Meet "BEAM": A Solution that Offers True Anonymity Coupled with Scalable Peer-to-Peer Transactions
We are now in 2018, and Bitcoin is still by far the leading digital currency and no doubt about it that, it is still as powerful as it was in 2008.
Why is it so? Oh yeah, it has to be so. The reason is simple and direct of course. This is simply because people are very passionate and concerned about how to carry out a transaction and store their money in a way that is very secure without depending on intermediaries like credit card companies, governments, banks, other centralized authority and their monetary policies.
All transactions in most cryptocurrencies including bitcoin can be traced. There is need for us to do everything in our capability to make sure we don't have any invalid transaction in a chain and that it was not controlled by any single entity in the process of achieving this (which is the main function that bitcoin nodes and miners perform), in order to give a demonstration that the validity of a system is viable or true.
The main idea behind this is that no participants in the system should trust people, but to trust an open network of computers that are not controlled by any single entity.
Blockchain transactions may appear more private due to the fact that they are not connected to your identity in a direct manner. A new wallet can be created by anyone at any point in time in an anonymous manner and transactions can done with it.
Nevertheless, it is not that simple as it seems.
There's no lie in it if I should say the most important promise of the blockchain technology is the state of being pseudonymous, of hiding one's true identity behind a pseudonym. All recorded and stored transactions in a public ledger are linked to the address of an account. Since this address are not directly connected to the identity of the originator, it seems very impossible to track the identity.
It's no lie that as long as the pseudonym covering the true identity of a person is not directly linked to that person, that person's identity is still very much anonymous. But as soon as they are directly connected by someone, the failure of anonymity would set in. An illustrative example of this is when law enforcement agencies during investigations brought into notice that they were able to identify specific users of Bitcoin, thereby making them non-anonymous and breaking into the privacy of the Blockchain transactions.
How does the failure of anonymity set in?
A transaction information can easily be leaked onto the web by cookies and web trackers on merchant website, where they can be used by any person without hesitation. Data can also leak from exchanges, OTC deals and the during the process of Blockchain data collection and clustering. These failure of deanonymizing has really discouraged a lot of companies, since they are aware that competitors, hackers, and other unauthorised parties can access the information of important business data that are uploaded into a Blockchain.
Let's consider few cases where the failure of anonymity would be very disastrous in blockchain.
Management of credentials such as private keys and passwords can not be useful in an open smart contract that is highly unsecured.
Records of electronic medical, which should never be deanonymized due to its sensitivity. They should be kept in ultimate privacy so that the confidential of a participant is not jeopardized.
Financial documents such as the salaries of employees should never be linked with addresses that are open to the public and are capable of being traced without difficulty.
Data required for the verification of identity, which include but not limited to social security numbers must not be stored in a smart contract which is not private and unsecured.
Anonymity or privacy has been a major challenge for individuals, institutions, industries and organisations that are very much concerned about confidentiality. Everybody want their transaction history and other private informations to be kept, so that nobody would be able to access it. Therefore, creating an opportunity for the emergence of private currencies. Quite a number of projects on private currencies have been developed, but the problem with most of this projects is that:
- They are not truly decentralized
- They are too computationally heavy
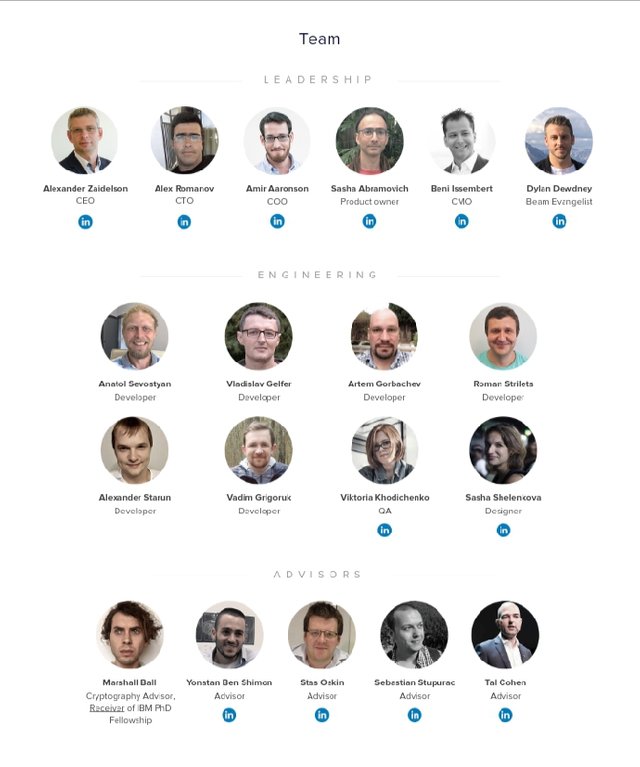
But come to think of it, isn't financial privacy a fundamental human right? Why do we have to feel like we are in bondage for something that is supposed to be a freedom to us? Well, the good news is that a significant team of first-class entrepreneurs and engineers have recognised the need for anonymity and have acted upon it. Thus, they gave birth to a truly decentralized currency called "BEAM".
