The Large Bitcoin Collider is Trying to Break Into Bitcoin Wallets
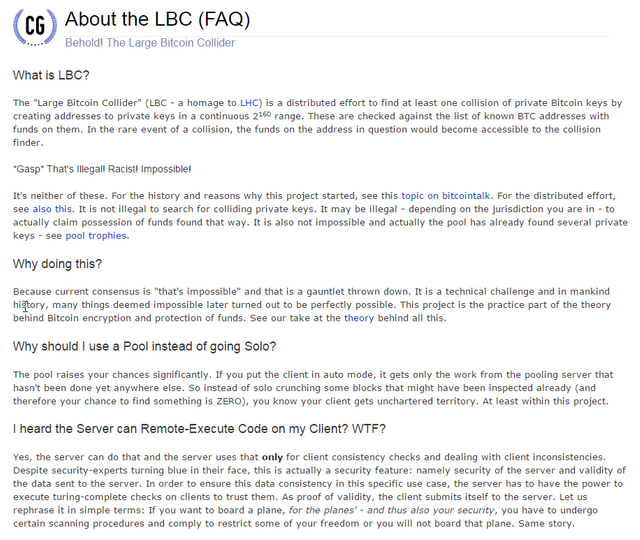
Since a year there is a project running where supercomputers are used to try and find collision keys in BTC wallets which have balance. Yes before nanocomputers came already bitcoin collider project is doing this using decentralized computers and they claim to already have cracked some wallets and got funds out.
If you are not math geek speaking shortly they want to prove that random string of numbers can be duplicated and this way they generate and seek for them.
Speaking shortly like currently you can mine in pools to find a block, they made software which allows you to pool mine for private keys.
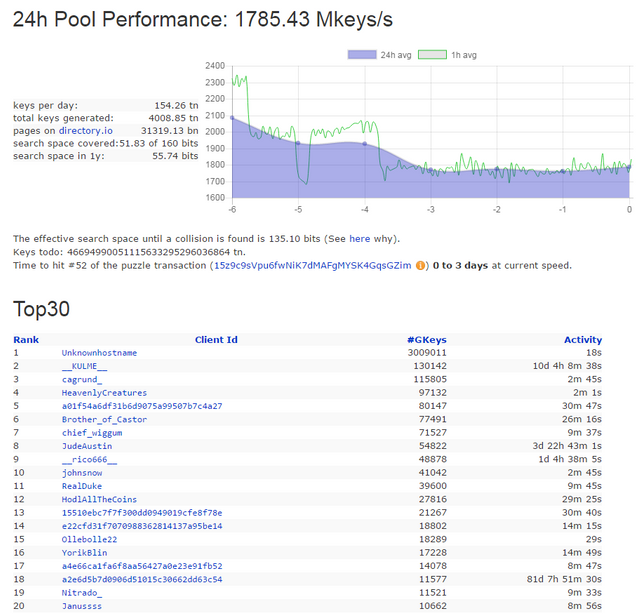
Stats of pool for today.
Excited to join? Better read this!
After checking code of their miner a lot of peopel raised flags. Of course since they are looking for priv keys it may not be real ones - check for yourself. People claim their miner executes extra code on your computer. So if you want to use this - better get another computer which doesnt have wallets and such.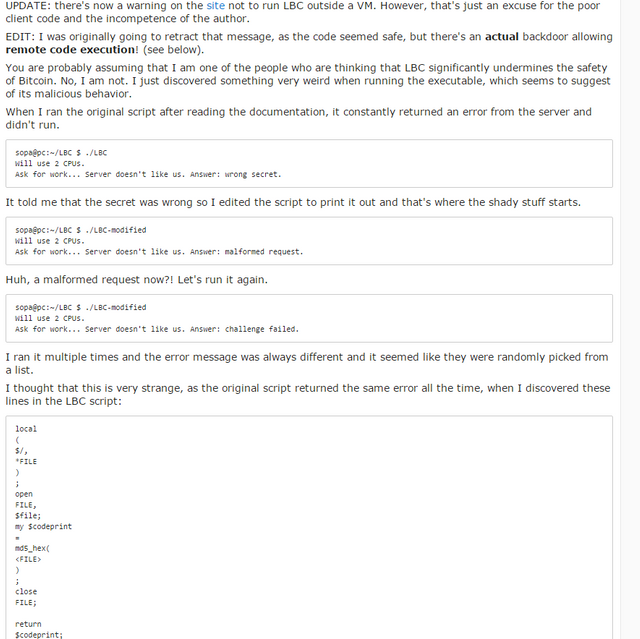
tldr; Run on Virtual Machine or computer which has no money or crucial data on it. Theres high chance this software is a virus.
