Crypto Academy :Season 3 Week 2| Homework Post For [@pelon53]- Hash and Cryptography
Hi @pelon53 ! I am excited to be one of your students in season 3 of the steemit crypto academy. Below is my entrance on your homework post.

Have you ever realized the algorithm behind the blockchain security and privacy, All these features that gives the blockchain it’s anonymity is driven by hash and cryptography. That is why our wallet addresses are unique and a lot of calculations are required in order to generate a block in POW mining.
What is Cryptography and hashing then?
By and large, cryptography and hashing are vital approaches to keep information secrecy in the blockchain.
Cryptography
Cryptography is the study of concealing data on display, to cover it from unapproved access. It is a method of putting away and communicating information in a specific structure so that solitary those for whom it is proposed can peruse and deal with it. All in all, it involves encrypting and decrypting data
Hashing
Hashing is the change of a series of characters into a normally more limited fixed-length value that addresses the first one. It shouldn't be feasible to transform the value from a hashed function other than attempting every one of the possible values . It ought to consistently deliver a similar value independent of various attempts. Indeed, even somewhat level change should make the entire hashed value change. Shouldnt prompts collission (No two numbers to have same hash value or event of such a case is close to nothing)
Resistance to collision
This is one of the properties of hashing. When a hash function say A, is resistant to collision, it means you have to find two inputs say, X and Y. To make finding the terms such that A=A and X=!Y difficult to achieve. The resistance to collision doesn’t mean there is no collision in the hash function but this is rare in resistance to collision. This is why cryptographic hash functions are built to be resistance to collision. For a hash function to be considered resistance to collision, it should have a minimum length of 160 bit
Preimage Resistance
A preimage attack enables to make an input that delivers a predefined result. A feasible preimage attack essentially implies that the hash algorithm is totally broken. The efforts and resistance to keep away from these attacks on the hashed functions is what is referred to as Preimage Resistance
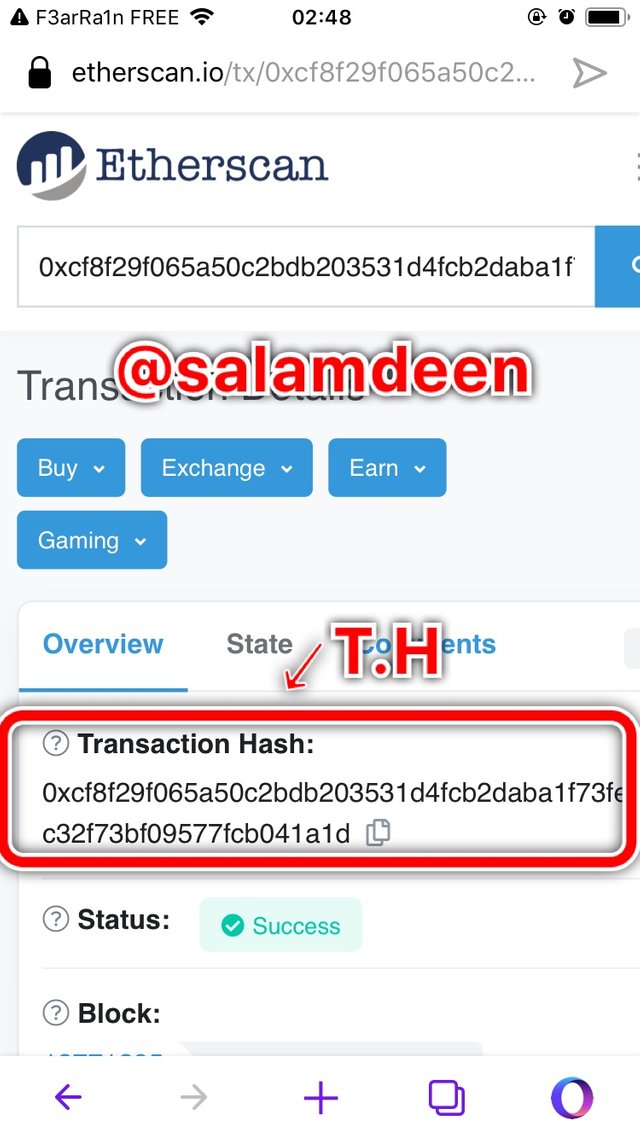
How I used Etherscan to verify the hash of the last block and the hash of the last transaction.
