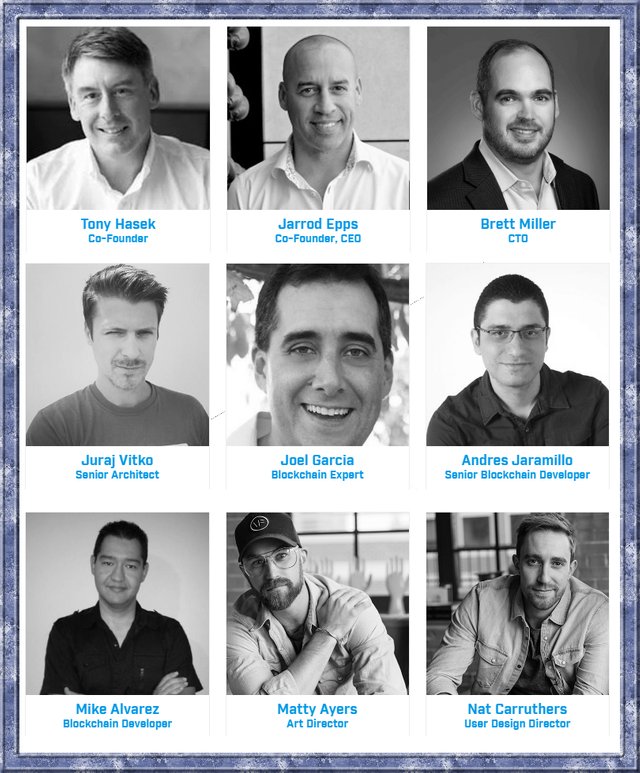
Goldilock Team
Goldilock Advisors
Goldilock Partners


Watch Goldilock introduction video
Find more information from the resource centers below:
Goldilock Website
Goldilock WhitePaper
Goldilock Tokenomics
Goldilock Telegram
Goldilock Discord
Goldilock Linkedin
Goldilock Facebook
Goldilock Twitter
Goldilock Reddit
Goldilock Github
Who Organized this Contest?
This contest was organized by @originalworks. You can participate in the contest by clicking here.
Image credits
Unless otherwise indicated, all images in this article were taken from the Goldilock website, Tokenomics and whitepaper.

My Twitter link
goldilock2018
goldilocktwitter

This post has been submitted for the @OriginalWorks Sponsored Writing Contest!
You can also follow @contestbot to be notified of future contests!
As a follower of @followforupvotes this post has been randomly selected and upvoted! Enjoy your upvote and have a great day!
Congratulations! This post has been upvoted from the communal account, @minnowsupport, by focusnow from the Minnow Support Project. It's a witness project run by aggroed, ausbitbank, teamsteem, someguy123, neoxian, followbtcnews, and netuoso. The goal is to help Steemit grow by supporting Minnows. Please find us at the Peace, Abundance, and Liberty Network (PALnet) Discord Channel. It's a completely public and open space to all members of the Steemit community who voluntarily choose to be there.
If you would like to delegate to the Minnow Support Project you can do so by clicking on the following links: 50SP, 100SP, 250SP, 500SP, 1000SP, 5000SP.
Be sure to leave at least 50SP undelegated on your account.