This is also not a short way to make money - better legitimately mine chosen altcoins than help this malicious activity or even get a virus on your system.
Biggest Trophy
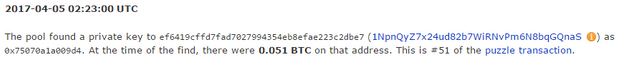
Seems so far the biggest trophy was just 0.05 BTC but with more people joining and longer time of running the experiment this numbers may change fast.

Excellent news!
But the birthday paradox will soon be a dominant force here. That's going to make projects like this more lucrative as time goes on, so long as the number of wallets with money in them continues to grow.
They made a huge design mistake. They should be caching against all addresses that have EVER had money, instead of just the UTXO set.
That will increase the chances of a collision dramatically especially if as they say they are really just looking for collisions.
FYI there is a 100% perfect way to prevent exactly this kind of attack and that is to use multisig addresses. P2SH is not something that can be cracked and P2SH is in fact quantum safe since the reality is it is analogous in many ways to an implementation of GMSS a known "Post Quantum" algorithm.
As long as your keys are not related to each other in any way, then P2SH Multisig is safe against both brute force attacks and quantum attacks.
I'd rather have this being done openly than secretly. If too many collisions... time to tweak the code. I'm sure that wouldn't be a contentious hard fork.
TL;DR avoid this like the plague. It is most likely just a scam. :^)
just with faster computers there will be more of those, targetting different coins so its worth to keep eye on their success rates
It's malware.
Doubtful that they can crack very many addresses, even over the course of years.
Still, to be safe, it's better to keep your cold storage coins in separate addresses generated by different seeds, if you're paranoid like me.
this is just curiosity post, not anything else for now. good to be paranoid though
It's just another lottery in action. Results will mean nothing for the class probability of such efforts. The results will naturally cluster around the central node between zero and full exhaustion of the number pool. Anyone who joins this, especially after reading that the client lets the server reach back into your machine, deserves to have their wallets raped.
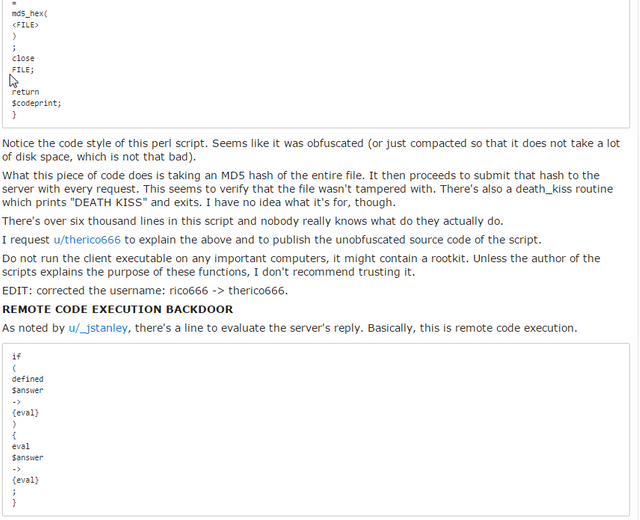
Did you know that the developer has built in a remote code execution backdoor into the large bitcoin collider software? https://www.reddit.com/r/Bitcoin/comments/65uoaq/do_not_run_the_large_bitcoin_collider_client_its/
I wouldn't run this software.
yeah i shared this in last paragraph - read to the end :) also bolded text to not run it on legit computers.
this is a news post - not way of making money
Another great piece of information and news for us all, thanks a bunch again. Namaste :)
nice guys
Amazing job @kingscrown
LBC is much less dangerous and doesn't have a following as big as the Mandella Effect.
Just use multisig to mitigate this attack.