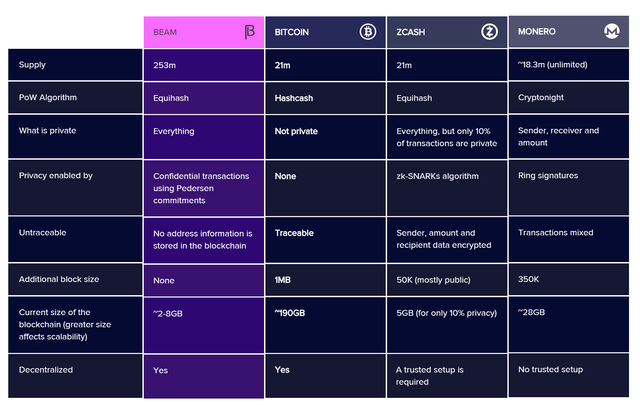
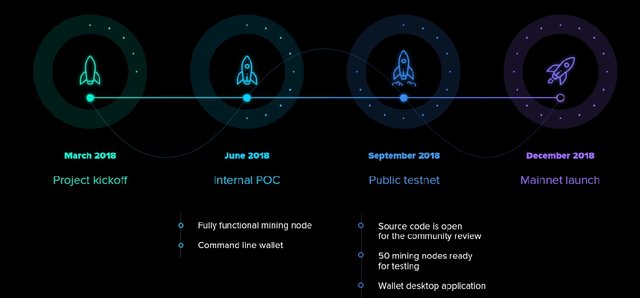
Just as I said earlier, BEAM is a truly decentralized and a next generation confidential cryptocurrencynext which works based on a forward looking MimbleWimble protocol with very strong privacy, scalability and fungibility. The transactions of BEAM are not accessible to the public by default, and it is not necessary to store all transaction history for the validation of blockchain, thereby causing reduction and improvement in the size of blockchain and scalability respectively.
The types of transaction that BEAM will support includes but not limited to: time-locked transactions, escrow transactions and atomic swaps.
The Outstanding Features that makes BEAM Unique - What can BEAM do?
Users are in total control of privacy. As such, they are in full charge of their personal data and can do with it anything they want in agreement to their will and applicable law. Therefore, the availability of information and to which party it is readily accessible to, is decided by users.
The need for trusted setup is out of place.
The mining of blocks that are done using Equihash Proof-of-Work Algorithm.
A team of professionals put it into practice from scratch in C++.
Confidentiality with no penalty: The Blockchain do not bloat in BEAM when confidential transaction is done, thereby keeping the history of transaction a secret, alongside its act of avoiding penalty on performance and scalability.
No address or the transaction information of a sender or receiver is stored in the blockchain.
The utilization of periodic halving with total amount of coins (210 million) bring about limited emission.