I first of all opened etherscan. Hence all images are screenshots from that site
Upon opening the site, the latest blocks are available on the homepage with the latest transactions. As shown in the picture below, the latest block at that time was with the block height: 1277128
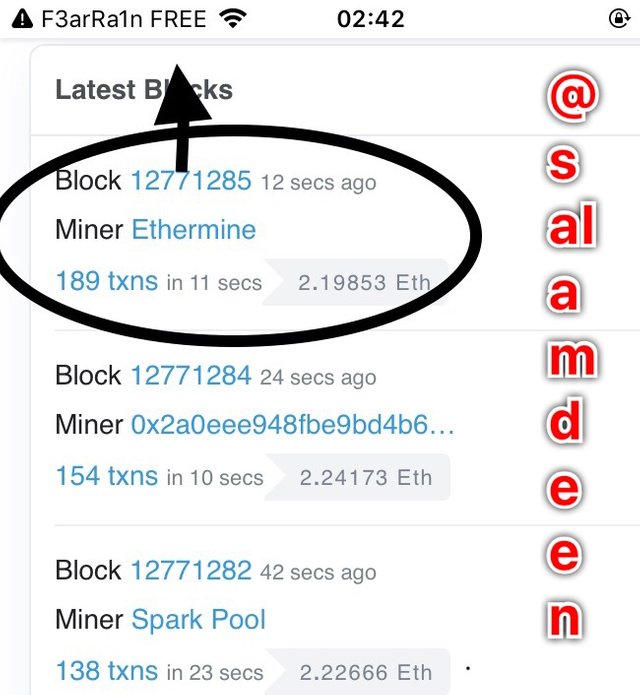
I want to verify that block so I clicked on that block and it’s details was shown. Including it’s transactions and hash.
The Hash of the block is
0x47492ad7d324d60163fb4d4882f95b4788cc787466bd7ed5f3de5837f8a601d1
