RIPA — A next generation exchange

The world is fast becoming a global village, technology is fast evolving and with this change comes a change in trade and an increased need for security in the trade process. RIPA exchange brings you the future of trade freely and most securely. It is the most secure place to be for both developers and end users.
What is the RIPA exchange?
What benefits do I as a manager get from RIPA?
With RIPA being an open source means 100% uniqueness for every exchange manager. This means that every manager can get the source base and alter the code as much as the desire without limitations. Just like with every other open source, alterations determine uniqueness and as every developer would appreciate being different, RIPA allows them to alter the source code. The source base will be realized under MIT license. However, they are a few things that may require the exchange manager to pay for. These will include, call center service, server space, network security operations among other factors that are needed for great client service.
With increased technology, introduction of the cryptocurrency and fiat money, the world has also seen a rise in the rate of cyber theft. This leads us to our next and most important question,
WHAT ABOUT MY SECURITY AS AN EXCHANGE MANAGER AND THE SECURITY OF MY CLIENT?
Not to worry, RIPA has you covered. The encryption of RIPA was done based on security and the AES256(Advanced Encryption Standard 256) established by the U.S National Institute Of Standards and Technology (NIST). This standard takes the highest number of bits in the standard thus it is 14 cycles of repetition for 256-bit keys. In short it is safe and secure encryption. With the clients in mind, RIPA did not adopt the whole of the PEATIO source code or open source base but decided to altar it by re-modularizing it so as to make a complete demarcation from client’s registry to the trade engine so that no end users information will be put at risk or under threat if the hacker or attacker is able to overcome the primary level of security, which is nearly impossible.
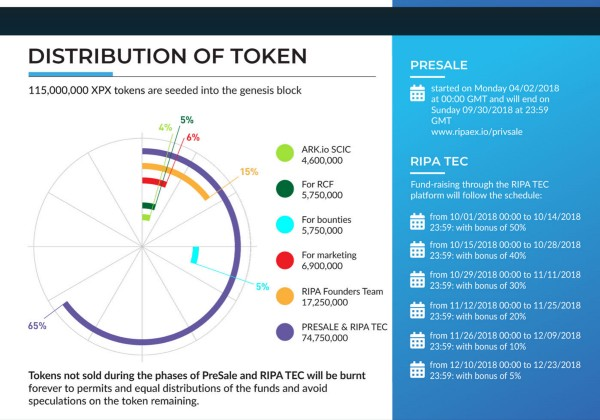
RIPA Tokens
Resources:
https://bitcointalk.org/index.php?topic=3759172
https://www.facebook.com/ripaex
https://t.me/ripaex
https://twitter.com/ripaex