BEAM: Security and privacy

Introduction
Beam
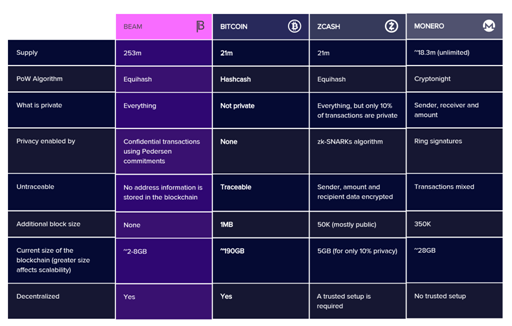
Beam cryptocurrency is a scalable confidential currency, since it uses the Mimblewimble protocol. Beam simulates Bitcoin and Mimblewimble to the Satochis offering users greater confidence in private transfers of assets, as it is done on an equal footing.

Source
Source
Mimblewimble automates the algorithms with the purpose of:
• Give users control over what transaction information is shared and with whom it is shared
• Make a thinner block chain with less transaction details per transaction: allowing faster confirmations and, therefore, very efficient scaling
• Tie multiple transactions in a single transaction, tying blocks in a single transaction, attaching a complete block chain in a single transaction
• Hide transaction values for the sake of privacy
• Hide addresses of both the sender and receiver
• Enabling multiple types of transactions privately: escrow, time locked, atomic swaps, etc.
This is how Beam offers the solution by keeping scalable peer-to-peer transactions in true anonymity.
Privacy. Problem and solution
People can track data, reduce the origin and end point of transactions and even though a cryptocurrency may seem anonymous, a careful analysis can be made of how the money has traveled and could reveal who the user is. This is a great concern that worries users who prioritize their safety.
Although there are Blockchains that promise an insurmountable privacy these are voluminous and computationally heavy, which makes them inefficient and prone to scalability problems as they grow to meet global demand.
That's why Beam, based on Mimblewimble, is the solution to this privacy problem. Mimblewimble enables privacy transactions without obstructing the network, since Beam is building its network from scratch in C ++ based on this protocol.
With the Mimblewimble protocol at its core, Beam can scale better for mass adoption, and by maintaining reasonable block sizes it allows total control over privacy.
Source
This protocol is based on:
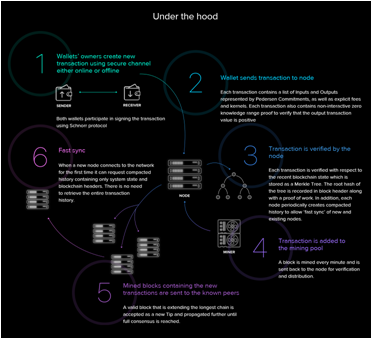
- Confidential transactions, since they use a cryptographic commitment scheme with two basic properties: concealment and linking.
- Reduction of the transaction, when this principle is applied in the blockchain the individual blocks further creates a system that only needs the current state of the transactions instead of the complete history of all the transactions as they occurred.
Source
By reducing the amount of data required to store and verify transaction data, this protocol works with smaller blocks, which can be tested in transactions, since they belong to the receiving user through the value of the message and the value of the factor. of blinding. After creating the transaction, only the commitment is recorded in the block chain; not the addresses of the users or the quantities exchanged.
Beam use case
Case 1:
Peter has made a large investment in cryptocurrencies and fears that they will track their transactions. When you tell Chris, he talks to you about Beam and explains that he can offer you what he is looking for: privacy in your transactions.
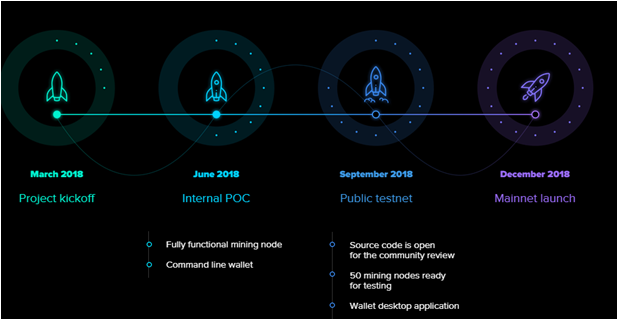
Roadmap
Source
Team

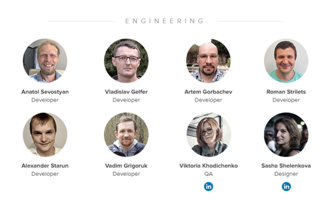
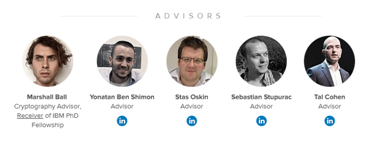
Source
More Information
beamtwitter
This post has been submitted for the @OriginalWorks Sponsored Writing Contest!
You can also follow @contestbot to be notified of future contests!