With 189 transaction.
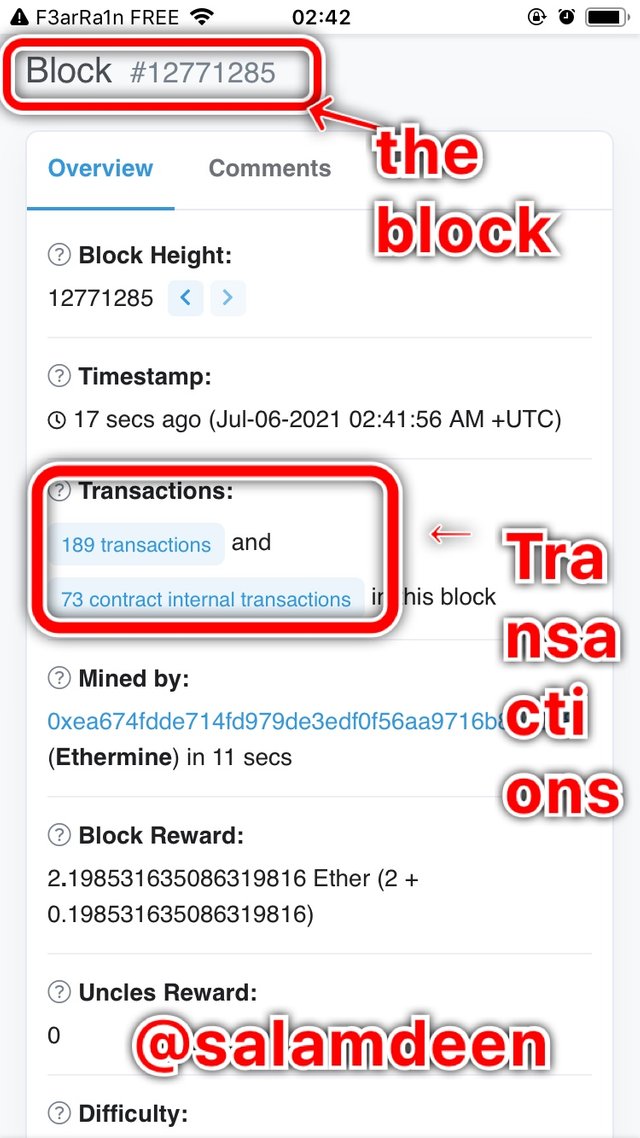
The hash of the block is shown here

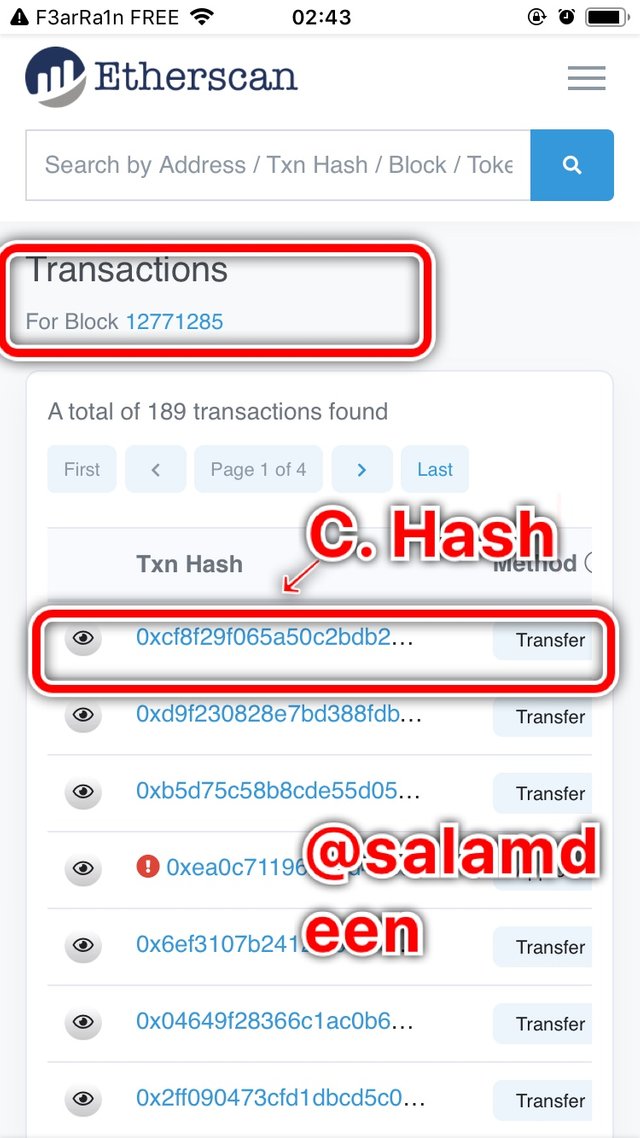
I clicked on transactions and the transactions under that block are shown below. The C. Hash indicates the hash I’ve confirmed
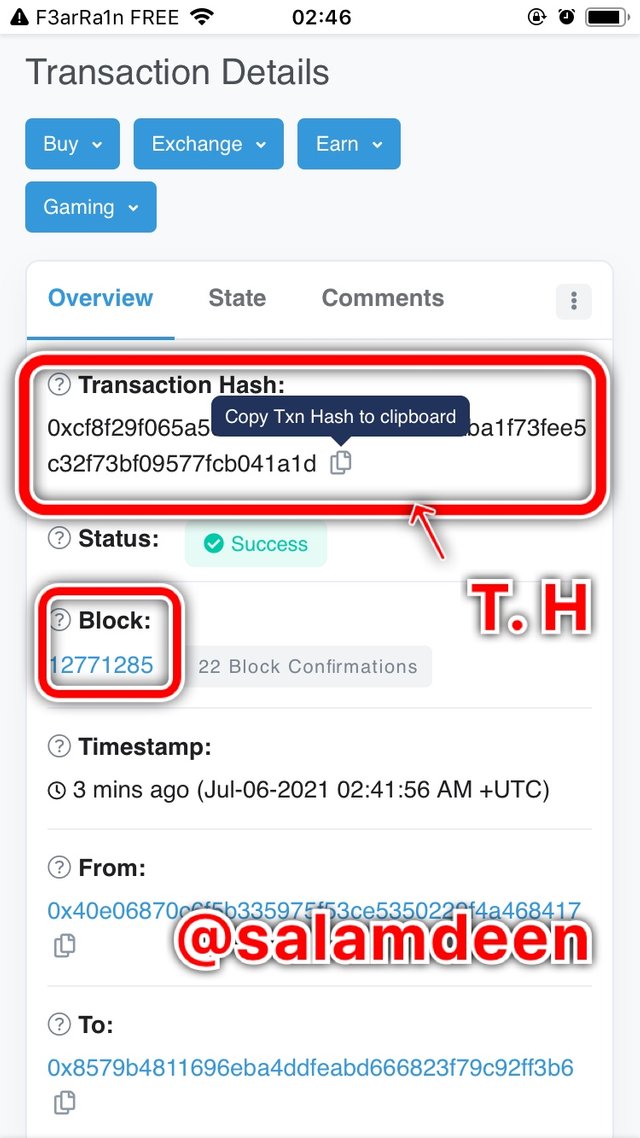
I clicked on one of the transactions and it’s details was shown. From the picture, it shows that the transaction belongs to the block with height of 12771285.
