Hijacker v1.5 - All-in-One Wi-Fi Cracking Tools for Android
Hijacker is a Graphical User Interface for the penetration testing tools Aircrack-ng, Airodump-ng, MDK3 and Reaver. It offers a simple and easy UI to use these tools without typing commands in a console and copy&pasting MAC addresses.
This application requires an ARM android device with an internal wireless adapter that supports Monitor Mode. A few android devices do, but none of them natively. This means that you will need a custom firmware. Any device that uses the BCM4339 chipset (MSM8974, such as Nexus 5, Xperia Z1/Z2, LG G2, LG G Flex, Samsung Galaxy Note 3) will work with Nexmon (which also supports some other chipsets). Devices that use BCM4330 can use bcmon.
An alternative would be to use an external adapter that supports monitor mode in Android with an OTG cable.
The required tools are included for armv7l and aarch64 devices as of version 1.1. The Nexmon driver and management utility for BCM4339 and BCM4358 are also included.
Root access is also necessary, as these tools need root to work.
Features
Information Gathering
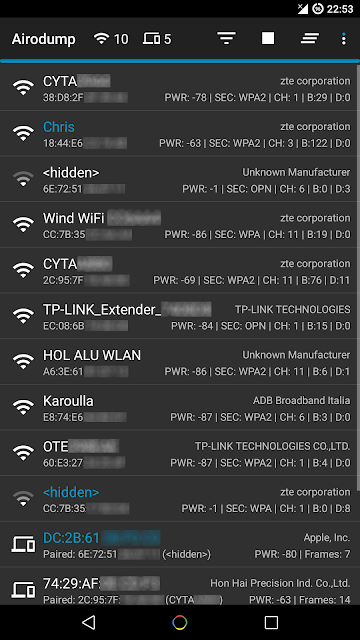
View a list of access points and stations (clients) around you (even hidden ones)
View the activity of a specific network (by measuring beacons and data packets) and its clients
Statistics about access points and stations
See the manufacturer of a device (AP or station) from the OUI database
See the signal power of devices and filter the ones that are closer to you
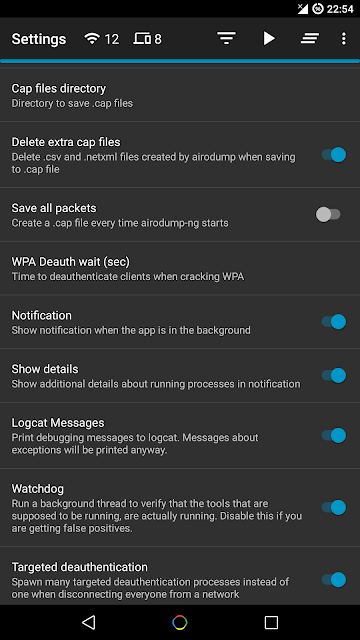
Save captured packets in .cap file
Attacks
Deauthenticate all the clients of a network (either targeting each one (effective) or without specific target)
Deauthenticate a specific client from the network it's connected
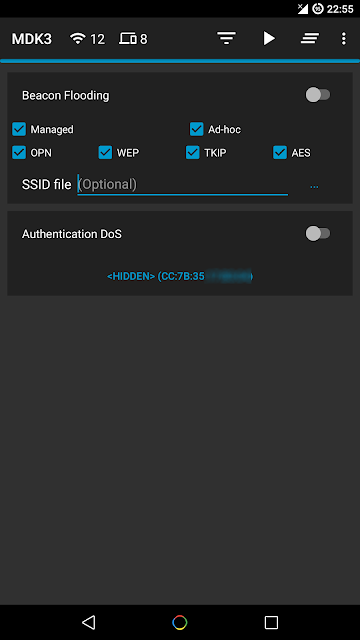
MDK3 Beacon Flooding with custom options and SSID list
MDK3 Authentication DoS for a specific network or to every nearby AP
Capture a WPA handshake or gather IVs to crack a WEP network
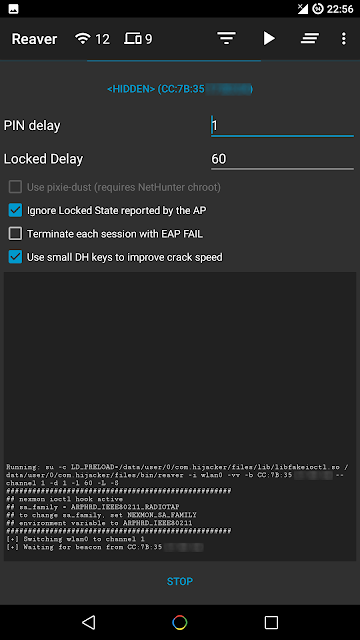
Reaver WPS cracking (pixie-dust attack using NetHunter chroot and external adapter)
Other
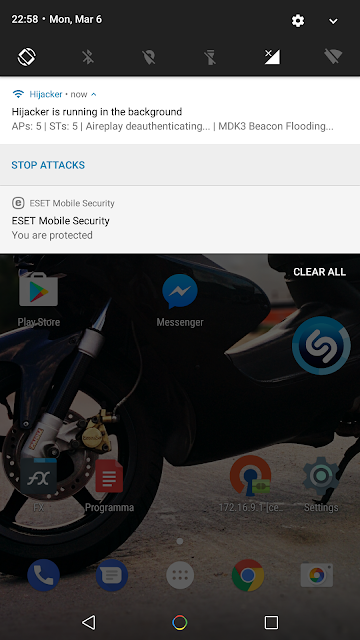
Leave the app running in the background, optionally with a notification
Copy commands or MAC addresses to clipboard
Includes the required tools, no need for manual installation
Includes the Nexmon driver, required library and management utility for BCM4339 and BCM4358 devices
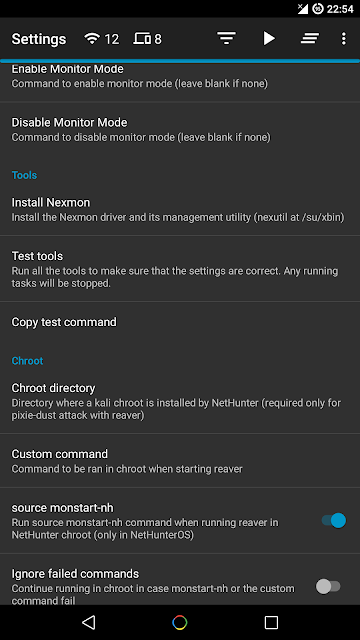
Set commands to enable and disable monitor mode automatically