During the first five years, it is backed by a treasury emitted from all blocks. Also, there's no ICO and premine.
The cut-through feature of MimbleWimble BEAM blockchain brings about superior scalability through the compact size of blockchain.
Multiple types of transaction can be privately carried out such as time-locked, escrow and atomic swaps.
MimbleWimble is a new protocol that was published in August 2016 by an anonymous author, which recommended a refined and effective approach to the issue of confidentiality in blockchain.
MimbleWimble works based on two concepts which includes:
- Confidential Transactions and
- Transaction Cut-Through.
Confidential Transactions
It makes use of cryptographic commitment scheme which is backed with two fundamental properties: hiding and binding. This can be described as not been different from giving someone a safe box which is closed and which has some messages inside of it, that no other person but you know the combination for it. You can disclose the key at a proper time, and as long as the person can't know what the message was before receiving the key, he can make sure that your commitment is well grounded.
The popular commitment scheme known as Pedersen commitment, which is achieved by the use of Elliptic Curve Cryptography is what MimbleWimble make do with. It is in the form below.
C = r * G + v * H
Where;
C is a Pedersen commitment
r is a blinding factor
v is a secret key hiding the real value
G & H are generator point on a specific elliptic curve
Transaction Cut-Through
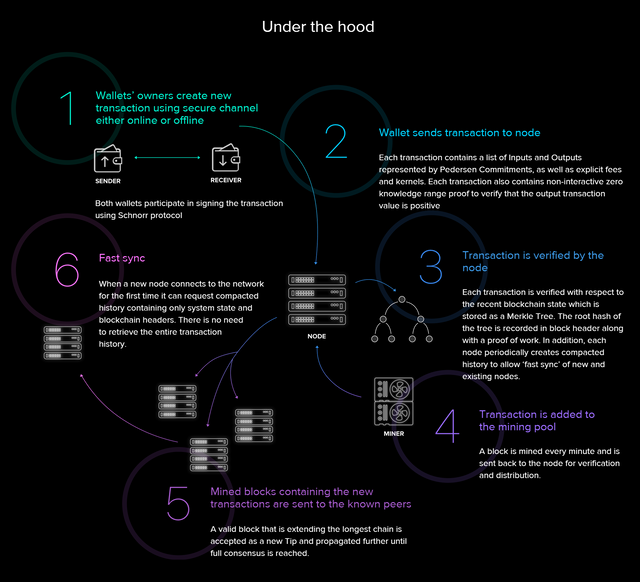
The combination of two factors in a linear form makes up each input and output of a transaction. That's factors include: The transaction actual value and a blinding factor. For ownership of UTXO (Unspent Transaction Output) to be transferred, there is need for its value and blinding factor to be disclosed to the receiver by a sender. The receiver will then make use of a different blinding factor in the creation of a new output commitment which is unknown to others but him/her.
Let's assume we have two transactions which is identical: from X to Y, and then from Y to Z, what can we do? Taking the linearity property of Pedersen commitments into consideration, we can definitely cut through the transaction that forms the intermediary, which then gives us a merged transaction from X to Z, which is a valid transaction in the system.
Block is a list of transactions, whereby each of the transaction has its list of inputs and outputs. Due to this, a block in a blockchain can be likened to be one large transaction, giving us a permission to cut through i.e combine all intermediate transactions into a whole both within a single block and throughout multiple blocks in the blockchain. The application of this principle helps create a system that has nothing to do with the entire transaction history (which is exactly how bitcoin works), but the current state of transaction only as they happened.
Therefore, The need to store any addresses in the blockchain becomes irrelevant since only the value and the unique blinding factor is required to prove ownership of the Unspent Transaction Output. A transaction can either be created online or through other secure mechanisms between two wallets. Irrespective of which one is used, nothing but the commitment is recorded in the blockchain.
What this is trying to emphasize is that: no matter the source of the attack, no matter the resources the attacker is using, there is no personal information that can be extracted from the blockchain.