The hash of the transaction is
0xcf8f29f065a50c2bdb203531d4fcb2daba1f73fee5c32f73bf09577fcb041a1d
NB: I used T. H in place of transaction hash
To confirm this, i pasted the transaction hash and the same details was given as when I checked through the block.
NB: I used T. H in place of transaction hash
How I used Tronscan to verify the hash of the last block and the hash of the last transaction.
- I visited tronscan.org Hence all images here are screenshots from that site
- On the homepage, the latest transactions and blocks are all available
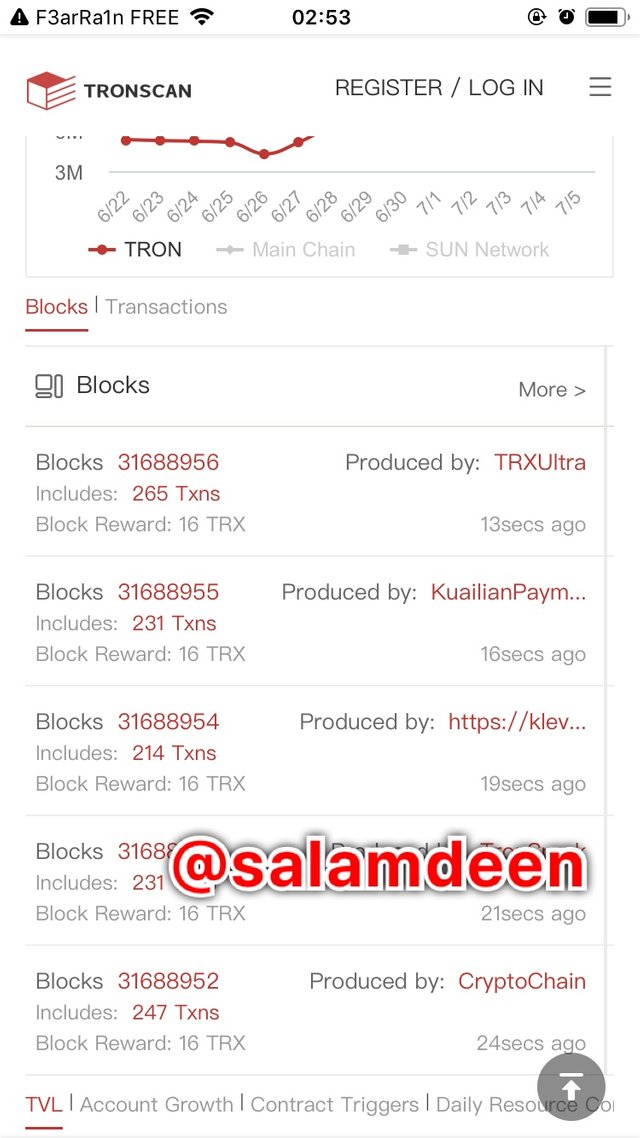