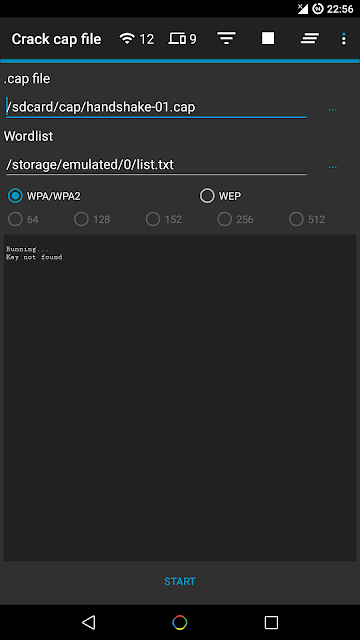
Crack .cap files with a custom wordlist
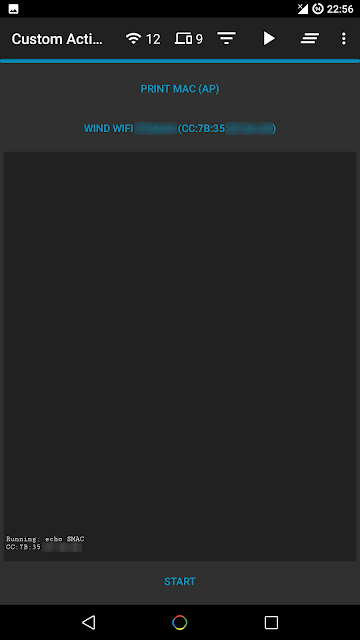
Create custom actions and run them on an access point or a client easily
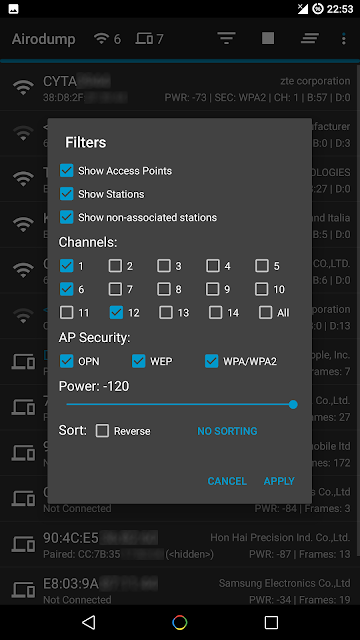
Sort and filter Access Points and Stations with many parameters
Export all gathered information to a file
Add a persistent alias to a device (by MAC) for easier identification
Screenshots
Installation
Make sure:
you are on Android 5+
you are rooted (SuperSU is required, if you are on CM/LineageOS install SuperSU)
you have a firmware to support Monitor Mode on your wireless interface
Download the latest version here:
https://github.com/chrisk44/Hijacker/releases
When you run Hijacker for the first time, you will be asked whether you want to install the nexmon firmware or go to home screen. If you have installed your firmware or use an external adapter, you can just go to the home screen. Otherwise, and if your device is supported, click 'Install Nexmon' and then 'Install'. Afterwards you will land on the home screen and airodump will start. Make sure you have enabled your WiFi and it's in monitor mode.
Note: On some devices, changing files in /system might trigger an Android security feature and your system partition will be restored when you reboot.
Troubleshooting
This app is designed and tested for ARM devices. All the binaries included are compiled for that architecture and will not work on anything else. You can check whether your device is compatible by going to Settings: if you have the option to install Nexmon, then you are on the correct architecture, otherwise you will have to install all the tools manually (busybox, aircrack-ng suite, mdk3, reaver, wireless tools, libfakeioctl.so library) in a PATH accessible directory and set the 'Prefix' option for the tools to preload the library they need: LD_PRELOAD=/path/to/libfakeioctl.so.
In settings, there is an option to test the tools. If something fails, you can click 'Copy test command' and select the tool that fails. This will copy a test command to your clipboard, which you can manually run in a root shell and see what's wrong. If all the tests pass and you still have a problem, feel free to open an issue here to fix it, or use the 'Send feedback' option in the app's settings.
If the app happens to crash, a new activity will start which will generate a bug report in your external storage and give you the option to submit it by email. The report is shown in the activity so you can see exactly what will be sent.