BEAM is using Equihash mining, which is based on solving generalized birthday problems. Miners make use of Equihash PoW mining algorithm across the world. This is mainly because it is IO bound i.e contrary to bitcoin SHA256 where a lot of processing power is required, Equihash mining makes use of a large amount of storage. It is developed in such a way to make trade-off difficult between memory and processing power, consequently making it difficult with existing miners of ASIC during the period of its creation.
Due to the fact that a Blockchain is append only by definition, no data in the Blockchain is ever deleted from it.
The performance of BEAM in terms of the transactions number per second will not high enough to use BEAM as a medium of exchange. Due to this, there is belief that BEAM will mainly be used as a store of value.
BEAM have a UI wallet. An application of desktop wallet for Mac, Linux, and Windows will be released by BEAM at launch.
- Case 1 - Financial Documents
An investment bank known as "Diamond Private Investment Company" that deals with the provision of various services that are related to finance and others to individuals, institutions, corporations, and governments have been in operation for few years, and are well recognised for their unending services in new technology. They are experts in financial investments in relation to cryptocurrencies. However, they got to find out that most of the financial documents or informations of the company that are meant to be private are becoming a common entity for the general public.
The challenge that Diamond Private Investment Company face is that; the capitalisation table of the company which gives analysis of the company's equity dilution, percentages of ownership, as well as the value of equity which the investors, founders and other owners has in each round of investment. Another issue is that the salaries of employees are now publicly associated with addresses that can easily be traced by other people.
Not long from that time, the head of the company find out about BEAM, which is a decentralized currency and a next-generation confidential protocol with a strong privacy.
With BEAM, the company can make sure crucial and private informations about the company are not accessible by the public. It also make sure that those informations are not publicly associated with addresses that can easily be traced. With BEAM, companies do not need to depend on cryptocurrencies but they rather make use of one layer of technology in the handling of their finances.
- Case 2 - Credential Management
Paul has been a good and passionate fan of cryptocurrency ever since he got his fortune from the sale of bitcoin at a higher rate last year. We are all aware of the low rate of bitcoin at the moment. Due to this, Paul sees this as another opportunity to make millions by buying at low rates and selling when the rate is high just as he did last year. He has been in this system for a while and he is aware of the loopholes in the system which makes important credentials such as passwords and private keys to be made public and unsecured to various attackers.
After making some research, Paul read through this very same article on steemit which lead him to a decentralized currency with strong privacy called "BEAM". With BEAM, he is rest assured that all his private keys and passwords which forms the basis of ultimate security for his cryptocurrencies that is worth millions of dollars have no place in an open smart contract which is ultimately unsecured. Moreover, he is also rest assured that all the transactions he made from his wallet is very secured and confidential, as it will never be traceable.
It has been quite a while that Bitcoin has been in existence. After the creation of bitcoin, individuals, corporations, governments and others was elated that a new technology which promises pseudonymity is coming up, due to the fact that blockchain transactions are not tied to one's identity directly, which makes them appear more private. However, it is not as simple as we taught because over the years, we've found out that the failure of anonymity is becoming established on a daily basis. Everybody want the history of their transactions to be seen only by them. Everybody want their bank account balance to be unaccessible to everyone but them. Thus, thus gave the opportunity for the implementation of private currencies.
A lot of privacy coin have been implemented In a view to putting a stop to this failure of anonymity but most of them usually encounter one problem or the other. However, a team of vibrant individuals recognised this disadvantages and they developed a scalable confidential cryptocurrency called "BEAM".
BEAM works based on the operation of MimbleWimble to give users the well deserved freedom of privacy they needed in sending and receiving money in a way that is private and secured. The entire team of BEAM are working very hard to make BEAM an ultimate Store-of-Value coin.
For more information about BEAM, You can watch this video presentation by the CEO, Alexander Zaidelson:
BEAMtwitter



.png)



This post has been submitted for the @OriginalWorks Sponsored Writing Contest!
You can also follow @contestbot to be notified of future contests!