- I clicked on one of the latest blocks and it’s details were shown with the hash of the block and the number of transactions
Block height: 31688956
Block hash: fc45df0939de81b35bc35c5819363cff95c1a31a89177512796c6050e45109a6

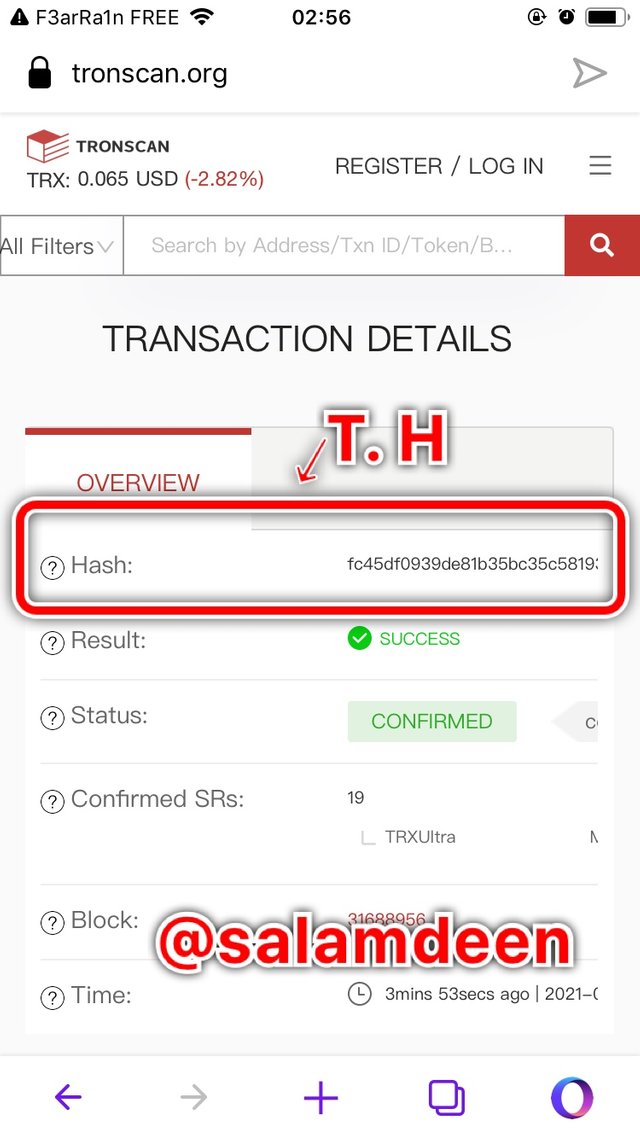
- The transactions of that block are beneath the details of the block. Hence I clicked on one of the transactions and it’s details are shown
Hash of the transaction : fc45df0939de81b35bc35c5819363cff95c1a31a89177512796c6050e45109a6
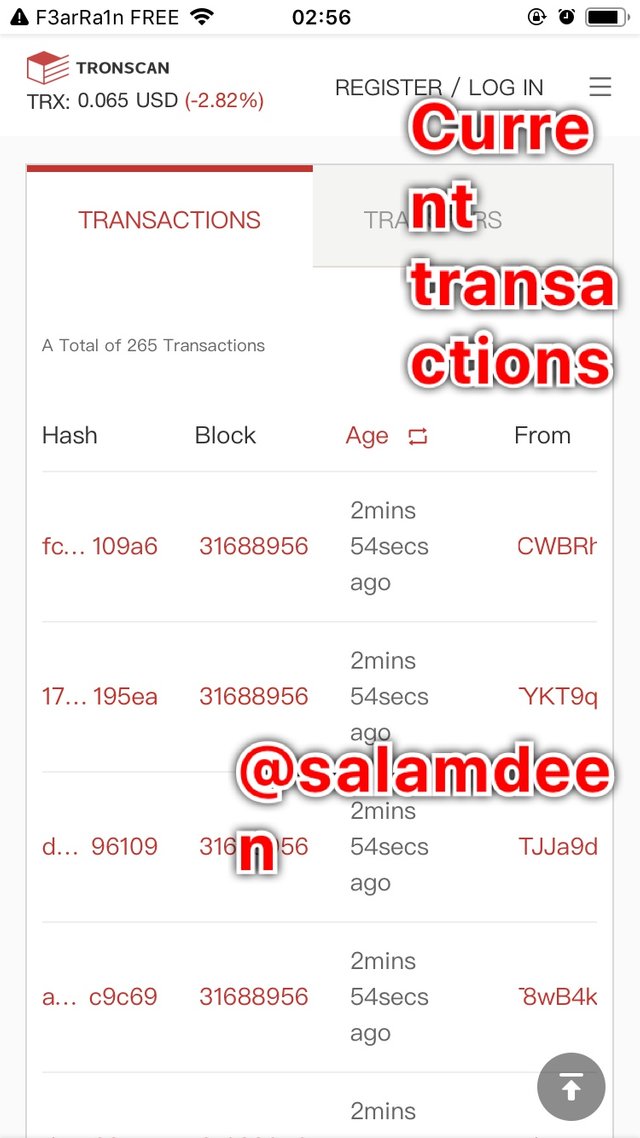
Transaction details of the latest transaction
How I generated the Hash SHA256 from cryptoacademy and Cryptoacademy
I will generate the Hash SHA-256 from these two words “cryptoacademy and Cryptoacademy” from this site https://passwordsgenerator.net/sha256-hash-generator/
Hence, all images in this section are screenshots from that link.
To generate cryptoacademy, I wrote the word in the text field then the hash was generated for me as shown in the picture below
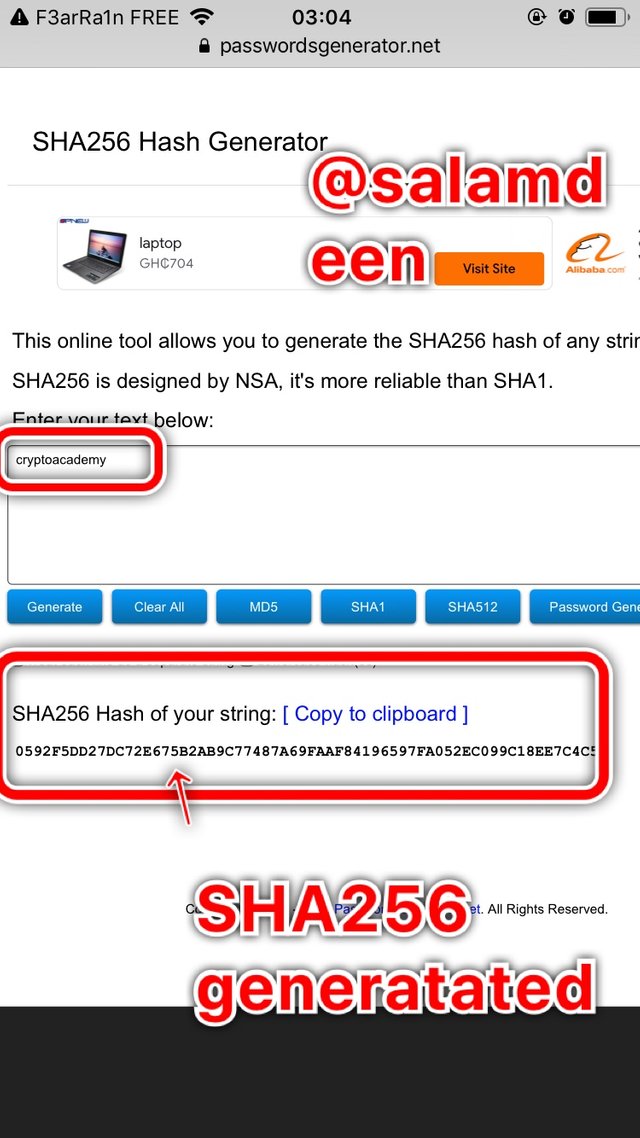
cryptoacademy Hash SHA-256 : 0592F5DD27DC72E675B2AB9C77487A69FAAF84196597FA052EC099C18EE7C4C5
To generate Hash SHA-256 Of Cryptoacademy, I wrote the word in the text box and it was automatically generated.
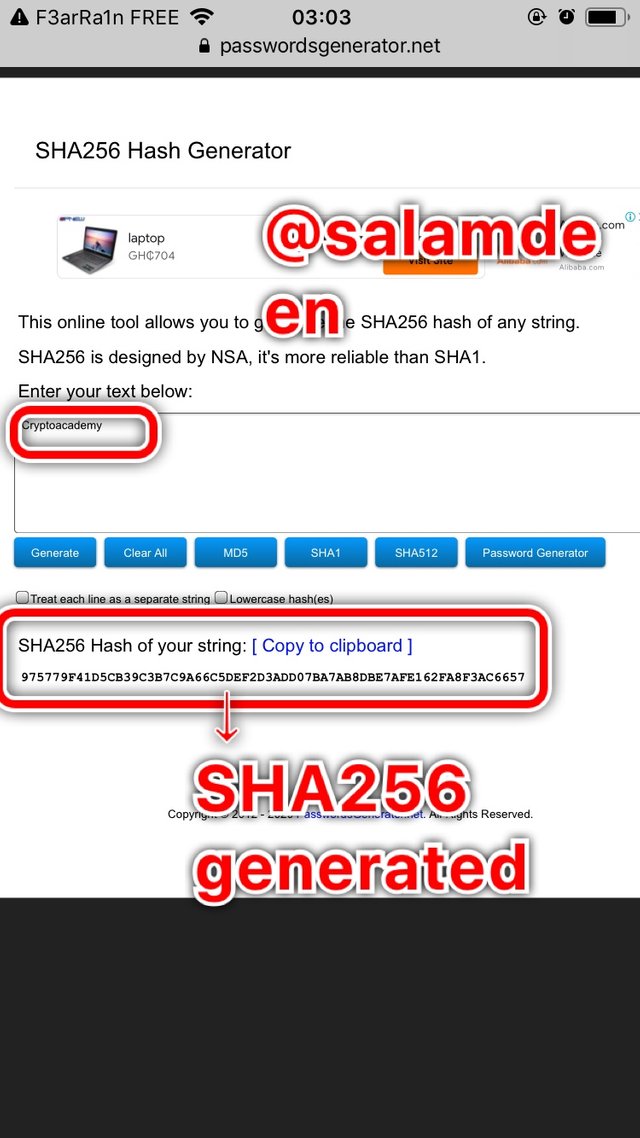
Cryptoacademy Hash SHA-256: 975779F41D5CB39C3B7C9A66C5DEF2D3ADD07BA7AB8DBE7AFE162FA8F3AC6657
As shown in all the demonstrations above, the Hash values generated from these two words looks totally difference, although they’re all the same words to the understanding of man. This is as a result of changing the case of just one word from uppercase to lower case. This is what gives the hash SHA-256 it’s resistance to collision property.
Difference between Cryptography and Hashing
The table below contains the main difference between Hashing and Cryptography
| Hashing | Cryptography |
|---|---|
| The process is irreversible. To know the original data, you have to compare the encoded data | The process is reversible. Meaning encrypted data can be decrypted |
| It basically involves conversion of data into a fixed value to represent the original data | The main aim is to hide the meaning behind data |
| Fixed length of all encoded data | In cryptography, length of encoded data varies |
| Keys are not required | Keys are required in cryptography. The brain behind cryptography is security |
Conclusion
After going through the lecture by professor @pelon53 , and doing research for this assignment I’ve learnt more about the blockchain technology with regards to hashing and cryptography and I’ve realized how important they are in the world of cryptocurrencies. The assignment have really helped me gain real world experience on how the two functions works. I can’t wait to take part in the continuation of the topic from the professor.
NB: All screenshots are taken from the above sites involved. For clearity of my demonstrations to the professor, these images are not resized because trying to do so makes the images blur in my phone.
Thank you
Cc:
@pelon53
No estuvo claro la explicación de Resistencia a la Colisión y la Resistencia a Preimagen no fue explicada bien.
La pregunta 3, la palabra era CryptoAcademy, tanto la C como la A eran mayúscula.
Puedes mejorar en las próximas tareas, sigue adelante.
Recomendaciones:
Es necesario que leas con detenimiento cada pregunta, para que tus respuestas puedan ser las correctas. Para mejorar tu presentación, puedes justificar el texto.Calificación: 7.5
.